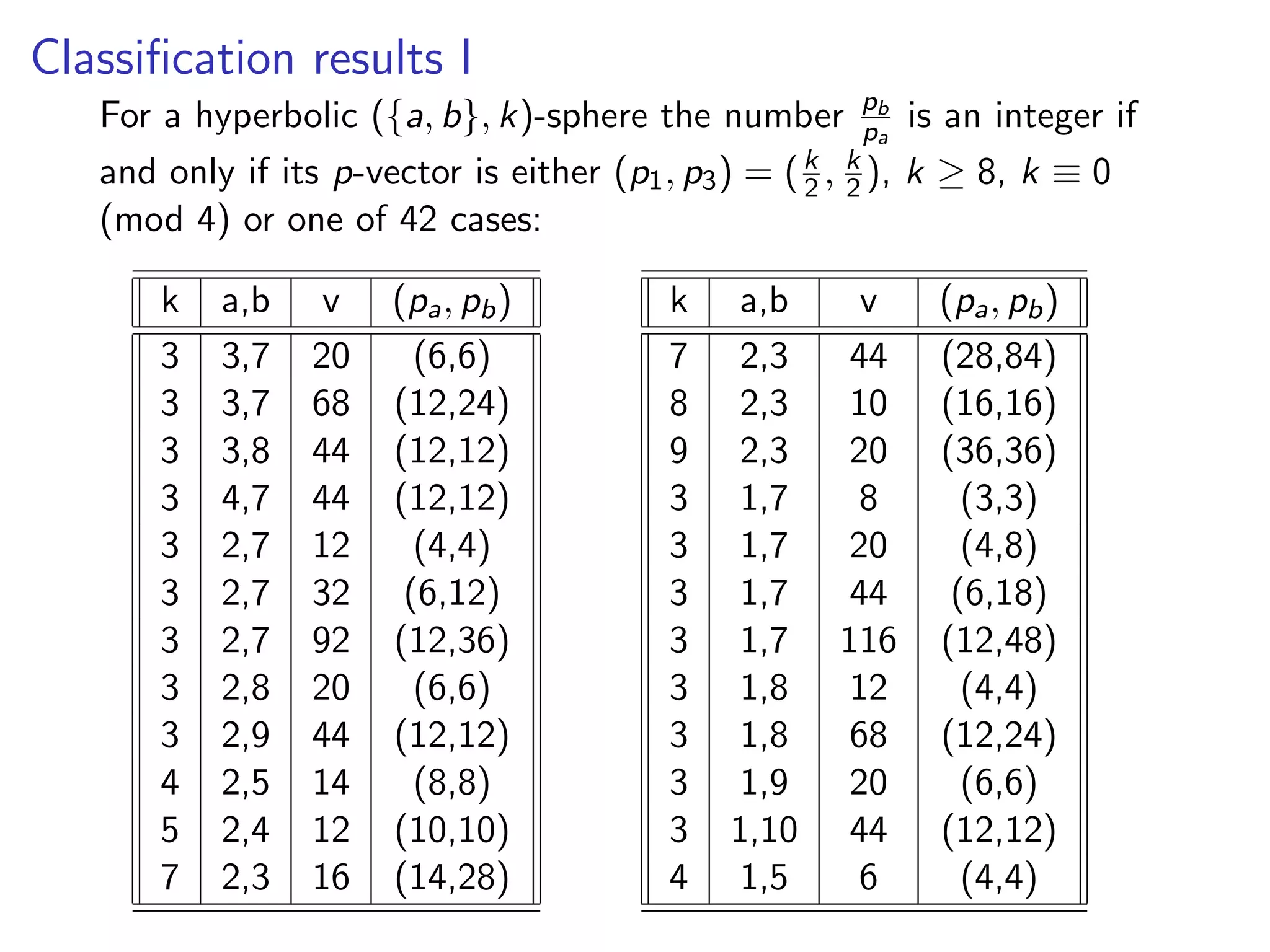
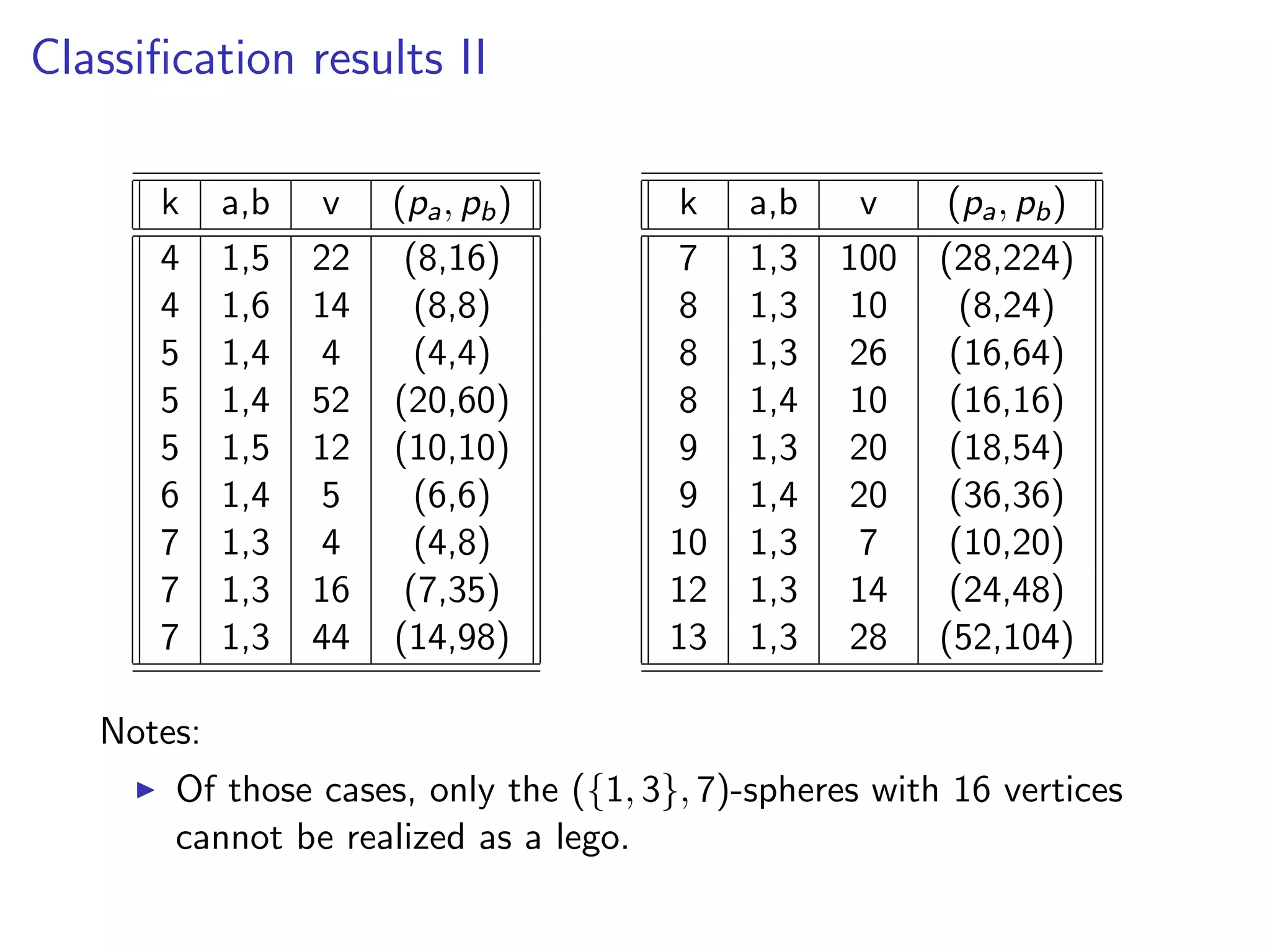
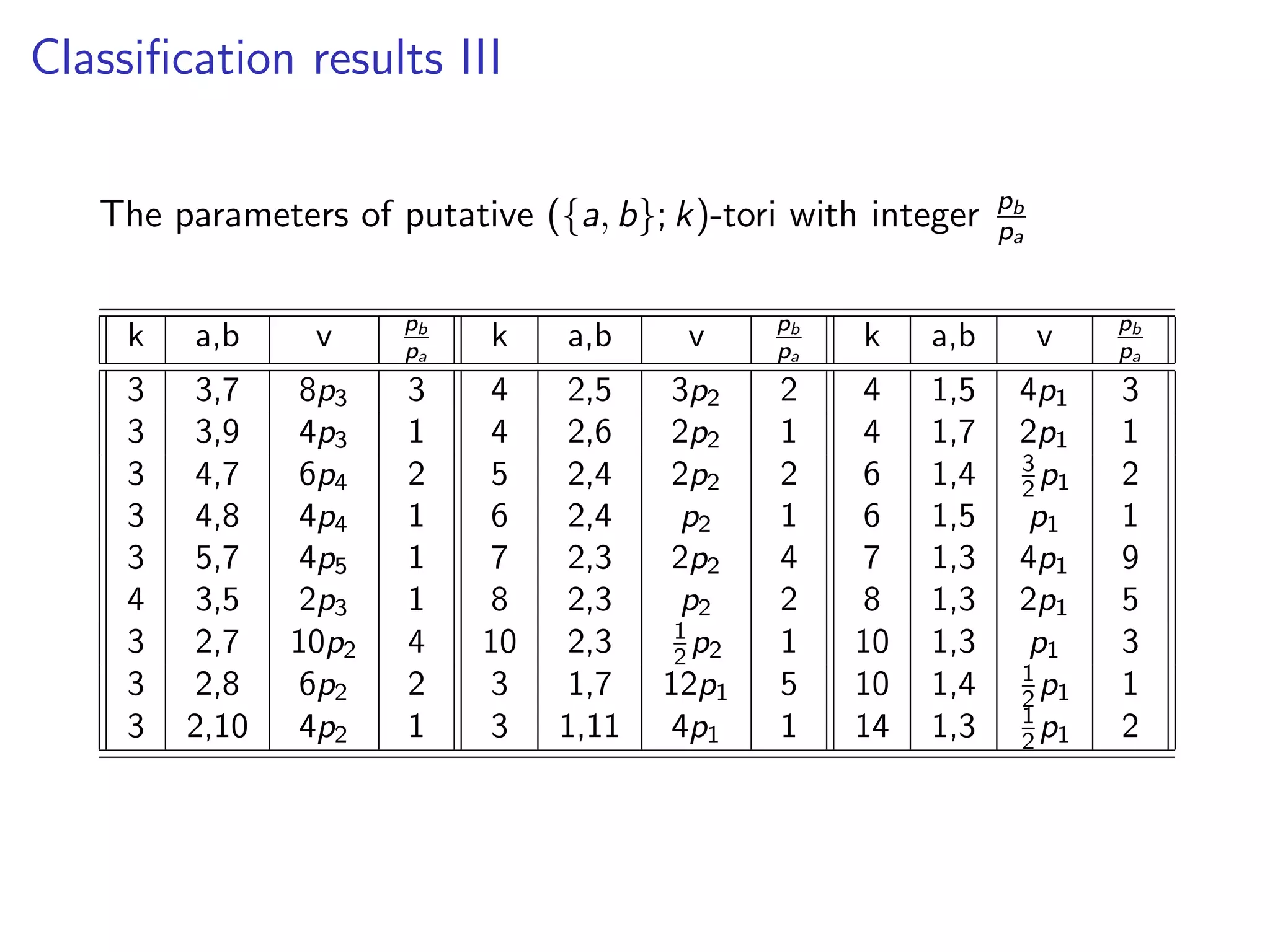
