This document summarizes research on simulating and modeling mobile computing protocols. It discusses issues like address binding, network infrastructure for mobility, and TCP connection management in mobile environments. It then reviews several papers that use simulation to evaluate performance of mobile protocols. One paper models handoff management algorithms in urban areas. Another compares the performance of Mobile IP and a multicast-based approach. A third evaluates Mobile IP and Route Optimization Mobile IP in wireless networks. The document concludes with discussing analytical modeling of mobility in cellular networks.


![Simulation and modeling of mobile protocols
Abstract
Mobile computing protocols are becoming one of the most important issues in state-of-the-art
technologies. In this paper we will provide important issues in terms of modeling and simulation of mobile
protocols. First, the survey discusses the theoretical issues in mobile or nomadic computing environment,
afterwards some performance measurements papers are explained, they show simulations done to routing
and hand-off optimizations. Finally, an analytical point of view is presented using queuing theory analysis
in pico-cell networks.
Introduction - Nomadic computing over the internet
There are several answers to the problem of mobility, mobile-IP is one of them, but there are other
frameworks found for instance in [Li98], where an universal personal computing (UPC) paradigm is
presented. The term nomadicity refers to the system support needed to provide a rich set of computing and
communication capabilities and services for mobile users in a transparent, integrated and convenient form
as they move between different places. The desired characteristics for nomadicity include independence of
location, motion, computing platform, communication device, and communication bandwidth, and the
widespread availability of access to remote files, systems and services.
There are some other standards for nomadicity, such as the Universal Personal
Telecommunication, studied by the CCITT (ITU), which is based on the intelligent network architecture
and focused on extending point-to-point connection-oriented services provided by the public switched
telephone network to mobile users. In addition to those efforts, the Telecommunications Information
Networking Architecture (TINA) has defined and validated an open architecture for telecommunications
systems providing personal mobility functions. Both frameworks, as explained before are designed to be
applicable in the Intelligent Network (IN) and Broadband ISDN (Integrated Services Digital Network).
The UPC paradigm presented by [Li98] follows these design issues:
• Only regular users of the internet are considered, each user should belong to a home network, a place
where the user is properly registered.
• Each mobile user has a service profile at her home network where all the services are defined.
• Services and terminal control have to be logically separated.
• Each user and her current terminal has to be identified by the Logical User Identifier (LIU) and Logical
Terminal Identifier (LTI), respectively, that are independent of each others as well as their curretn
location.
3](https://image.slidesharecdn.com/mobilesurvey-100731090639-phpapp02/75/Mobile-Survey-on-Simulation-for-Networks-3-2048.jpg)

![TCP connection management
Another important issue is the TCP connection management. TCP utilizes the three way
handshake protocol, with a sequence of ACK – SYN – ACK, we have to recall the state machine for the
TCP handshake defined in the TCP protocol.. In [Li98] is proposed three different solutions for mobile
communication in TCP links. a) a Transparent Solution b) The TCP layer solution c) the middleware layer
solution.
In the Transparent Solution, the UHA has two finite states machines, it establishes a
communication link using TCP between the source and then initiates a communication link to the Mobile
Terminal (MT) or host. In fact [Li98] point out that the TCP connection between the UHA and the MT is
supported by mobile-ip. However, movements of the MT will require routing optimization and cache
validation techniques.
Meanwhile the TCP Layer Solution , the source request to set up a connection to the UAH using
an IP address of the MT. The UHA transfers the message to the MT, the message is tunneled and the MT
piggyback the source. The TCP layer of the source is modified with the new IP address piggybacked by the
MT. The main problem with this solution is the lack of transparency between the source and the
destination, and this modification should be taken into consideration by the IETF which is not feasible.
Finally the Middleware Layer Solution, in which the middleware is aware of the mobility of the
MT at the UHA, therefore when the MT is moved and the directory service is requested the middleware
should provide the source of information with updated addresses. This is similar to the TCP layer solution
but it can be implemented in alignment with OSI principles.
