Managing Cloud Business Solutions Worksheets v2 Nov 13
•Download as DOCX, PDF•
0 likes•568 views
Worksheets to support the "Managing Cloud Business Solutions" Digital Enterprise Workshop - http://www.slideshare.net/vanguardvisions/managing-cloud-business-solutions-updated-nov-13
Report
Share
Report
Share
Recommended
Building the Global "Cloud 2"

Peter Coffee presentation to Wipro Leading Edge conference in Bali, Indonesia, November 2010
What's new in Security and Compliance in SharePoint , OneDrive for Business &...

What's new in Security and Compliance in SharePoint , OneDrive for Business &...Vignesh Ganesan I Microsoft MVP
Slide deck used on our presentation for Modern Workplace Conference,Paris 2021 Virtual event where myself and Vijai Anand did a session on "What's new in Security and Compliance in SharePoint , OneDrive for Business & MS Teams"Web 2.0 goes to work for business: Enabling the power of participation

IBM presentation at Enterprise 2.0 Executive Forum 2009 in Sydney
Real world risks for all Knowledge areas of PMBOK

PMBOK, Risk management, Risk Managers, Knowledge areas
Cloud Computing - Benefits and Risks

Recent economic pressures have resulted in increased requirements for the availability, scalability and efficiency of enterprise IT solutions.
Many parties claim that “cloud computing” can help enterprises meet the increased requirements of lower TCO, higher ROI, increased efficiency, dynamic provisioning and utility-like services.
However, many IT professionals are citing the increased risks associated with trusting information assets to the cloud as something that must be clearly understood and managed by relevant stakeholders.
This presentation examines the potential business benefits, risks and assurance considerations.
Summer 2015 Worldwide Netskope Cloud Report

In this Netskope Cloud Report infographic, we've compiled the most interesting trends on cloud app adoption and usage based on aggregated, anonymized data from the Netskope Active Platform.
OSB310: Whitelisting: The Good, The Bad, and The Ugly!

OSB310: Whitelisting: The Good, The Bad, and The Ugly! Josh Borges
Schahin presentation at IBM Connect 2014

Schahin presentation at IBM Connect 2014 about their Corporate Social Network beeSocial.
Keynote Tech Talks: Watching SaaS Apps with Keynote

SaaS has transformed your business. The numbers say you’re running at least 4 apps today, powering everything from Sales to Operations to IT. SaaS delivers agility.
So why would you need to monitor Salesforce.com, NetSuite, Marketo, or Office365? The more you run on SaaS, the more your business resiliency is dependent on actionable performance insight.
DIY guide to runbooks, incident reports, and incident response

In this session, we explore the cost of incidents and consider creative ways to look at future threats. We walk you through the threat landscape, looking at what has happened over the last year. Learn about the best open-source tools to have in your security arsenal now and in the future to help you detect and deal with the threats of today and tomorrow. Finally, learn how to identify where these threats are coming from and how to detect them more easily. The information in this session is provided by various teams and sources
CMGT 430 V3 Focus Dreams/newtonhelp.com

For more course tutorials visit
www.newtonhelp.com
CMGT 430 Assignment Week 1 IT Systems Connection Table
CMGT 430 Assignment Week 2 Enterprise Security Concerns
CMGT 430 Assignment Week 3 Responding to Threats
CMGT 430 Assignment Week 4 Cloud Computing
CMGT 430 V3 Imagine Your Future/newtonhelp.com 

For more course tutorials visit
www.newtonhelp.com
CMGT 430 Assignment Week 1 IT Systems Connection Table
CMGT 430 Assignment Week 2 Enterprise Security Concerns
CMGT 430 Assignment Week 3 Responding to Threats
Follow these steps to get started with sentinel city® 

Follow these steps to get started with sentinel city®
The 1% Who Can Take Down your Organization

The Cloud Cybersecurity Lessons We Learned from 10M Users. Learn about the top cloud cybersecurity trends that fly under your radar, what the distribution of cloud cybersecurity risk means for your ability to act on it, along with 3 key security skills you should master for an immediately safer cloud environment.
Marketing is the New Sales: Engaging the (Anonymous) Digital Buyer | Mark Stuyt

