LiPari_Assignment8
•Download as DOCX, PDF•
0 likes•104 views
Malware called SYNful Knock has been hijacking internet routers by exploiting default login credentials, allowing threat actors to integrate their own operating system on the routers. Over 200 routers across 31 countries have been infected so far. With access to the routers, threat actors can view all network traffic and use the routers to launch further cyber attacks. Countermeasures have been ineffective due to the new and complex nature of these router hijacking attacks.
Report
Share
Report
Share
Recommended
IoT Cyber+Physical+Social Engineering Attack Security (v0.1.6 / sep2020)

Work-in-Progress!
IoT Cyber+Physical+Social Security
An encyclopedic compendium of tools, techniques, and practices to defend systems that sit at the intersection of the cyber and physical domains; chiefly building automation systems and the Internet of Things.
Internet Security

Overview of Internet and network security protocols and architectures.
Network and Internet security is about authenticity, secrecy, privacy, authorization, non-repudiation, data integrity and protection from denial of service (DOS) attacks.
In the early days of the Internet, security was not a concern so most protocols were developed without protection from various kinds of attacks in mind. The Internet is now infested with malware like worms, viruses, trojan horses and killer packets. Unprotected hosts run the risk of being seized by hackers and become part of botnets to launch even more elaborate attacks.
Careful protection of hosts in a network is therefore of paramount importance. Hosts that need not be reachable from the Internet are typically placed in a protected LAN. Hosts with reachability requirements like mail and web servers are placed in a special network zone called DMZ (DeMilitarized Zone).
Firewalls protect the different networks. Firewall functionality ranges from simple port and address filters up to stateful application and deep packet inspection firewalls that provide more protection.
In general, security policies should be as restrictive as reasonable possible. So usually something not explicitly allowed should be classified as forbidden and thus be blocked.
Recommended
IoT Cyber+Physical+Social Engineering Attack Security (v0.1.6 / sep2020)

Work-in-Progress!
IoT Cyber+Physical+Social Security
An encyclopedic compendium of tools, techniques, and practices to defend systems that sit at the intersection of the cyber and physical domains; chiefly building automation systems and the Internet of Things.
Internet Security

Overview of Internet and network security protocols and architectures.
Network and Internet security is about authenticity, secrecy, privacy, authorization, non-repudiation, data integrity and protection from denial of service (DOS) attacks.
In the early days of the Internet, security was not a concern so most protocols were developed without protection from various kinds of attacks in mind. The Internet is now infested with malware like worms, viruses, trojan horses and killer packets. Unprotected hosts run the risk of being seized by hackers and become part of botnets to launch even more elaborate attacks.
Careful protection of hosts in a network is therefore of paramount importance. Hosts that need not be reachable from the Internet are typically placed in a protected LAN. Hosts with reachability requirements like mail and web servers are placed in a special network zone called DMZ (DeMilitarized Zone).
Firewalls protect the different networks. Firewall functionality ranges from simple port and address filters up to stateful application and deep packet inspection firewalls that provide more protection.
In general, security policies should be as restrictive as reasonable possible. So usually something not explicitly allowed should be classified as forbidden and thus be blocked.
What is network security and Types

Network Security protects your network and data from breaches, intrusions and other threats. View this presentation now to understand what is network security and the types of network security.
Happy learning!!
Network Security Research Paper

With the explosion of the public Internet and e-commerce, private computers and computer networks, if not adequately secured are increasingly vulnerable to damaging attacks. Hackers, viruses, vindictive employees and even human error all represent
clear and present dangers to networks. And all computer users from the most casual Internet surfers to large enterprises could be affected by network security breaches. However, security breaches can often be easily prevented. How? This white paper provides you an overview of the most common network security threats and its solution which protects you and your organization from threats, hackers and ensures that the
data traveling across your networks is safe.
Network security (vulnerabilities, threats, and attacks)

Network security deals with different types of vulnerabilities, threats and attacks.
Types of cyber attacks

