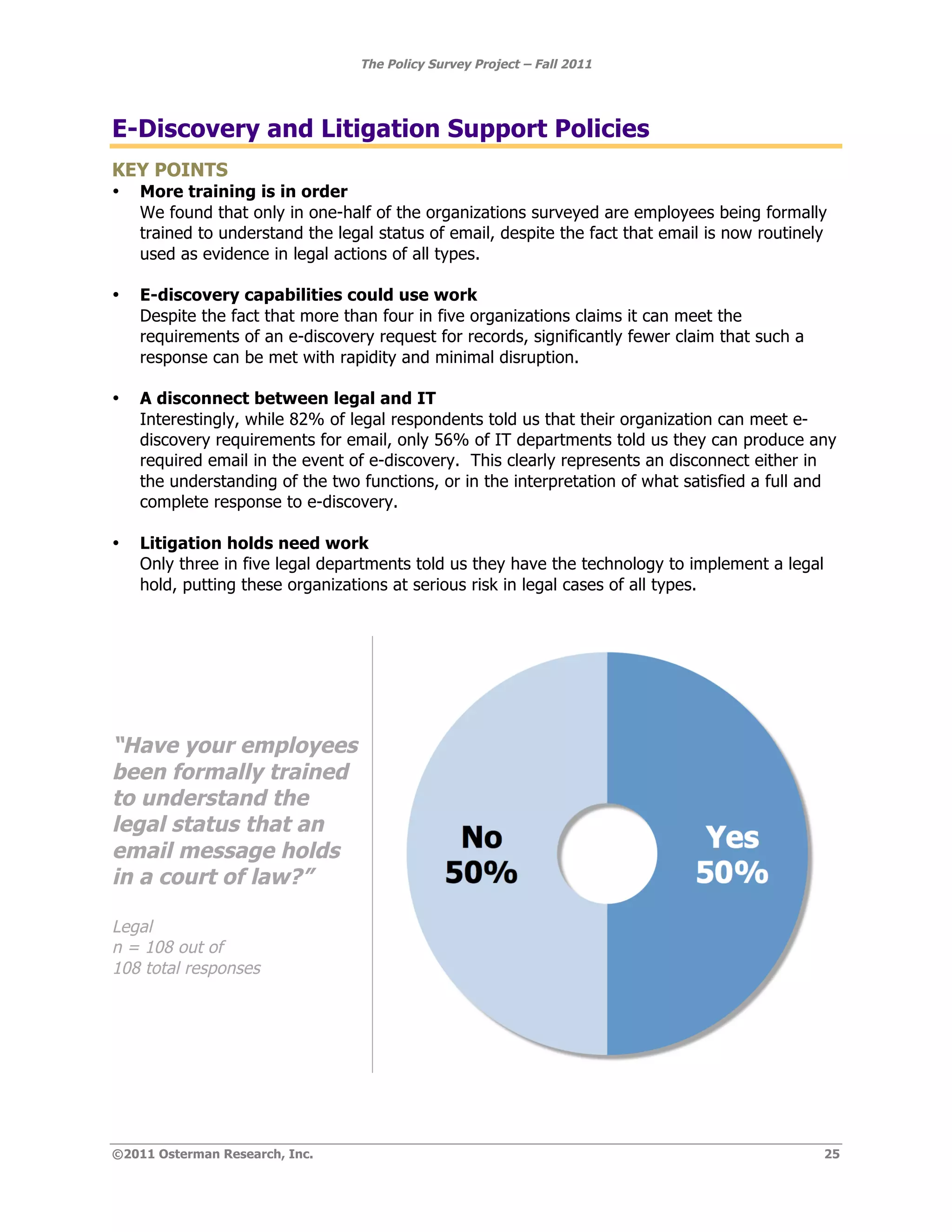
The document summarizes the key findings of a survey of 472 individuals from IT, HR, legal, and operations functions regarding their organizations' email and messaging policies. Some of the main findings include:
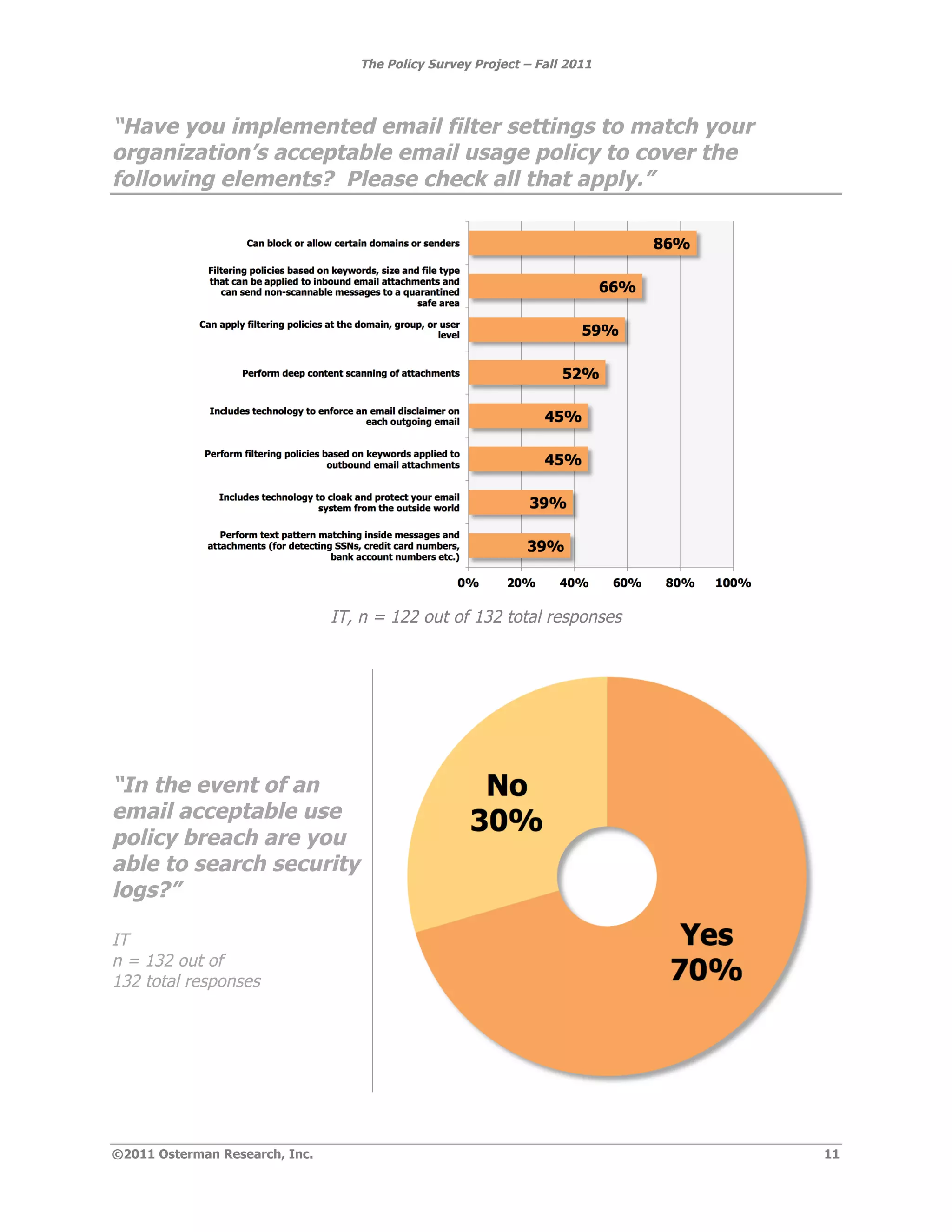
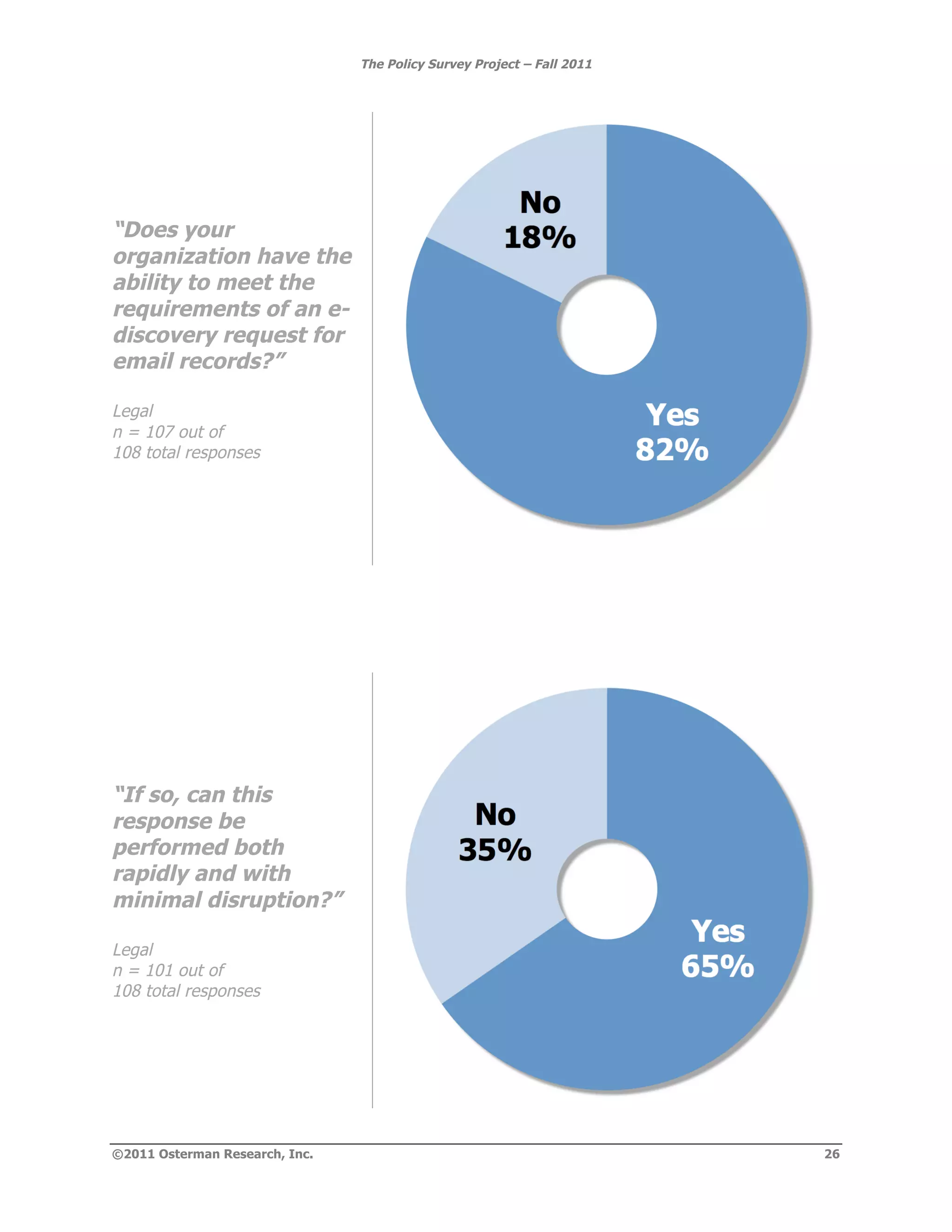
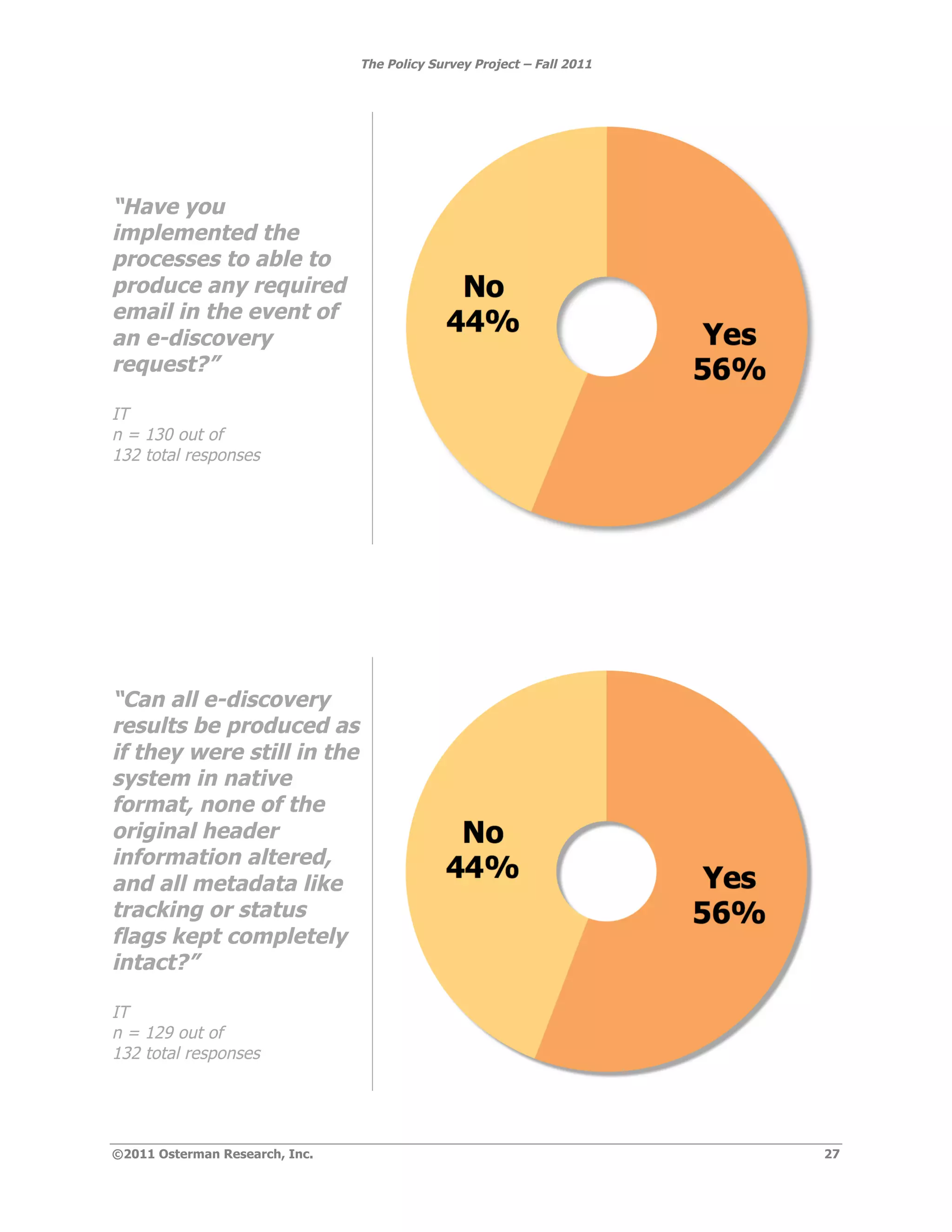
- Opinions on policies often diverge between functions due to lack of communication and different priorities.