With most prospects completing the majority of their B2B purchasing research online, they will likely find you long before you find them; which means their 1st, 2nd and often 3rd interaction with your organization will be digital in nature, not human. If you understand how to engage their emotions, they will consume your content and share their contact information. But if you don’t, they’ll move on to the next website and your future customer will be lost forever. With sales professionals effectively removed from much of the buying cycle, marketing is now ultimately responsible for prospect engagement, education and bias creation. Unfortunately, traditional outbound marketing techniques no longer produce the short-term lead volume they once did…….so what do you do? This workshop focuses on the strategic shifts and tactical adjustments that Marketing must execute to engage, influence and bias an increasingly educated and elusive buying community.
Topics include:
• Reimagining the customer acquisition process
• Tribal messaging - creating high-impact emotional content
• Creating industry/vertical oriented emotional messaging
• Improving digital engagement - converting reluctant online visitors
• Selecting images that engage emotions
• Leveraging reciprocity – Developing conversion tactics that work
• And more
Mark Stuyt
Neural Impact
BDO Connections 2016 |
Discussion 300 wordsSearch scholar.google.com or your textbook

Discussion 300 words
Search "scholar.google.com" or your textbook. Discuss how organizations have faced the challenges that incident handlers are challenged with in identifying incidents when resources have been moved to a cloud environment.
Reply to classmate 1: 275 words
Incident Handlers Challenges
The cloud computer helps the people to share their distributed resources which are related to different business organizations. Cloud computing helps business organizations in managing their business around the globe. The cloud computing application helps business organizations in expanding their business at a large level. It can be assessed on web devices from anywhere. Nowadays cloud computing helps the business organizations in meeting the demands of their customers more efficiently. The malicious cloud system has been noticed by the incident handlers which is a core concern for the business organization. Nowadays every business organization is using cloud computing in order to manage their important data and information of the business. The business organization is facing many incidents in their organization which can directly affect the working of their business. The main challenge that has been faced by the incident handlers is the accuracy in identification (John W. Rittinghouse, 2017).
The number of challenges that faced in the cloud environment are as follows:-
1. Challenge of denial of services: - The first main challenge that has been faced by the incident handler is the denial of services. There are various incidents of service attacks which can create a bogus request for preventing the system within the stipulated time. Such physical attack creates a challenge of service denial for the system.
2. Challenge of malicious code: - The second main challenge which can be faced by the incident handler is the challenge of malicious code. It can quickly affect the number of workstations in the business organization. It effects the working of the business organization.
3. Challenge of unauthorized access:- The third main challenge which is being faced by the incident handler is the unauthorized access of the system by the third party in the business organization. It can affect important data and information about the business. The attackers can access the system by the unauthorized way and steal the important data of the business organization.
4. Challenge of inappropriate use:- The fourth main challenge which may be faced by the incident handlers is the challenge of inappropriate use of the system. In the business organization, any employee can provide the illegal copies of the software to the other company employees. They can take advantage of the data and can misuse it.
5. Cloud service provider challenge:- The fifth main challenge that can be faced by the incident handler is the cloud service providers. This situation occurs when there is no control over the actions provided by cloud service provid ...
Social proof yourself in less than an hour a week 

Having an online social media profile is simply not enough when networking professionally online. You also need to social proof yourself by showcasing who you are without being too “in your face”.
Social proofing yourself is the act of sharing information online which people in your network find useful and interact with. This activity then creates a picture in people’s mind about the type of person (or business) you are which helps you build credibility.
What can I do with my eportfolio after formal education and training?

Research shows (Leeson, 2011) that learners are much more likely to engage in the use of an eportfolio to support their formal education and training if they know that they will be able to use their eportfolio for beyond their course. Thinking about how learners will be able to use and access their eportfolio beyond their studies is very important, but it also a difficult issue to solve for many institutions.
This hands-on workshop looked at why learners should be using their eportfolio beyond formal study and what they can do with their eportfolio. It also looked at how they can get their eportfolio out of a formal institution’s system and where they can house it. The workshop was a combination of ideas from the workshop facilitator’s experience, as well as draw on the questions and experiences of the participants in the workshop which will lead to new ideas, solutions and questions.
More Related Content
Similar to Managing Cloud Business Solutions Worksheets v2 Nov 13
Building the Global "Cloud 2"

Peter Coffee presentation to Wipro Leading Edge conference in Bali, Indonesia, November 2010
What's new in Security and Compliance in SharePoint , OneDrive for Business &...

