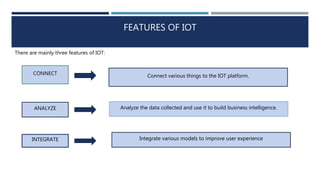
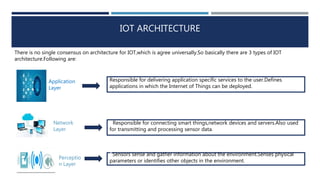
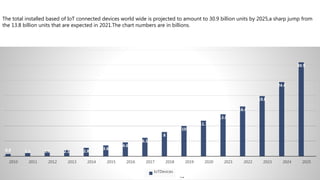
The document discusses Internet of Things (IoT). It defines IoT as a platform that connects everyday devices with electronics, software, or sensors to the internet. This allows for the collection and sharing of data between connected things. IoT has benefits like efficient resource utilization, minimizing human effort, and saving time. It also enables the development of artificial intelligence. The architecture of IoT generally includes application, network, and perception layers. IoT has applications in smart environments, transportation, supply chain/logistics, energy conservation, agriculture, social/entertainment, health, and home automation. While IoT is still facing challenges in Bangladesh, its use is growing and has good potential.