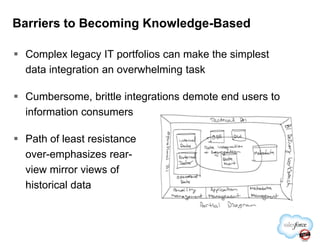
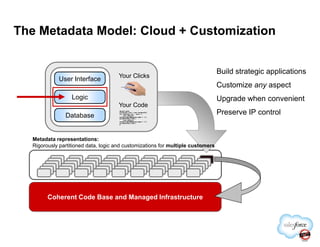
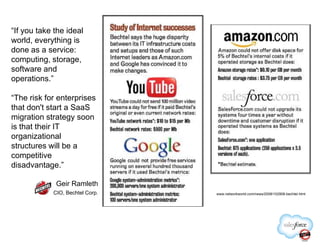
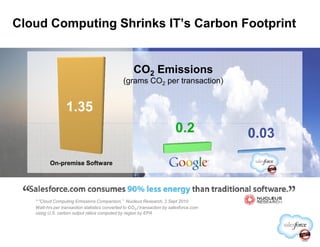
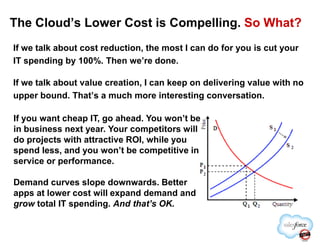
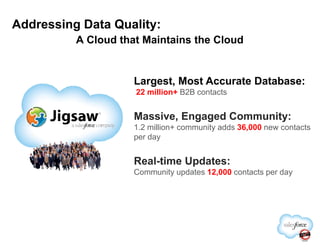
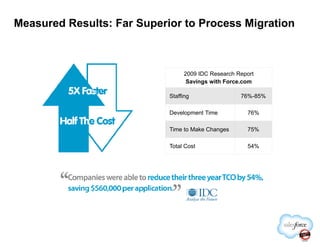
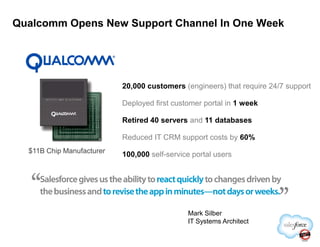
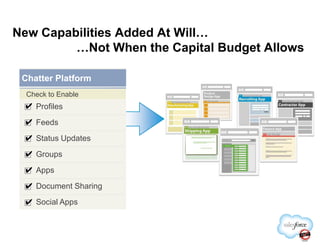
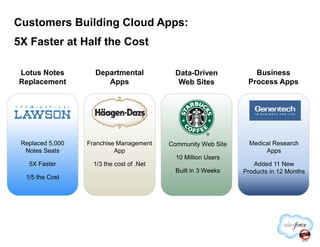
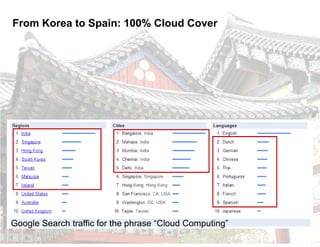
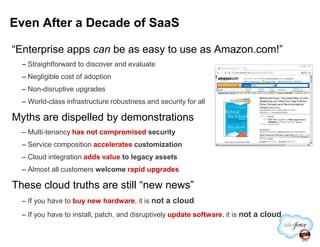
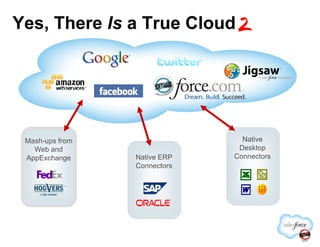
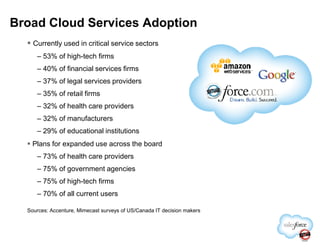
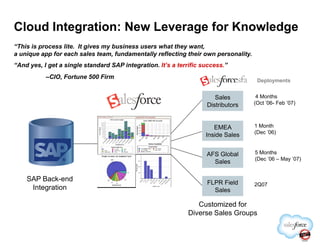
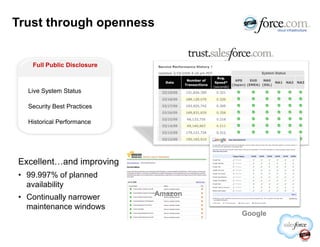
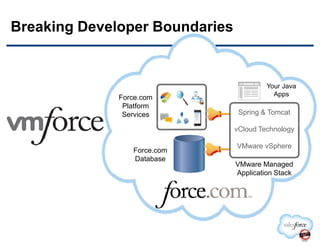
This document discusses the benefits and realities of cloud computing. It argues that true cloud computing provides major advantages over traditional on-premise software like lower costs, easier upgrades, and world-class security. However, some current cloud offerings do not provide true cloud benefits if they still require installing software or hardware. The document outlines how cloud computing can enable knowledge-based organizations and discusses examples of large companies successfully using cloud technologies.