What's new in Security and Compliance in SharePoint , OneDrive for Business &...Vignesh Ganesan I Microsoft MVP
Slide deck used on our presentation for Modern Workplace Conference,Paris 2021 Virtual event where myself and Vijai Anand did a session on "What's new in Security and Compliance in SharePoint , OneDrive for Business & MS Teams"Web 2.0 goes to work for business: Enabling the power of participation

IBM presentation at Enterprise 2.0 Executive Forum 2009 in Sydney
Real world risks for all Knowledge areas of PMBOK

PMBOK, Risk management, Risk Managers, Knowledge areas
Cloud Computing - Benefits and Risks

Recent economic pressures have resulted in increased requirements for the availability, scalability and efficiency of enterprise IT solutions.
Many parties claim that “cloud computing” can help enterprises meet the increased requirements of lower TCO, higher ROI, increased efficiency, dynamic provisioning and utility-like services.
However, many IT professionals are citing the increased risks associated with trusting information assets to the cloud as something that must be clearly understood and managed by relevant stakeholders.
This presentation examines the potential business benefits, risks and assurance considerations.
Summer 2015 Worldwide Netskope Cloud Report

In this Netskope Cloud Report infographic, we've compiled the most interesting trends on cloud app adoption and usage based on aggregated, anonymized data from the Netskope Active Platform.
OSB310: Whitelisting: The Good, The Bad, and The Ugly!

OSB310: Whitelisting: The Good, The Bad, and The Ugly! Josh Borges
Schahin presentation at IBM Connect 2014

Schahin presentation at IBM Connect 2014 about their Corporate Social Network beeSocial.
Keynote Tech Talks: Watching SaaS Apps with Keynote

SaaS has transformed your business. The numbers say you’re running at least 4 apps today, powering everything from Sales to Operations to IT. SaaS delivers agility.
So why would you need to monitor Salesforce.com, NetSuite, Marketo, or Office365? The more you run on SaaS, the more your business resiliency is dependent on actionable performance insight.
DIY guide to runbooks, incident reports, and incident response

In this session, we explore the cost of incidents and consider creative ways to look at future threats. We walk you through the threat landscape, looking at what has happened over the last year. Learn about the best open-source tools to have in your security arsenal now and in the future to help you detect and deal with the threats of today and tomorrow. Finally, learn how to identify where these threats are coming from and how to detect them more easily. The information in this session is provided by various teams and sources
CMGT 430 V3 Focus Dreams/newtonhelp.com

For more course tutorials visit
www.newtonhelp.com
CMGT 430 Assignment Week 1 IT Systems Connection Table
CMGT 430 Assignment Week 2 Enterprise Security Concerns
CMGT 430 Assignment Week 3 Responding to Threats
CMGT 430 Assignment Week 4 Cloud Computing
CMGT 430 V3 Imagine Your Future/newtonhelp.com 

For more course tutorials visit
www.newtonhelp.com
CMGT 430 Assignment Week 1 IT Systems Connection Table
CMGT 430 Assignment Week 2 Enterprise Security Concerns
CMGT 430 Assignment Week 3 Responding to Threats
Follow these steps to get started with sentinel city® 

Follow these steps to get started with sentinel city®
The 1% Who Can Take Down your Organization

The Cloud Cybersecurity Lessons We Learned from 10M Users. Learn about the top cloud cybersecurity trends that fly under your radar, what the distribution of cloud cybersecurity risk means for your ability to act on it, along with 3 key security skills you should master for an immediately safer cloud environment.
Marketing is the New Sales: Engaging the (Anonymous) Digital Buyer | Mark Stuyt

With most prospects completing the majority of their B2B purchasing research online, they will likely find you long before you find them; which means their 1st, 2nd and often 3rd interaction with your organization will be digital in nature, not human. If you understand how to engage their emotions, they will consume your content and share their contact information. But if you don’t, they’ll move on to the next website and your future customer will be lost forever. With sales professionals effectively removed from much of the buying cycle, marketing is now ultimately responsible for prospect engagement, education and bias creation. Unfortunately, traditional outbound marketing techniques no longer produce the short-term lead volume they once did…….so what do you do? This workshop focuses on the strategic shifts and tactical adjustments that Marketing must execute to engage, influence and bias an increasingly educated and elusive buying community.
Topics include:
• Reimagining the customer acquisition process
• Tribal messaging - creating high-impact emotional content
• Creating industry/vertical oriented emotional messaging
• Improving digital engagement - converting reluctant online visitors
• Selecting images that engage emotions
• Leveraging reciprocity – Developing conversion tactics that work
• And more
Mark Stuyt
Neural Impact
BDO Connections 2016 |
Discussion 300 wordsSearch scholar.google.com or your textbook

