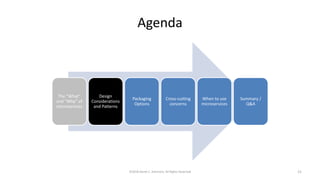
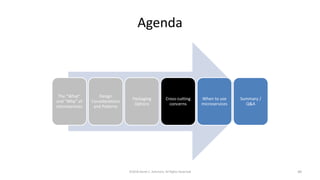
This document summarizes Derek Ashmore's presentation on microservices for architects. The presentation covers:
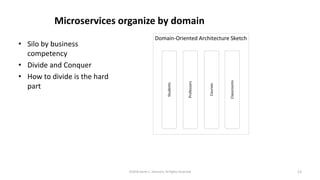
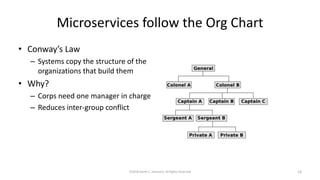
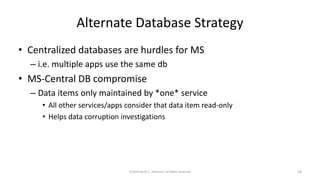
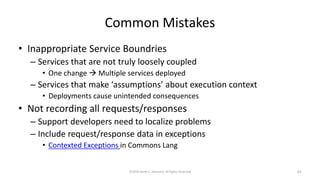
- The definition and common traits of microservices including single functional purpose and loose coupling.
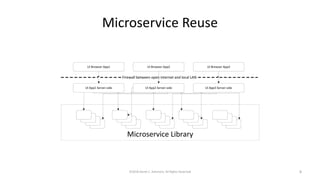
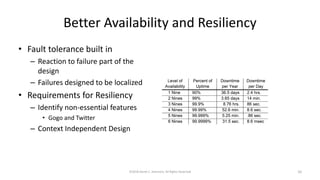
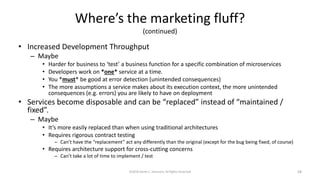
- The benefits of microservices including faster delivery to market through continuous delivery, increased reuse, and better availability through fault tolerance and localization of failures.
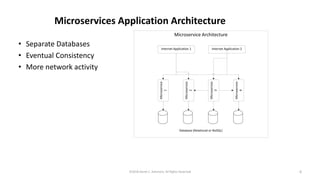
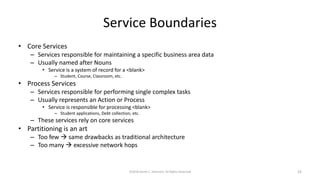
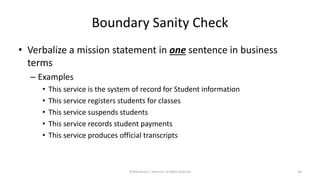
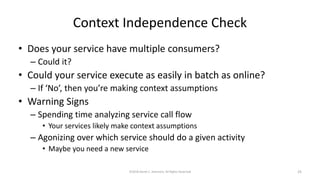
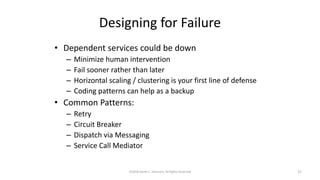
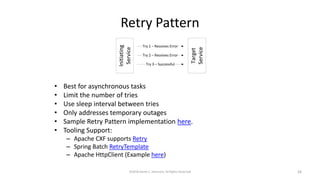
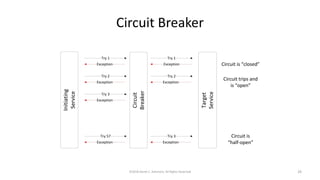
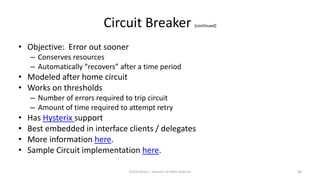
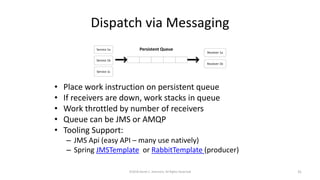
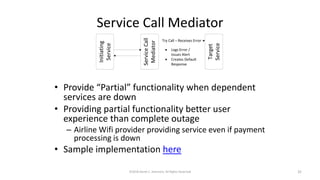
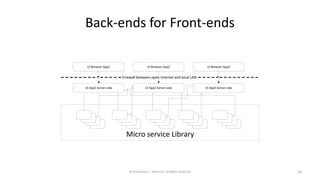
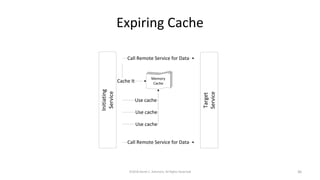
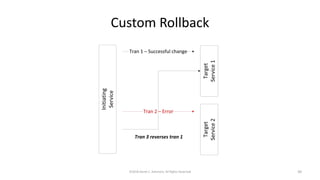
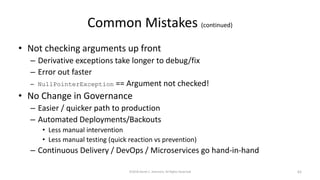
- Design considerations for microservices including service boundaries, handling service call failures, ensuring data integrity, and improving performance through patterns like circuit breakers, caching, and back-ends for front-ends.