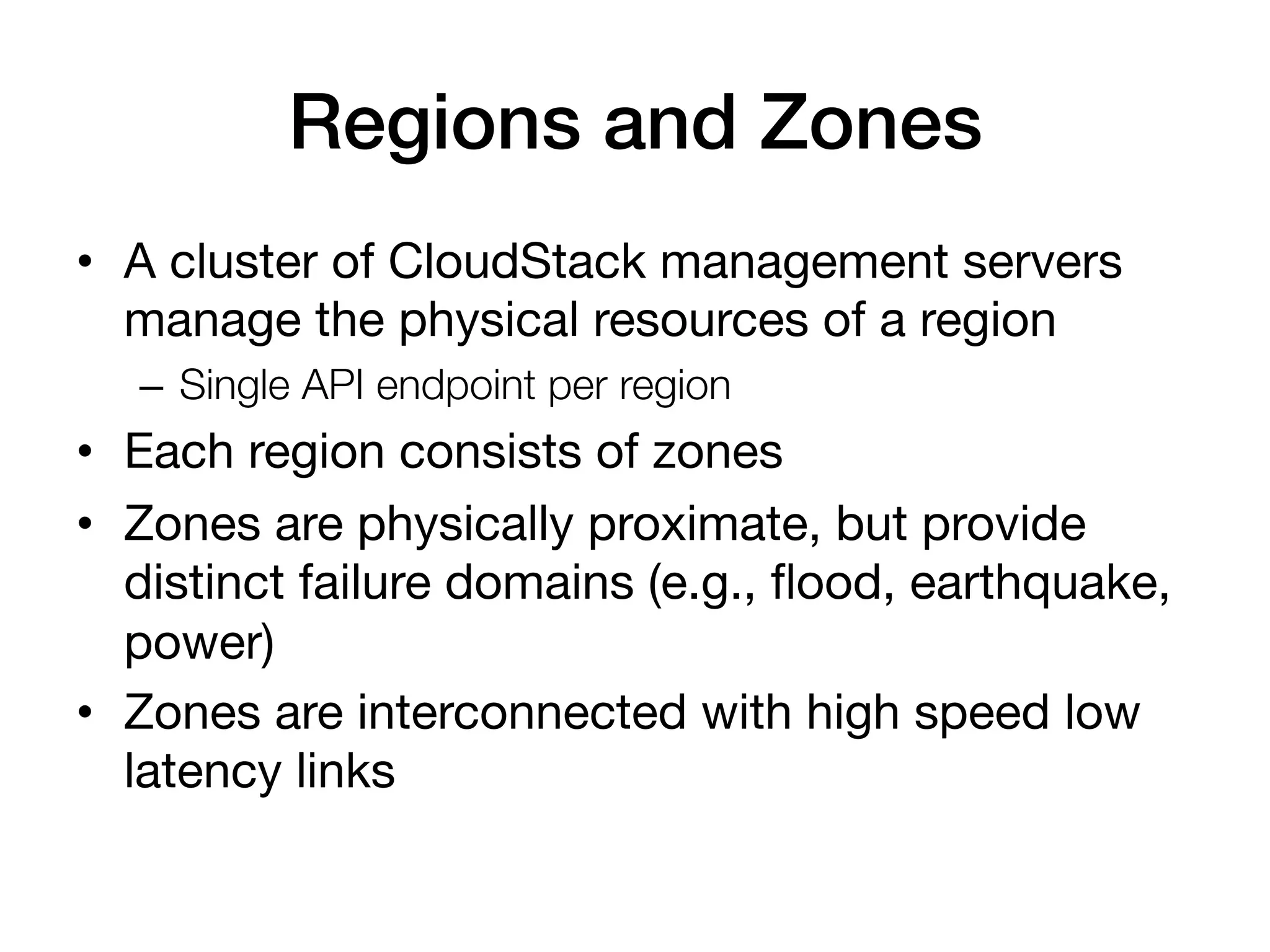
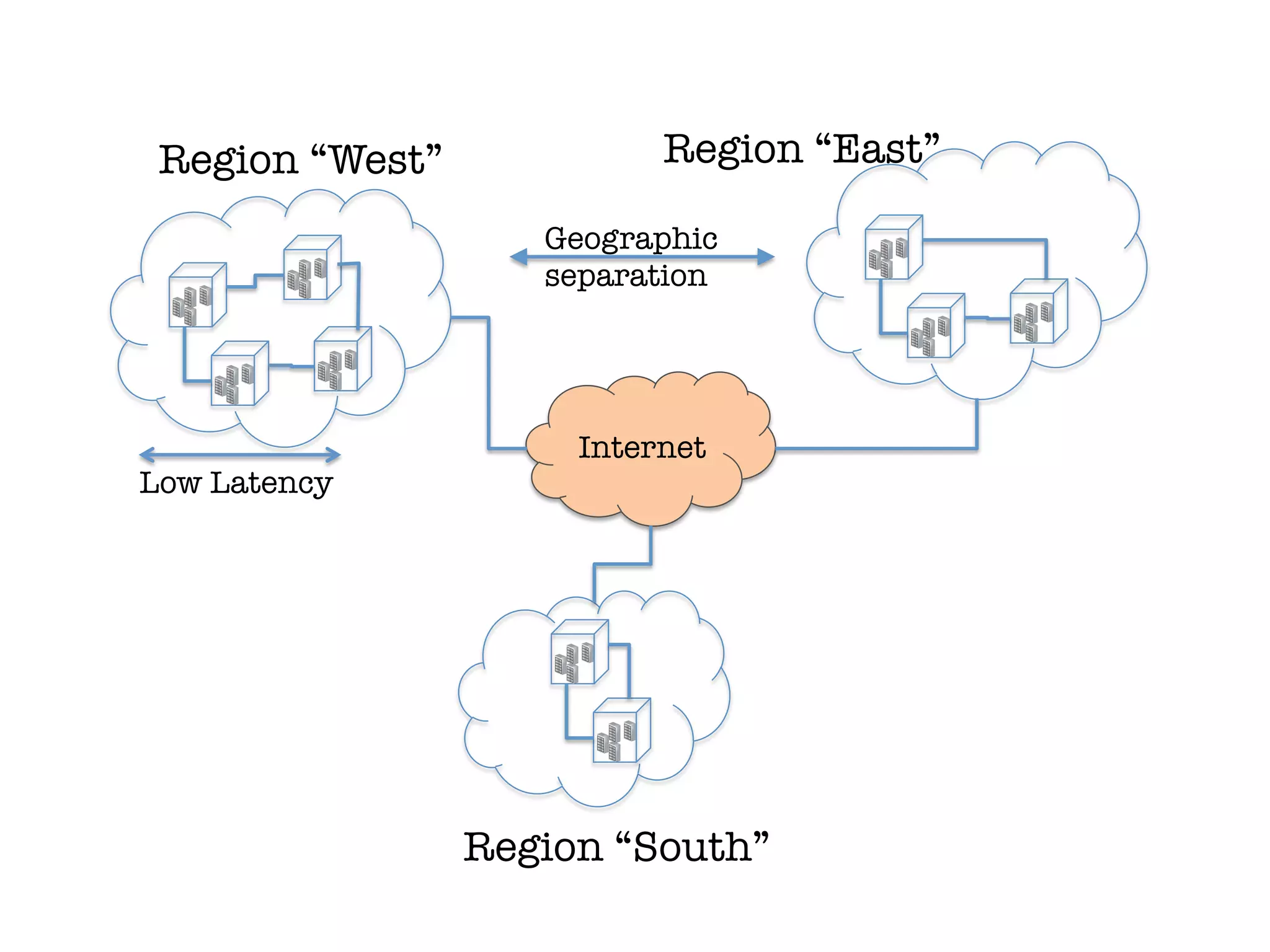
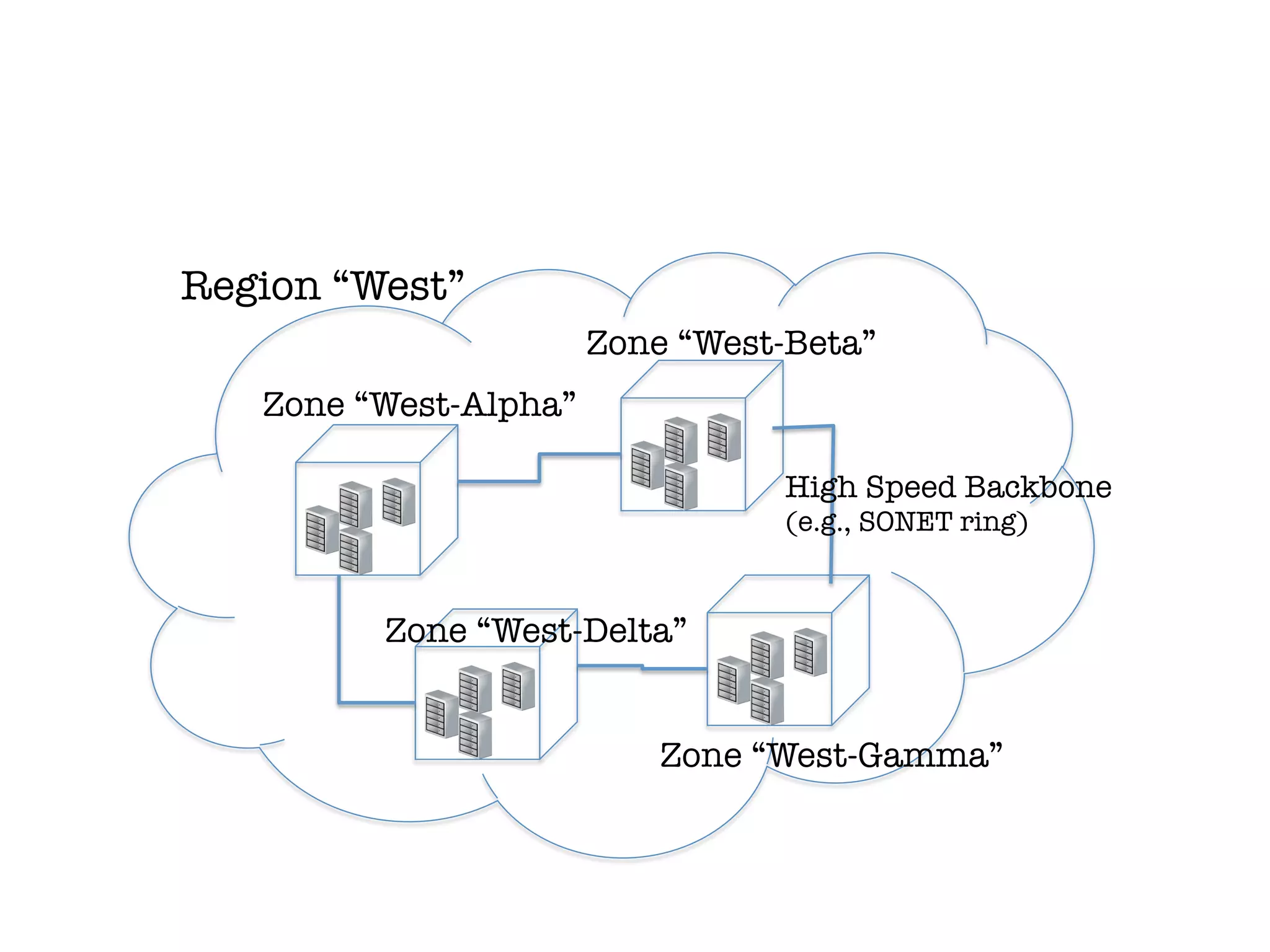
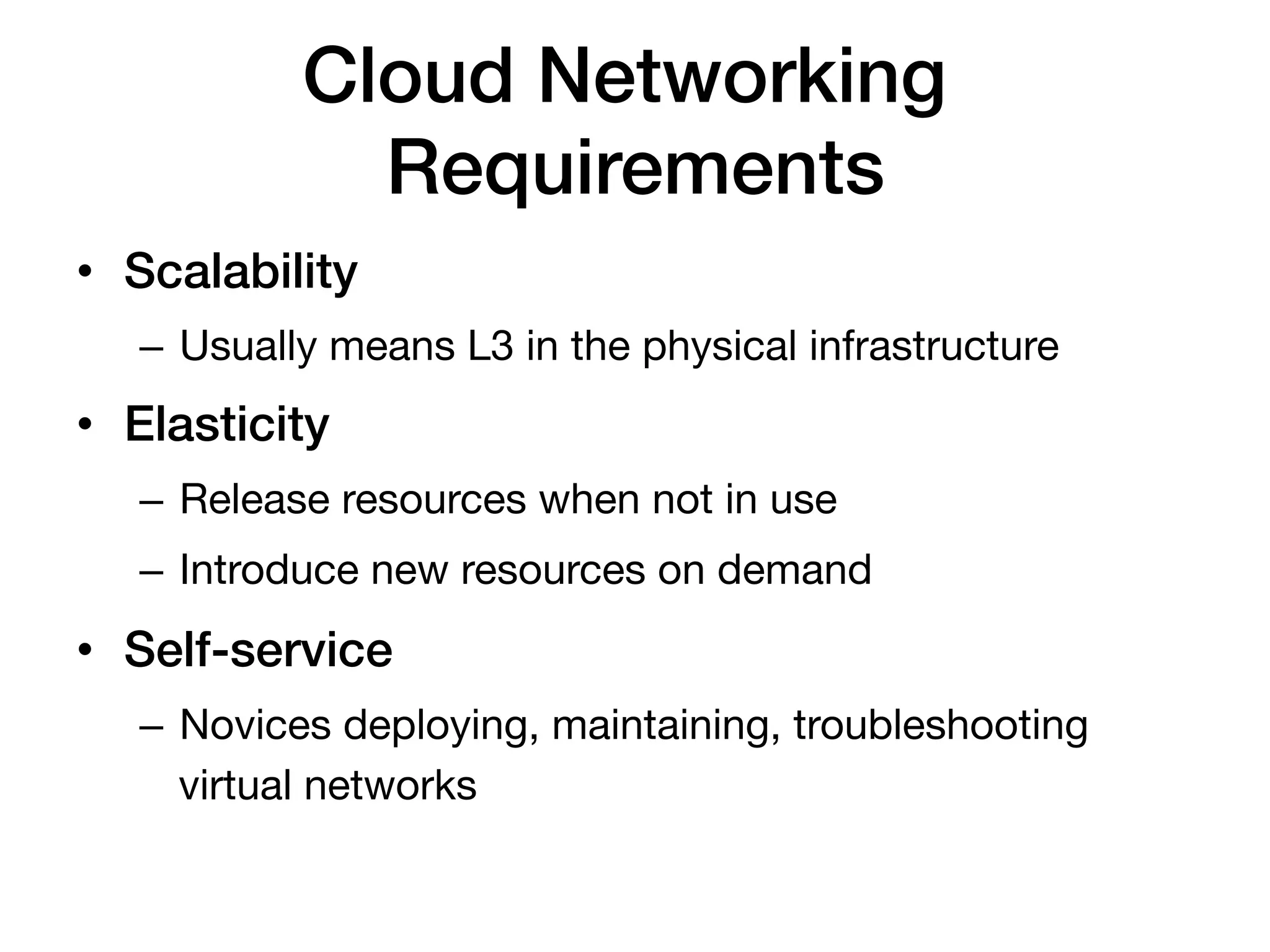
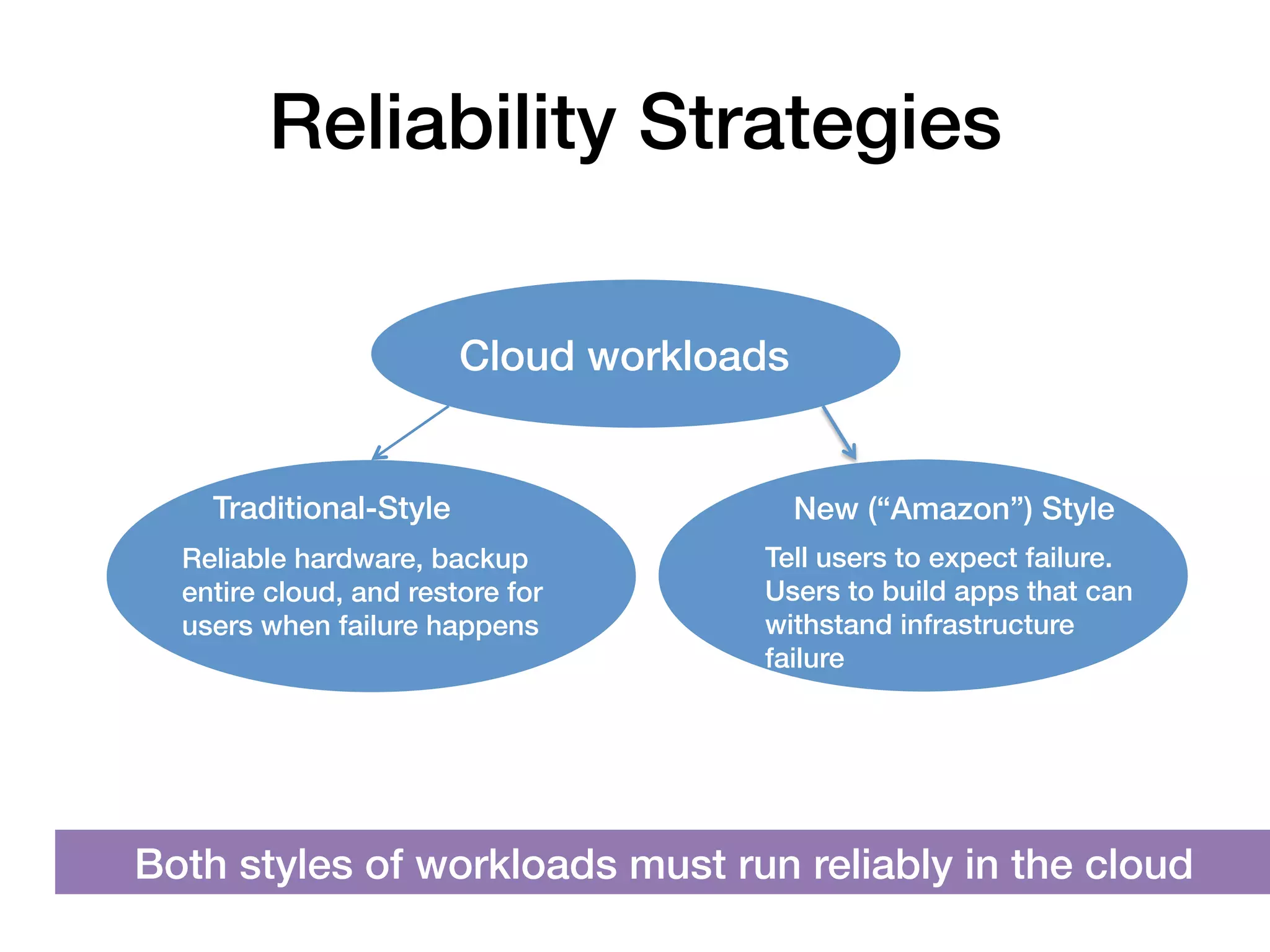
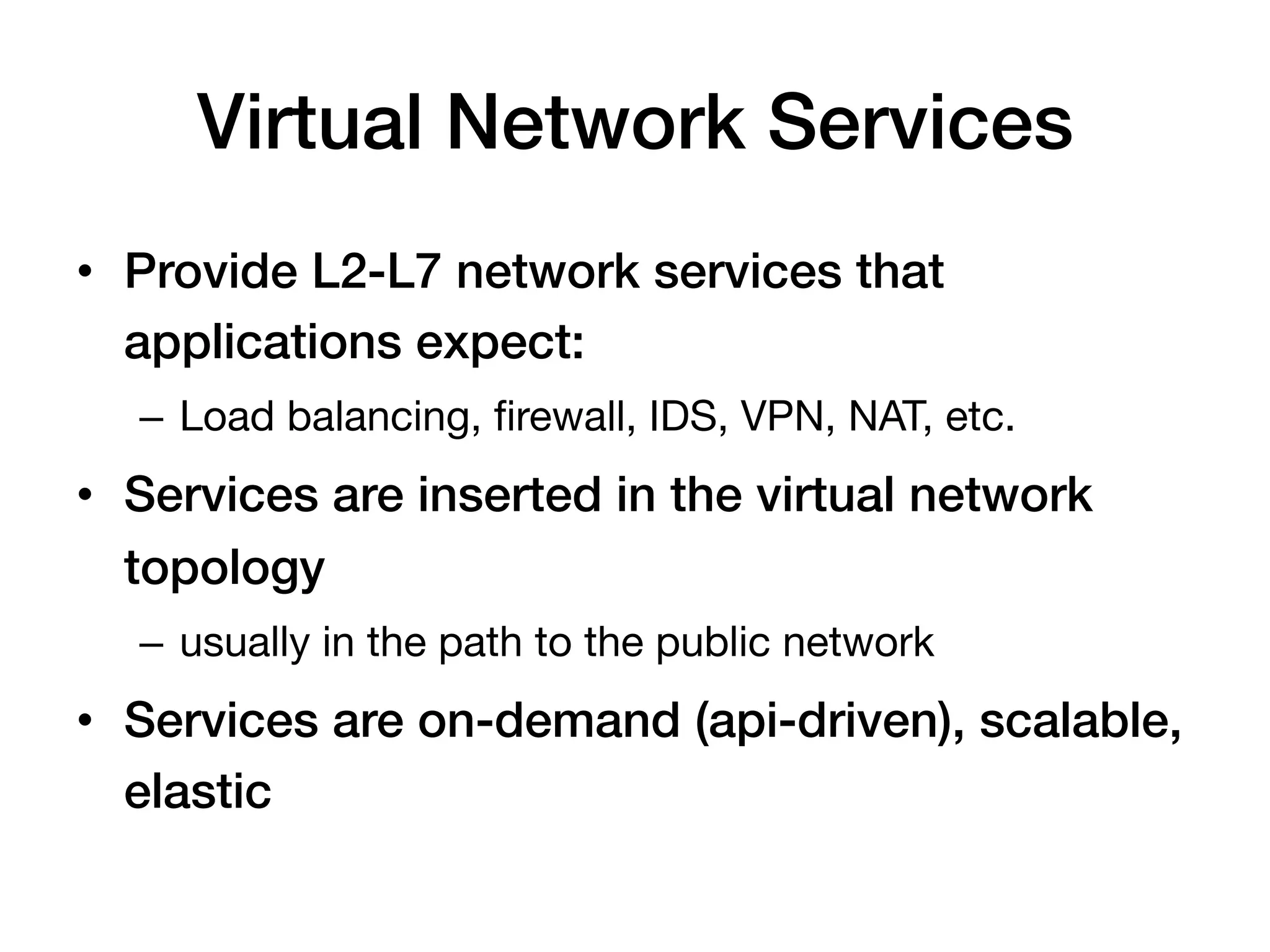