Discussion 300 words
Search "scholar.google.com" or your textbook. Discuss how organizations have faced the challenges that incident handlers are challenged with in identifying incidents when resources have been moved to a cloud environment.
Reply to classmate 1: 275 words
Incident Handlers Challenges
The cloud computer helps the people to share their distributed resources which are related to different business organizations. Cloud computing helps business organizations in managing their business around the globe. The cloud computing application helps business organizations in expanding their business at a large level. It can be assessed on web devices from anywhere. Nowadays cloud computing helps the business organizations in meeting the demands of their customers more efficiently. The malicious cloud system has been noticed by the incident handlers which is a core concern for the business organization. Nowadays every business organization is using cloud computing in order to manage their important data and information of the business. The business organization is facing many incidents in their organization which can directly affect the working of their business. The main challenge that has been faced by the incident handlers is the accuracy in identification (John W. Rittinghouse, 2017).
The number of challenges that faced in the cloud environment are as follows:-
1. Challenge of denial of services: - The first main challenge that has been faced by the incident handler is the denial of services. There are various incidents of service attacks which can create a bogus request for preventing the system within the stipulated time. Such physical attack creates a challenge of service denial for the system.
2. Challenge of malicious code: - The second main challenge which can be faced by the incident handler is the challenge of malicious code. It can quickly affect the number of workstations in the business organization. It effects the working of the business organization.
3. Challenge of unauthorized access:- The third main challenge which is being faced by the incident handler is the unauthorized access of the system by the third party in the business organization. It can affect important data and information about the business. The attackers can access the system by the unauthorized way and steal the important data of the business organization.
4. Challenge of inappropriate use:- The fourth main challenge which may be faced by the incident handlers is the challenge of inappropriate use of the system. In the business organization, any employee can provide the illegal copies of the software to the other company employees. They can take advantage of the data and can misuse it.
5. Cloud service provider challenge:- The fifth main challenge that can be faced by the incident handler is the cloud service providers. This situation occurs when there is no control over the actions provided by cloud service provid ...
Similar to Managing Cloud Business Solutions Worksheets v2 Nov 13 (20)
What's new in Security and Compliance in SharePoint , OneDrive for Business &...

What's new in Security and Compliance in SharePoint , OneDrive for Business &...
Web 2.0 goes to work for business: Enabling the power of participation

Web 2.0 goes to work for business: Enabling the power of participation
OSB310: Whitelisting: The Good, The Bad, and The Ugly!

OSB310: Whitelisting: The Good, The Bad, and The Ugly!
Keynote Tech Talks: Watching SaaS Apps with Keynote

Keynote Tech Talks: Watching SaaS Apps with Keynote
DIY guide to runbooks, incident reports, and incident response

DIY guide to runbooks, incident reports, and incident response
Follow these steps to get started with sentinel city® 

Follow these steps to get started with sentinel city®
2015_buyers_guide_to_accounting_and_financial_software

2015_buyers_guide_to_accounting_and_financial_software
Marketing is the New Sales: Engaging the (Anonymous) Digital Buyer | Mark Stuyt

Marketing is the New Sales: Engaging the (Anonymous) Digital Buyer | Mark Stuyt
Discussion 300 wordsSearch scholar.google.com or your textbook

Discussion 300 wordsSearch scholar.google.com or your textbook
More from Vanguard Visions
Social proof yourself in less than an hour a week 

Having an online social media profile is simply not enough when networking professionally online. You also need to social proof yourself by showcasing who you are without being too “in your face”.
Social proofing yourself is the act of sharing information online which people in your network find useful and interact with. This activity then creates a picture in people’s mind about the type of person (or business) you are which helps you build credibility.
What can I do with my eportfolio after formal education and training?

Research shows (Leeson, 2011) that learners are much more likely to engage in the use of an eportfolio to support their formal education and training if they know that they will be able to use their eportfolio for beyond their course. Thinking about how learners will be able to use and access their eportfolio beyond their studies is very important, but it also a difficult issue to solve for many institutions.
This hands-on workshop looked at why learners should be using their eportfolio beyond formal study and what they can do with their eportfolio. It also looked at how they can get their eportfolio out of a formal institution’s system and where they can house it. The workshop was a combination of ideas from the workshop facilitator’s experience, as well as draw on the questions and experiences of the participants in the workshop which will lead to new ideas, solutions and questions.
Choosing the right learning management system (LMS) / virtual learning enviro...