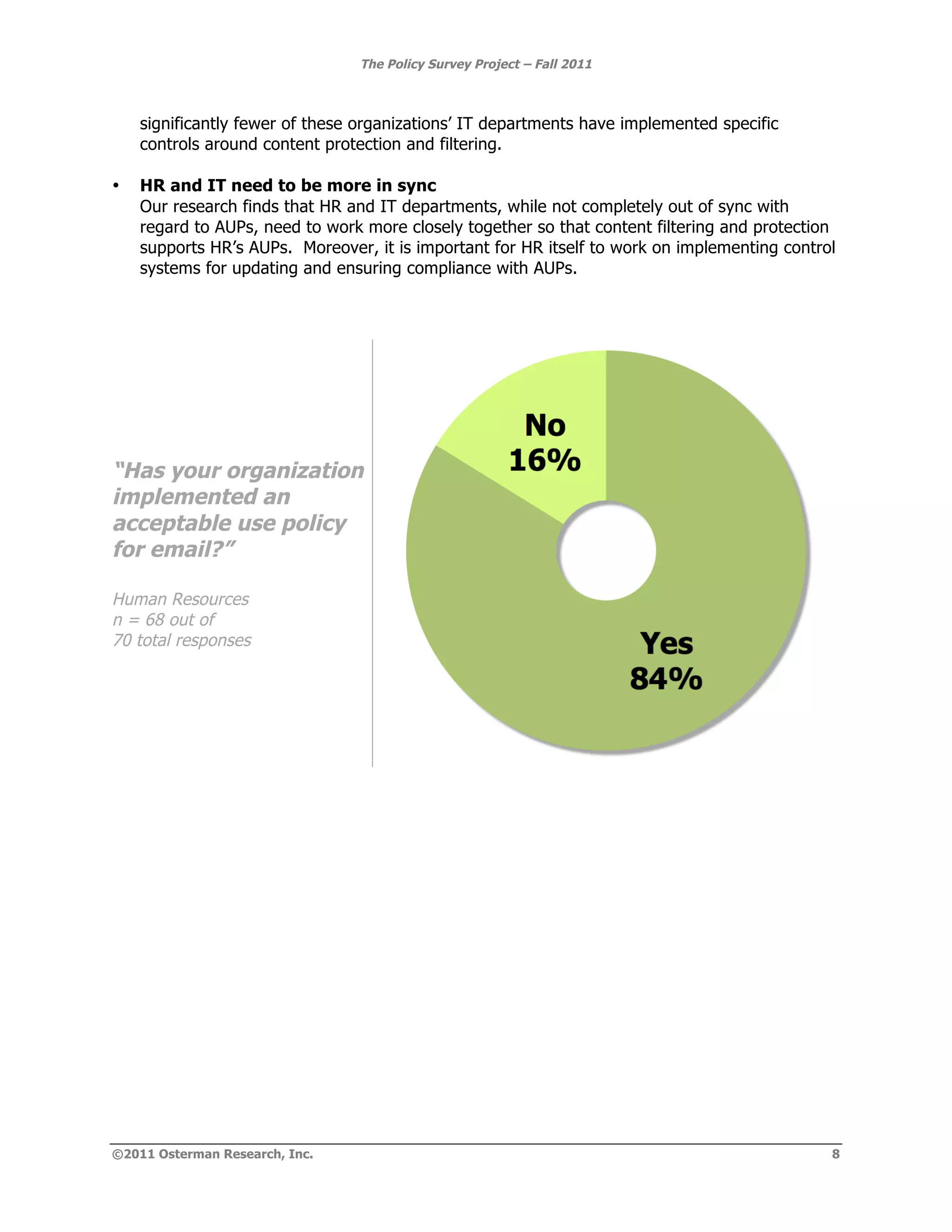
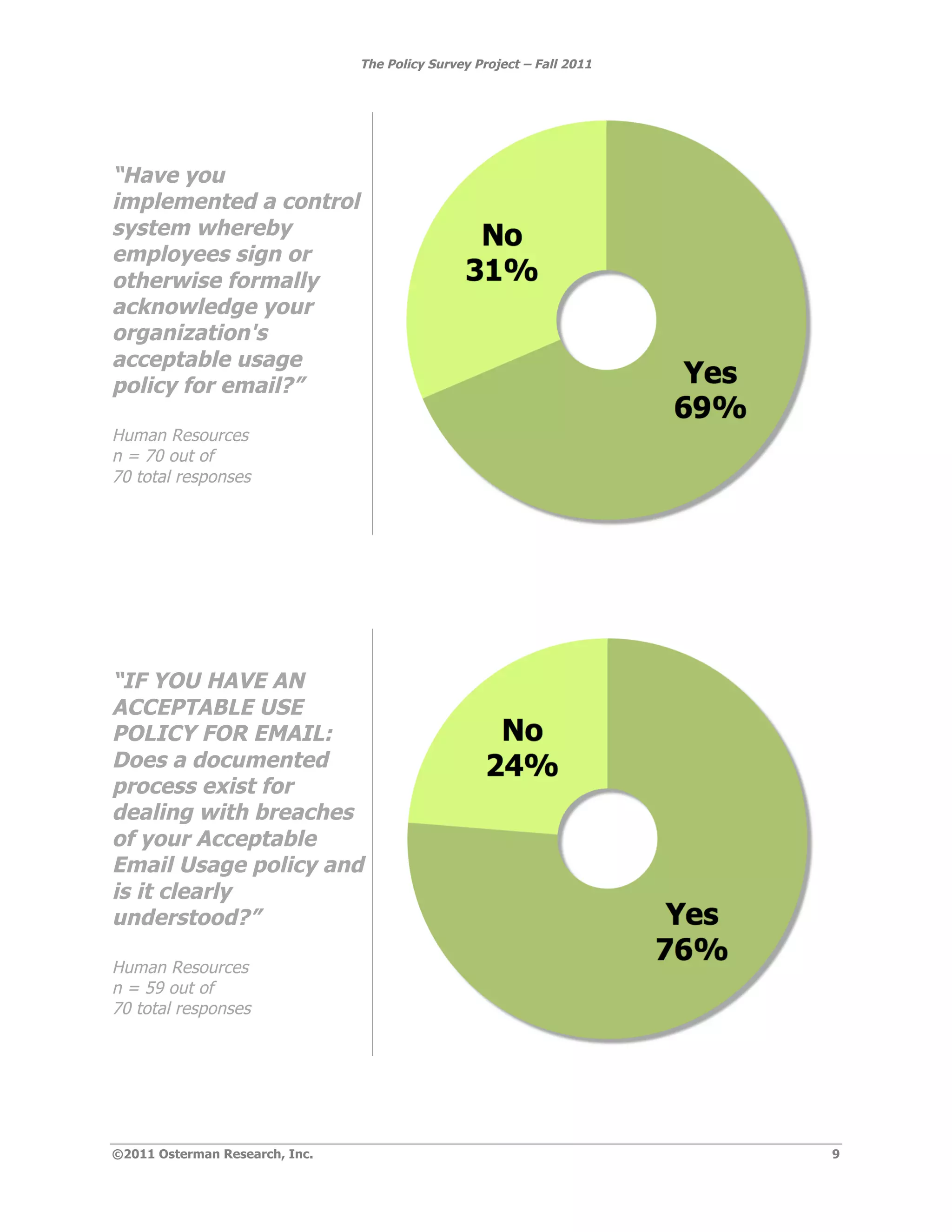
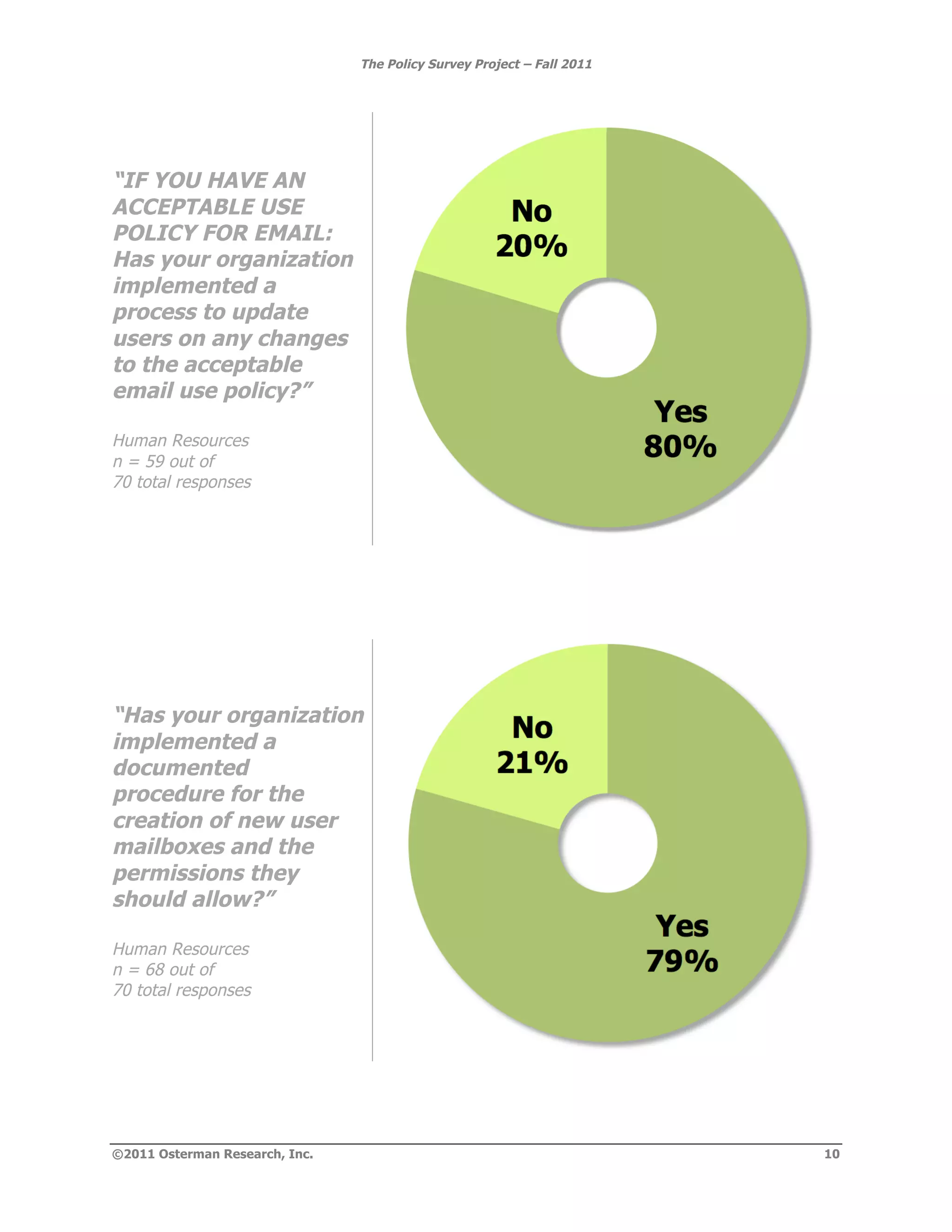
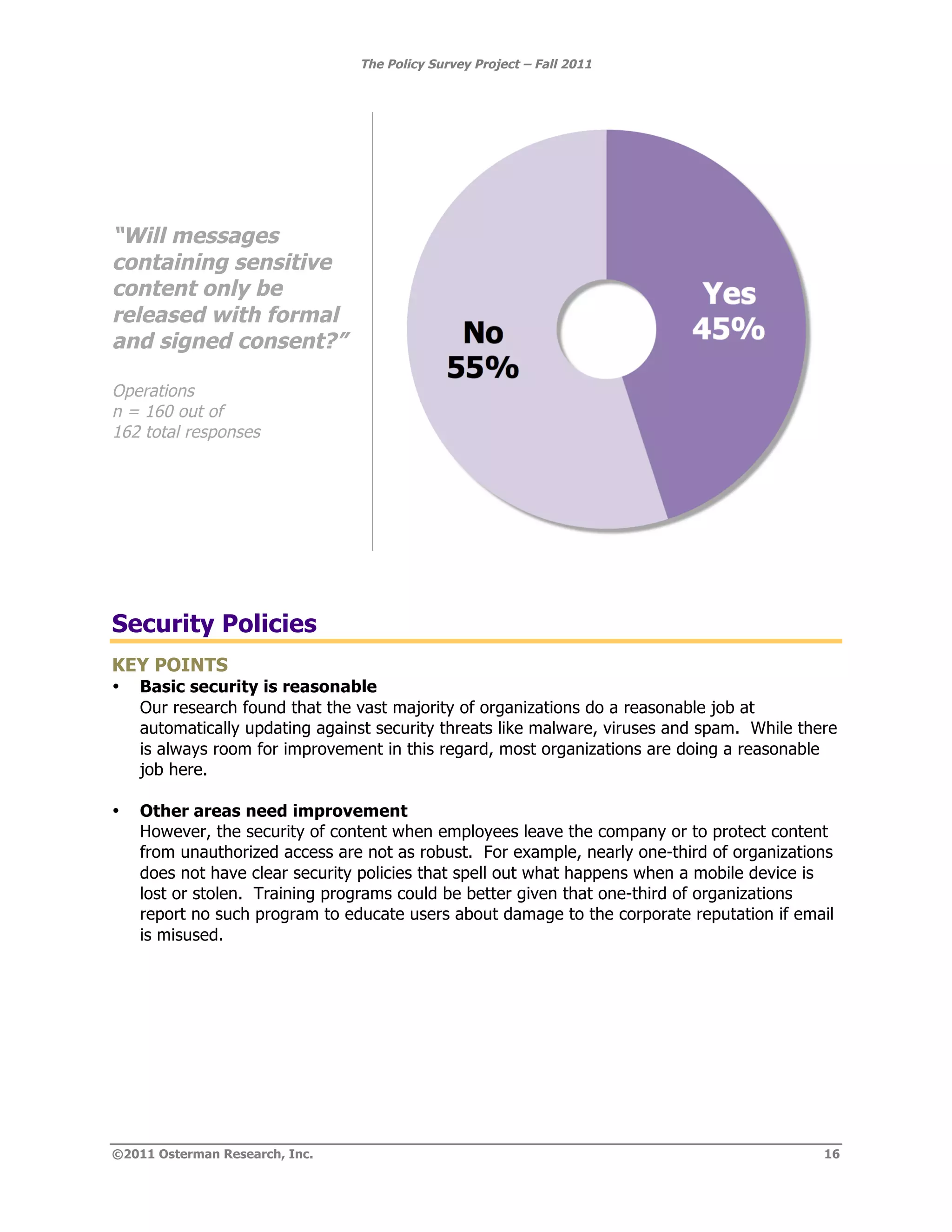