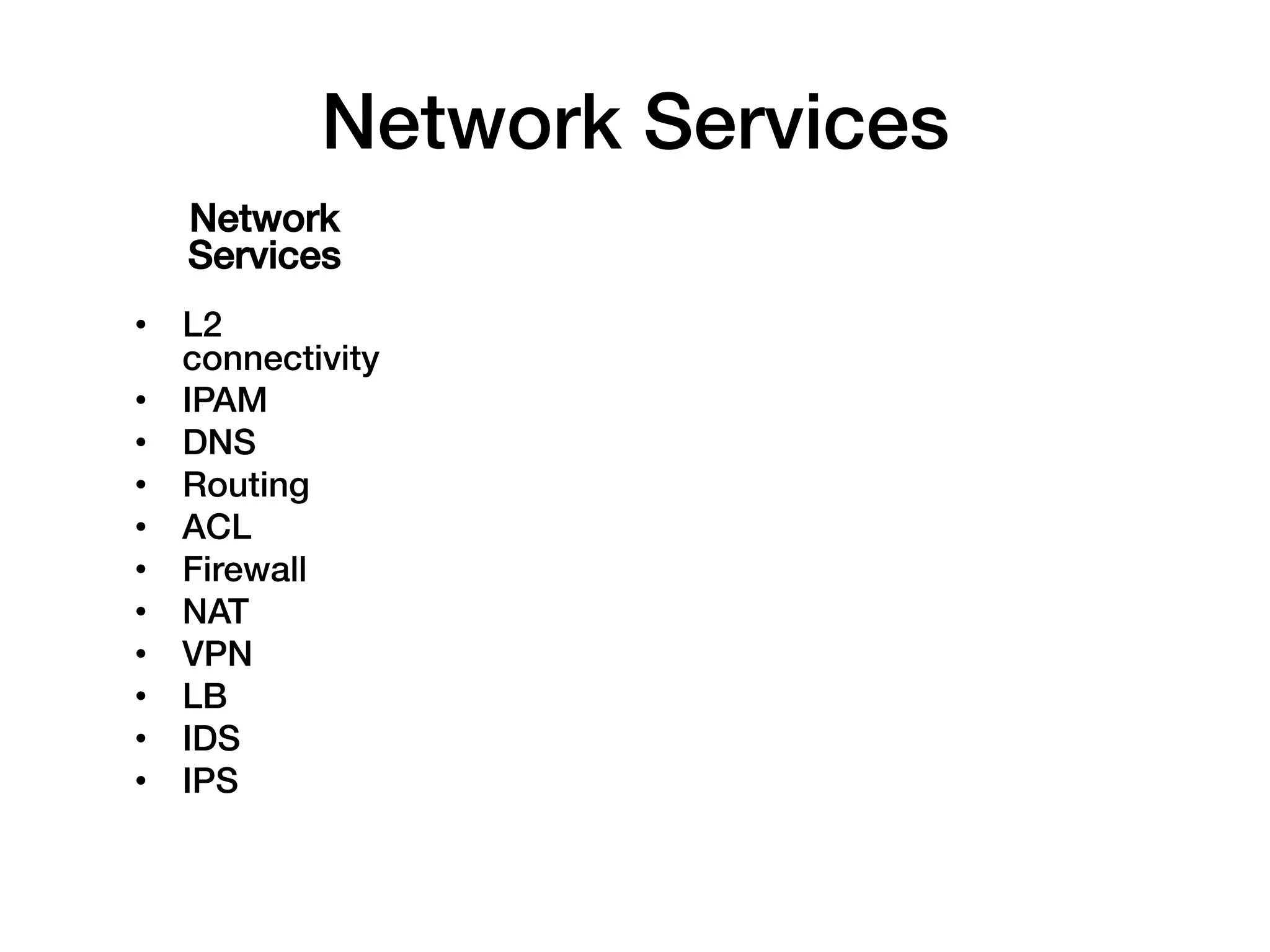
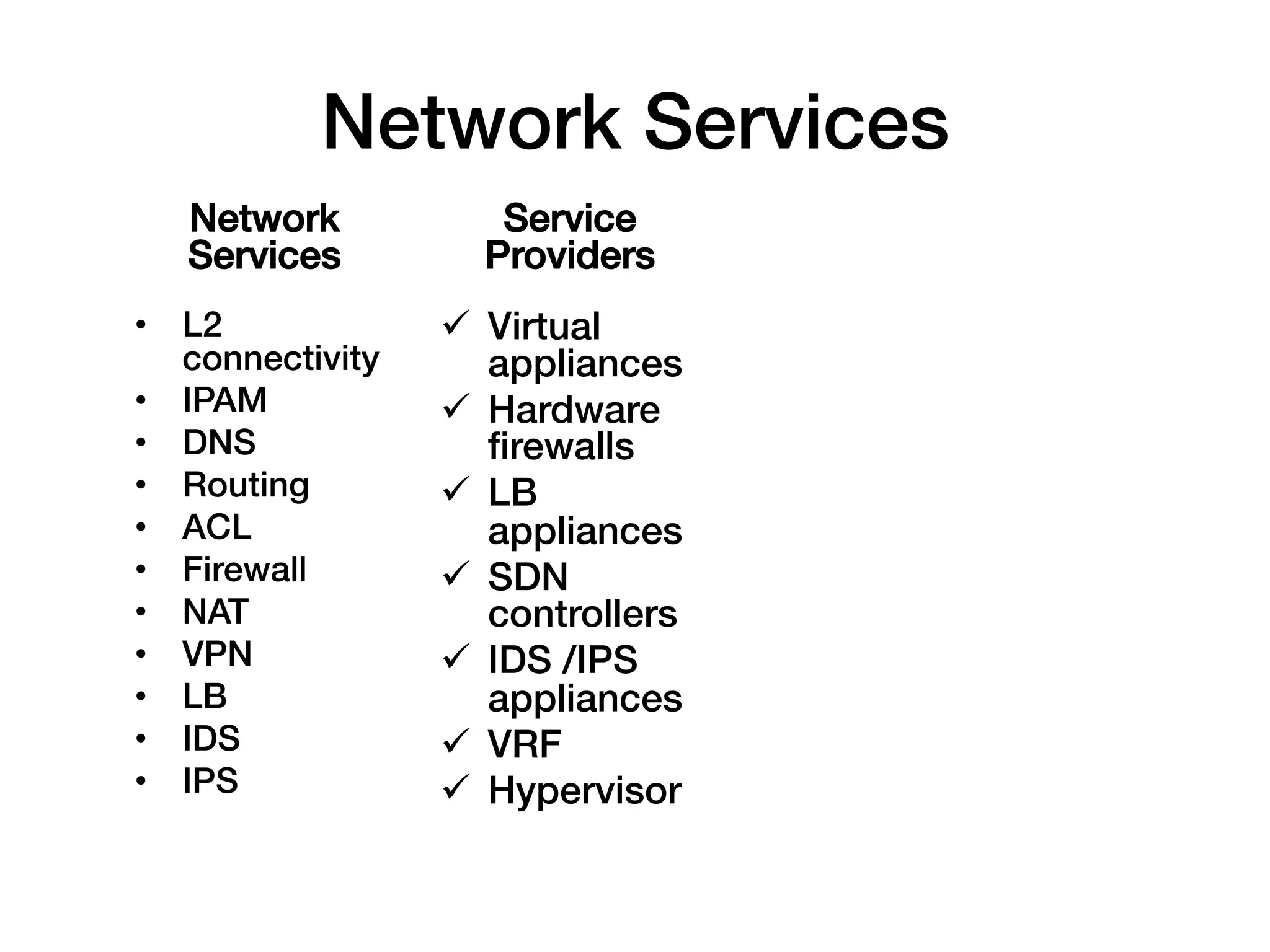
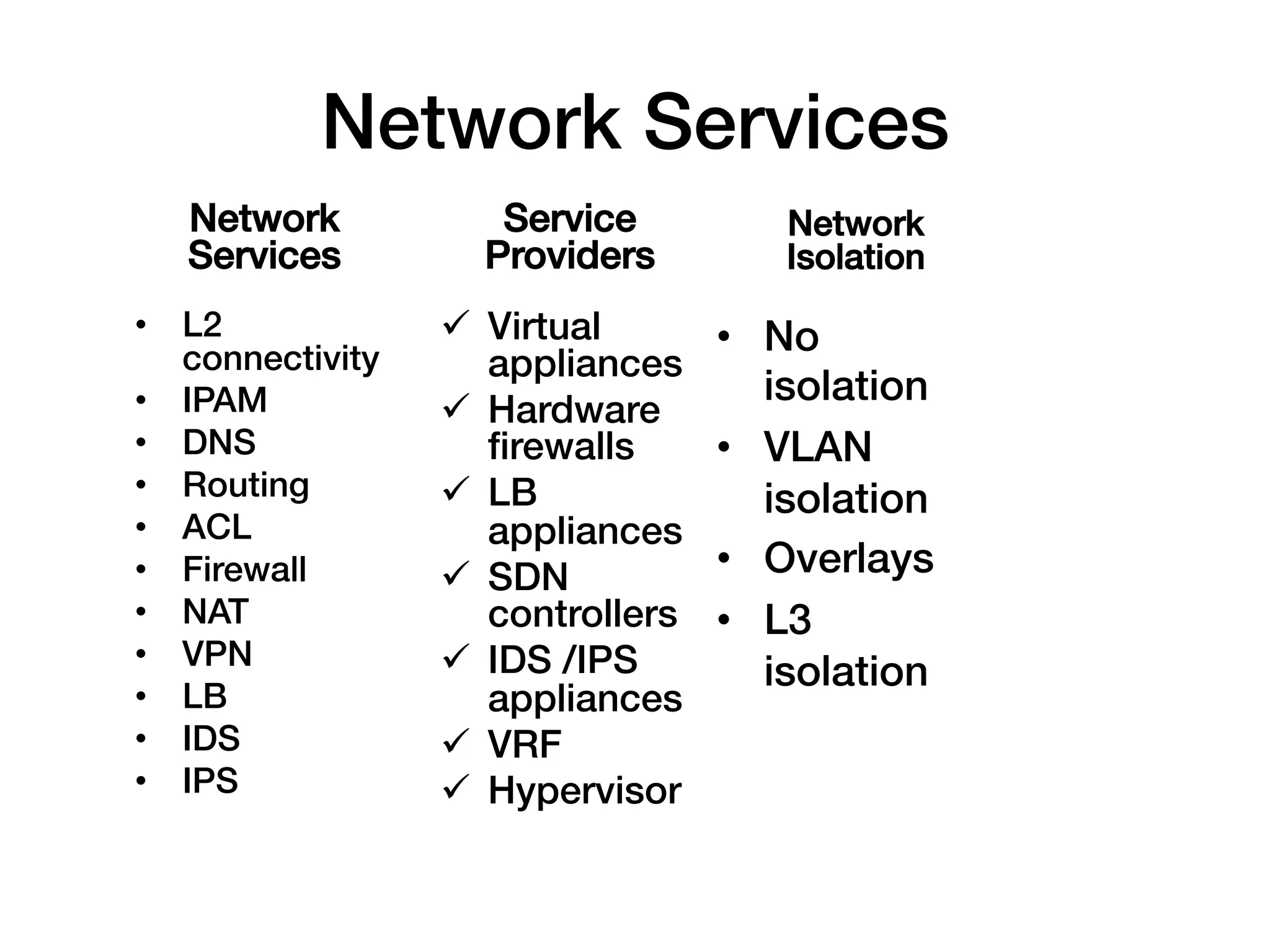
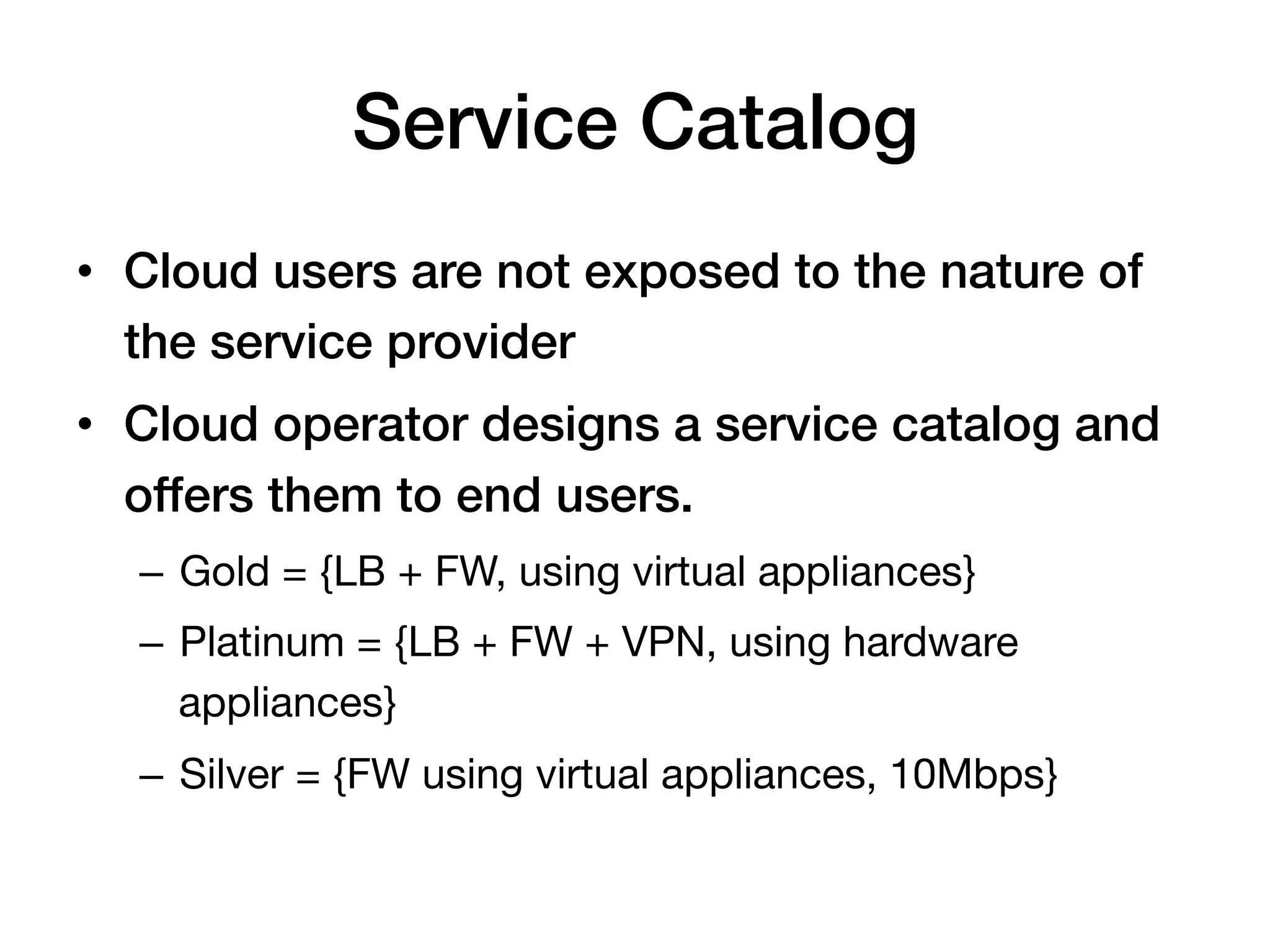
The document discusses the evolution of networking in the cloud, particularly emphasizing services like Apache CloudStack