The learning management system (LMS) or virtual learning environment (VLE)) has become the default core component of any blended and online learning. While LMSs/VLEs typically share the common purpose of managing and administering learning and assessment activities, their individual features and functions of each platforms can vary widely. With hundreds of different LMSs/VLEs to choose from, selecting the right one requires a clear understanding of what key features and functionalities which are needed by all key stakeholders using the LMS/VLE. This session will outline the processes needed to ensure that you choose the right LMS/VLE. This will be done through a comparison of popular LMSs/VLEs, such as Moodle and Blackboard, together with corporate and integrated LMS/VLE options
Tips and tools for working smarter

Digital technologies and environments such as mobile devices, social media and ‘the Cloud’ are not only changing the way people are interacting with your business but they can also transform the way you run your business. These digital tools can help you work smarter and help you grow your business at the same time.
But which digital tools do what, and how can you easily adopt them without having to be a computer nerd?
Allison Miller, e-Business mentor and consultant, shares the digital tools that she uses to run her home-based business smarter for the Northern Women's Business Network in Adelaide, South Australia
Increase student motivation (and reduce cheating) using Moodle and Mahara 

Offering education and training online means that people who live outside your geographical area, who are time poor or who cannot get to regular classes, can get a chance to study. Online learning, however, can result in some students feeling isolated. It can also increase the risk of cheating, as it can be harder to get to know your online students in the same way than those you teach face-to-face.
A recent study identified that the best way to reduce cheating is to increase your students’ motivation and interest in their learning (Lang 2013 via Morris, 2014).
Increasing the intrinsic or ‘what’s in it for me (WIIFM)’ value of online learning provides a win-win situation for the online student, through more interaction with other people and a better learning experience as a result. This presentation will share how Mahara can increase the intrinsic motivation in your students and therefore reduce the chances of your students cheating.
Increase student motivation (and reduce cheating) using Mahara

Offering education and training online means that people who live outside your geographical area, who are time poor or who cannot get to regular classes, can get a chance to study. Online learning, however, can result in some students feeling isolated. It can also increase the risk of cheating, as it can be harder to get to know your online students in the same way than those you teach face-to-face.
A recent study identified that the best way to reduce cheating is to increase your students’ motivation and interest in their learning (Lang 2013 via Morris, 2014). Increasing the intrinsic or ‘what’s in it for me (WIIFM)’ value of online learning provides a win-win situation for the online student, through more interaction with other people and a better learning experience as a result.
This presentation will share how Mahara can increase the intrinsic motivation in your students and therefore reduce the chances of your students cheating.
Top tips and techniques for getting started (or expanding) your flexible trai...

Learners are looking for flexible training options that allow them to learn anytime, any where and from any device. Designing and implementing flexible or blended learning programs can be challenging as they require trainers rethink their current training program.
These slides showcase some best practice examples of flexible learning design techniques which will allow you to get started (or benchmark) your existing flexible training program. You will walk away with some useful resources and some solid actions to kick start your flexible training program design process (or which will help you breath some life into your existing implementation).
Managing and measuring your social media activities using Hootsuite - October...

Social media sites such as Facebook, LinkedIn and Twitter offer businesses an effective way of promoting their business online through building relationships with their target market and providing good customer service for their existing customers. However, people interact with these social media sites for different purposes, so a well-constructed and executed digital marketing strategy is important to ensure that the right message is posted at the right time. But who has the time to be in all of these spaces all of the time?
Use these slides to learn how you can maximise your time while managing and measuring your social media activities using Hootsuite.
Evidencing compliance of quality training and assessment (SNR 15) through e-l...

A vast majority of Australian RTOs are still struggling to demonstrate compliance of quality training and assessment (SNR 15) due to poor program design, trainers and assessors lacking the skills and expertise in conducting training and assessment, as well as ineffective validation and moderation processes (ASQA presentation at Skills Tasmania, Sept 2013). However, taking your training and assessment online often means you can better evidence your audit compliance requirements through the e-learning tools and processes which are used. Join this session to learn how using e-learning tools are enabling RTOs to effectively evidence their compliance of quality training and assessment.
Blogging brings you business - but how? - August 2014

Many businesses have their website in set and forget mode hoping this will be a useful digital shop front which will attract new business. Static websites may as well be invisible online, and they do not make the most of an expensive investment in terms of online customer service opportunities.
Blogging or having a ‘latest news’ section on a website means that your business can not only help your website flourish, it can bring their business’s personality alive to attract new business, and maintain existing business relationships.
This presentation demonstrates the power of blogging for your business to support your digital marketing strategies, as well as improve customer service strategies.
Emerging E-learning Trends, Tools, Techniques supporting 70 20 10 

The emerging e-learning trends, tools and techniques which are being used to support the 70 20 10 model of organisational learning and development.
Don't let your business become digital road kill - 250614