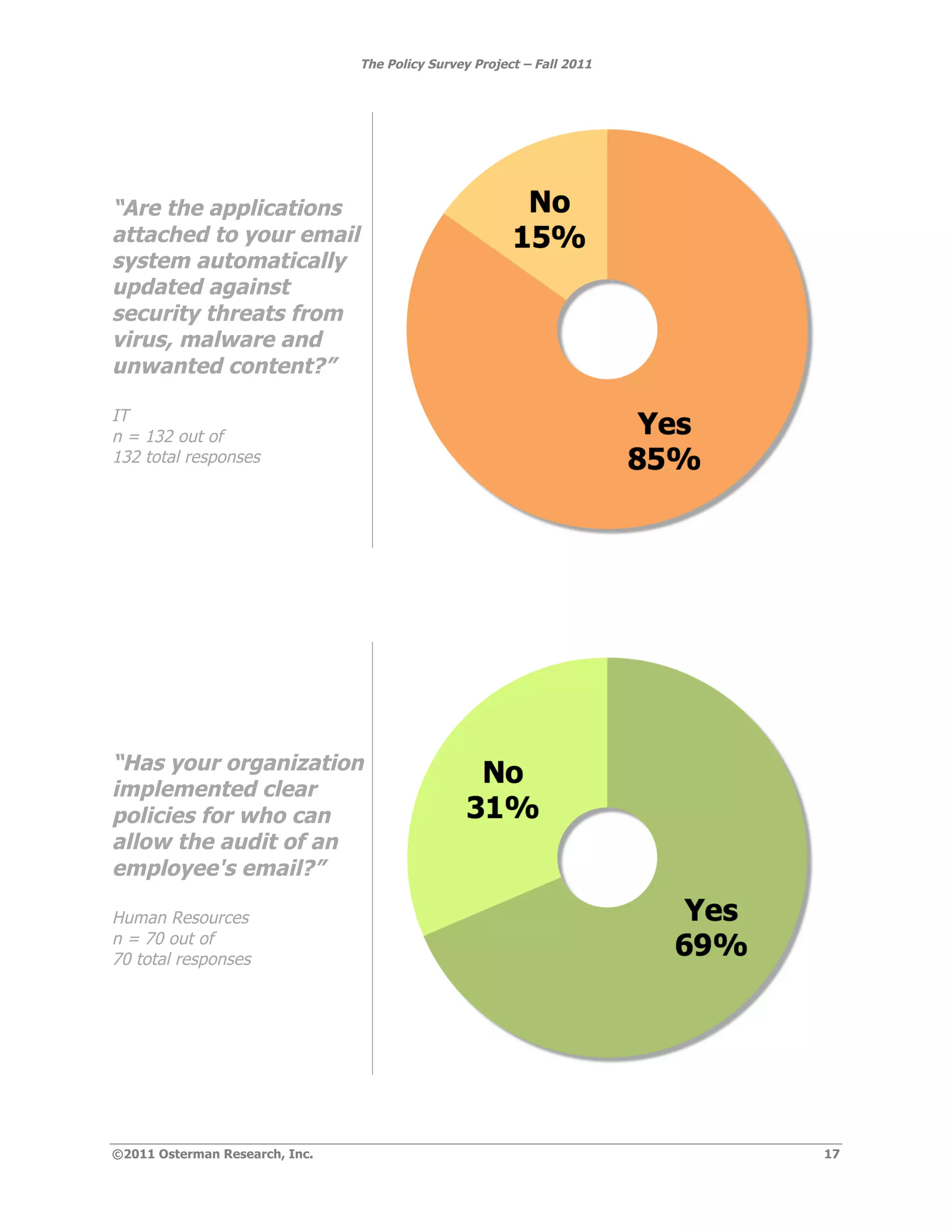
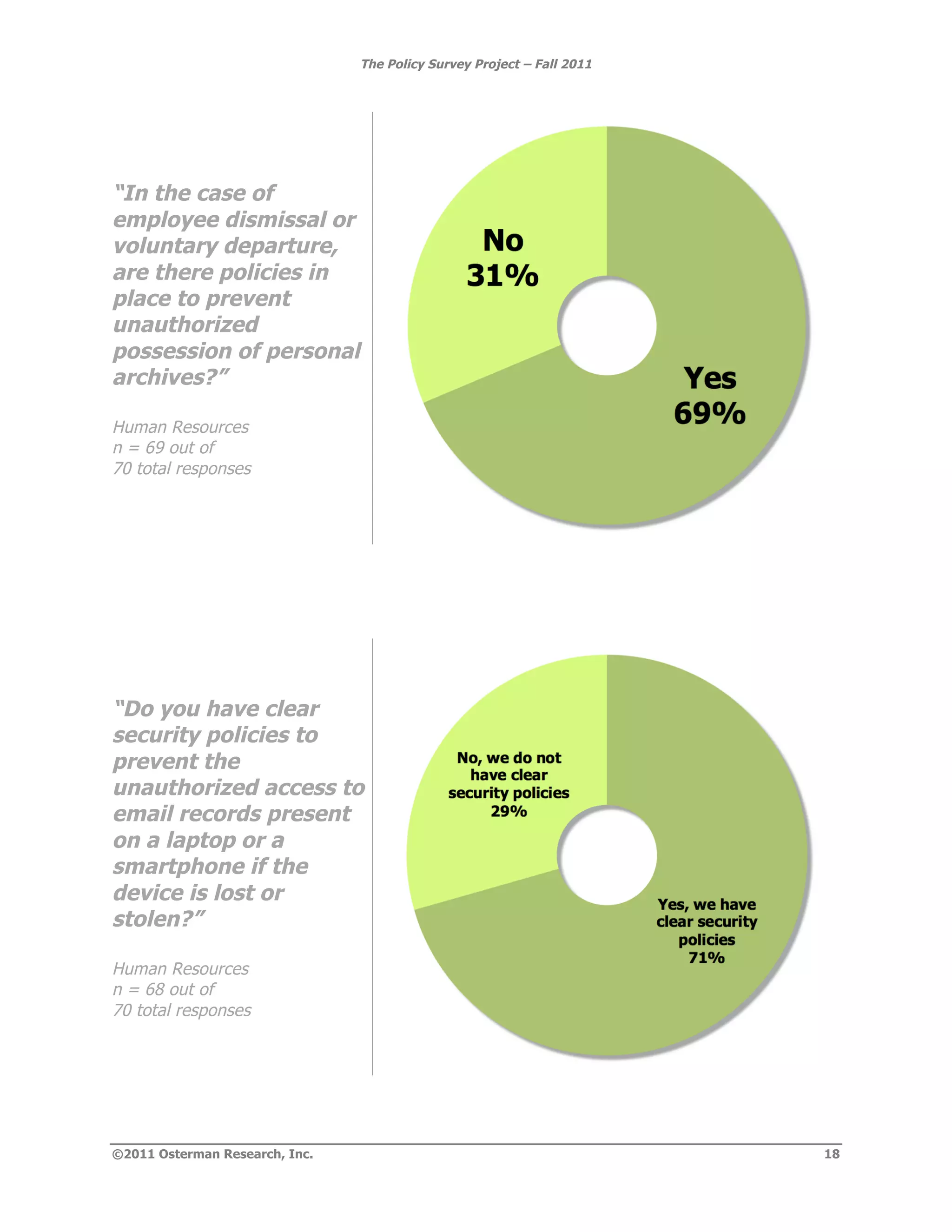
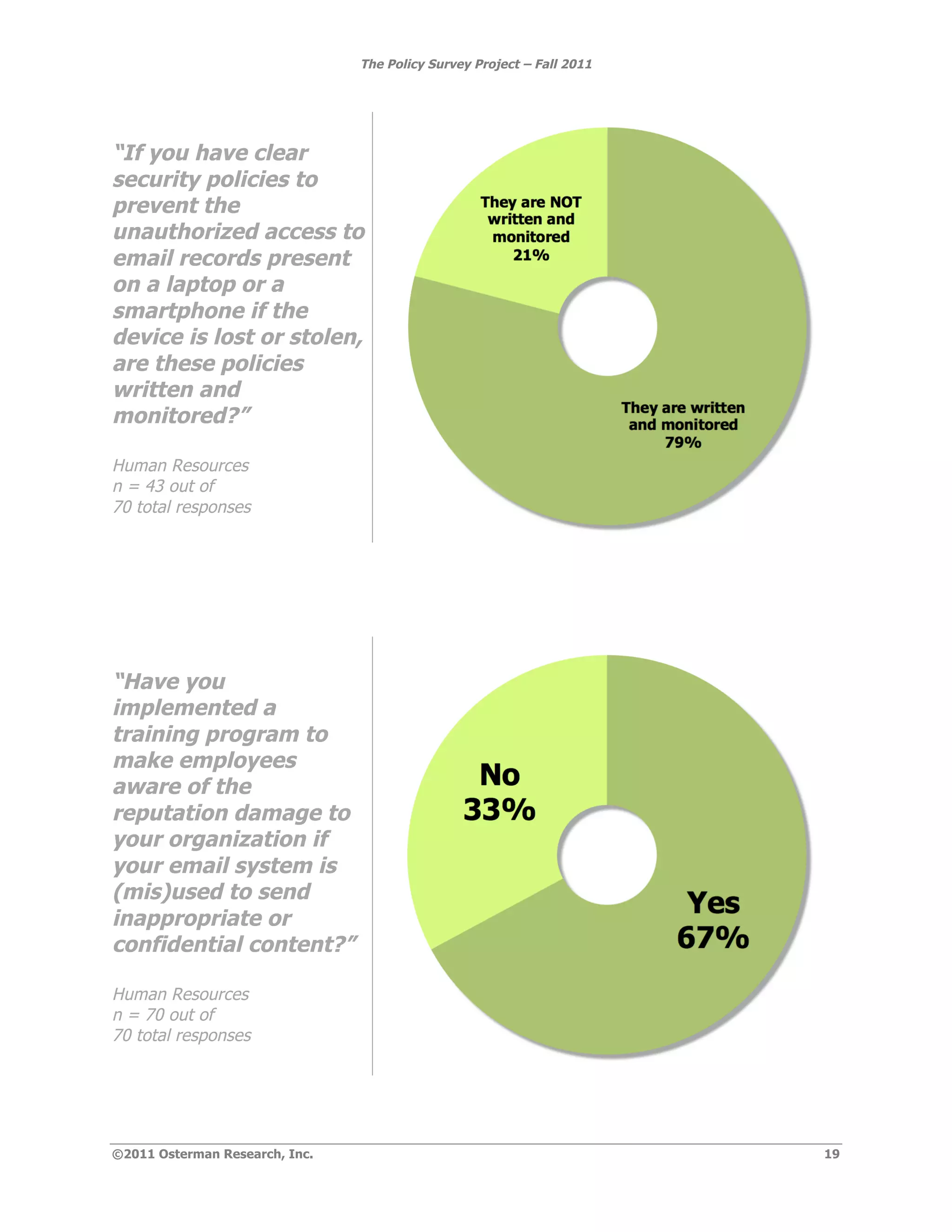
