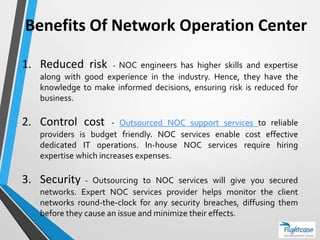
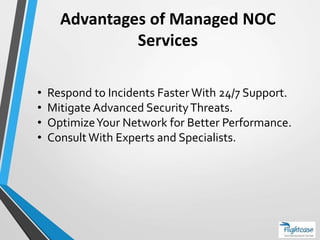
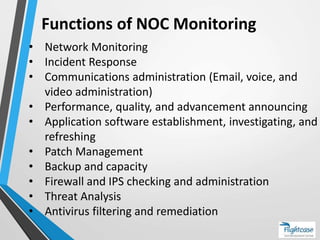
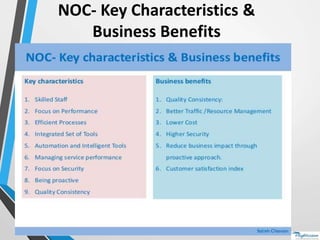
A Network Operations Center (NOC) is a centralized location for monitoring and managing networks, ensuring efficient troubleshooting of IT and network issues. Outsourcing NOC services offers benefits such as reduced risk through expert monitoring, cost control, and enhanced security with round-the-clock support. Key functions include network monitoring, incident response, and performance optimization, supported by specialized professionals.