which enable agile cloud orchestration for both private and public clouds. It outlines key concepts such as virtual networking, infrastructure-as-a-service (IaaS), and the principles of cloud computing like scalability, elasticity, and self-service, while addressing traditional networking challenges. The document also highlights the importance of reliability strategies for cloud workloads and how virtual network services support the demands of modern applications.
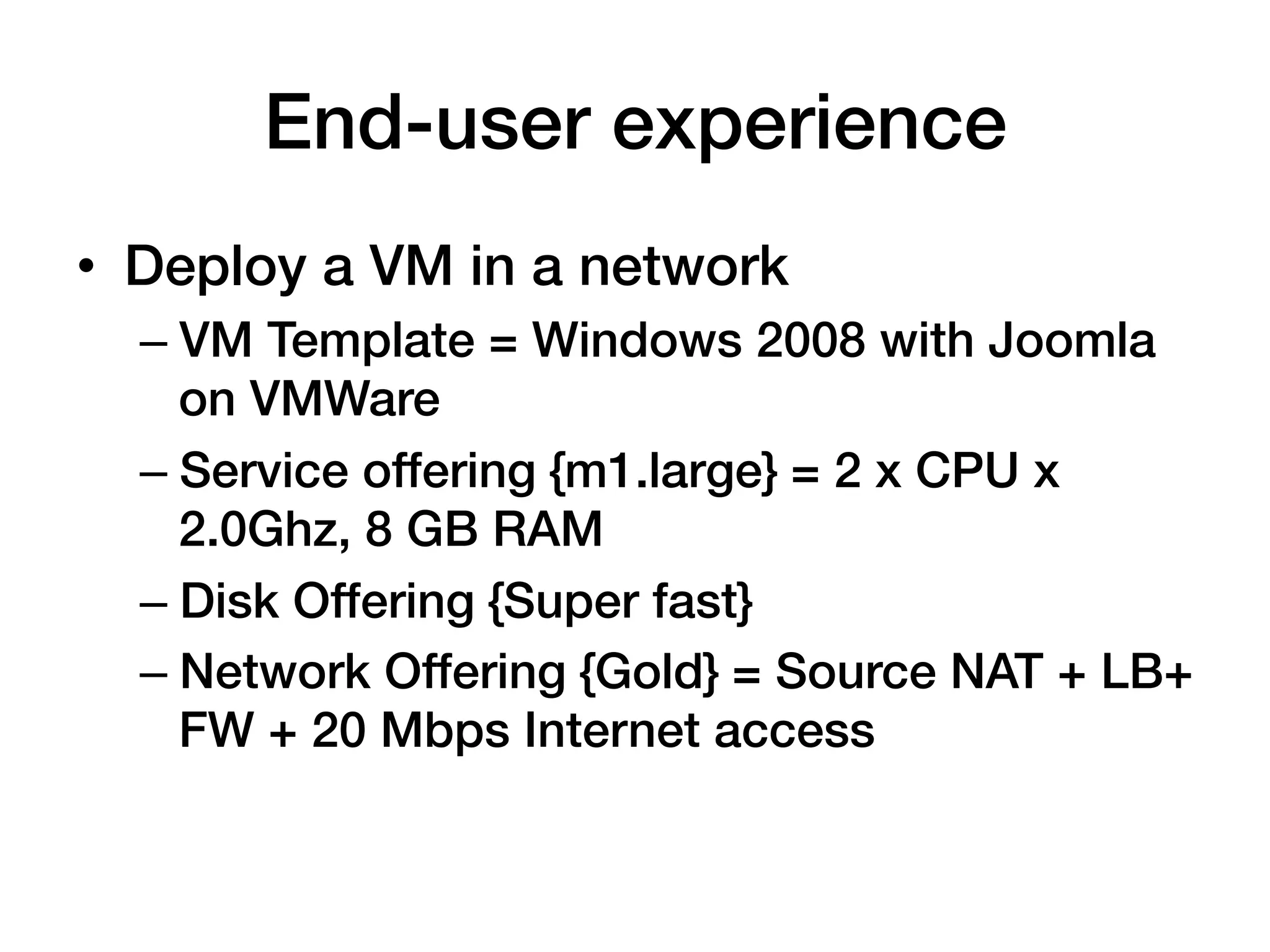
![Traditional! Cloud!