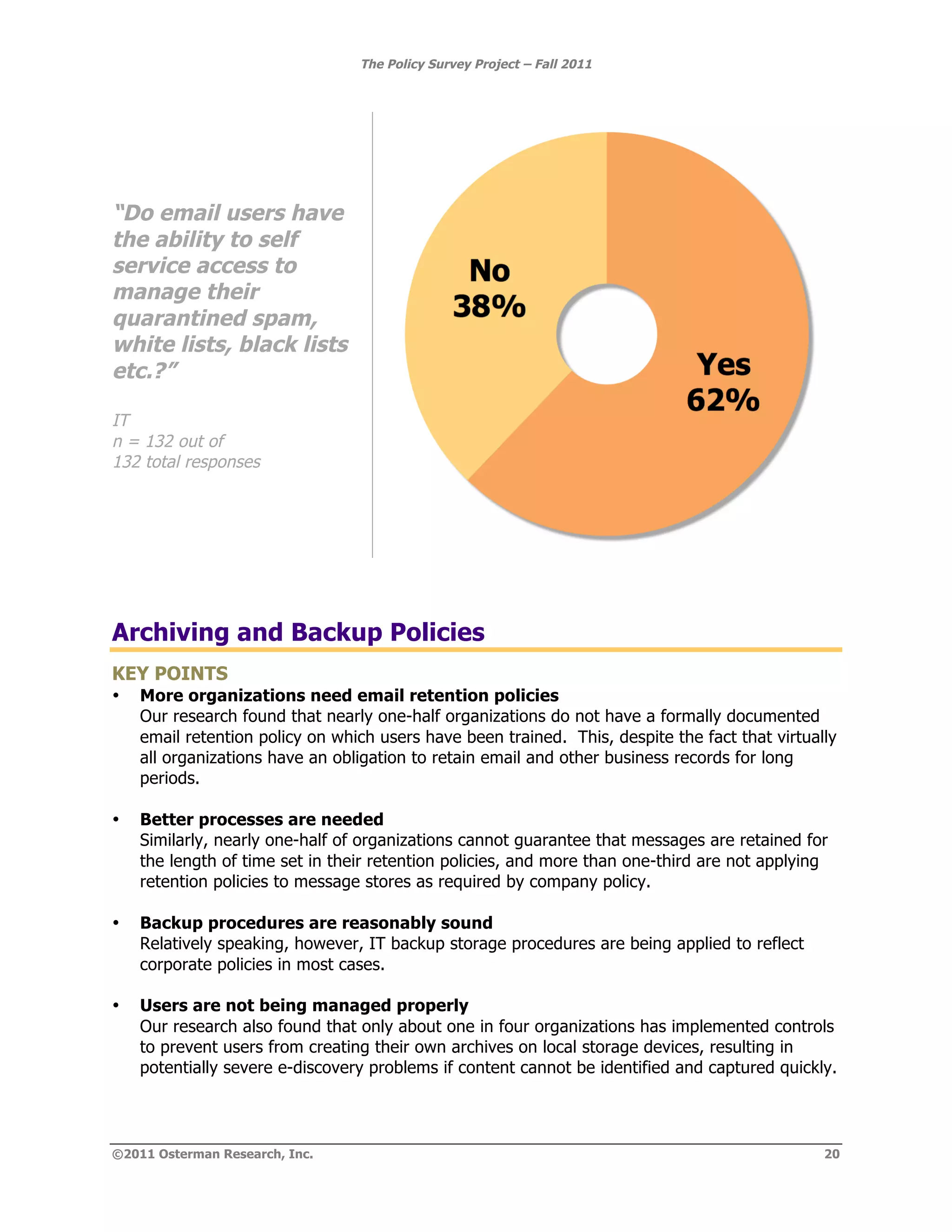
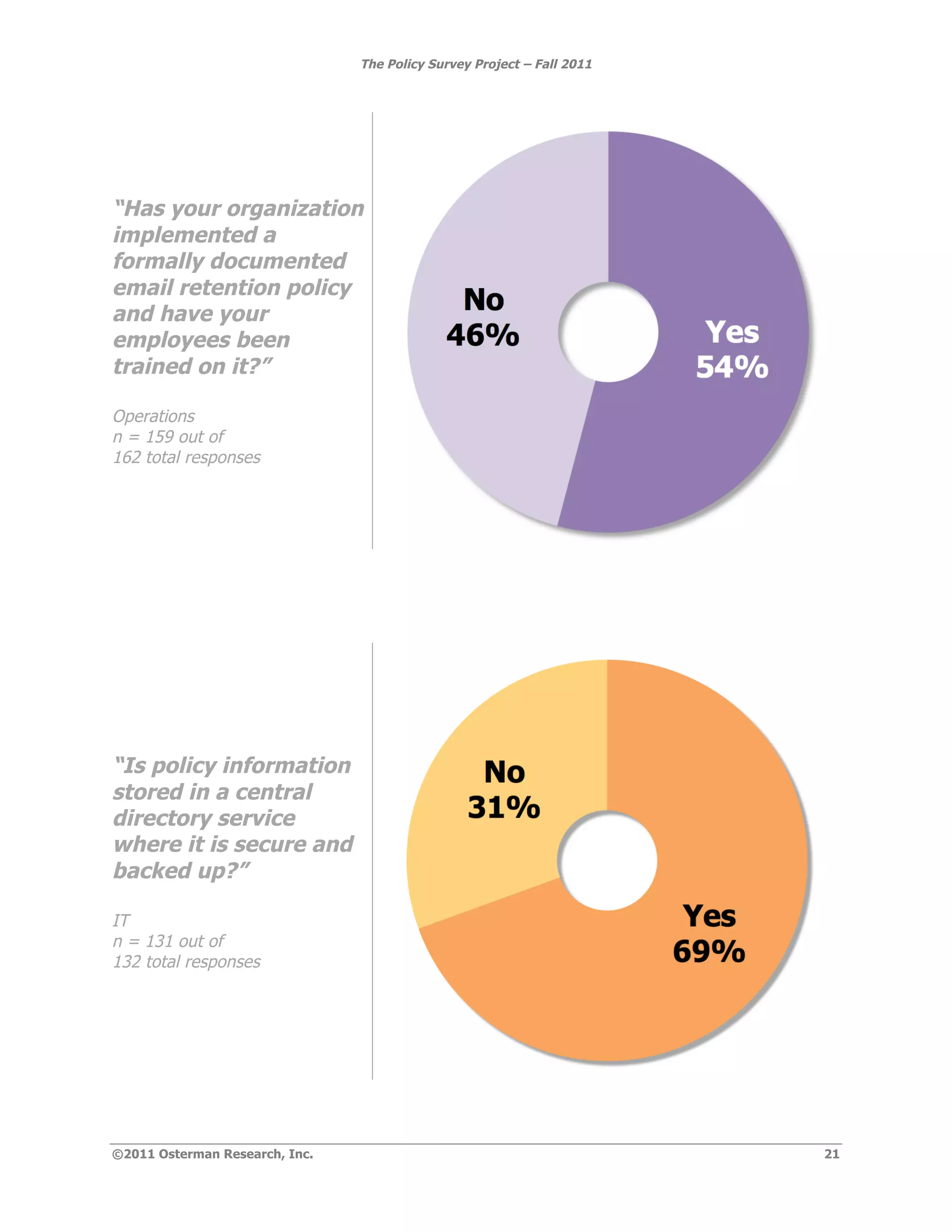
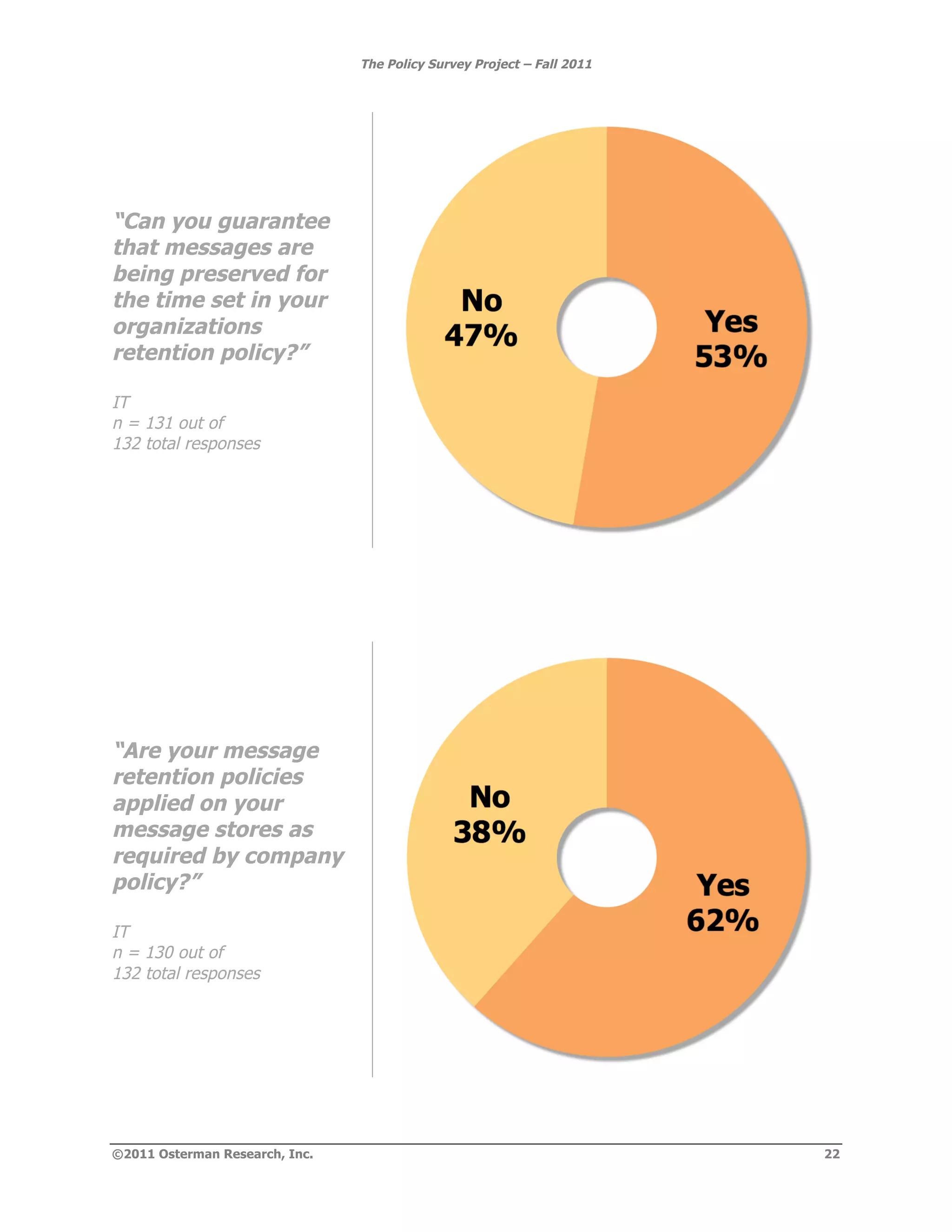
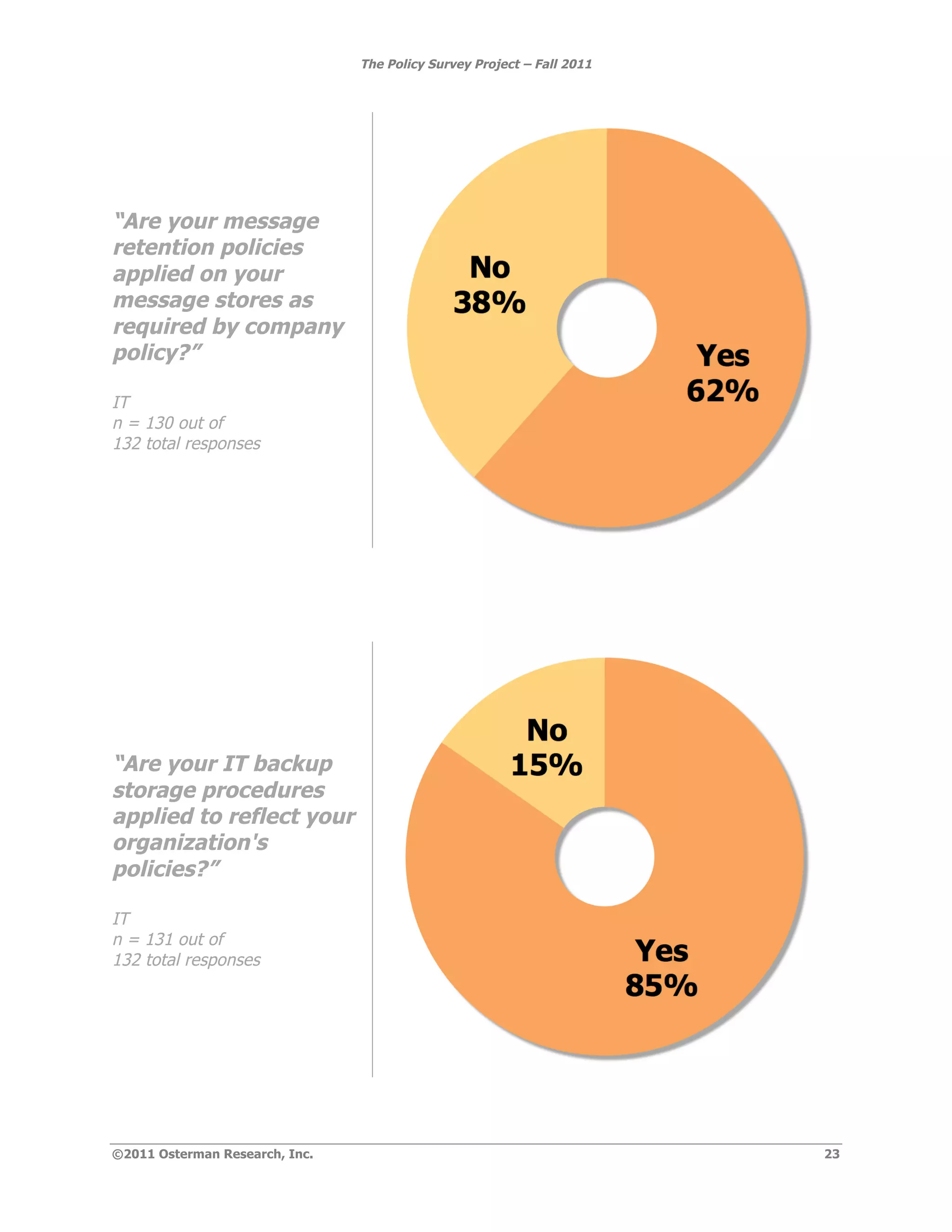
