Embed presentation
Download as PDF, PPTX






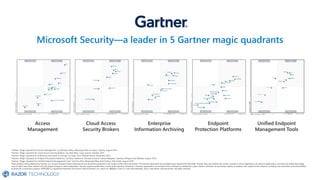


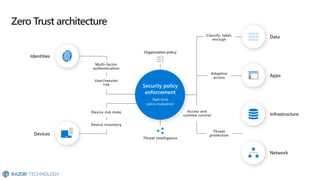





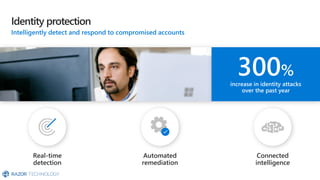


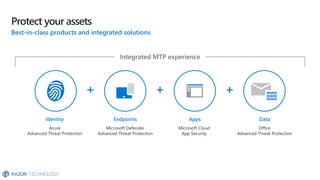

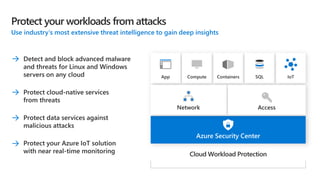

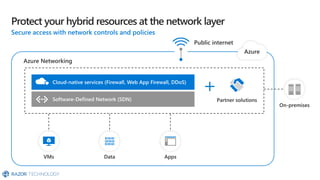

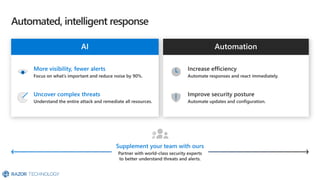







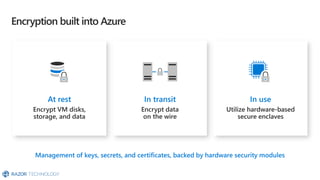

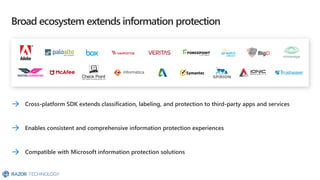



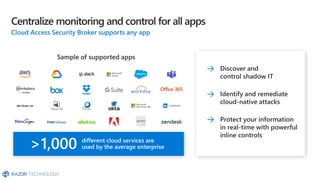
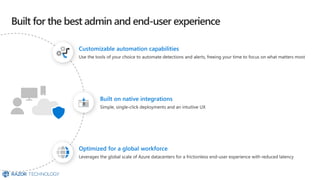
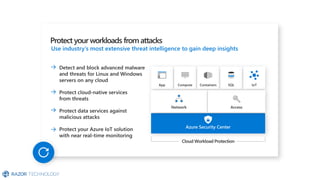
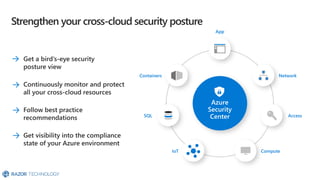
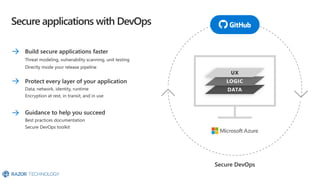
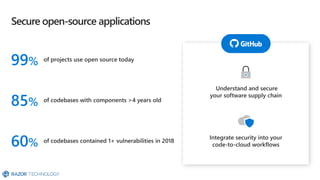
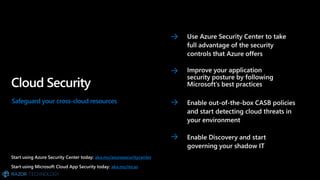










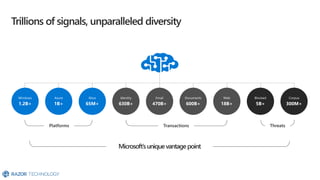
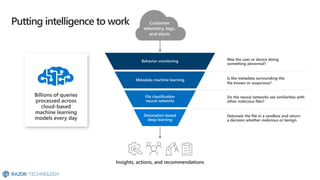
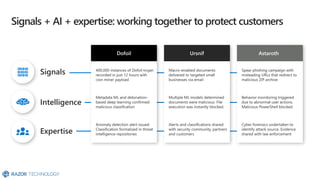