Those businesses which are highly engaged online are twice as likely to be growing their revenue, however only small percentage of Australian small businesses are fully making the most of the internet.
This presentation covers how digital disruption is impacting Australian businesses, and help you understand can do to ensure your business is a digital survivor.
You will be encouraged to set yourself actions to further investigate key digital business strategies which will help you utilise the economic and social benefits of a digital economy to ensure that your business does not end up as digital road kill.
Driving customers to your website

Just because you have a website, and hopefully a social media presence, doesn’t mean that people can easily find your business online. There are millions and millions of websites on the internet so how can website stand out from all of the others to attract customers to it?
You need to be regularly updating your website, undertaking simple steps which will increase your search engine optimisation (SEO), and using other online marketing techniques to be driving people there, but this requires careful consideration and planning.
These slides will help you plan your digital marketing approach to ensure you are driving customers to your website and making the most of your online business opportunities.
Top tips for running your business safely online - 030614

You know you should be doing more business online and in ‘the Cloud’ but you’re worried about being cyber-scammed.
This presentation explains why now is a good time to be doing business online, along with the top 10 tips for safely running your business online through a few simple and effective cyber-safety steps.
Creating and managing a WordPress business website - March 2014

Having a business website is a key component of a business’s marketing strategy in a digital economy, however, knowing where to get started and how to manage it can be a very daunting task. For a lot of small businesses, outsourcing the creation and management of their website just isn’t a viable option. To overcome this, a number of businesses are using simple to operate website platforms like WordPress.
These slides go through why so many people are using WordPress as a business website, and how to get started creating and setting up your WordPress business website.
Mahara Hui 14 - What to consider when introducing educators to Mahara - 200214

Eportfolios offer an excellent way for learners to manage and demonstrate their learning, however, they are not always the natural first choice e-learning tool for a lot of educators. This means introducing eportfolio systems like Mahara can be quite alien to a lot of educators. It requires careful planning and support to ensure educators can confidently and successfully incorporate Mahara into their teaching and assessment program. This presentation explains what you should consider when introducing Mahara to educators.
Implementing workplace online training - 130214

More and more workplaces are looking for effective ways to train their staff which doesn’t require them to travel long distances or being away from the organisation for long periods of time. Implementing workplace online training (iWOT) is a natural fit to meet this need, but not all training organisations have the knowledge, skills and experiences to make it happen.
This presentation provides an overview of what is required to implement, support and facilitate workplace online training based on case studies and resources already being used to support this type of training.
Top tips for protecting your business online (updated) Feb 14

You know you should be using more online business services in ‘the Cloud’ but you’re worried about being cyber-scammed?
This presentation provides you with the top tips of protecting your online business operations through a few simple and effective cyber-safety steps.
E-portfolios: It’s more than filing stuff in a shoebox - 040214

An e-portfolio is a learner-driven collection of digital objects demonstrating experiences, achievements and evidence of learning. So is this just a fancy way of saying it is about collecting documentation and evidence….in a shoe-box? In this webinar session, Allison shares her considerable experience with e-portfolios, explaining the basics of what they are, how to capture evidence, media/technology options and the best way to structure them. Find out how to get started on either an e-portfolio for yourself...or perhaps how to set them up for your own students
Managing Cloud Business Solutions for Salisbury/Modbury Digital Enterprise Pr...

Using web-based business solutions in the Cloud offers your business greater efficiency, the ability to expand without the up-front costs, while being able to work from anywhere.
But:
what Cloud business solutions will best suit your business?
what Cloud security considerations should you be thinking about?
This interactive workshop will help you with implementing Cloud business solutions in your business.
This workshop will provide you with the top tips of protecting your online business operations through a few simple and effective cyber-safety steps.
More from Vanguard Visions (20)
What can I do with my eportfolio after formal education and training?

What can I do with my eportfolio after formal education and training?
Choosing the right learning management system (LMS) / virtual learning enviro...

Choosing the right learning management system (LMS) / virtual learning enviro...
Increase student motivation (and reduce cheating) using Moodle and Mahara 

Increase student motivation (and reduce cheating) using Moodle and Mahara
Increase student motivation (and reduce cheating) using Mahara

Increase student motivation (and reduce cheating) using Mahara
Top tips and techniques for getting started (or expanding) your flexible trai...

Top tips and techniques for getting started (or expanding) your flexible trai...
Managing and measuring your social media activities using Hootsuite - October...

Managing and measuring your social media activities using Hootsuite - October...
Evidencing compliance of quality training and assessment (SNR 15) through e-l...