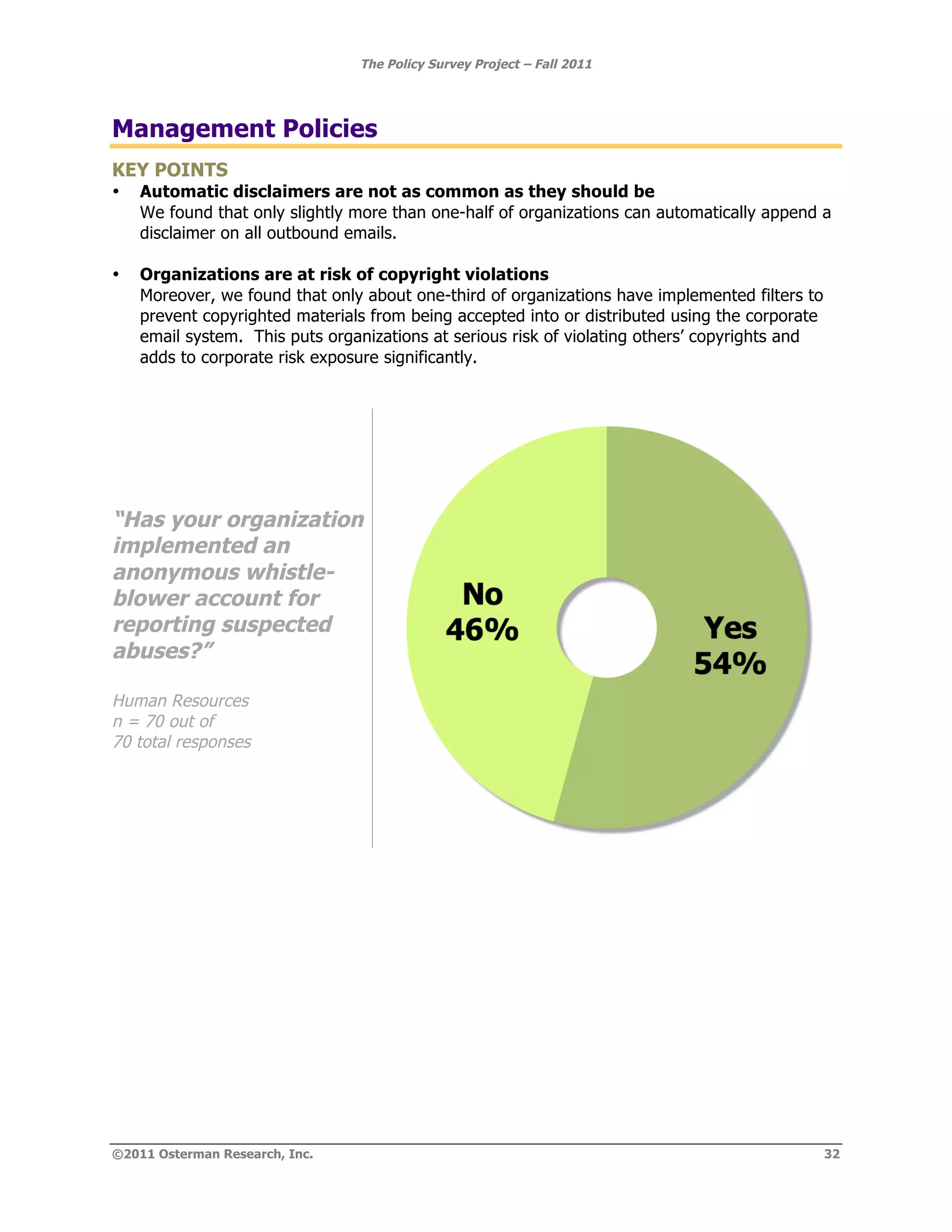
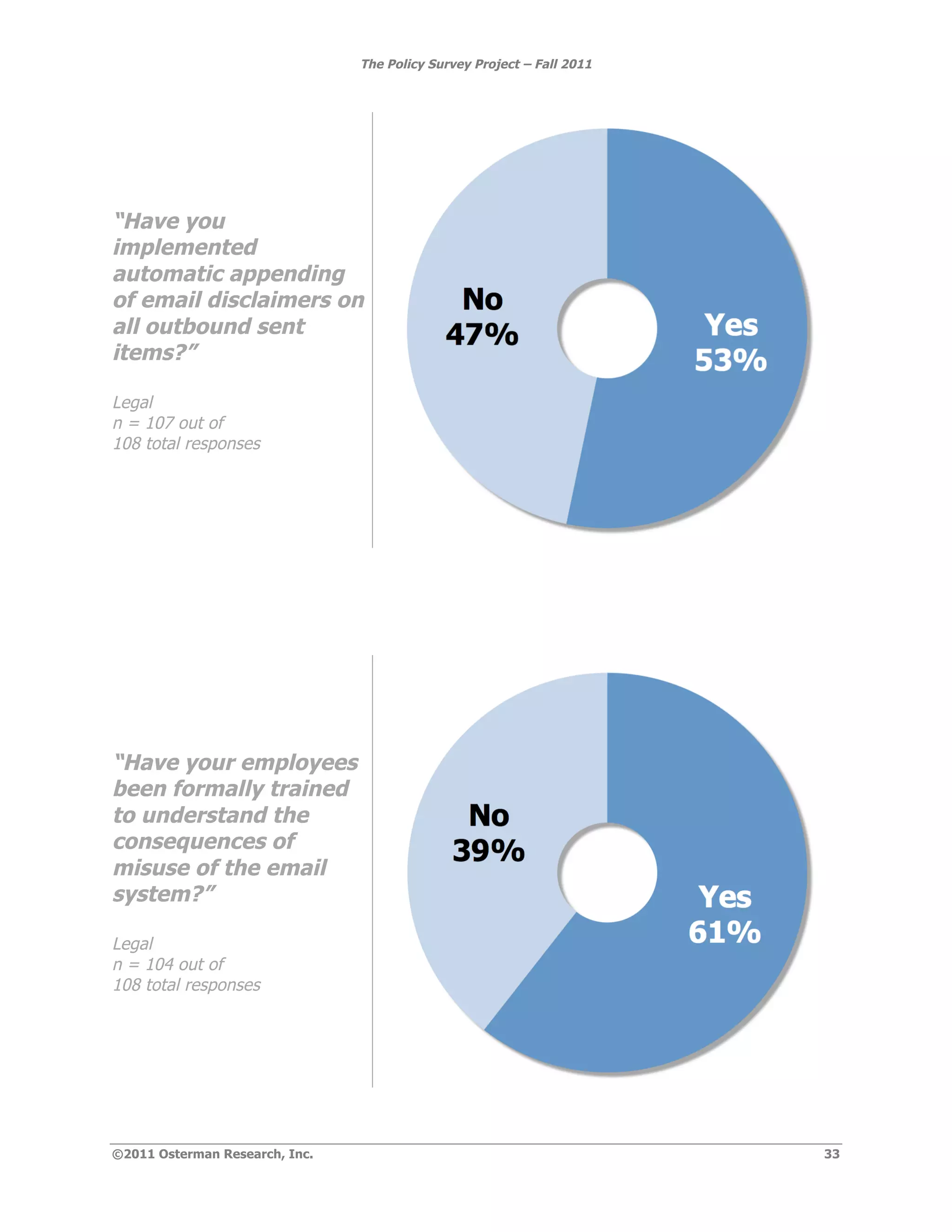
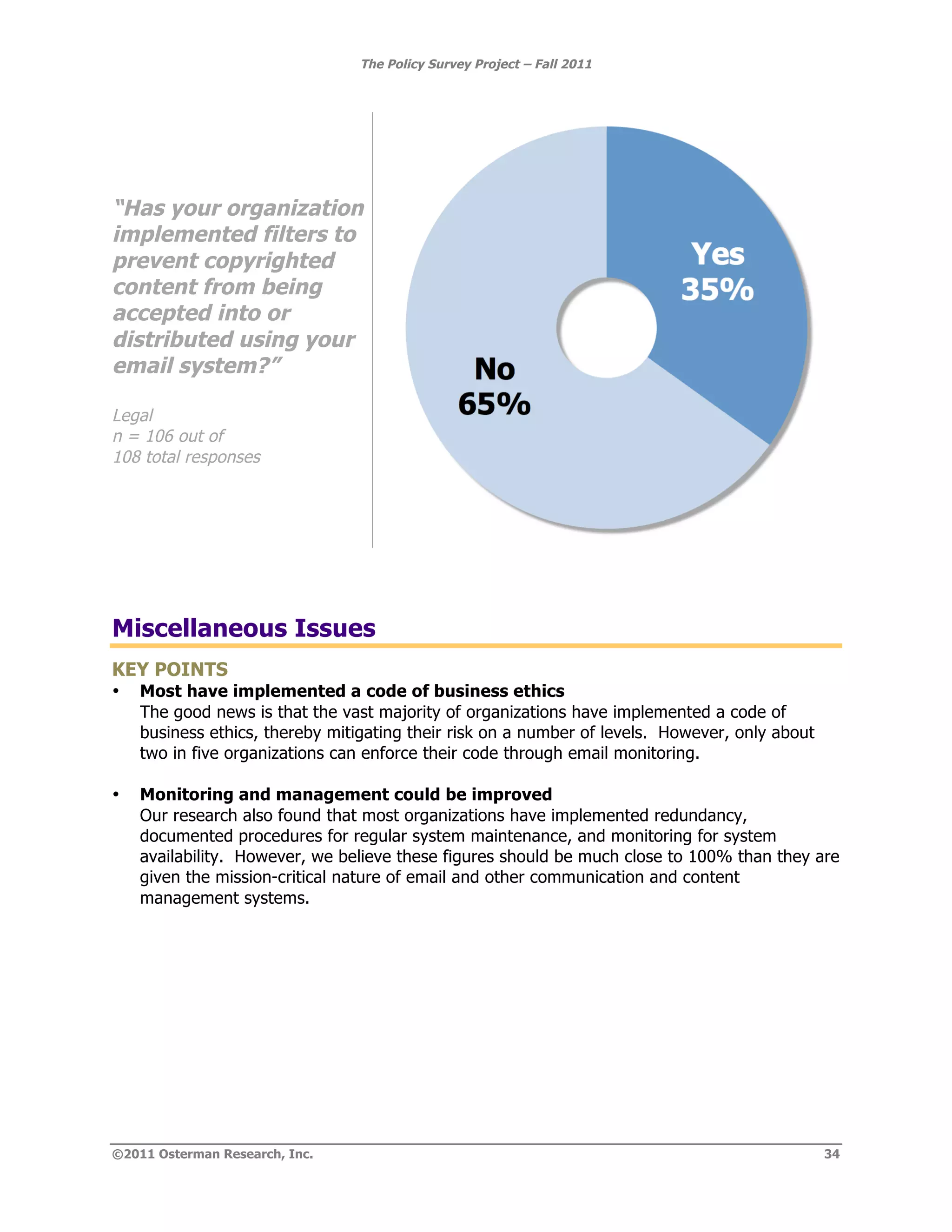
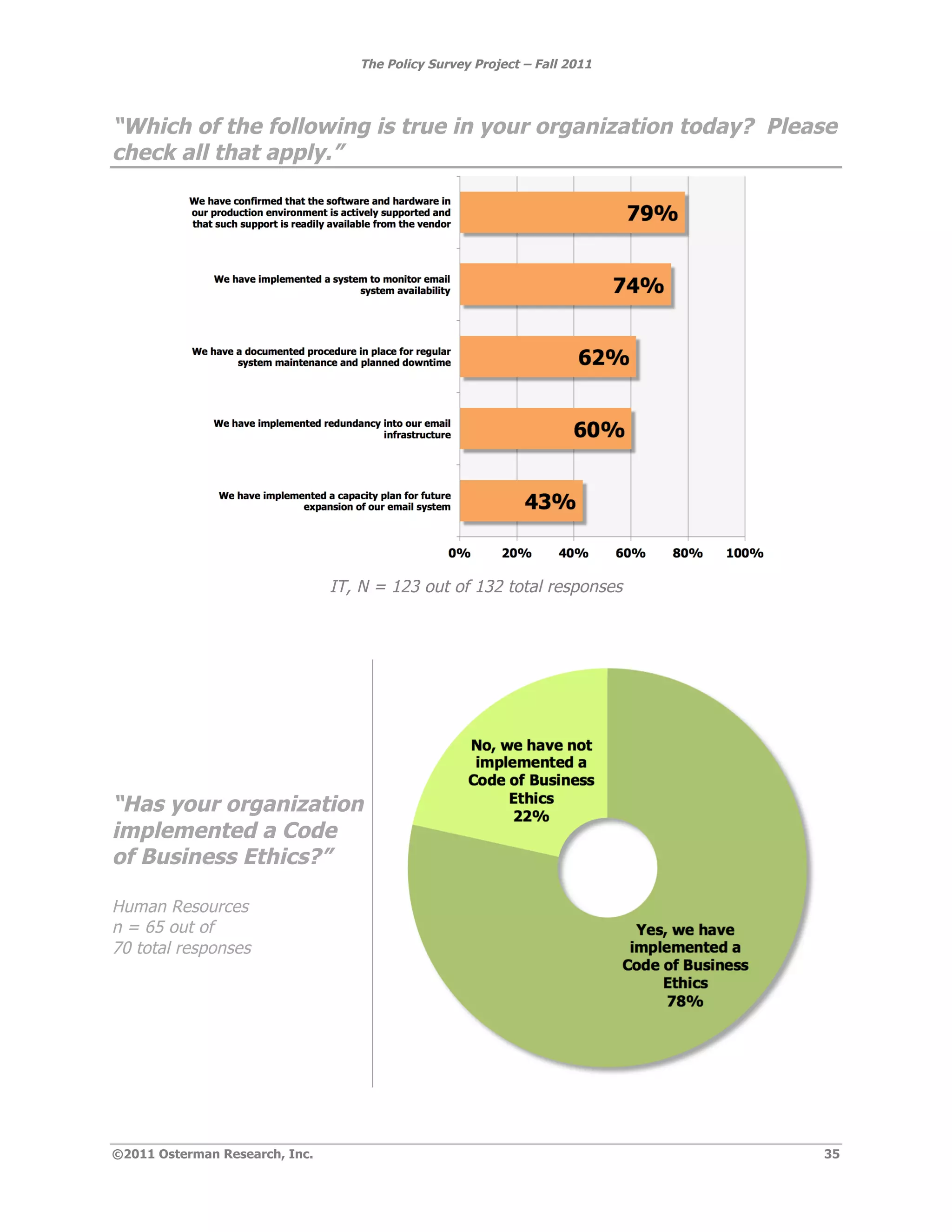
- Most organizations have implemented basic security policies like anti-malware but fewer have formal email retention or acceptable use policies.
