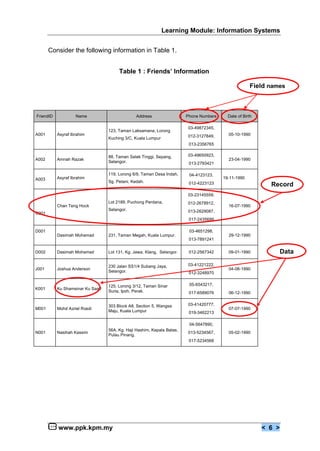
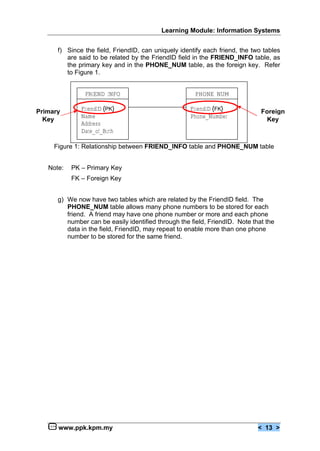
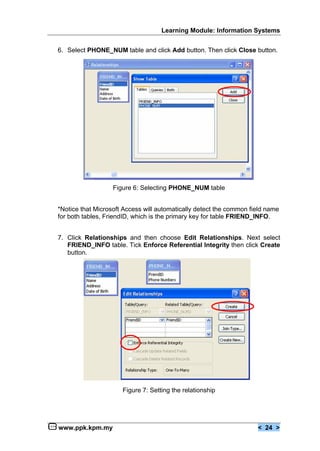
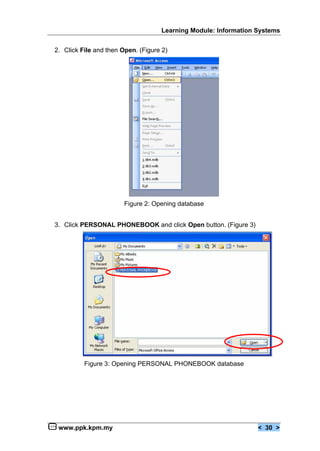
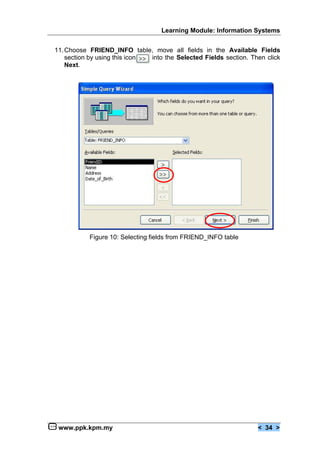
The document describes the steps to develop a database project. It includes identifying the project requirements, classifying the data into seldom and frequently changed types, and designing two database tables - one for friend information (seldom changed) and one for phone numbers (frequently changed). The tables are designed to store data about friends and their phone numbers, with the Friend ID field used to uniquely identify each friend.