5](https://image.slidesharecdn.com/mobilesurvey-100731090639-phpapp02/75/Mobile-Survey-on-Simulation-for-Networks-5-2048.jpg)
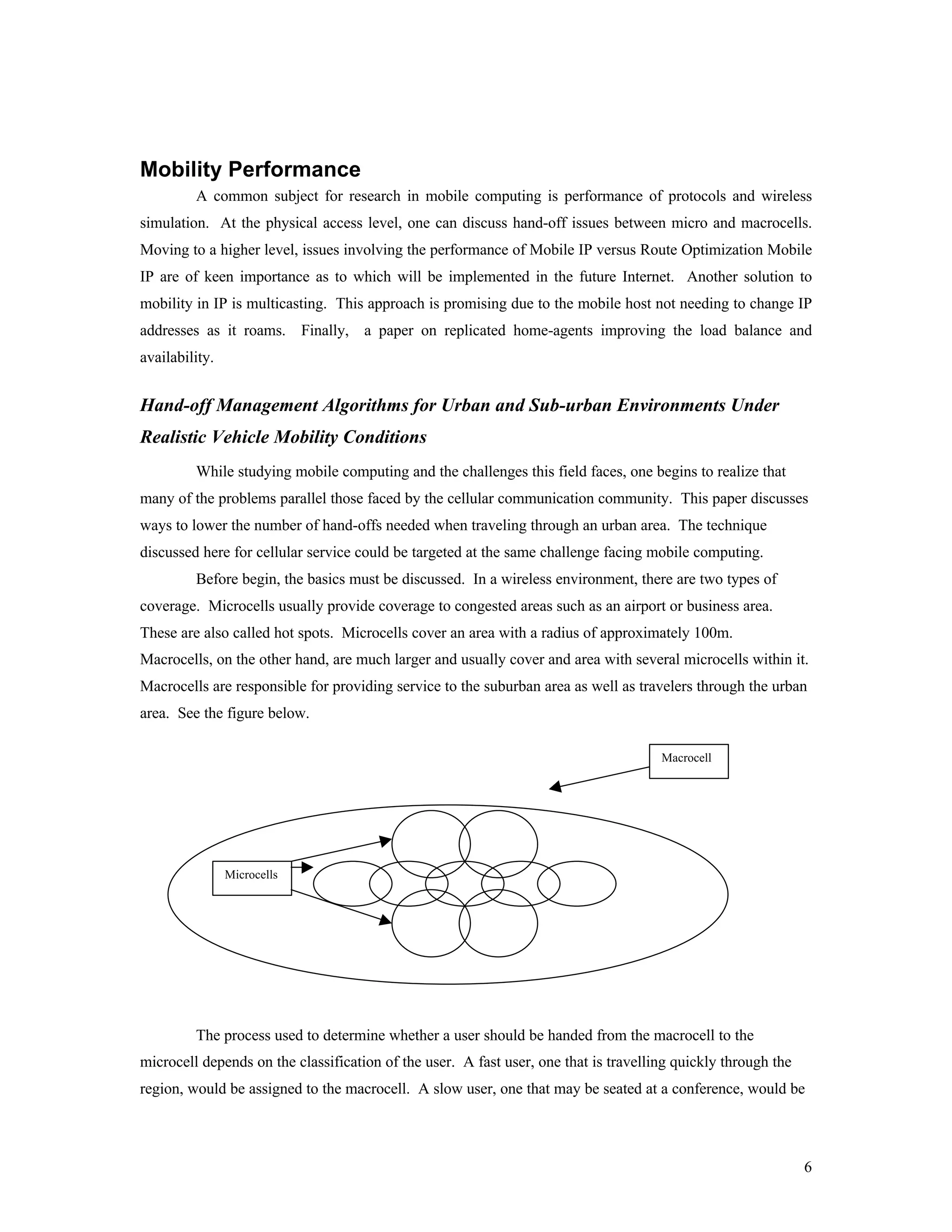
![assigned to a microcell. This scheme works well except when a user is travelling through the region but is
slowed considerably by a congested area with many traffic lights and is classified as slow. Under the
current approach, the user would experience many hand-offs from one macrocell to the other. This method
is grossly inefficient and increases the chance of the user becoming disconnected.