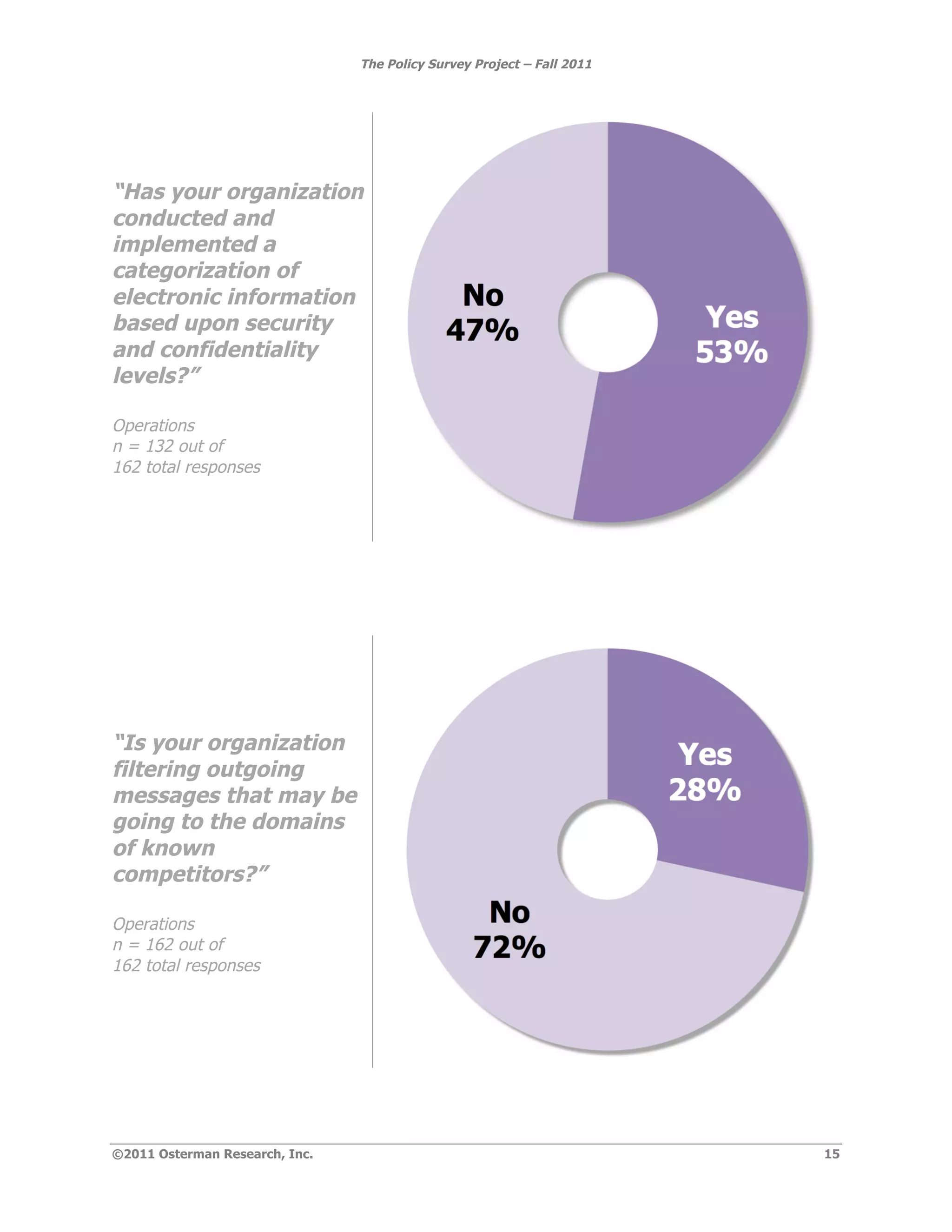
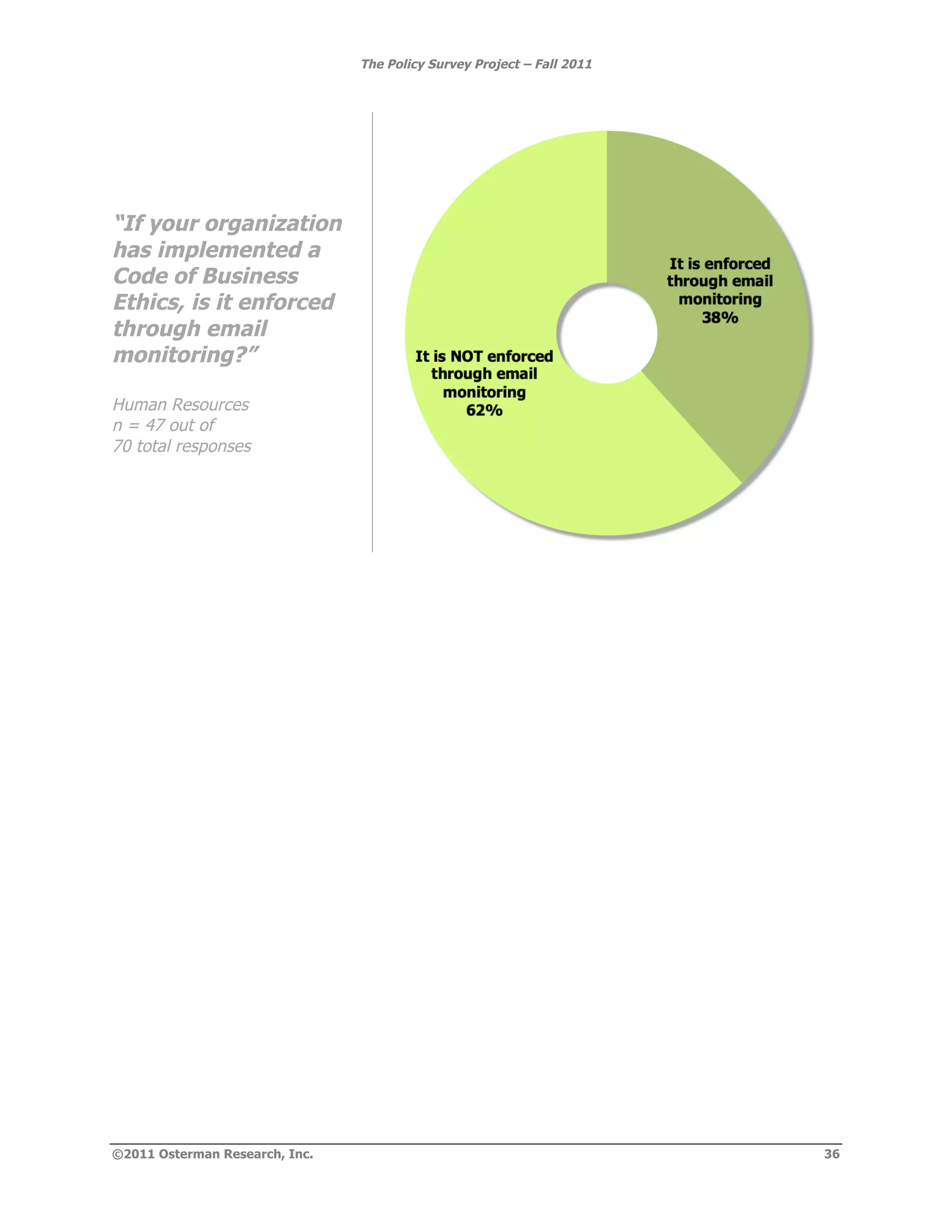
- Technology to support policies is often deployed but not consistently enforced or audited.
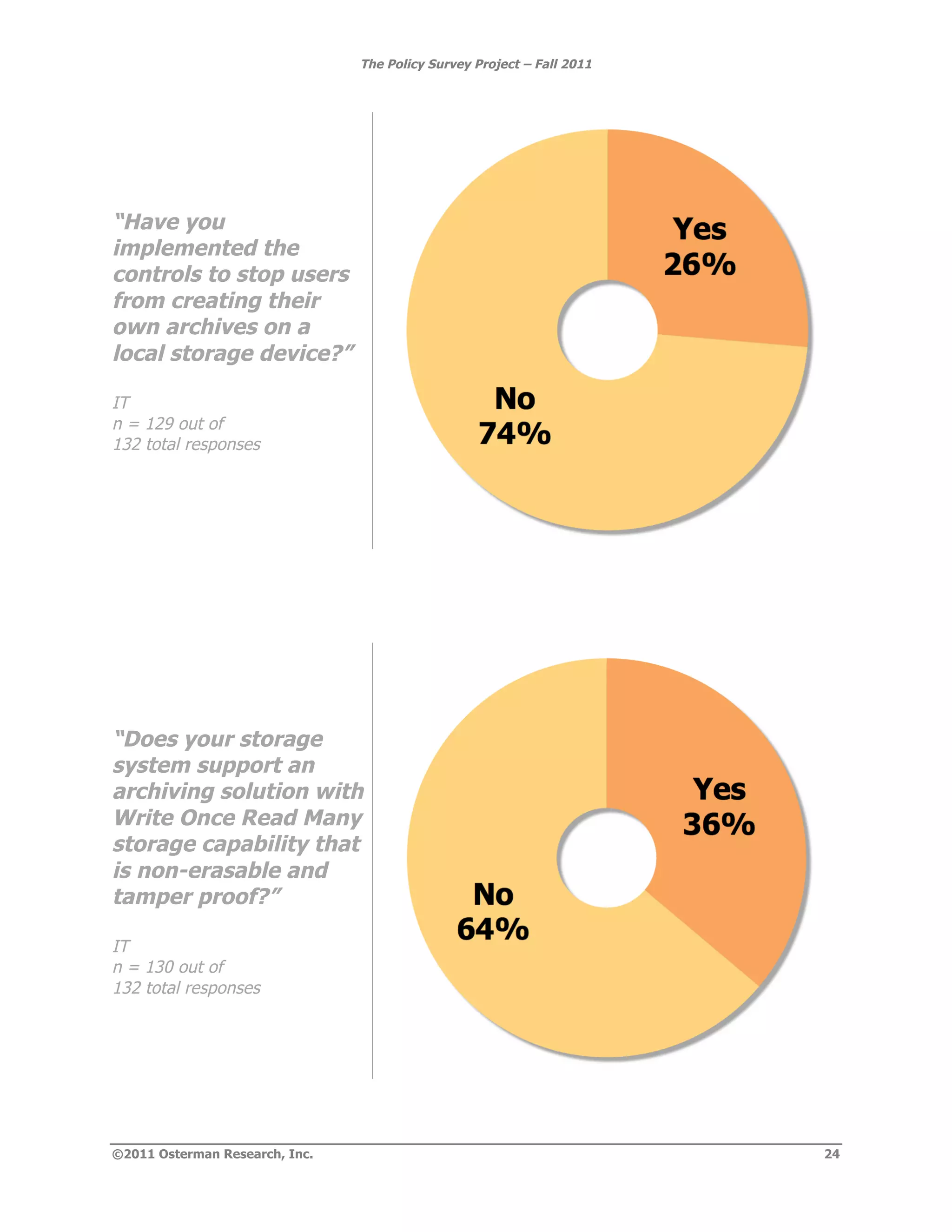
- Content is frequently not centrally stored, increasing risks for e-discovery and compliance.
