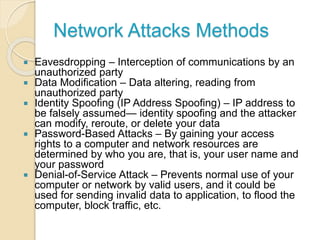
The document discusses network security, emphasizing its importance as more individuals engage with digital networks. It covers fundamental concepts, types of network security methods, authentication processes, and common network attacks, along with the advantages and challenges of implementing security measures. The conclusion notes the ongoing need for improved security technologies in response to evolving threats as internet usage expands.