This presentation takes you to a tour of different types of attacks in the world of computers i.e, cyber world
Anatomy of a cyber attack

Looking to understand how hackers and other attackers use cyber technology to attack your network and your executives? This slide set provides an overview and details the anatomy of a cyber attack, and the strategies you can use to manage and mitigate risk.
IMPLEMENTATION OF A SECURITY PROTOCOL FOR BLUETOOTH AND WI-FI

This paper is mainly based on providing security to the wireless networks through which devices like
Bluetooth gets connected. The Wi-Fi connections are also prone to various attacks these days. The
protocols that are required to provide security to wireless networks can be implemented by creating a
wireless scenario using the software Network Simulator. This paper illustrates a scenario to check the
security protocol. As NS2 mainly has the implementation of routing protocols, a new protocol should be
designed especially for security purpose. This is done by following many tutorials to get a minimum basic
knowledge of NS2, C/C++ coding. The security feature followed in the paper is encryption/decryption of
the data that is being exchanged. Data should be ensured as and then there will be a perfect
implementation of the protocol. So, the paper throughout concentrates on adding a new security protocol to
NS2 and implementation of that protocol by providing a wireless scenario.
Trusted Wireless Environment (TWE)

Wi-Fi hacking leads to stolen passwords, email, social accounts, malware, and identity theft. The worst part is that 20 year old attacks still work today and nearly no one has the technology to detect Wi-Fi hacks making hotspots and office Wi-Fi easy targets for cybercriminals. Food, medicine, even toothpaste has minimum safety standards but Wi-Fi has nothing. The Trusted Wireless Environment (TWE) Framework is the industry's first safety standard for Wi-Fi explaining the six Wi-Fi threats that a WLAN network needs to be protected from to meet the TWE standards.
IoT security-arrow-roadshow #iotconfua

Intel Security - Безопасность мира Интернет Вещей
http://conf.iotua.org/
SS7 Vulnerabilities

Nowadays mobile networks are the most dynamic part of critical communication infrastructures and the key instrument used to perform daily activities ranging from voice and text messaging to providing signaling for emergency services and critical infrastructure.
Is Security Optional20100608

Notes from the presentation "Is security essential" delivered at Lindholmen 2010-06-09
More Related Content
What's hot
What is network security and Types

Network Security protects your network and data from breaches, intrusions and other threats. View this presentation now to understand what is network security and the types of network security.
Happy learning!!
Network Security Research Paper

With the explosion of the public Internet and e-commerce, private computers and computer networks, if not adequately secured are increasingly vulnerable to damaging attacks. Hackers, viruses, vindictive employees and even human error all represent
clear and present dangers to networks. And all computer users from the most casual Internet surfers to large enterprises could be affected by network security breaches. However, security breaches can often be easily prevented. How? This white paper provides you an overview of the most common network security threats and its solution which protects you and your organization from threats, hackers and ensures that the
data traveling across your networks is safe.
Network security (vulnerabilities, threats, and attacks)

Network security deals with different types of vulnerabilities, threats and attacks.
Types of cyber attacks

This presentation takes you to a tour of different types of attacks in the world of computers i.e, cyber world
Anatomy of a cyber attack

Looking to understand how hackers and other attackers use cyber technology to attack your network and your executives? This slide set provides an overview and details the anatomy of a cyber attack, and the strategies you can use to manage and mitigate risk.
IMPLEMENTATION OF A SECURITY PROTOCOL FOR BLUETOOTH AND WI-FI