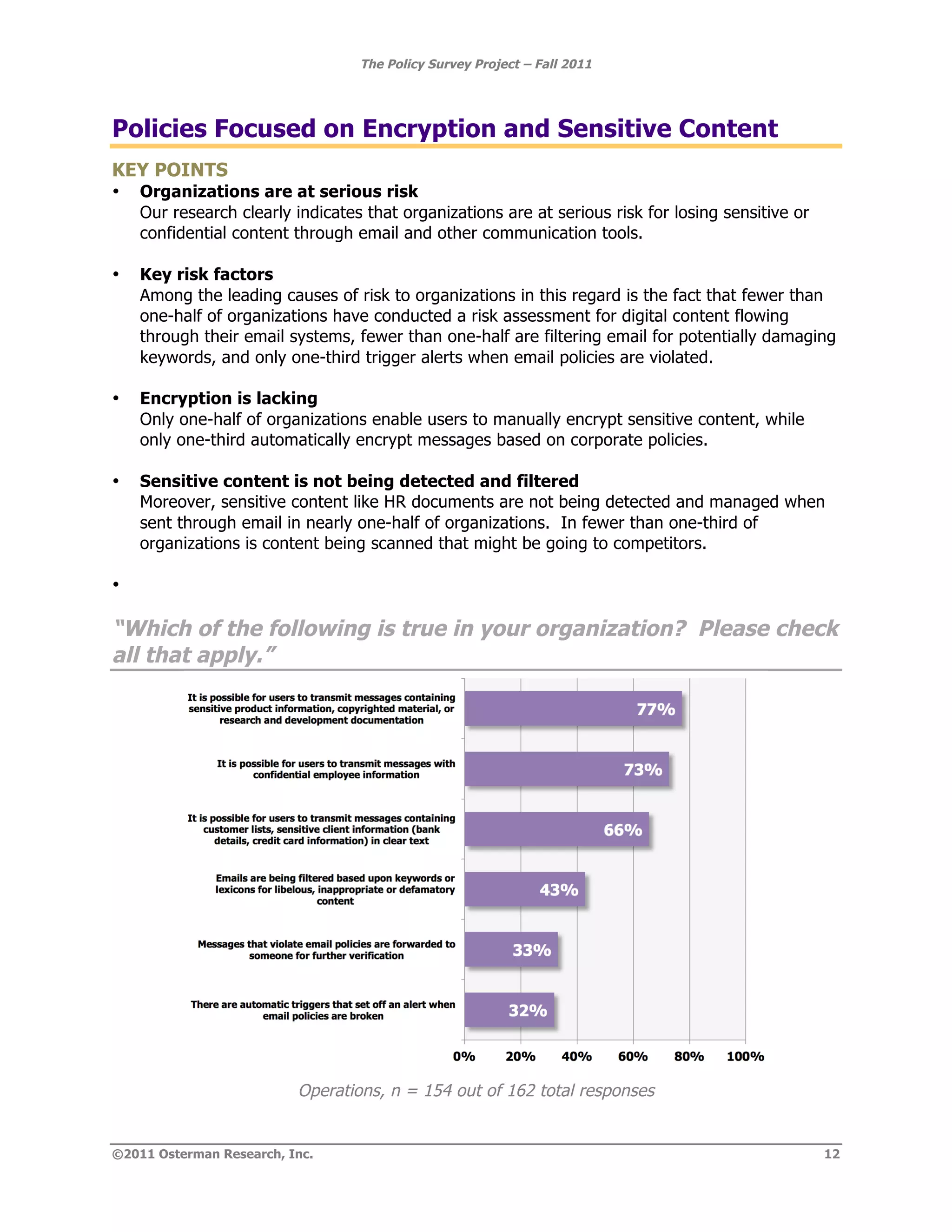
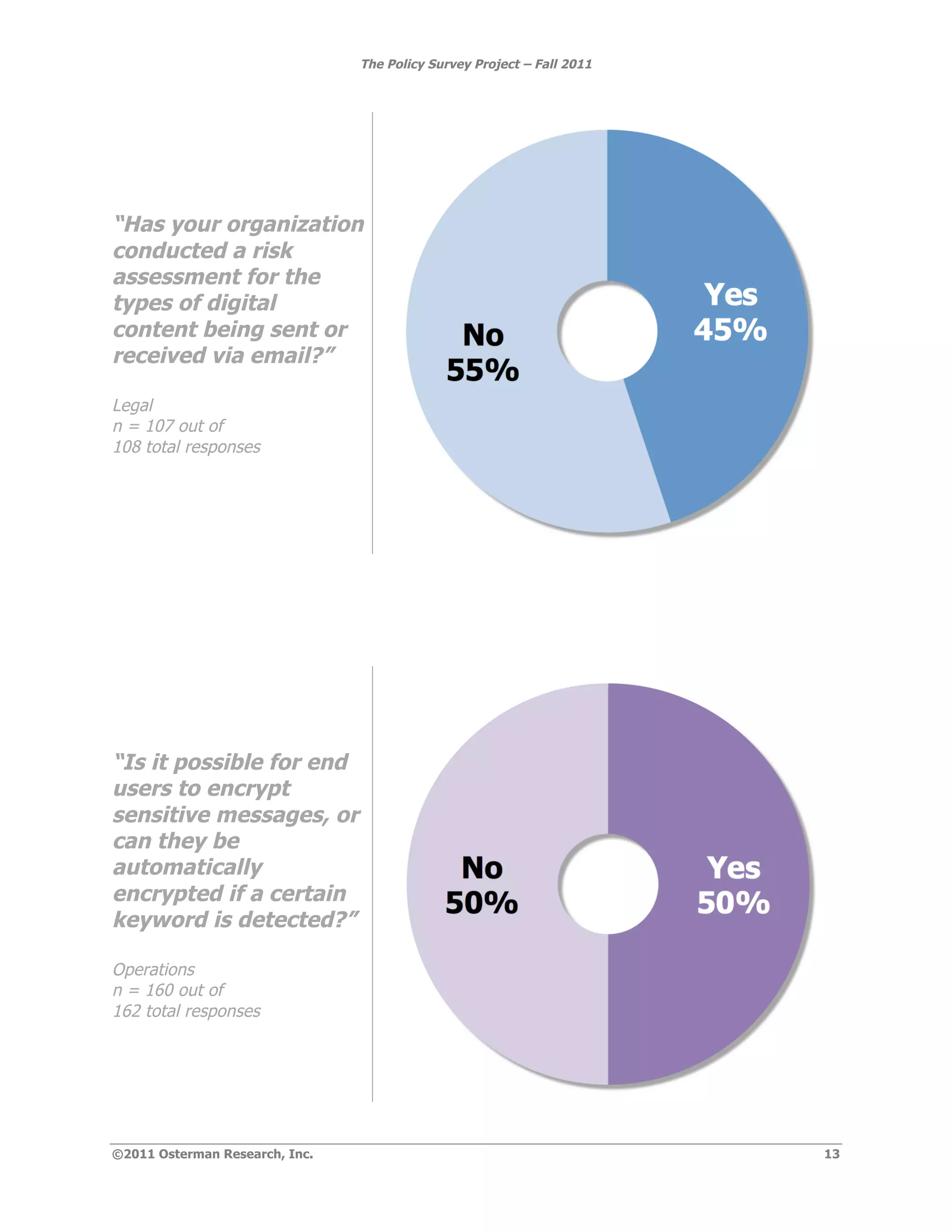
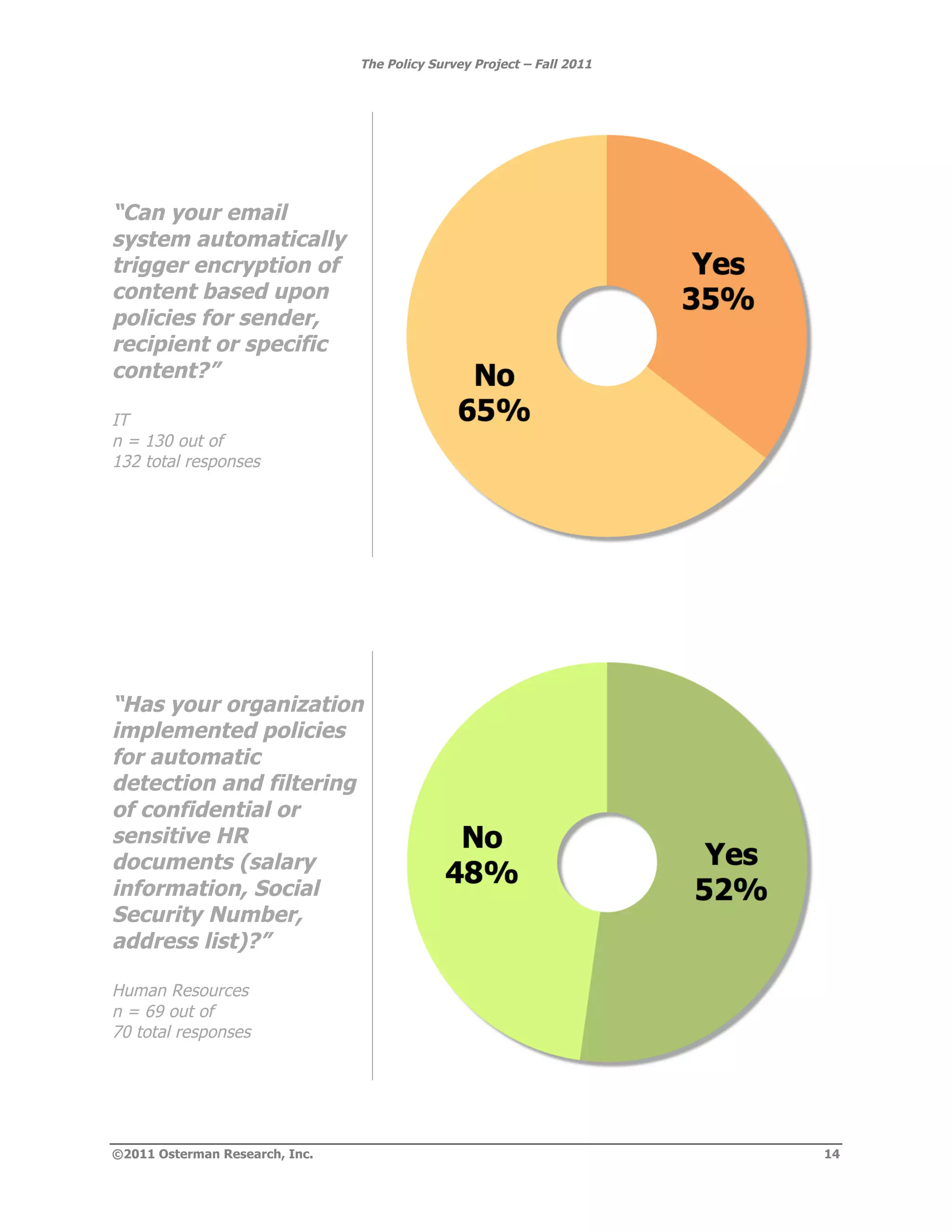
- Encryption and secure storage capabilities are not universally implemented.