Evidencing compliance of quality training and assessment (SNR 15) through e-l...
Blogging brings you business - but how? - August 2014

Blogging brings you business - but how? - August 2014
Emerging E-learning Trends, Tools, Techniques supporting 70 20 10 

Emerging E-learning Trends, Tools, Techniques supporting 70 20 10
Don't let your business become digital road kill - 250614

Don't let your business become digital road kill - 250614
Top tips for running your business safely online - 030614

Top tips for running your business safely online - 030614
Creating and managing a WordPress business website - March 2014

Creating and managing a WordPress business website - March 2014
Mahara Hui 14 - What to consider when introducing educators to Mahara - 200214

Mahara Hui 14 - What to consider when introducing educators to Mahara - 200214
Top tips for protecting your business online (updated) Feb 14

Top tips for protecting your business online (updated) Feb 14
E-portfolios: It’s more than filing stuff in a shoebox - 040214

E-portfolios: It’s more than filing stuff in a shoebox - 040214
Managing Cloud Business Solutions for Salisbury/Modbury Digital Enterprise Pr...

Managing Cloud Business Solutions for Salisbury/Modbury Digital Enterprise Pr...
Recently uploaded
Creative Web Design Company in Singapore

At Techbox Square, in Singapore, we're not just creative web designers and developers, we're the driving force behind your brand identity. Contact us today.
Mastering B2B Payments Webinar from BlueSnap

B2B payments are rapidly changing. Find out the 5 key questions you need to be asking yourself to be sure you are mastering B2B payments today. Learn more at www.BlueSnap.com.
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection -Introduction to Social Dreaming
#Systems Psychodynamics
#Innovation
#Creativity
#Consultancy
#Coaching
LA HUG - Video Testimonials with Chynna Morgan - June 2024

Have you ever heard that user-generated content or video testimonials can take your brand to the next level? We will explore how you can effectively use video testimonials to leverage and boost your sales, content strategy, and increase your CRM data.🤯
We will dig deeper into:
1. How to capture video testimonials that convert from your audience 🎥
2. How to leverage your testimonials to boost your sales 💲
3. How you can capture more CRM data to understand your audience better through video testimonials. 📊
Helen Lubchak: Тренди в управлінні проєктами та miltech (UA)

Helen Lubchak: Тренди в управлінні проєктами та miltech (UA)
Kyiv PMDay 2024 Summer
Website – www.pmday.org
Youtube – https://www.youtube.com/startuplviv
FB – https://www.facebook.com/pmdayconference
Agency Managed Advisory Board As a Solution To Career Path Defining Business ...

Agency Managed Advisory Board
3.0 Project 2_ Developing My Brand Identity Kit.pptx

A personal brand exploration presentation summarizes an individual's unique qualities and goals, covering strengths, values, passions, and target audience. It helps individuals understand what makes them stand out, their desired image, and how they aim to achieve it.
Understanding User Needs and Satisfying Them

https://www.productmanagementtoday.com/frs/26903918/understanding-user-needs-and-satisfying-them
We know we want to create products which our customers find to be valuable. Whether we label it as customer-centric or product-led depends on how long we've been doing product management. There are three challenges we face when doing this. The obvious challenge is figuring out what our users need; the non-obvious challenges are in creating a shared understanding of those needs and in sensing if what we're doing is meeting those needs.
In this webinar, we won't focus on the research methods for discovering user-needs. We will focus on synthesis of the needs we discover, communication and alignment tools, and how we operationalize addressing those needs.
Industry expert Scott Sehlhorst will:
• Introduce a taxonomy for user goals with real world examples
• Present the Onion Diagram, a tool for contextualizing task-level goals
• Illustrate how customer journey maps capture activity-level and task-level goals
• Demonstrate the best approach to selection and prioritization of user-goals to address
• Highlight the crucial benchmarks, observable changes, in ensuring fulfillment of customer needs
Maksym Vyshnivetskyi: PMO Quality Management (UA)

Maksym Vyshnivetskyi: PMO Quality Management (UA)
Lemberg PMO School 2024
Website – https://lembs.com/pmoschool
Youtube – https://www.youtube.com/startuplviv
FB – https://www.facebook.com/pmdayconference
Top mailing list providers in the USA.pptx

Discover the top mailing list providers in the USA, offering targeted lists, segmentation, and analytics to optimize your marketing campaigns and drive engagement.
Evgen Osmak: Methods of key project parameters estimation: from the shaman-in...

