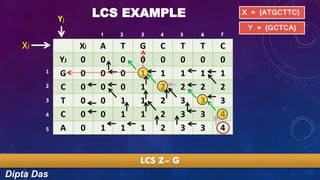
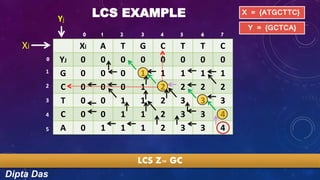
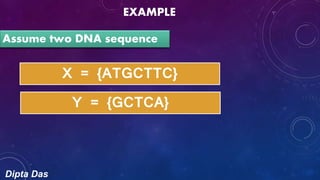
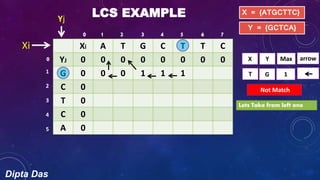
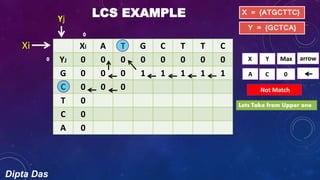
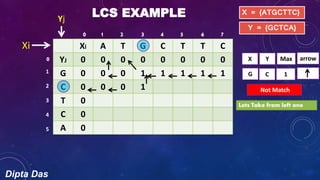
The document discusses the longest common subsequence (LCS) problem. It provides an example to calculate the LCS of two DNA sequences, X={ATGCTTC} and Y={GCTCA}, using a dynamic programming algorithm. The algorithm populates a 2D matrix by incrementing values when characters match and otherwise copying values from above or left. The LCS is read from the populated matrix as GCTC, demonstrating the method to find the longest common subsequence of two sequences.


![Dipta Das
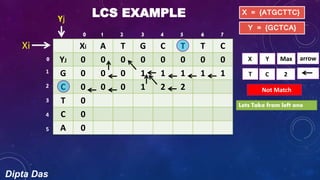
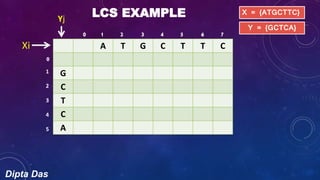
LCS EXAMPLE
A T G C T T C
0 0 0 0 0 0 0 0
G 0
C 0
T 0
C 0
A 0
X = {ATGCTTC}
Y = {GCTCA}
1 2 3 4 5 6 7
1
2
3
4
5
Yj
Xi
0
0
Z[j,i]
Here I = 1, j = 1
Z[1,1]](https://image.slidesharecdn.com/longestcommonsubsequence-151208231702-lva1-app6891/85/Longest-common-subsequence-8-320.jpg)
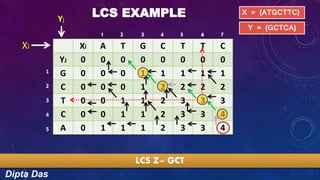
![Dipta Das
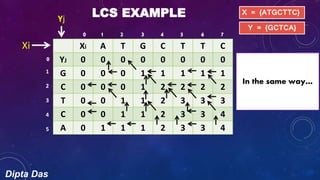
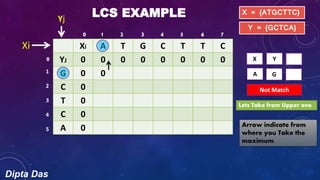
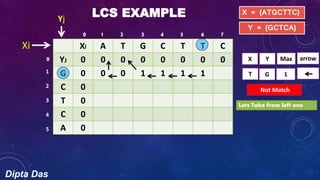
LCS EXAMPLE
Xi A T G C T T C
YJ 0 0 0 0 0 0 0 0
G 0
C 0
T 0
C 0
A 0
X = {ATGCTTC}
Y = {GCTCAGA}
Yj
Xi
X Y
A G
Not Match
Maximum of
two box
z[J-1, i] and
[J, i-1]
1 2 3 4 5 6 7
1
2
3
4
5
0
0
Z[1,1]
Z[j-1, i]=Z[1-1, 1]= Z[0,1]
Z[j, i-1]=Z[1, 1-1]= Z[1,0]](https://image.slidesharecdn.com/longestcommonsubsequence-151208231702-lva1-app6891/85/Longest-common-subsequence-9-320.jpg)
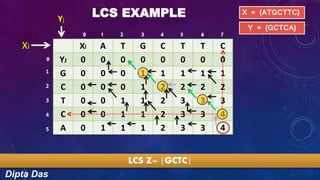
![Dipta Das
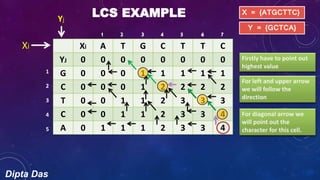
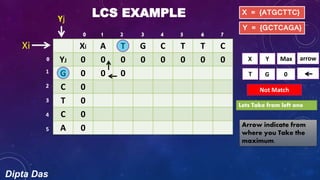
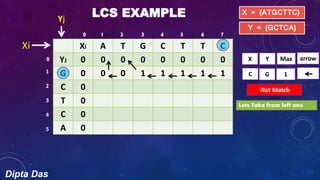
LCS EXAMPLE
Xi A T G C T T C
YJ 0 0 0 0 0 0 0 0
G 0 0 0
C 0
T 0
C 0
A 0
X = {ATGCTTC}
Y = {GCTCAGA}
Yj
Xi
X Y Max
G G
Match
arrow
When match arrow will
be diagonal because we
will increment the
value of this cell
Z[i-1, j-1] + 10 = 1
1 2 3 4 5 6 7
1
2
3
4
5
0
0](https://image.slidesharecdn.com/longestcommonsubsequence-151208231702-lva1-app6891/85/Longest-common-subsequence-12-320.jpg)
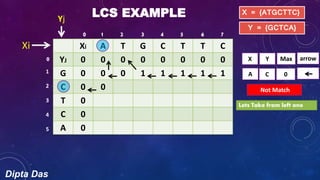
![Dipta Das
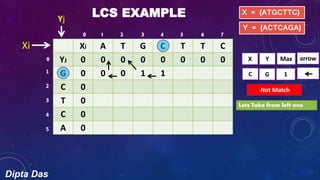
LCS EXAMPLE
Xi A T G C T T C
YJ 0 0 0 0 0 0 0 0
G 0 0 0 1
C 0
T 0
C 0
A 0
X = {ATGCTTC}
Y = {GCTCA}
Yj
Xi
X Y Max
G G
Match
arrow
Incremented value X[i-1] Y[j-1]
1 2 3 4 5 6 7
1
2
3
4
5
0
0
Z[I,j] = Z[3,1]](https://image.slidesharecdn.com/longestcommonsubsequence-151208231702-lva1-app6891/85/Longest-common-subsequence-13-320.jpg)
![Dipta Das
LCS EXAMPLE
Xi A T G C T T C
YJ 0 0 0 0 0 0 0 0
G 0 0 0 1 1 1 1 1
C 0 0 0 1 2
T 0
C 0
A 0
X = {ATGCTTC}
Y = {GCTCA}
Yj
Xi
X Y Max
C C
Match
arrow
Increment Z[i-1,j-1]
1 2 3 4 5 6 7
1
2
3
4
5
0
0](https://image.slidesharecdn.com/longestcommonsubsequence-151208231702-lva1-app6891/85/Longest-common-subsequence-21-320.jpg)