• 10x more
scaleable!
• 2-5x lower
cost!
• 100% more
open!
Built for traditional Designed around big data,
enterprise apps & client- massive scale & next-gen
server compute! apps!
• Enterprise arch for 100s of • Cloud architecture for 1000s
hosts! of hosts!
• Scale-up (server clusters) ! • Scale-out (multi-site server
• Apps assume reliability! farms)!
• IT Mgmt-centric [1:Dozens]! • Apps assume failure!
• Proprietary vendor stack! • Autonomic [1:1,000’s]!
• Open, value-added stack!](https://image.slidesharecdn.com/networkinginthecloudagelisa2012-121214005629-phpapp01/75/Networking-in-the-Cloud-Age-LISA-2012-Tutorial-9-2048.jpg)
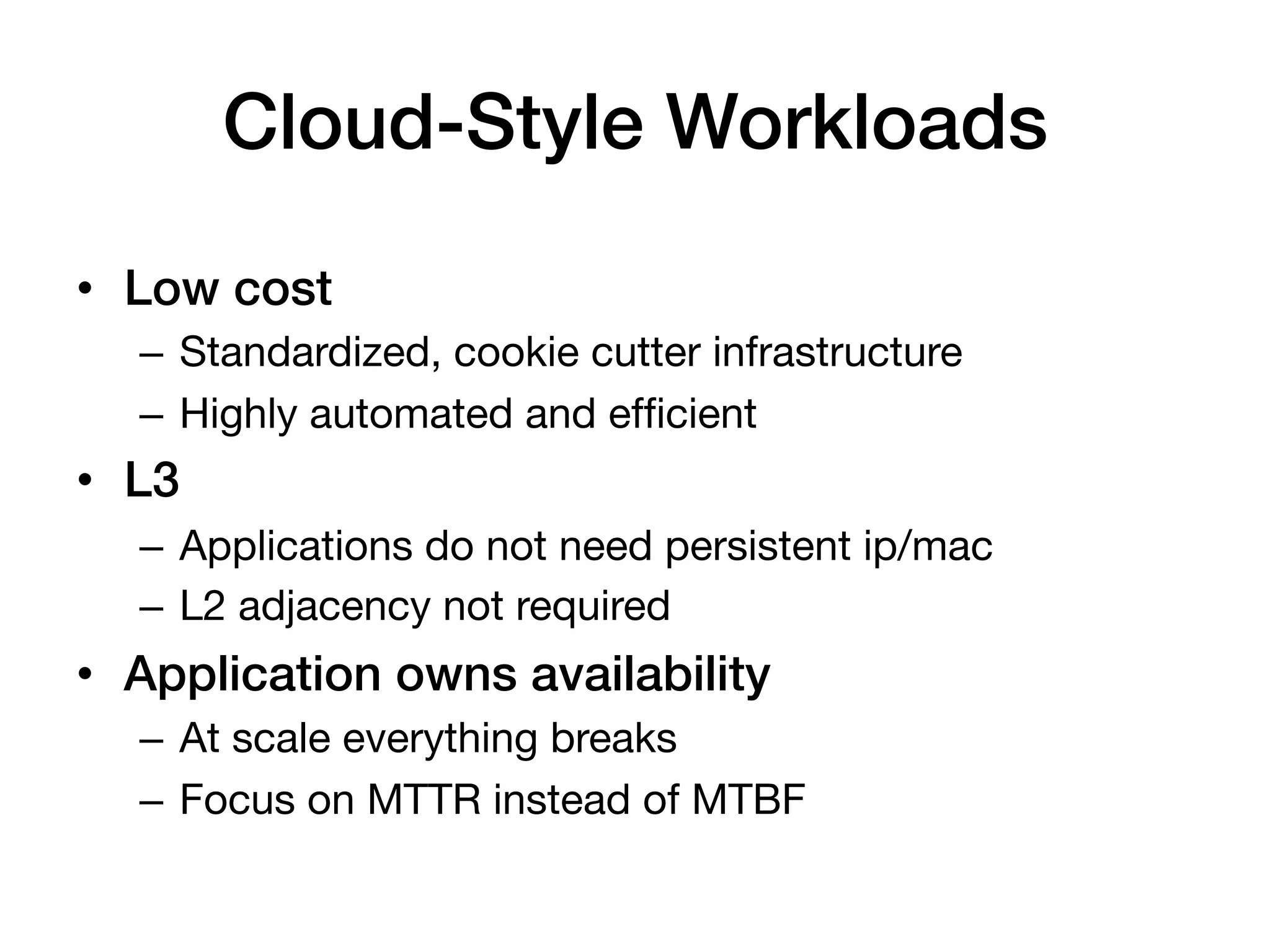
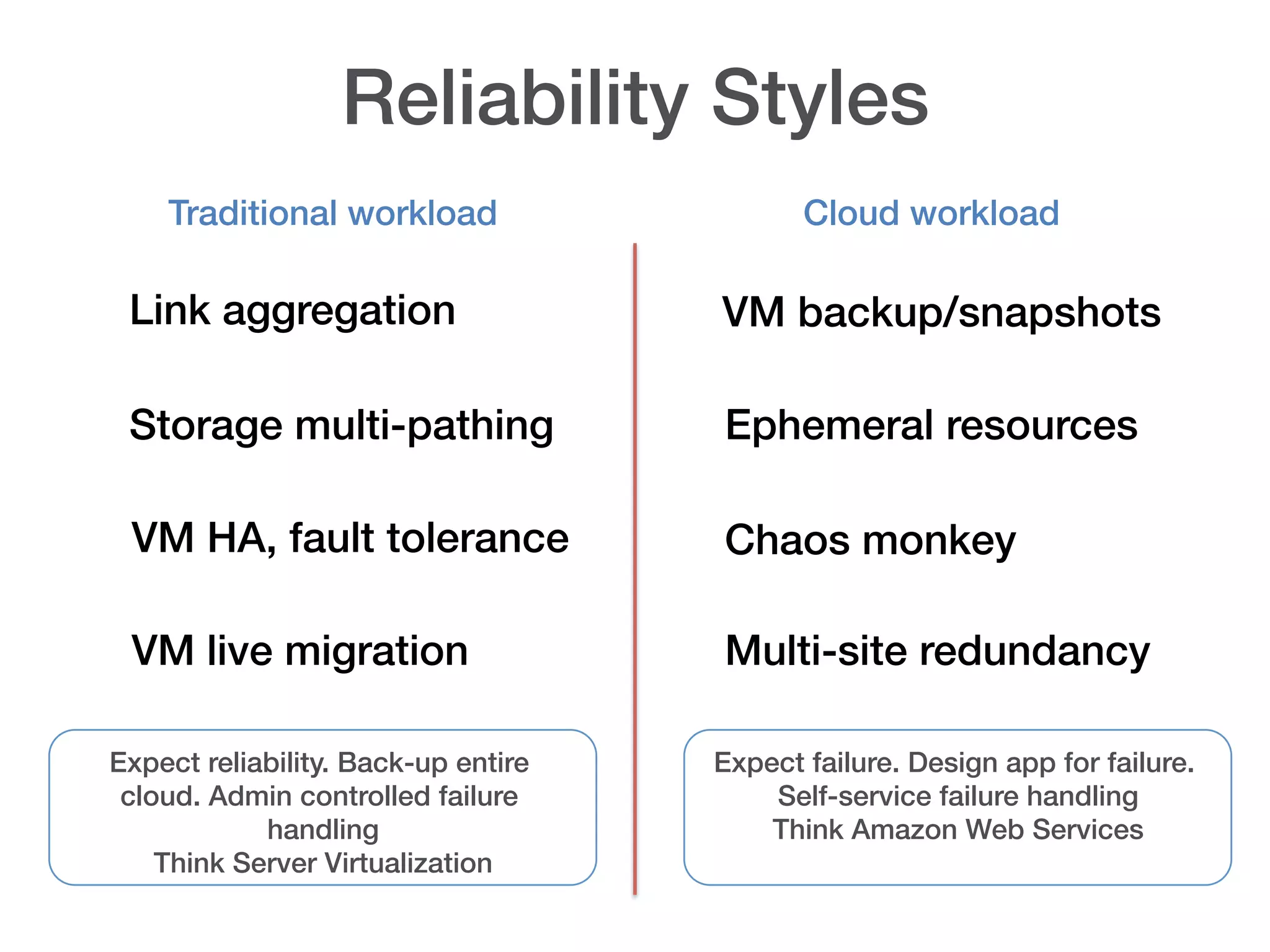
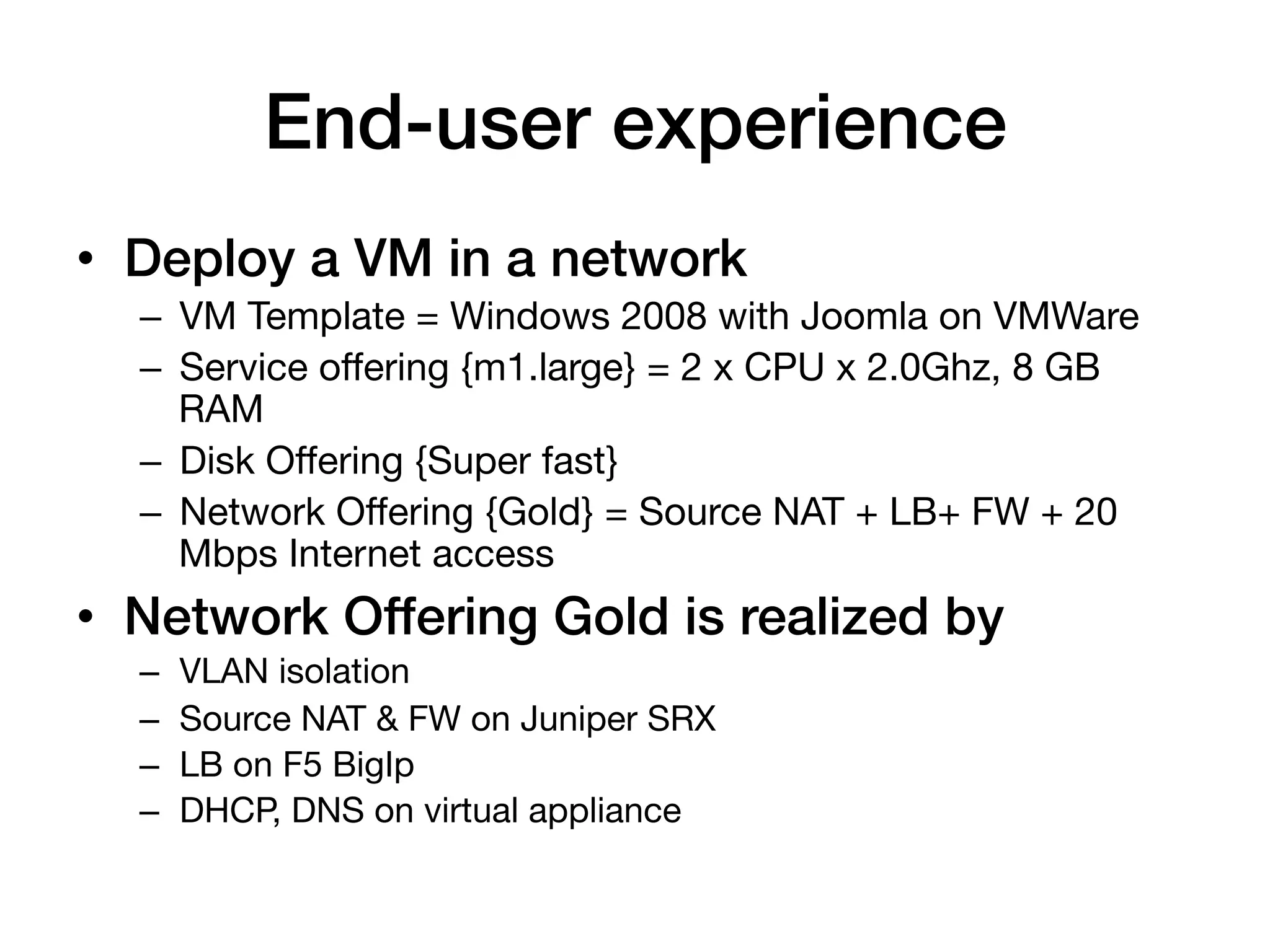
![Multi-tier virtual networking!