This paper is mainly based on providing security to the wireless networks through which devices like
Bluetooth gets connected. The Wi-Fi connections are also prone to various attacks these days. The
protocols that are required to provide security to wireless networks can be implemented by creating a
wireless scenario using the software Network Simulator. This paper illustrates a scenario to check the
security protocol. As NS2 mainly has the implementation of routing protocols, a new protocol should be
designed especially for security purpose. This is done by following many tutorials to get a minimum basic
knowledge of NS2, C/C++ coding. The security feature followed in the paper is encryption/decryption of
the data that is being exchanged. Data should be ensured as and then there will be a perfect
implementation of the protocol. So, the paper throughout concentrates on adding a new security protocol to
NS2 and implementation of that protocol by providing a wireless scenario.
Trusted Wireless Environment (TWE)

Wi-Fi hacking leads to stolen passwords, email, social accounts, malware, and identity theft. The worst part is that 20 year old attacks still work today and nearly no one has the technology to detect Wi-Fi hacks making hotspots and office Wi-Fi easy targets for cybercriminals. Food, medicine, even toothpaste has minimum safety standards but Wi-Fi has nothing. The Trusted Wireless Environment (TWE) Framework is the industry's first safety standard for Wi-Fi explaining the six Wi-Fi threats that a WLAN network needs to be protected from to meet the TWE standards.
IoT security-arrow-roadshow #iotconfua

Intel Security - Безопасность мира Интернет Вещей
http://conf.iotua.org/
SS7 Vulnerabilities

Nowadays mobile networks are the most dynamic part of critical communication infrastructures and the key instrument used to perform daily activities ranging from voice and text messaging to providing signaling for emergency services and critical infrastructure.
Is Security Optional20100608

Notes from the presentation "Is security essential" delivered at Lindholmen 2010-06-09
What's hot (20)
Network security (vulnerabilities, threats, and attacks)

Network security (vulnerabilities, threats, and attacks)
IMPLEMENTATION OF A SECURITY PROTOCOL FOR BLUETOOTH AND WI-FI

IMPLEMENTATION OF A SECURITY PROTOCOL FOR BLUETOOTH AND WI-FI
Viewers also liked
Iscon Platinum Details

ISCON Platinum is truly a once in a lifetime opportunity to own a home in a residential development that has all the ingredients to become an iconic Ahmedabad landmark.
Financial management

Please help me with my assignment for Financial management, especial question 2-4. Thank you in advance.
(343)long populismo, neoliberalismo y neonacionalism odocx

El fenomeno TRUMP eleva el populismo a categoría global.
(350)pdf long los regalos de los magos

LA ECONOMIA ESPAÑOLA SIGUE UNA SENDA DE RECUPERACION ESPECTACULAR, PERO NO SOLO POR MERITOS PROPIOS...
Viewers also liked (13)
(343)long populismo, neoliberalismo y neonacionalism odocx

(343)long populismo, neoliberalismo y neonacionalism odocx
Similar to LiPari_Assignment8
Using Your Network as a Sensor for Enhanced Visibility and Security 

Driven by the mobility, cloud computing, and Internet of Everything megatrends and fueled by increasingly sophisticated cybercriminals, today’s information landscape is more dynamic and more vulnerable than ever before.
Join Cisco and Lancope for a complimentary webinar to learn how you can implement a comprehensive, network-enabled approach to cybersecurity.
During the webinar we will discuss:
Using the Network as a Security Sensor with Lancope’s StealthWatch System and Flexible NetFlow and to obtain visibility at scale, monitor network activity efficiently, discover security incidents quickly, and help achieve compliance.
Using the Network as a Security Enforcer with Cisco TrustSec to ensure policy-based access control and network segmentation for containment of the network attacks, assist compliance and reduce risks of data-breaches.
12 IoT Cyber Security Threats to Avoid - CyberHive.pdf

As IoT (Internet of Things) devices weave into the fabric of our daily lives, from smart thermostats to connected cars, the need for robust IoT cyber security measures has never been more pressing. Let’s dive into 12 IoT cyber security threats that pose significant risks and offer guidance on navigating these digital waters safely. please visit: https://www.cyberhive.com/insights/12-iot-cyber-security-threats-to-avoid/
The Sharp Increase in Unmasking of Obtrusion into Internet of Things (IoT) IP...

