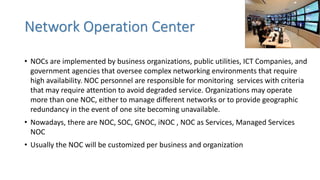
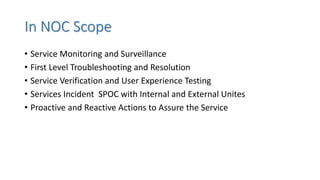
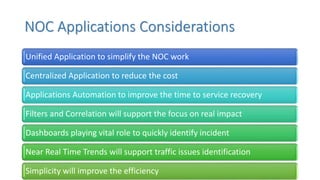
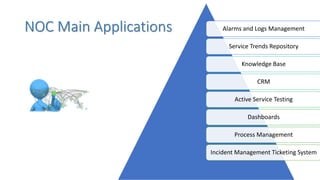
The document outlines the role and essential functions of a Network Operations Center (NOC), including service monitoring, incident management, and knowledge management. It emphasizes the importance of customized applications, training, communication channels, and performance metrics for efficient network management. Additionally, it highlights the need for disaster recovery planning and continuous service improvement through structured processes and collaboration with internal and external stakeholders.