Internet!
!
Loadbalancer Virtual appliance/!
Hardware Devices!
(virtual or HW)!
Network Services!
• IPAM!
• DNS! Web VM
1!
• LB [intra]!
• S-2-S VPN!
• Static Routes! Web VM
• ACLs! 2!
• NAT, PF!
• FW [ingress & egress]!
Web VM
3!
Web VM
4!
Web subnet !
10.1.1.0/24! VLAN 101](https://image.slidesharecdn.com/networkinginthecloudagelisa2012-121214005629-phpapp01/75/Networking-in-the-Cloud-Age-LISA-2012-Tutorial-58-2048.jpg)
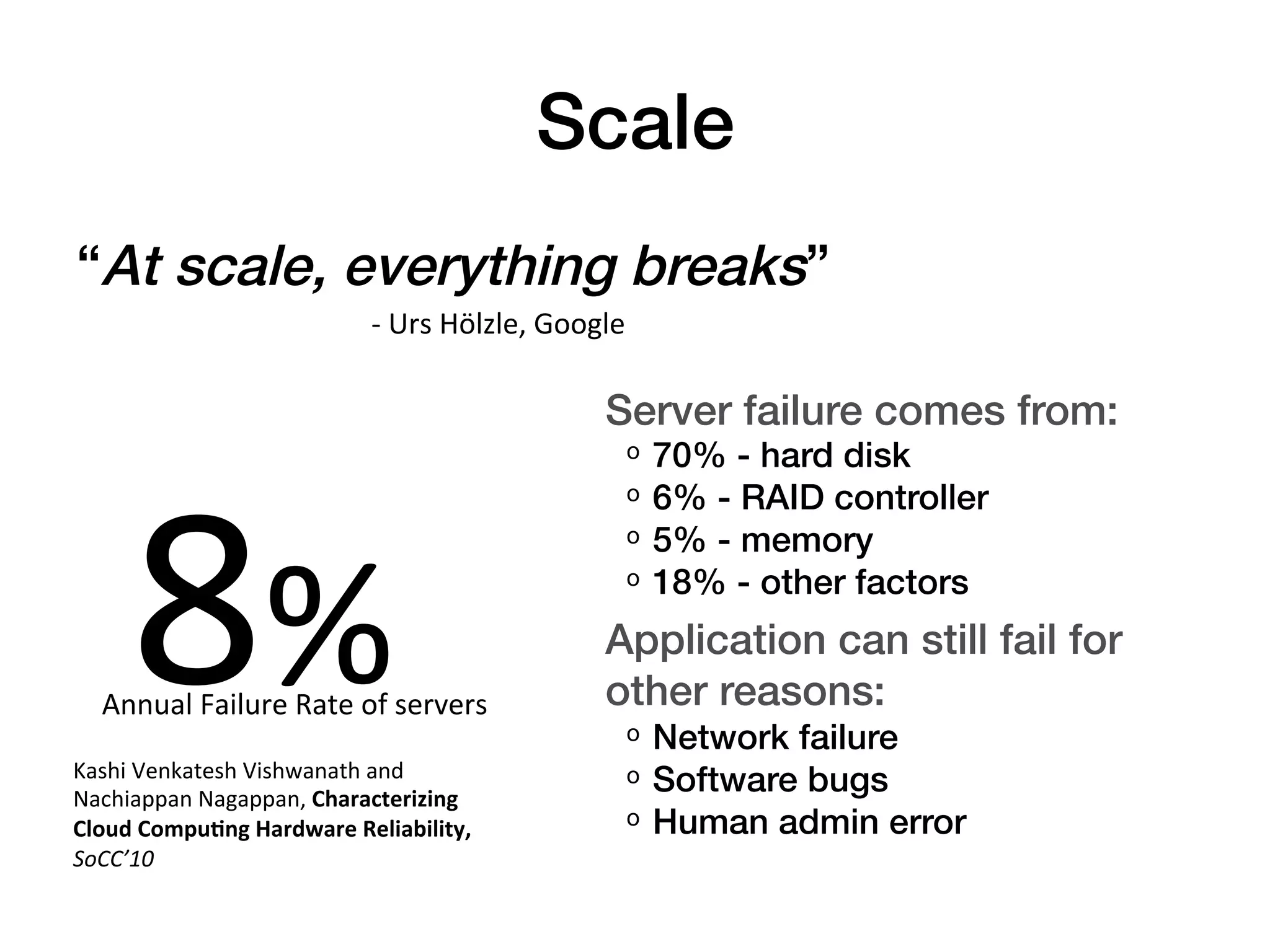
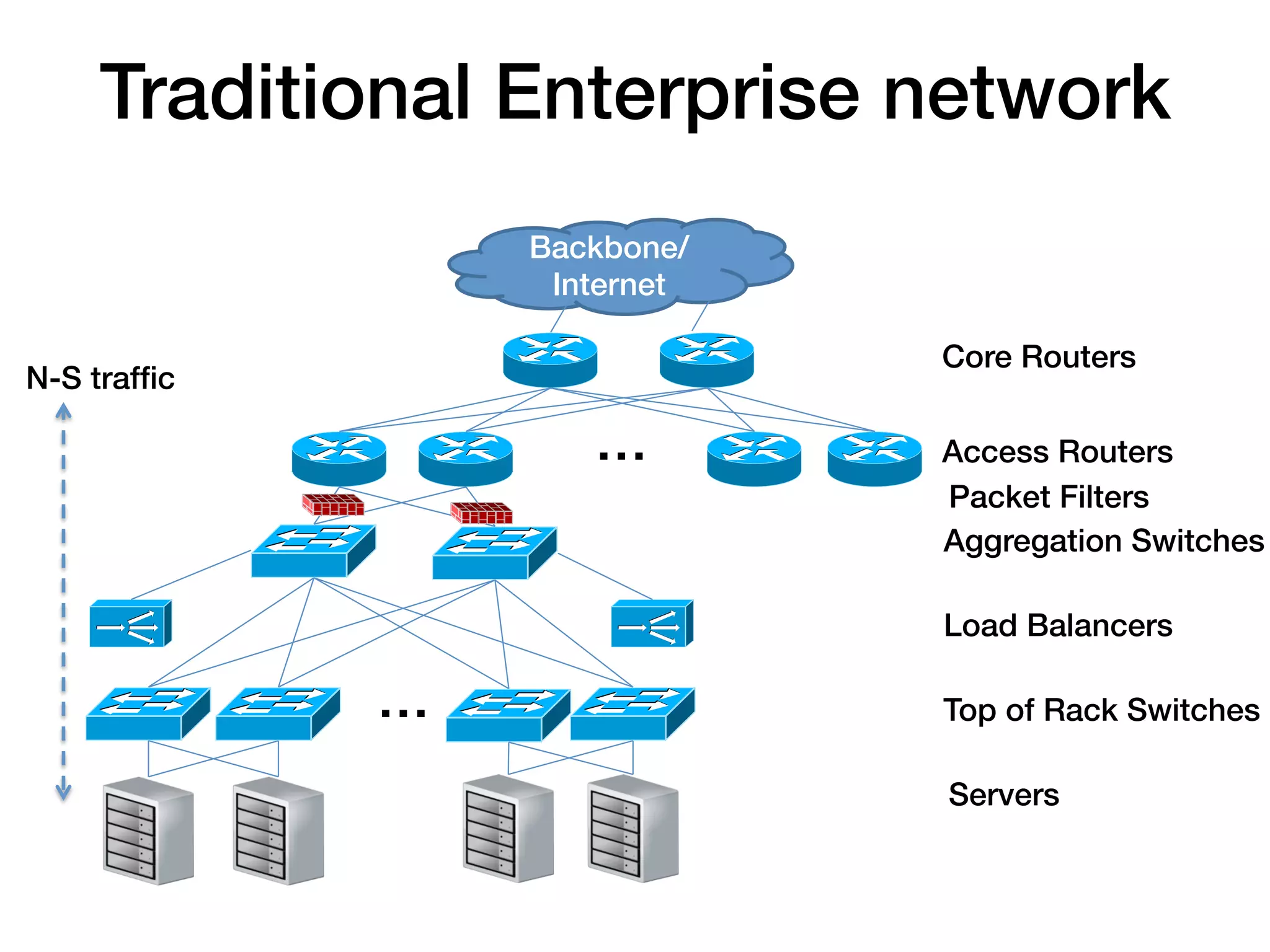
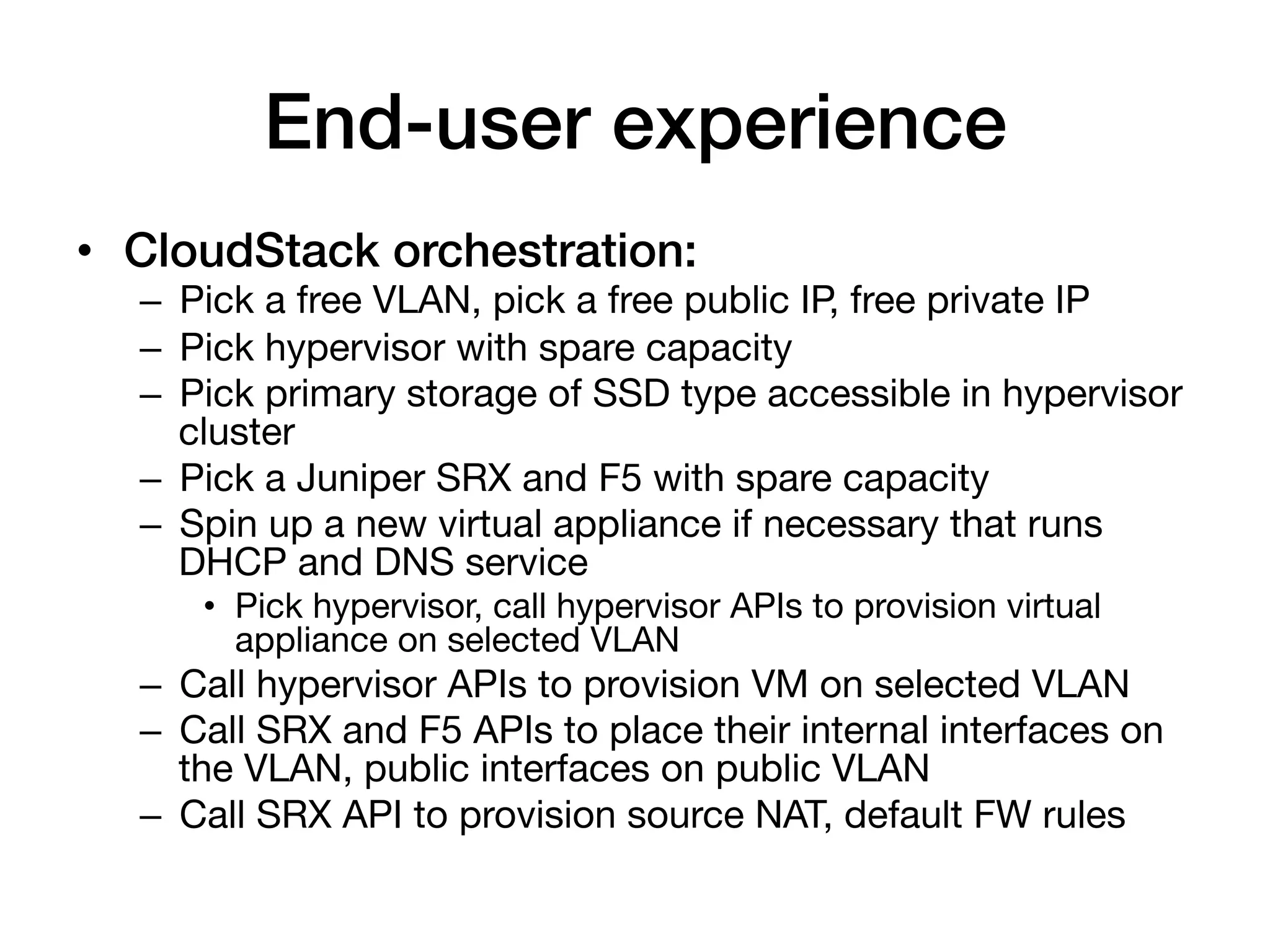
![Multi-tier virtual networking!
Internet!
!
Loadbalancer Virtual appliance/!
Hardware Devices!
(virtual or HW)!
Network Services!
App VM
• IPAM!
1!
• DNS! Web VM
1!
• LB [intra]!
• S-2-S VPN! App VM
• Static Routes! Web VM 2! VLAN 2724
• ACLs! 2!
• NAT, PF!
• FW [ingress & egress]! VLAN 353