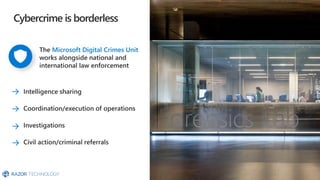

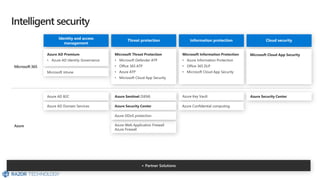

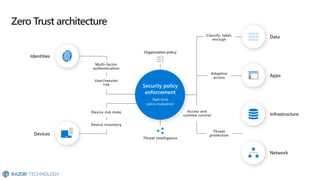
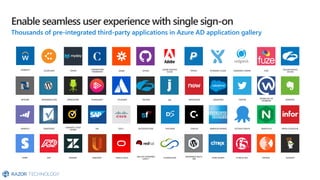
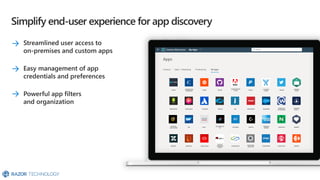
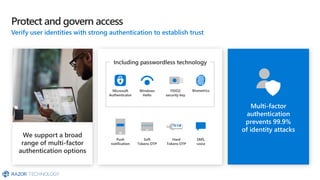
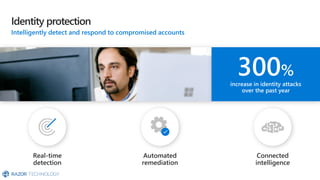
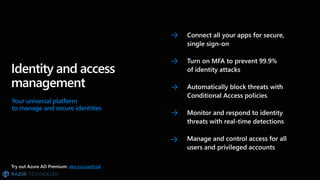
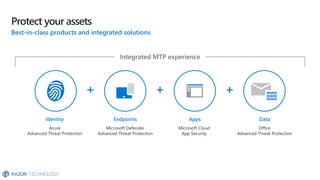
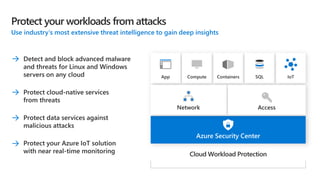
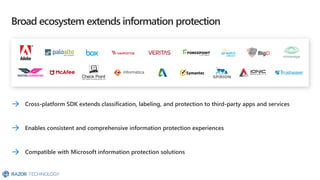
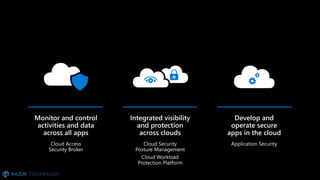
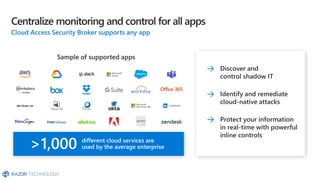
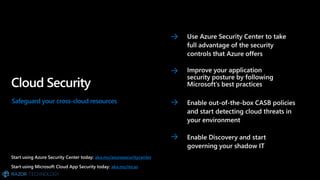
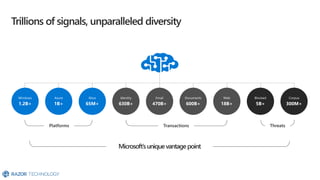
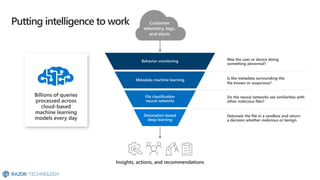
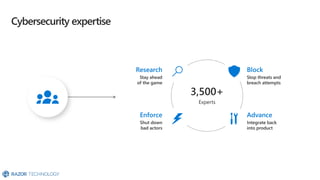
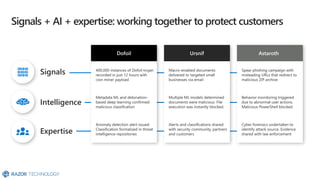
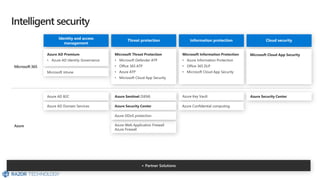
The document promotes various Microsoft security resources and services, including threat protection and information protection. It provides links to guides and support for utilizing these security features effectively. Additionally, it includes contact information for Razor Technology for further inquiries.