Dr. Iera of the University of Reggio Calabrai, Italy [Iera08] purposed a solution to this problem.
A fast user connected to the macrocell is given a time bonus when he reaches the border of a microcell. If
the user travels through the microcell in time less than t_threshold, the user gets keeps 100% of the time
bonus for the next microcell. If the traveler takes time less than t_threshold + time bonus, but greater than
t_threshold, the time bonus us decreased for the next microcell. If the traveler takes more time than
t_threshold + time bonus, then the traveler is immediately assigned to a microcell.
In order to test this method, an elaborate traffic simulator was used in conjunction with the newly
purposed algorithm. Varying the number of traffic lights as well as varying the light duration set the
simulator parameters. Results were rather promising, as the average number of hand-offs per call
decreased from 4.25 to 2.8. This improvement came at a cost though, as the number of calls blocked and
forcefully terminated increased slightly with the new algorithm. This drawback can be contributed to the
overloading of the macrocell in this scheme. Since the drawback seems small compared to the
improvement in the number of hand-offs, this algorithm show promise for both the wireless communication
environment.
Performance of Transport Protocols over a Multicasting-based Architecture for
Internet Host Mobility
Although Mobile IP is gaining momentum towards being the standard, other solutions to mobility
have been researched. One of those possible solutions is to use IP multicasting. IP multicasting provides
packet delivery to location independent addresses and allows hosts to leave and join multicast groups.
These abilities parallel the needs of host mobility in the wireless network environment.
Jayanth Mysore and Vaduvur Bharghavan wrote this paper to explore the performance of Mobility
Support using Multicasting in IP (MSM-IP) versus the standard Mobile IP protocol. In order to provide
more complete results, both UDP and TCP were run over both MSM-IP and Mobile IP. Before discussing
the results, the reader needs to understand how MSM-IP and Mobile IP work.
In Mobile IP, each mobile host has its own home address. When the host moves from its home
subnetwork to another, the mobile host receives a care-of-address. The care-of-address is a dynamic
identifier that reflects the current point of attachment. When a correspondent host sends packets to the