Web VM DB VM
• BGP! 3! 1!
Web VM
4!
Web subnet ! App subnet DB Subnet!
10.1.1.0/24! VLAN 101
10.1.2.0/24! 10.1.3.0/24!](https://image.slidesharecdn.com/networkinginthecloudagelisa2012-121214005629-phpapp01/75/Networking-in-the-Cloud-Age-LISA-2012-Tutorial-59-2048.jpg)
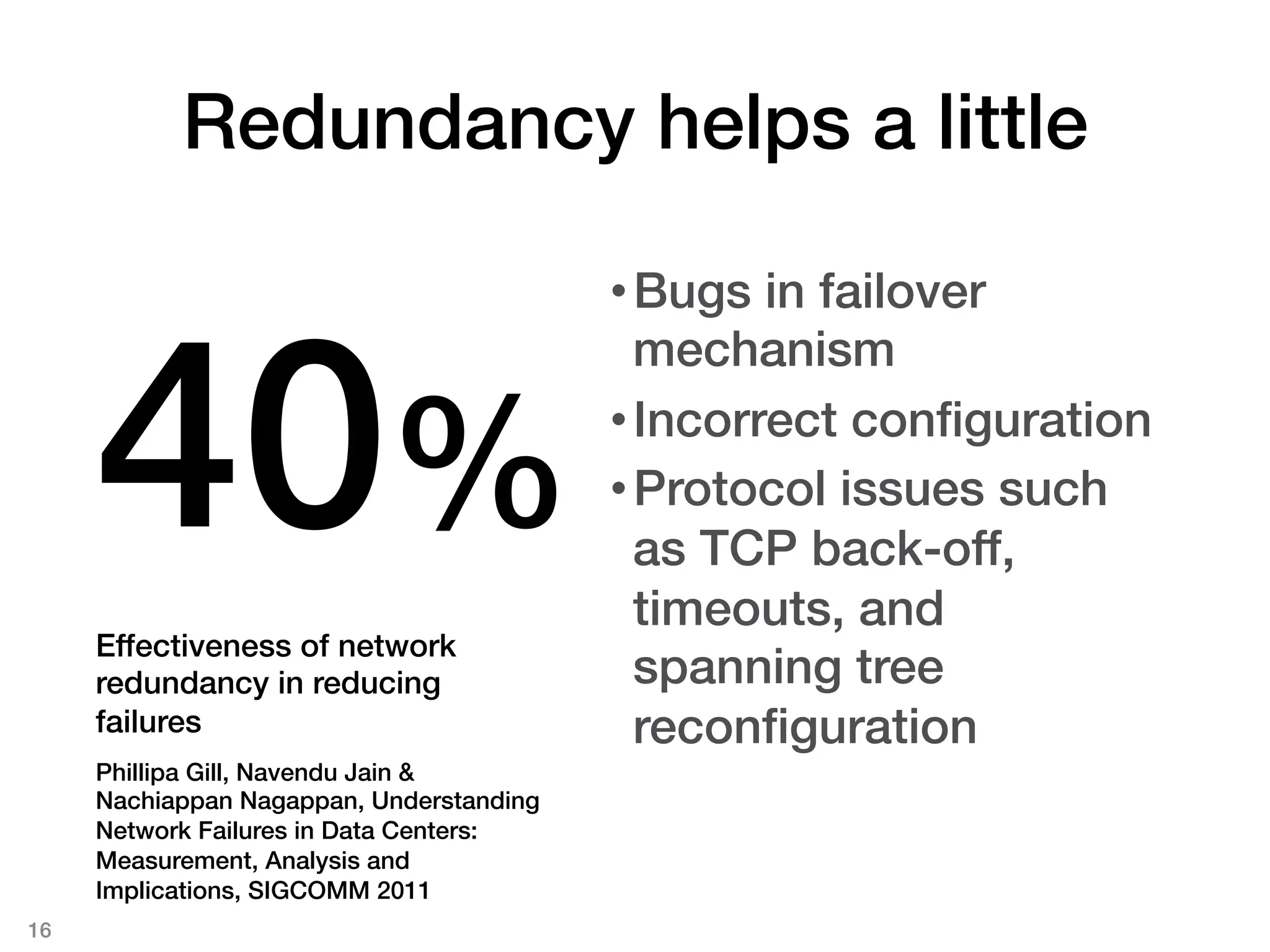
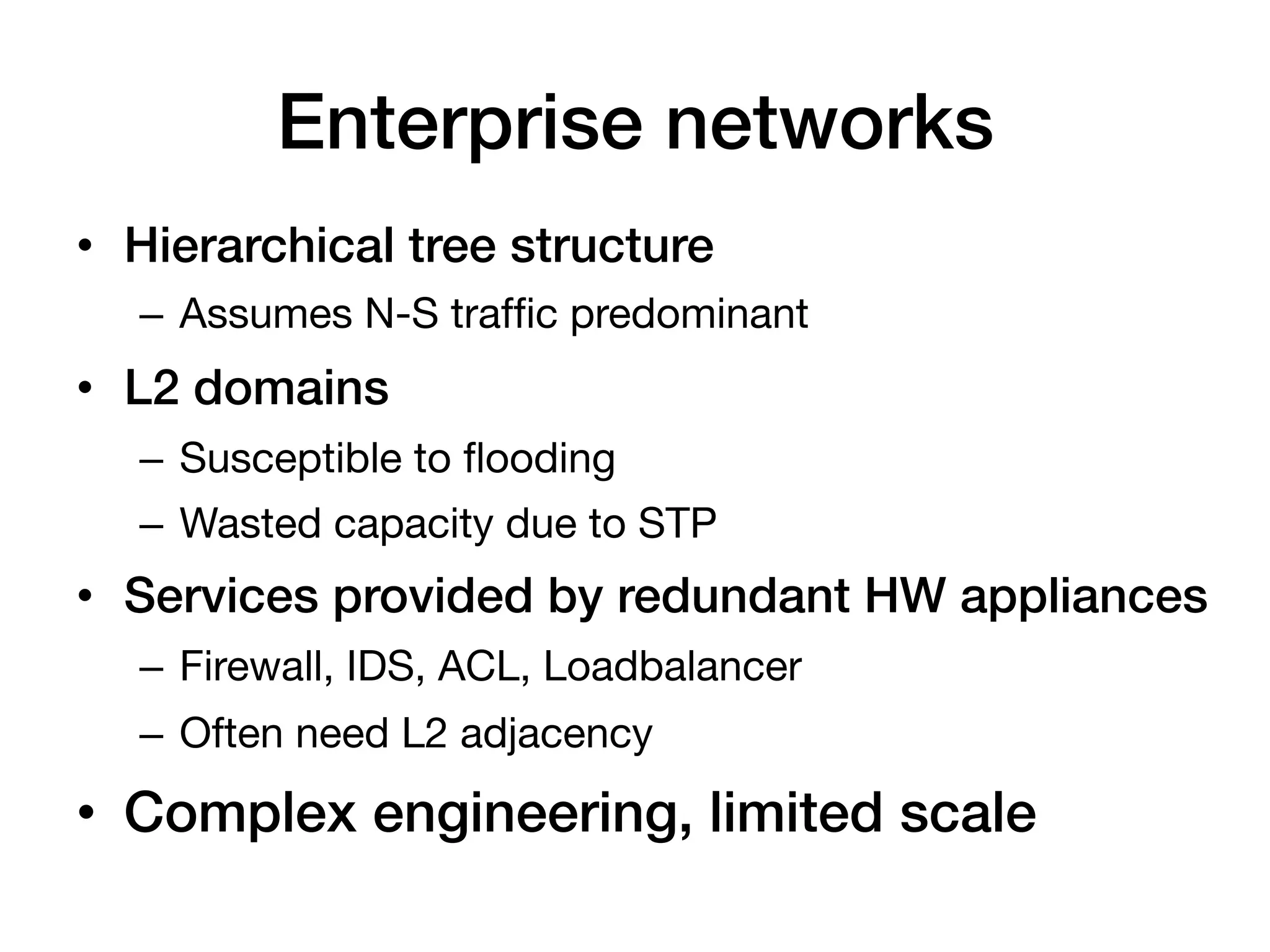
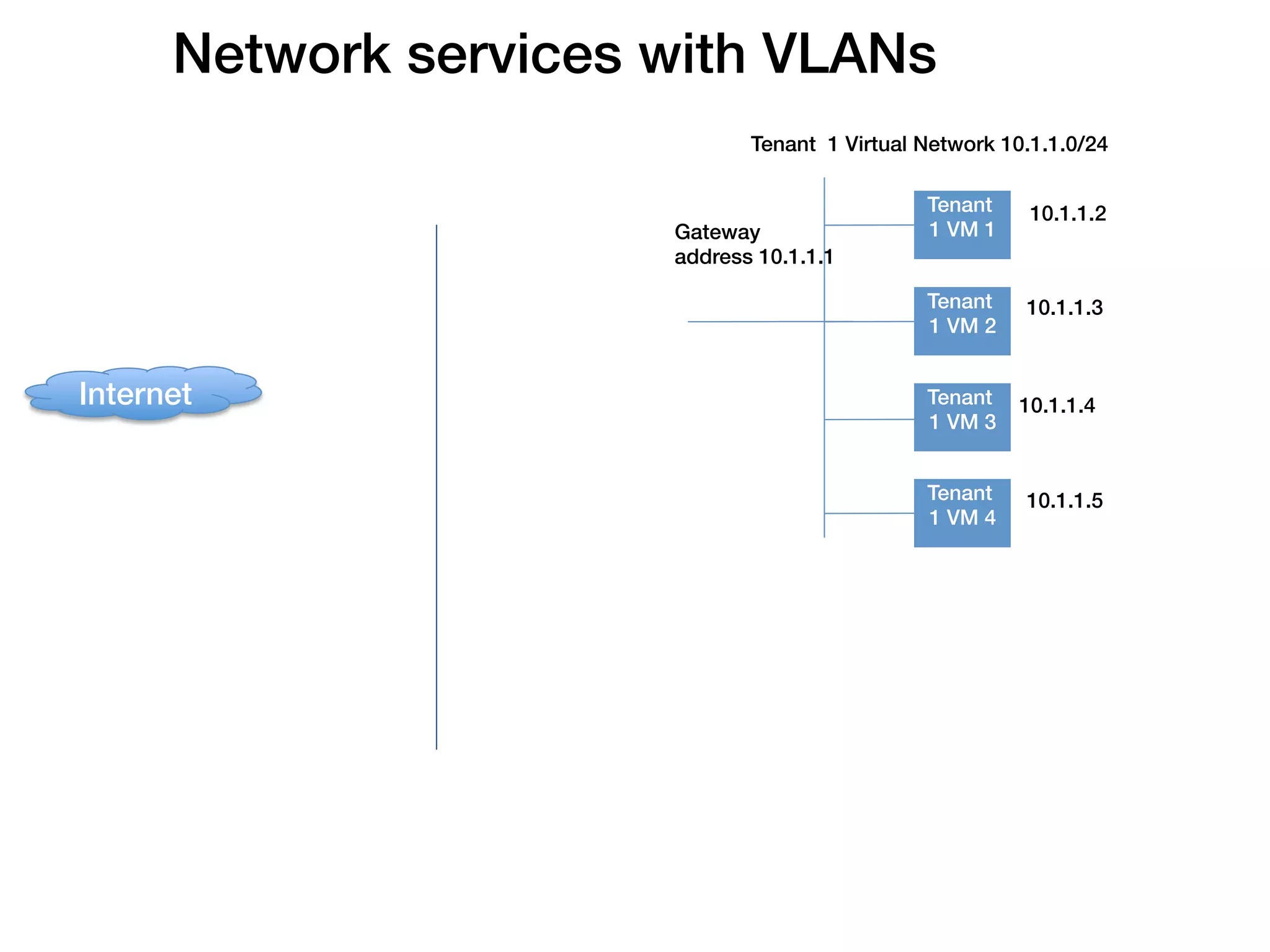
![Multi-tier virtual networking!
Internet!
IPSec or SSL site-to-site VPN!
! Custome
Loadbalancer Virtual appliance/!
r!
Hardware Devices!
(virtual or HW)! Premises!
MPLS VLAN!
Network Services!
App VM
• IPAM!
1!
• DNS! Web VM
1!
• LB [intra]!
• S-2-S VPN! App VM
• Static Routes! Web VM 2! VLAN 2724
• ACLs! 2!
• NAT, PF!
• FW [ingress & egress]! VLAN 353
Web VM DB VM
• BGP! 3! 1!
Web VM
4!
Web subnet ! App subnet DB Subnet!
10.1.1.0/24! VLAN 101