Evgen Osmak: Methods of key project parameters estimation: from the shaman-inspired to the data-driven praxis (UA)
Kyiv PMDay 2024 Summer
Website – www.pmday.org
Youtube – https://www.youtube.com/startuplviv
FB – https://www.facebook.com/pmdayconference
Best Forex Brokers Comparison in INDIA 2024

Navigating the world of forex trading can be challenging, especially for beginners. To help you make an informed decision, we have comprehensively compared the best forex brokers in India for 2024. This article, reviewed by Top Forex Brokers Review, will cover featured award winners, the best forex brokers, featured offers, the best copy trading platforms, the best forex brokers for beginners, the best MetaTrader brokers, and recently updated reviews. We will focus on FP Markets, Black Bull, EightCap, IC Markets, and Octa.
-- June 2024 is National Volunteer Month --

Check out our June display of books on voluntary organisations
Building Your Employer Brand with Social Media

Presented at The Global HR Summit, 6th June 2024
In this keynote, Luan Wise will provide invaluable insights to elevate your employer brand on social media platforms including LinkedIn, Facebook, Instagram, X (formerly Twitter) and TikTok. You'll learn how compelling content can authentically showcase your company culture, values, and employee experiences to support your talent acquisition and retention objectives. Additionally, you'll understand the power of employee advocacy to amplify reach and engagement – helping to position your organization as an employer of choice in today's competitive talent landscape.
Company Valuation webinar series - Tuesday, 4 June 2024

This session provided an update as to the latest valuation data in the UK and then delved into a discussion on the upcoming election and the impacts on valuation. We finished, as always with a Q&A
Recently uploaded (20)
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection with Social Dreaming
LA HUG - Video Testimonials with Chynna Morgan - June 2024

LA HUG - Video Testimonials with Chynna Morgan - June 2024
The Influence of Marketing Strategy and Market Competition on Business Perfor...

The Influence of Marketing Strategy and Market Competition on Business Perfor...
Helen Lubchak: Тренди в управлінні проєктами та miltech (UA)

Helen Lubchak: Тренди в управлінні проєктами та miltech (UA)
Agency Managed Advisory Board As a Solution To Career Path Defining Business ...

Agency Managed Advisory Board As a Solution To Career Path Defining Business ...
3.0 Project 2_ Developing My Brand Identity Kit.pptx

3.0 Project 2_ Developing My Brand Identity Kit.pptx
Evgen Osmak: Methods of key project parameters estimation: from the shaman-in...

Evgen Osmak: Methods of key project parameters estimation: from the shaman-in...
Company Valuation webinar series - Tuesday, 4 June 2024

Company Valuation webinar series - Tuesday, 4 June 2024
Managing Cloud Business Solutions Worksheets v2 Nov 13
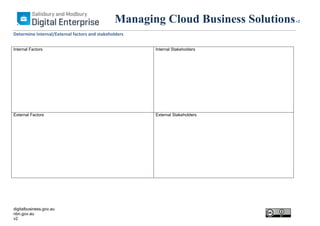
- 1. Managing Cloud Business Solutions Determine Internal/External factors and stakeholders Internal Factors Internal Stakeholders External Factors External Stakeholders digitalbusiness.gov.au nbn.gov.au v2 v2
- 2. Managing Cloud Business Solutions SWOT Analysis Table: Strengths Weaknesses Opportunities Threats digitalbusiness.gov.au nbn.gov.au v2 v2
- 3. Managing Cloud Business Solutions Risk Analysis Table (use in conjunction with the Risk Matrix on the next page) Potential Risk EgUse cloud storage for all company documents digitalbusiness.gov.au nbn.gov.au v2 What might happen? Unable to access company salesrecords due to loss of connectivity What is the likelihood of it happening Likely What is the consequence of it happening? - Loss of productivity - Loss of customer service/sales What is the impact of this? Major Rating Action Eg Low/Acceptable, Medium/Acceptable, High/Unacceptable or Extreme/Unacceptable Unacceptable risk - Back up internet connectivity - Synchronise files v2
- 4. Managing Cloud Business Solutions Source: Chris Toselli – Elearning& Risk digitalbusiness.gov.au nbn.gov.au v2 v2
- 5. Managing Cloud Business Solutions Business Solutions Comparison Software/Service Computer/Server Advantages Disadvantages Cloud Services Can access emails with offline Can only access on one device X Advantages Disadvantages Hard drive/USB/CD EgEmail digitalbusiness.gov.au nbn.gov.au v2 X Access from multiple devices Password required v2