mobile host, the packets first go to the home agent. The home agent, who knows the care-of-address,
forwards these packets to the mobile host. The mobile host, on the other hand, can send packets directly to
the correspondent host. Thus, the name triangle routing originated.
MSM-IP takes advantage of multicast routing to support host mobility. Multicast routing uses the
virtual interconnection of tunnels over the existing internet. The source of data packets is the root of the
7](https://image.slidesharecdn.com/mobilesurvey-100731090639-phpapp02/75/Mobile-Survey-on-Simulation-for-Networks-7-2048.jpg)

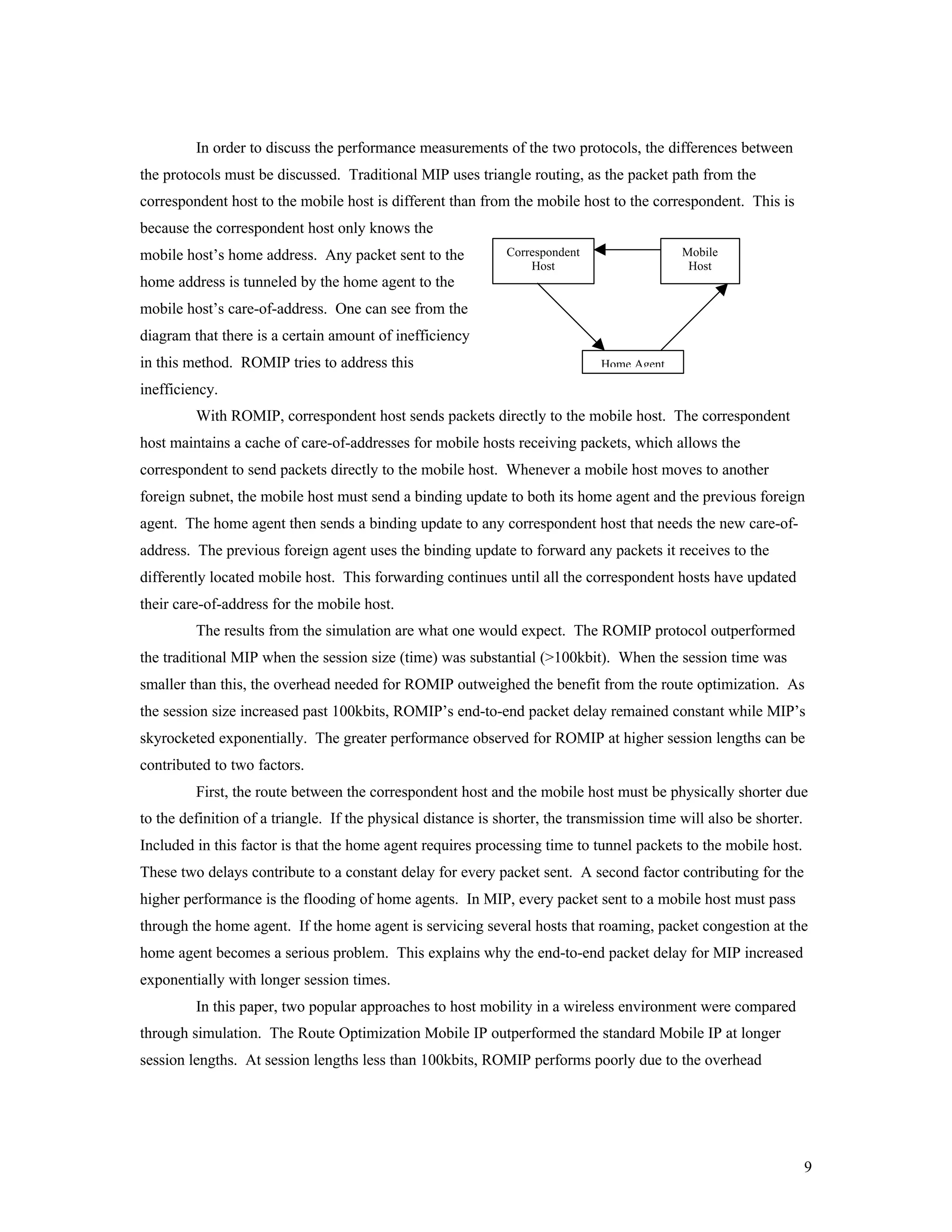
![required for route optimization. Any session exceeding 100Kbits allows the route optimization to be
beneficial. Since most sessions are longer than 100kbits, ROMIP seems to be the most attractive solution.
Replicated servers for ip-host mobility
In [Jue98], an extension for the mobile-ip protocol is presented in terms of the use of replicated
home-agents to handle multiple request for different mobile hosts groups. Replication will provide load-
balancing and avoid the single-point of failure provided by the home-agent.
We have to recall that in the mobile-ip architecture, a foreign agent and a home agent are required
for mobility. The mobile host moves to another network where the foreign agent expect to receive a
`registration packet in order to keep track of the mobile host and make the home-agent forward the
information to the proper destination.
The approach followed here consists in the use of not one, if not several replicated home-agents,
using different techniques to access and load balance between each other. The basic mobile-ip protocol has
evolved out of the efforts of the mobile IP working group and specifies mobility support under Ipv4. The
home-agent is usually a router or host in the mobile host’s home network which maintain mobility bindings
(a permanent IP address to a temporary IP address translation) for the mobile host. Meanwhile, the foreign
agent may be a router or host in the network where the mobile host is visiting, and it provides the mobile
host with a temporary IP address. If the number of available IP addresses in the foreign network is limited,
then the foreign agent may act as a proxy server for the mobile host, in this case the temporary IP address
will belong to the foreign agent’s IP address.
