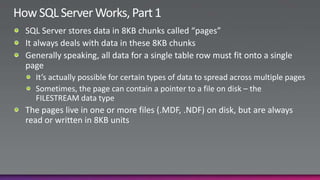
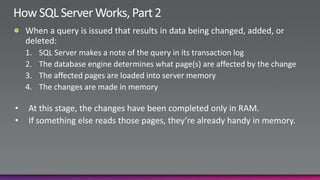
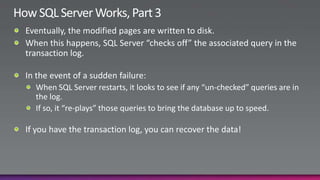
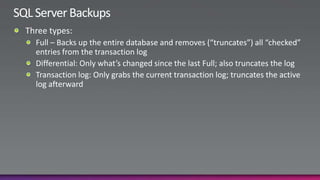
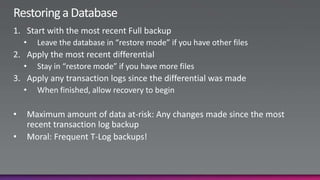
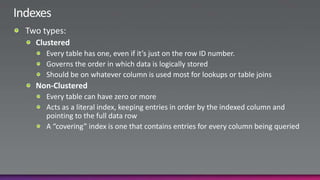
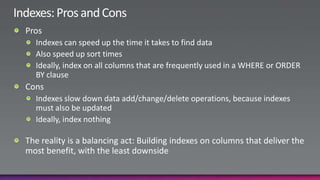
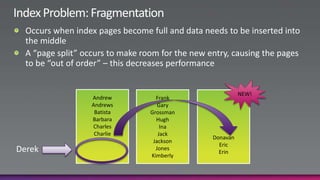
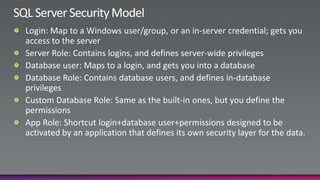
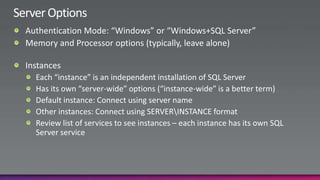
This slide deck presentation provides an overview of managing Microsoft SQL Server for those who are not primarily database administrators. The presentation covers how SQL Server works, backup and restore operations, indexes, database and server configuration options, security models, and high availability and replication options. It also demonstrates various SQL Server management tasks in the SQL Server Management Studio tool. The presentation encourages attendees to reuse the material and provides contact information for the company that created the presentation for additional training opportunities.