10.1.2.0/24! 10.1.3.0/24!](https://image.slidesharecdn.com/networkinginthecloudagelisa2012-121214005629-phpapp01/75/Networking-in-the-Cloud-Age-LISA-2012-Tutorial-60-2048.jpg)
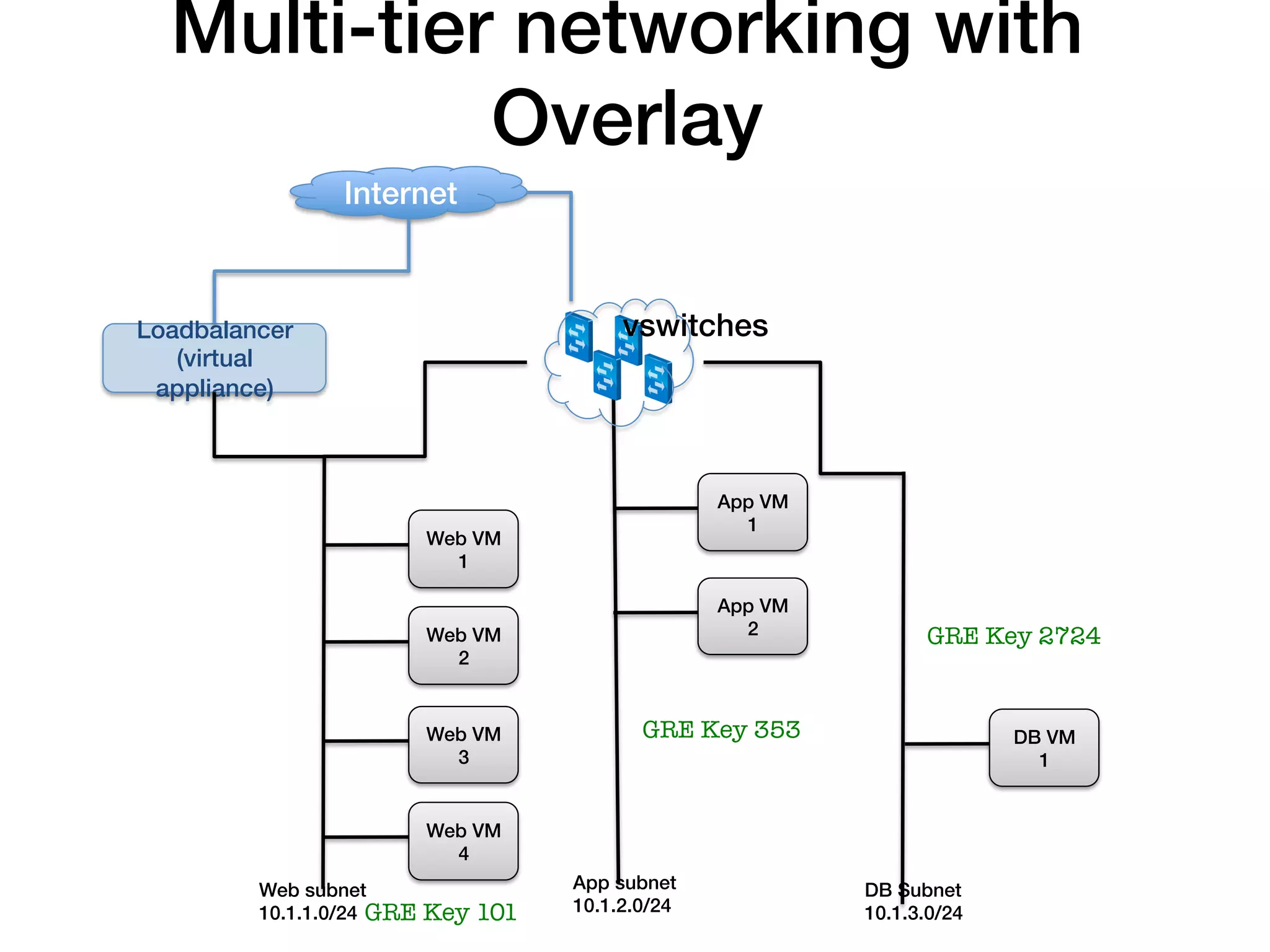
![Multi-tier networking with
Overlay!
Internet!
IPSec or SSL site-to-site VPN!
Loadbalancer ! Custome
(virtual Virtual Router! r!
Premises!
appliance)!
MPLS VLAN!
Network Services! App VM
• IPAM! Web VM
1!
• DNS! 1!
• LB [intra]!
App VM
• S-2-S VPN! 2!
• Static Routes! Web VM GRE Key 2724
2!
• ACLs!
• NAT, PF!
• FW [ingress & egress]! Web VM GRE Key 353
DB VM
• BGP! 3! 1!
Web VM
4!
Web subnet ! App subnet DB Subnet!
10.1.1.0/24! GRE Key 101
10.1.2.0/24! 10.1.3.0/24!](https://image.slidesharecdn.com/networkinginthecloudagelisa2012-121214005629-phpapp01/75/Networking-in-the-Cloud-Age-LISA-2012-Tutorial-61-2048.jpg)