The protocol proposed in [Jue98] the mobile host will have the IP addresses of all the home agents in
the home network. When the mobile hosts sends a registration request (issue of Mobile-IP protocol). It will
randomly choose one of the home agents to service the request. As defined in the mobile-IP protocol, it is
assumed that each mobile registration request has an unique identification and a lifetime which defines the
time for which the registration is valid. This time is defined by Treg. The registration packet also contains
the IP address of the mobile host, and the temporary IP address of the mobile host. As part of the mobility
binding, the agent maintains the following information:
1. The unique registration numbers
2. The permanent IP address of the mobile host
3. The temporary IP address of the mobile host
4. A boolean variable called PROXY (on or off), which indicates if the proxy is on or not. If proxy is ON,
then the home agent is acting as a proxy for the mobile host and responds with a proxy ARP reply
whenever an ARP query is received for the mobile host. If it is off, a different home agent is serving
the mobile host.
10](https://image.slidesharecdn.com/mobilesurvey-100731090639-phpapp02/75/Mobile-Survey-on-Simulation-for-Networks-10-2048.jpg)
![5. Treg which defines the time for which the registration is valid.
With multiple home agents load balancing will be achieved by allowing a home agent to transfer
control of a mobile host to another home agent based on some load balancing algorithm. The load
balancing algorithms consist of two parts: a) A transfer policy which determines when a transfer should
take place and b) a Selection policy which determines to which home agent the control should be
transferred.
In fact, [Jue98] choose different load balancing strategies, for instance for policy transfer, three
approaches were made:
• Timer-based: In this approach, each home agent maintains a timer for each mobile host that is serving.
The time value will be referred to as the stream transfer time and will be denoted as Tstt. When a home
agent acquires control of a mobile host, it starts the timer after the first packet for the mobile host is
received. When Tstt expires, a new home agent is selected, and a registration request is forwarded to a
new home agent.
• Counter-based: This approach is different, the home agent counts the number of packets forwarded to
each mobile host. When the counter reaches a specified limit, the home agent transfers the registration
of the mobile host to another home-agent. This counter is referred as Tstc
• Threshold-based: For each mobile host, the home-agent maintains a count of the number of packets in
its queue which are destined to the mobile host. When the number of packets in the queue for a given
mobile host exceeds the threshold, the home-agent forwards that mobile host’s registration to another
home agent. The threshold value will be referred as Tsth
There is not much difference between policies requires some extra overhead, in other words, re-register
the mobile host to a new home-agent and selection procedure involved. As shown here is expected to see
that the Timer-based approach will lead to switching from home-agents even though the traffic is zero. This
situation is not present in the counter based approach. The values for thresholds and timeouts were modeled
in the paper.
There is another factor in this protocol, and it is the selection of the next home-agent, three different
policies where also studied in this paper:
• Random policy: The next home-agent is selected randomly from all home agents, including the home
agent attempting the transfer.
• Round-robin policy (RR): The home agent are logically ordered and the next home agent is selected
using a simple round-robin policy
11](https://image.slidesharecdn.com/mobilesurvey-100731090639-phpapp02/75/Mobile-Survey-on-Simulation-for-Networks-11-2048.jpg)
![ANALITICAL SIMULATION OF MOBILE NETWORKS
Mobility and performance modeling in cellular communication networks
A simply analytical model for cellular communication networks can be found in [Camar98], where the
model assumes a finite population of mobiles moving in a finite number of cells. This model tries to
evaluate the Fixed Channel Allocation (FCA) factor, as well as, user load, mobility and distribution of users
among cells. This model is suitable for the future of Pico-cellular systems.
The main assumptions of the model are:
• A finite population of users moving in a finite set of cells
• Users are indistinguishable from each other and pass from a cell to another following a probability
transition patters with the same transmission rate
• A parameter called µP, or the cell transition rate. The model assumes a FCA assignment for the channel
frequencies.
According to the results shown in [Camar98], the use of uniform channel allocation scheme is worse
than the use of a non uniform one. In fact, minimum-blocking probability is obtained with a number of
channels allocated to each cell approximately proportional to the number of users in the cell.