The Sharp Increase in Unmasking of Obtrusion into Internet of Things (IoT) IP...IJCSIS Research Publications
The Internet of Things (IoT) is thriving network of smart objects where one physical object can exchange information with another physical object. In today’s Internet of Things (IoT) the interest is the concealment and security of data in a network. The obtrusion into Internet of Things (IoT) exposes the extent with which the internet of things is vulnerable to attacks and how such attack can be detected to prevent extreme damage. It emphasises on threats, vulnerability, attacks and possible methods of detecting intruders to stop the system from further destruction, this paper proposes a way out of the impending security situation of Internet of things using IPV6 Low -power wireless personal Area Network.Iot(security)

the ppt describes about the basics of iot,its applications, security challenges , hacks and the solutions to the security challenges
Co-operative Wireless Intrusion Detection System Using MIBs From SNMP

In emerging technology of Internet, security issues are becoming more challenging. In case of wired LAN it is somewhat in control, but in case of wireless networks due to exponential growth in attacks, it has made difficult to detect such security loopholes. Wireless network security is being addressed using firewalls, encryption techniques and wired IDS (Intrusion Detection System) methods. But the approaches which were used in wired network were not successful in producing effective results for wireless networks. It is so because of features of wireless network such as open medium, dynamic changing topology, cooperative algorithms, lack of centralized monitoring and management point, and lack of a clear line of defense etc. So, there is need for new approach which will efficiently detect intrusion in wireless network. Efficiency can be achieved by implementing distributive, co-operative based, multi-agent IDS. The proposed system supports all these three features. It includes mobile agents for intrusion detection which uses SNMP (Simple network Management Protocol) and MIB (Management Information Base) variables for mobile wireless networks.
Ransomware protection in loT using software defined networking 

Internet of things (IoT) is the network of physical objects connected to provide various services. IoT is expanding rapidly, and is positively influencing many areas. The impact of IoT is evident in medical field, manufacturing units and livestock. The IoT is also vulnerable to many cyber threats, owing to its limited resources and battery operation. In contemporary times the security threats like DDoS, botnet malware, man in the middle, flood attacks and ransomware are affecting the smooth functioning of IoT. Ransomware has emerged as one of the biggest threat in cyber world. Ransomware is a type of malware that stops the access to files by encrypting them and decrypts the files only when a ransom is paid. The negligence towards the IoT ransomware can result in disastrous outcomes. In this paper, the growth of ransomware attacks for past few years is shown with special focus on ransomwares threatening IoT. A detection mechanism for IoT ransomware attack is presented that is designed after study of ransomware for IoT. The proposed model monitors the incoming IoT traffic through Software Defined Network (SDN) gateway. It uses policies framed in SDN controller for detection and alleviation of ransomware in IoT.
LIFT OFF 2017: IoT and MSS Deep Dive

Presentation by Toni Buhrke from ForeScout about IoT-related security issues and how managed security services (MSS) can help mitigate IoT risks.
Deterring hacking strategies via

Network infrastructures have played important part in most daily communications for business industries,
social networking, government sectors and etc. Despites the advantages that came from such
functionalities, security threats have become a daily struggle. One major security threat is hacking.
Consequently, security experts and researchers have suggested possible security solutions such as
Firewalls, Intrusion Detection Systems (IDS), Intrusion Detection and Prevention Systems (IDP) and
Honeynet. Yet, none of these solutions have proven their ability to completely address hacking. The reason
behind that, there is a few researches that examine the behavior of hackers. This paper formally and
practically examines in details the behavior of hackers and their targeted environments. Moreover, this
paper formally examines the properties of one essential pre-hacking step called scanning and highlights its
importance in developing hacking strategies. Also, it illustrates the properties of hacking that is common in
most hacking strategies to assist security experts and researchers towards minimizing the risk of hack.
DETERRING HACKING STRATEGIES VIA TARGETING SCANNING PROPERTIES

