Network & Internet Working Devices
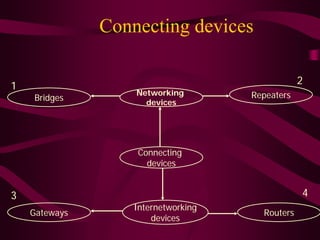
- 1. Connecting devices 2 1 Networking Repeaters Bridges devices Connecting devices 3 4 Internetworking Gateways Routers devices
- 2. Connection devices with the OSI model 7 layers of OSI model All 7 layers 1 Layer Physical data link, Physical + Physical Network Layers Datalink layer 3 layers 2 layers Gateway Router Bridge Repeater
- 3. A repeater in the OSI model Device A Device B Repeater Subnet R Subnet 7 7 OSI LAYERS OSI LAYERS 6 6 5 5 4 4 3 3 2 2 Repeater extends the physical 1 length of a network 1 R
- 4. A repeater Frame Repeater B A D C
- 5. Repeater Functions Regenerate Corrupted Regenerates Corrupted Signal Repeater Corrupted Signal Regenerate Corrupted
- 6. Bridge to connect two LANs LAN 1 LAN 2 A A HUB HUB B B Bridge C C D D
- 7. A Bridge in the OSI model Device A Device B Repeater Subnet R Subnet 7 7 OSI LAYERS OSI LAYERS 6 6 5 5 4 4 3 3 2 2 1 1 1 Data link 2 Physical
- 8. Functions of a Bridge Seg ment 1 Packet A B Bridge e nt 2 Se gm C Packet D
- 9. Three types of bridges I. Simple bridges I. Learning bridges I. Multiport bridges
- 10. Simple bridge - 1 • Primitive type • Least expensive • Links two segments • Contains a table that lists the addresses of all the stations in each of them • Addresses are to be entered manually • Before functioning the operator must set down & program the addresses of every station
- 11. Use of routers to connect LANs Server Device 4 Device 1 Token Ethernet Server ring hub hub Device 2 Device 5 Bridge Device 3 Device 6
- 12. A router in the OSI Model Device Repeater Device A B Network R Network 7 7 OSI LAYERS OSI LAYERS 6 6 5 5 4 4 3 3 2 2 Network 1 1 Data link Physical
- 13. Routers in an internet Router Network B Network A Router Router Router Network E Network C Router Router Network D
- 14. Route for the packets from network A to network D Network B Network C Network A Network D Network Q
- 15. Use of gateways (connecting LANs and Mainframe) Front- end Server Device 4 Main frame Device 1 Server Token Ethernet ring hub hub Device 2 Device 5 Device 3 D i 6
- 16. A Gateway in the OSI model Device Device Network Gateway Network A B 7 7 7 OSI LAYERS OSI LAYERS 6 6 6 5 5 5 4 4 4 3 3 3 2 2 2 1 1 1
- 17. Routing table An inter net 05 1 _ 08 1 _ 24 1 _ 25 1 _ 36 1 _ LAN5 LA R2 N8 LAN36 LAN53 R1 10 1 _ R5 08 1 _ R3 LA N 24 36 1 _ 53 1 _ LAN10 LAN18 R4 R5 18 1 _ 18 1 _ 10 1 _ 24 1 _
- 18. Updating the table R,’s old table 05 1 _ 24 1 _ 05 1 _ 36 1 _ 05 2 R2 05 1 _ 08 2 R2 08 2 R2 Received from R2 After adjustment 24 1 _ 24 1 _ 08 1 _ + one 08 2 R2 36 1 _ 36 1 _ 05 1 _ hop 05 2 R2 Combined R,’s new tabl
- 19. Updating the table R,’s old table 10 1 _ 08 1 _ 08 1 _ 10 1 _ 08 1 _ Received from R2 After adjustment 10 2 R4 10 1 _ 10 2 R4 18 2 R4 18 1 _ + one 18 2 R4 10 1 _ hop 10 2 R4 Combined R,’s new tabl
- 21. Updated routing tables for R1, R5 Routing table & R6 05 1 08 1 _ 08 2 R2 25 1 _ 24 1 _ 36 1 _ LAN5 LA R2 N8 LAN36 LAN53 R5 08 1 _ R1 10 1_ R3 18 2 R4 LA 05 2R1 N 24 08 3 R1 24 2R1 36 1_ 53 1_ LAN10 LAN18 R4 R5 18 1 _ 18 1 _ 10 1 _ 24 1 _
- 22. Routing table Final routing tables 05 1 08 1 _ 08 2 R2 25 1 _ 24 1 _ 36 1 _ LAN5 LA R2 N8 LAN36 LAN53 R5 08 1 _ R1 10 1_ R3 18 2 R4 LA 05 2R1 N 24 08 3 R1 24 2R1 36 1_ 53 1_ LAN10 LAN18 R4 R5 18 1 _ 18 1 _ 10 1 _ 24 1 _
- 23. Cost in link state routing Routing table 05 1 _ 08 1 _ 24 1 _ 25 1 _ 36 1 _ LAN5 LA R2 N8 LAN36 LAN53 R1 10 1 _ R5 08 1 _ R3 LA N 24 36 1 _ 53 1 _ LAN10 LAN18 R4 R5 18 1 _ 18 1 _ 10 1 _ 24 1 _
- 24. The flooding of R2 ‘s LSP Routing table 05 1 _ 08 1 _ 24 1 _ 25 1 _ 36 1 _ LAN5 LA R2 N8 LAN36 LAN53 R1 10 1 _ R5 08 1 _ R3 LA N 24 36 1 _ 53 1 _ LAN10 LAN18 R4 R5 18 1 _ 18 1 _ 10 1 _ 24 1 _
- 25. The flooding of R2 ‘s LSP Routing table 05 1 _ 08 1 _ 24 1 _ 25 1 _ 36 1 _ LAN5 LA R2 N8 LAN36 LAN53 R1 10 1 _ R5 08 1 _ R3 LA N 24 36 1 _ 53 1 _ LAN10 LAN18 R4 R5 18 1 _ 18 1 _ 10 1 _ 24 1 _
- 26. Costs in the Dijkstra algorithm Routing table 05 1 _ 08 1 _ 24 1 _ 25 1 _ 36 1 _ LAN5 LA R2 N8 LAN36 LAN53 R1 10 1 _ R5 08 1 _ R3 LA N 24 36 1 _ 53 1 _ LAN10 LAN18 R4 R5 18 1 _ 18 1 _ 10 1 _ 24 1 _
- 27. Networks 5, 36, 24 added LAN5 1 LAN36 R1 3 Root LAN24 2
- 28. (ii) R2 added ; 5 permanent LAN5 R2 1 LAN36 R1 3 Root LAN24 2
- 29. (iii) R2 permanent, 55 added LAN5 R2 1 3 LAN36 R1 3 LAN55 Root LAN24 2
- 30. (iv) 24 permanent, R5 added LAN5 R2 1 3 LAN55 R1 3 LAN36 Root LAN24 2 R5
- 31. (v) R5 permanent, 18 added LAN5 R2 1 3 LAN55 R1 3 LAN36 Root LAN24 2 R5 LAN18
- 32. Dijkstra algorithm 5 R2 55 LAN36 LAN53 R1 R5 R3 2 3 LA N 24 10 LAN18 R4 9 R5
- 33. “Like” us on Facebook: p // / http://www.facebook.com/welearnindia “Follow” us on Twitter: http://twitter.com/WeLearnIndia http://twitter com/WeLearnIndia Watch informative videos on Youtube: http://www.youtube.com/WelingkarDLP
