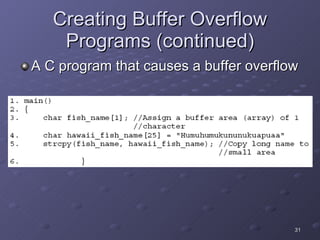
The document discusses vulnerabilities in the Linux operating system and countermeasures to protect Linux systems from remote attacks. It describes how attackers can use tools like Nessus to discover vulnerabilities, deploy trojan programs, and create buffer overflows. It also provides recommendations for system administrators, including keeping systems updated with the latest patches, using rootkit detectors, and training users to avoid social engineering attacks.