Network infrastructures have played important part in most daily communications for business industries, social networking, government sectors and etc. Despites the advantages that came from such functionalities, security threats have become a daily struggle. One major security threat is hacking. Consequently, security experts and researchers have suggested possible security solutions such as Firewalls, Intrusion Detection Systems (IDS), Intrusion Detection and Prevention Systems (IDP) and Honeynet. Yet, none of these solutions have proven their ability to completely address hacking. The reason behind that, there is a few researches that examine the behavior of hackers. This paper formally and practically examines in details the behavior of hackers and their targeted environments. Moreover, this paper formally examines the properties of one essential pre-hacking step called scanning and highlights its importance in developing hacking strategies. Also, it illustrates the properties of hacking that is common in most hacking strategies to assist security experts and researchers towards minimizing the risk of hack.
Cybersecurity in the Age of IoT - Skillmine

Cybersecurity stands as the bedrock of our digital world, safeguarding systems, networks, and data from a rising tide of cyber threats. In the era of the Internet of Things (IoT), wherean ever-expanding array of devices and objects are seamlessly interconnected, the importance of cybersecurity has escalated to unprecedented levels.
IoT Security, Threats and Challenges By V.P.Prabhakaran

This presentation discusses about IoT, challenges associated with it, common threats to IoT. It also briefs about how OWASP introduces Vulnerabilities in IoT.
Unlocking the Potential: A Comprehensive Guide to Understanding and Securing ...

The Internet of Things, or IoT, has become a disruptive force in the era of connected devices, changing the way we interact with our surroundings. In the center of this networked web is an essential element called IoT gateways. The purpose of this paper is to offer a thorough overview of IoT gateways, their importance in enabling smooth device connectivity, and the critical necessity to safeguard these gateways against growing cyber threats.
Safeguarding the Internet of Things

The Internet of Things (IoT) promises to change the way enterprises connect, communicate, operate, and compete. At the same time, the IoT has left enterprise networks and IoT devices extremely vulnerable to security breaches. Current IoT devices and infrastructures are simply not equipped to tackle today’s sophisticated attack methods. Vulnerabilities can be easily exploited unless security is embedded from the inside out – from conception, deployment, and maintenance, to the network edge and across connected devices and infrastructures.
Similar to LiPari_Assignment8 (20)
Using Your Network as a Sensor for Enhanced Visibility and Security 

Using Your Network as a Sensor for Enhanced Visibility and Security
12 IoT Cyber Security Threats to Avoid - CyberHive.pdf

12 IoT Cyber Security Threats to Avoid - CyberHive.pdf
The Sharp Increase in Unmasking of Obtrusion into Internet of Things (IoT) IP...

The Sharp Increase in Unmasking of Obtrusion into Internet of Things (IoT) IP...
Co-operative Wireless Intrusion Detection System Using MIBs From SNMP

Co-operative Wireless Intrusion Detection System Using MIBs From SNMP
Ransomware protection in loT using software defined networking 

Ransomware protection in loT using software defined networking
DETERRING HACKING STRATEGIES VIA TARGETING SCANNING PROPERTIES

DETERRING HACKING STRATEGIES VIA TARGETING SCANNING PROPERTIES
IoT Security, Threats and Challenges By V.P.Prabhakaran

IoT Security, Threats and Challenges By V.P.Prabhakaran
Unlocking the Potential: A Comprehensive Guide to Understanding and Securing ...

