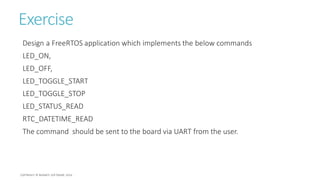
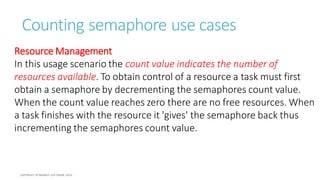
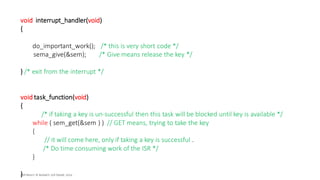
The document discusses the implementation and management of FreeRTOS on STM32 microcontrollers, focusing on queues, semaphores, and their roles in task synchronization and communication. It explains how to create, send, and receive data through queues, as well as the difference between binary and counting semaphores for managing synchronization and mutual exclusion. Additionally, practical exercises are provided to illustrate the concepts, including designing applications and using semaphores to manage interrupt-driven tasks.






![Command Format
struct APP_CMD
{
uint8_t COMMAND_NUM;
uint8_t COMMAND_ARGS[10];
};
/* Lets use this data
structure to store
command number and
its associated
arguments. */](https://image.slidesharecdn.com/masteringrtosfreertosandstm32fxwithdebugging-part3-190826055453/85/PART-3-Mastering-RTOS-FreeRTOS-and-STM32Fx-with-Debugging-26-320.jpg)






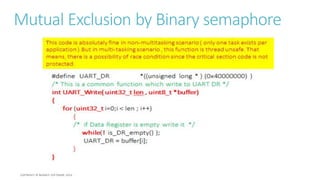
![#define UART_DR *((unsigned long * ) (0x40000000) )
/* This is a common function which write to UART DR */
int UART_Write( uint32_t len , uint8_t *buffer)
{
for (uint32_ti=0;i < len ; i++)
{
/* if Data Register is empty write it */
while(! is_DR_empty() );
UART_DR = buffer[i];
}
}
This is Thread-Unsafe code](https://image.slidesharecdn.com/masteringrtosfreertosandstm32fxwithdebugging-part3-190826055453/85/PART-3-Mastering-RTOS-FreeRTOS-and-STM32Fx-with-Debugging-90-320.jpg)
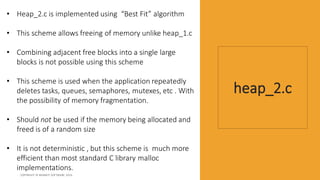
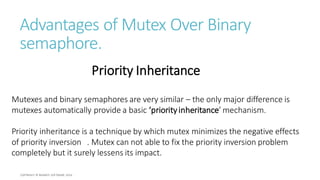
![#define UART_DR *((unsigned long * ) (0x40000000) )
/* This is a common function which write to UART DR */
int UART_Write( uint32_t len , uint8_t *buffer)
{
for (uint32_ti=0;i < len ; i++)
{
/* if Data Register is empty write it */
while(! is_DR_empty() );
UART_DR = buffer[i];
}
}
This is Thread-Unsafe code
This codeis absolutelyfine in non-multitaskingscenario( onlyone taskexistsper
application).But in multi-taskingscenario, this functionis thread unsafe.That means,
there is a possibility of race conditionsincethe critical section codeis notprotected.](https://image.slidesharecdn.com/masteringrtosfreertosandstm32fxwithdebugging-part3-190826055453/85/PART-3-Mastering-RTOS-FreeRTOS-and-STM32Fx-with-Debugging-91-320.jpg)
![Mutual Exclusion by Binary semaphore
#define UART_DR *((unsigned long * ) (0x40000000) )
/* This is a common function which write to UART DR */
int UART_Write( uint32_t len , uint8_t *buffer)
{
for (uint32_t i=0;i < len ; i++)
{
/* if Data Register is empty write it */
while(! is_DR_empty() );
UART_DR = buffer[i];
}
}](https://image.slidesharecdn.com/masteringrtosfreertosandstm32fxwithdebugging-part3-190826055453/85/PART-3-Mastering-RTOS-FreeRTOS-and-STM32Fx-with-Debugging-93-320.jpg)

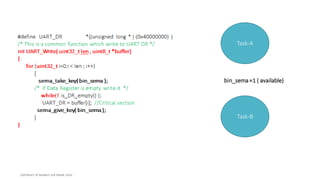
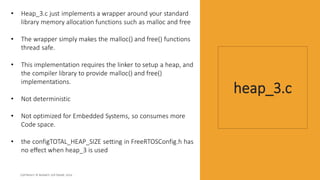
![#define UART_DR *((unsigned long * ) (0x40000000) )
/* This is a common function which write to UART DR */
int UART_Write( uint32_t len , uint8_t *buffer)
{
for (uint32_t i=0;i < len ; i++)
{
sema_take_key(bin_sema );
/* if Data Register is empty write it */
while(! is_DR_empty() );
UART_DR = buffer[i]; //Critical section
sema_give_key( bin_sema );
}
}](https://image.slidesharecdn.com/masteringrtosfreertosandstm32fxwithdebugging-part3-190826055453/85/PART-3-Mastering-RTOS-FreeRTOS-and-STM32Fx-with-Debugging-96-320.jpg)
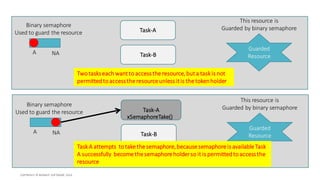
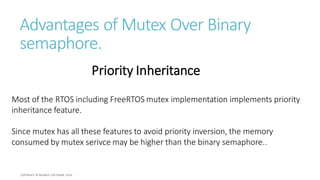
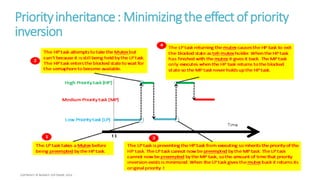
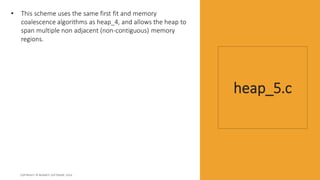
![t1
LowPriority task[LP]
MediumPriority task[MP]
HighPriority task[HP]
TheHP taskattempts to takethe Mutexbut
can't becauseit is stillbeingheldby theLP task.
TheHP task enters theblockedstateto wait for
thesemaphoreto becomeavailable.
TheLP taskreturningthe mutexcauses theHP taskto exit
theblockedstateas themutexholder.WhentheHP task
has finishedwiththe mutexit gives it back.TheMP task
only executes when theHP taskreturns totheblocked
stateso theMP taskneverholds up theHP task.
The LP tasktakes a Mutexbefore
being preempted by theHP task.
TheLP taskis preventingtheHP taskfromexecutingso inherits thepriorityof the
HP task. TheLP taskcannotnowbe preemptedby theMP task.TheLP task
cannot nowbe preempted by theMP task, so theamountof timethat priority
inversionexists is minimized. WhentheLP taskgives the mutexback it returns its
original priority.!
Time
1
2
3
4](https://image.slidesharecdn.com/masteringrtosfreertosandstm32fxwithdebugging-part3-190826055453/85/PART-3-Mastering-RTOS-FreeRTOS-and-STM32Fx-with-Debugging-105-320.jpg)