Network Modeling
Hexagonal cells arranged in (2R –1) rows, as shown in Figure 1 can represent an ideal network.
As shown, there are R rows of K cells and (R-1) row of (K+1) cells. The total number of cells is M=RK +
(R-1)(K+1). We assume N users circulating in the network. It is supposed that the occupation time of a user
is defined by an exponential distribution with mean 1/µP i.e. the pdf of this random variable (called TP) is:
f T p (t ) = µ P e − µ Pt
13](https://image.slidesharecdn.com/mobilesurvey-100731090639-phpapp02/75/Mobile-Survey-on-Simulation-for-Networks-13-2048.jpg)

![g(n,m)=hm(n), m=1; n=1…N
n
g (n, m) = ∑ hm (k ) g (n − k , m − 1) , n=1…N, m=2…M,
k =0
the marginal state probability of the Mth cell is given by:
1
P ( nM = k ) = hM (k ) g ( N − k , M − 1) (4)
G
while the average number of users is given by:
N
E[nm ] = ∑ kP(nM = k ) =
k =1
1 N
= ∑ k ⋅ hM (k ) g ( N − k , M − 1) (5)
G k =1
Using little’s formula, the true arrival rate can be easily calculated as:
E ( nM )
λM ( N ) = = E (nM ) µ P (6)
E (T p )
it can be also shown that, the Utilization of the queue M, that is cell M, are given respectively by:
g ( N , M − 1)
U M (N ) = 1− (7)
G
g ( N − 1, M )
X M (N ) = 1− (8)
G
In this case Xm which is the throughput is expected to be:
λ M ( N ) = X M ( N ) (9)
Cell modeling
In addition to the Throughput and utilization equation mentioned in the previous section,
[Camar98] points out the need to model de cells in the network and specific processes such as call blocking
and hand-off blocking. For example, when considering the service offered to the users, the possibility to
make a call, the cell can be represented by a finite population (n) in a M/M/m/m/n queue. This is a loss
system where the maximum number of contemporary calls in progress is given by the number of channels
m assigned to the cell. As a resulting equation, the steady state probabilitie is given by:
15](https://image.slidesharecdn.com/mobilesurvey-100731090639-phpapp02/75/Mobile-Survey-on-Simulation-for-Networks-15-2048.jpg)


![REFERENCES
[Camar98] P. Camarda, G. Shiraldi, et.al. “ Mobility and Performance Modeling in Cellular
Communication Networks”, Mobile Computing and Communication Review, Vol.1 No.
4, 1998, 25-32.
[Jue98] J. Jue, D. Ghosal “Design and Analysis of Replicated Server Architecture for Supporting
IP-Host Mobility”, Mobile Computing and Communication Review, Vol 2, No. 3, 1998,
16-23,
[Li98] Y. Li and V. Leung. “Supporting Personal Mobility for Nomadic Computing over the
Internet”, Mobile Computing and Communication Review, Vol. 1, Number 1, 1998,
22-31.
[Iera98] A. Iera, A. Fazio, et.al. “Hand-off management algorithms for urban and sub-urban
environments under realistic vehicle mobility conditions”, IEEE International Conference
on Communications v 3 1998. IEEE, Piscataway, NJ, USA,98CH36220. p 1375-1379
[Dell98] M. Dell’Abate, M. DeMarco and V. Trecordi “Performance evaluation of mobile IP
protocols in a wireless environment” IEEE International Conference on Communications
v 3 1998. IEEE, Piscataway, NJ, USA,98CH36220. p 1810-1816
[Mysore98] J. Mysore, B. Vaduvur. “Performance of transport protocols over a multicasting-based
architecture for Internet host mobility” IEEE International Conference on
Communications v 3 1998. IEEE, Piscataway, NJ, USA,98CH36220. p 1817-1823
18](https://image.slidesharecdn.com/mobilesurvey-100731090639-phpapp02/75/Mobile-Survey-on-Simulation-for-Networks-18-2048.jpg)