Unlocking the Potential: A Comprehensive Guide to Understanding and Securing ...
LiPari_Assignment8
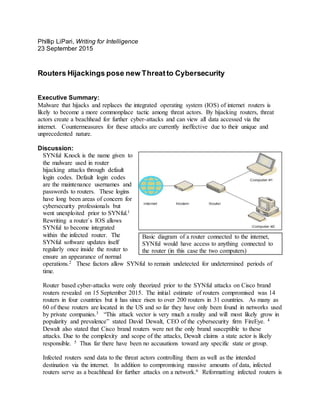
- 1. Phillip LiPari, Writing for Intelligence 23 September 2015 Routers Hijackings pose new Threatto Cybersecurity Executive Summary: Malware that hijacks and replaces the integrated operating system (IOS) of internet routers is likely to become a more commonplace tactic among threat actors. By hijacking routers, threat actors create a beachhead for further cyber-attacks and can view all data accessed via the internet. Countermeasures for these attacks are currently ineffective due to their unique and unprecedented nature. Discussion: SYNful Knock is the name given to the malware used in router hijacking attacks through default login codes. Default login codes are the maintenance usernames and passwords to routers. These logins have long been areas of concern for cybersecurity professionals but went unexploited prior to SYNful.1 Rewriting a router`s IOS allows SYNful to become integrated within the infected router. The SYNful software updates itself regularly once inside the router to ensure an appearance of normal operations.2 These factors allow SYNful to remain undetected for undetermined periods of time. Router based cyber-attacks were only theorized prior to the SYNful attacks on Cisco brand routers revealed on 15 September 2015. The initial estimate of routers compromised was 14 routers in four countries but it has since risen to over 200 routers in 31 countries. As many as 60 of these routers are located in the US and so far they have only been found in networks used by private companies.3 “This attack vector is very much a reality and will most likely grow in popularity and prevalence” stated David Dewalt, CEO of the cybersecurity firm FireEye. 4 Dewalt also stated that Cisco brand routers were not the only brand susceptible to these attacks. Due to the complexity and scope of the attacks, Dewalt claims a state actor is likely responsible. 5 Thus far there have been no accusations toward any specific state or group. Infected routers send data to the threat actors controlling them as well as the intended destination via the internet. In addition to compromising massive amounts of data, infected routers serve as a beachhead for further attacks on a network.6 Reformatting infected routers is Basic diagram of a router connected to the internet, SYNful would have access to anything connected to the router (in this case the two computers)
- 2. the only way to eliminate SYNful due to the IOS integration. FireEye recommends a thorough examination of networks compromised by infected routers.7 Cisco stated that routers are both valuable to threat actors as well as key points of defense within a network. Since SYNful and router attacks in general are still vague and difficult to prevent, they will remain an effective attack method.8 Considering the lack of a defensive strategy, Cisco`s security division is currently developing methods to detect and repel router attacks.9 Source Reliability: Moderate With questions or concerns, please contact the author: Email: plipar35@lakers.mercyhurst.edu Phone: (585) 752-9449 Peer reviewed by: Austin Wood Graphic source: http://www.microsoft.com/library/media/1033/windowsxp/images/using/networking/setup/68573- router-diagram.gif Endnotes 1 http://news.softpedia.com/news/some-wifi-routers-can-be-hacked-using-a-hard-coded-default-login- 490207.shtml (L) 2 http://searchsecurity.techtarget.com/news/4500253817/Cisco-router-malware-in-the-wild-more-widespread- than-first-believed (H) 3 http://fcw.com/articles/2015/09/15/cisco-router.aspx (M) 4 http://www.networkworld.com/article/2984124/security/attackers-can-take-over-cisco-routers-other-routers- at-risk-too.html (M) 5 http://www.fierceenterprisecommunications.com/story/even-more-cisco-devices-found-be-infected-synful- knock/2015-09-21 (M) 6 http://www.crn.com/news/networking/300078193/hundreds-of-cisco-routers-infected-with-synful-knock- partners-say-attack-changing-sales-strategy.htm (M) 7 http://www.infosecurity-magazine.com/news/cisco-synful-knock-threat-victims/ (M) 8 http://www.ibtimes.com/router-hack-creates-ultimate-listening-device-monitor-countrys-entire-internet- 2097511 (M) 9 http://www.eweek.com/security/synful-knock-malware-found-on-almost-200-cisco-routers.html (M)