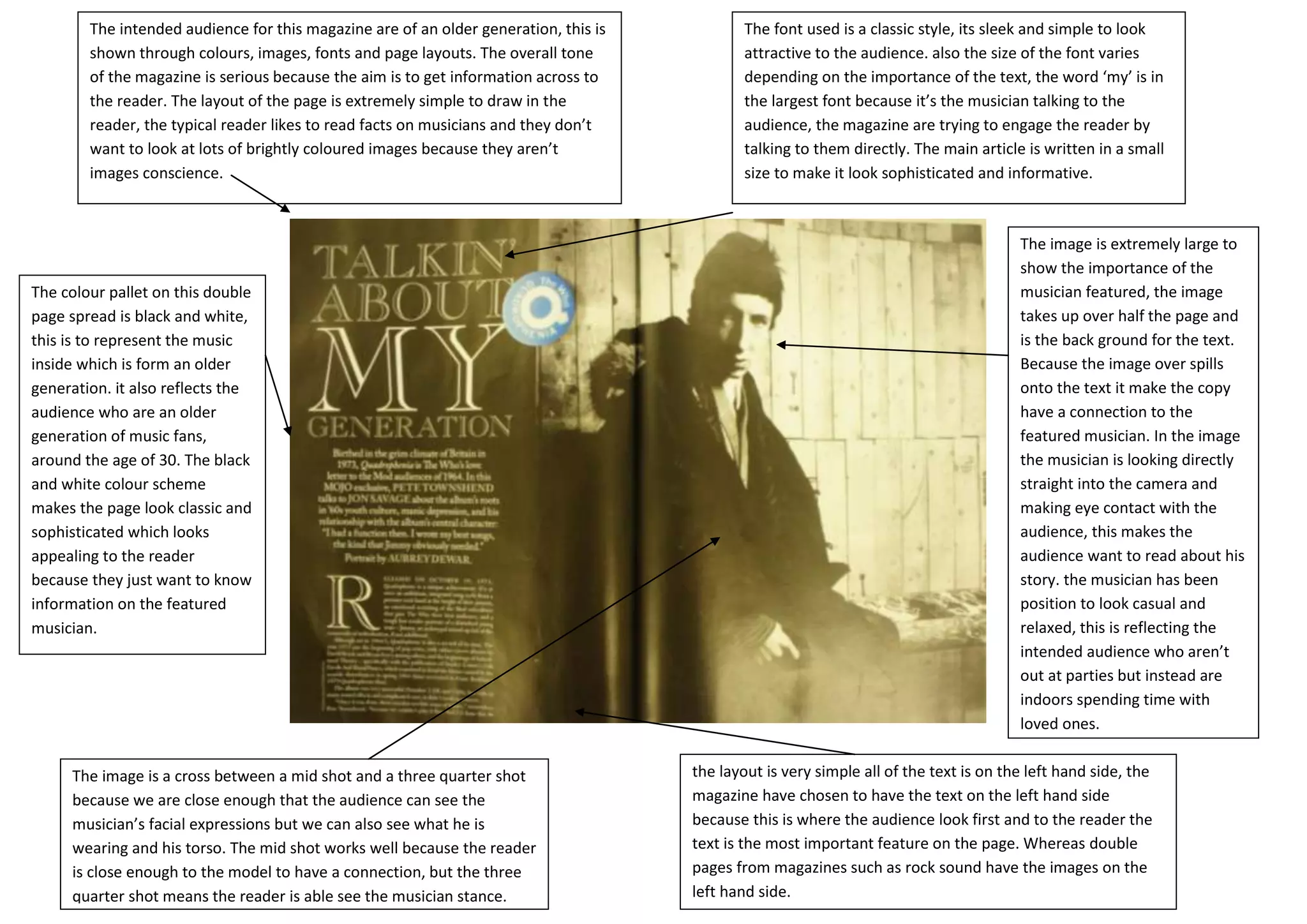
The magazine is aimed at an older generation of music fans. It uses a classic font style and layout with simple images to appeal to its mature audience. The overall tone is serious, aiming to inform readers about musicians. Large images and fonts are used for important elements, while other text is smaller to seem sophisticated.