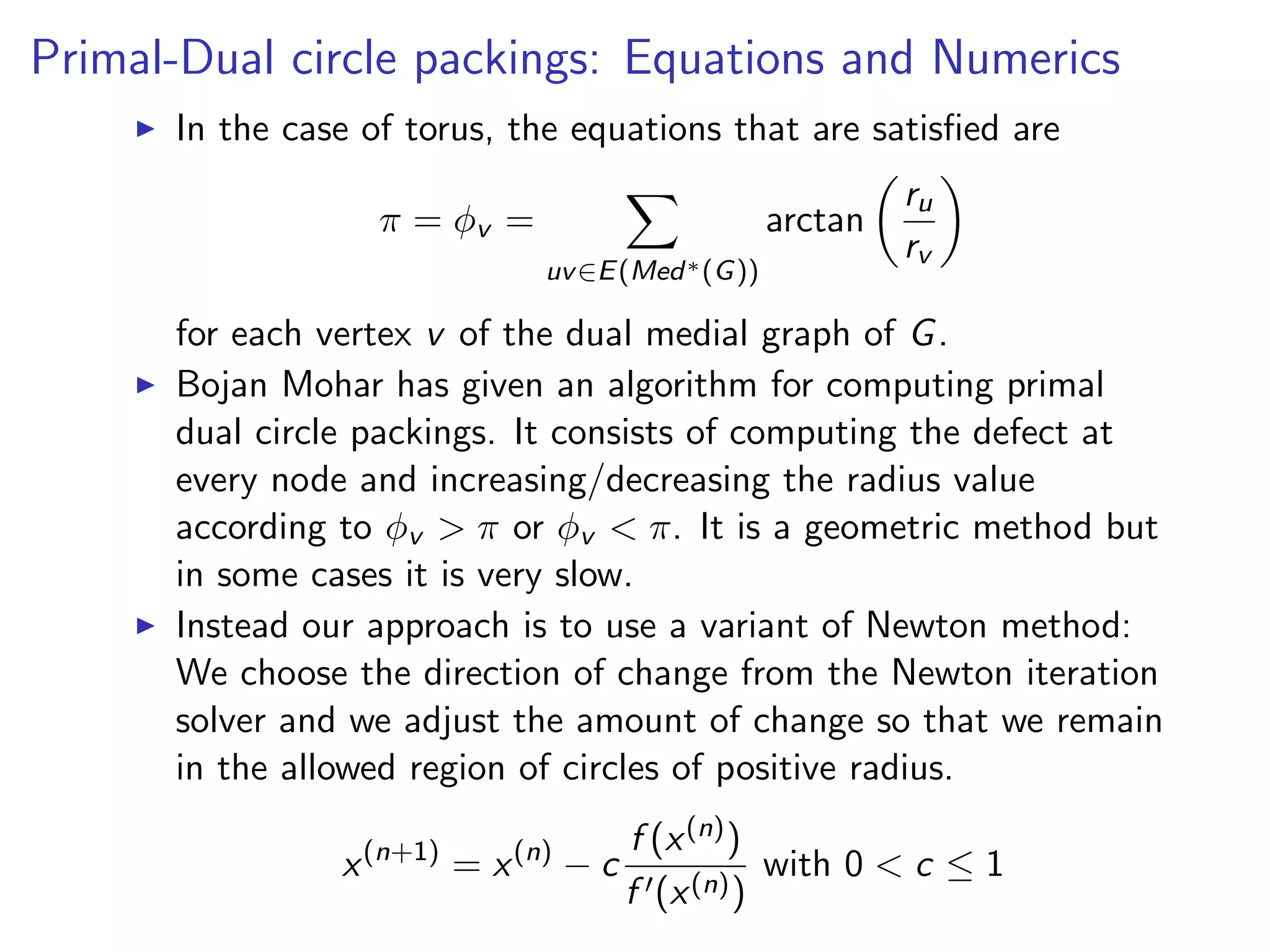
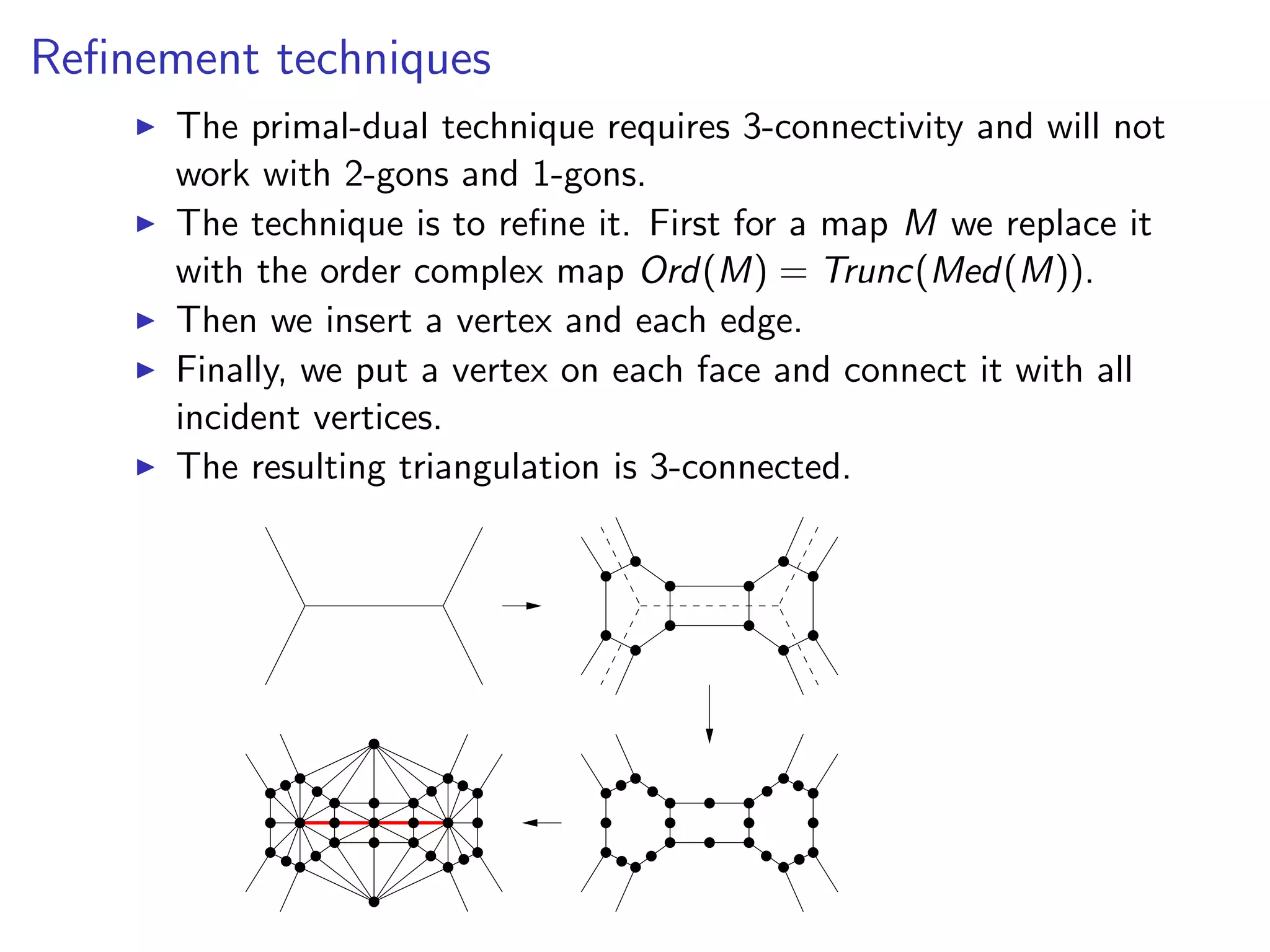
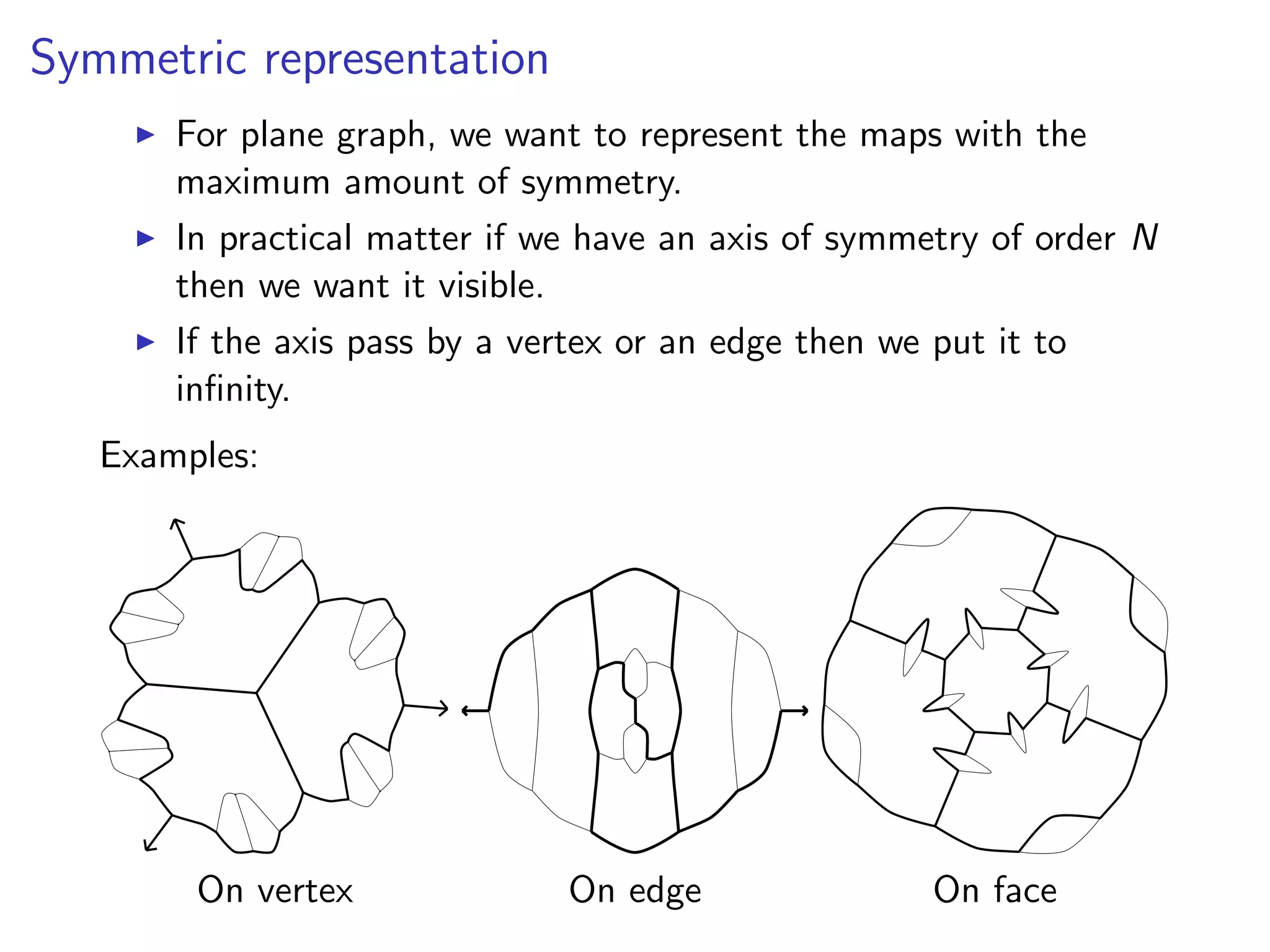
This document discusses methods for summarizing Lego-like sphere and torus maps. It begins by introducing the concept of ({a,b},k)-maps, which are k-valent maps with faces of size a or b. It then discusses several challenges in enumerating and drawing such maps, including enumerating all possible Lego decompositions. Specific enumeration methods are described, such as using exact covering problems or satisfiability problems. The document also discusses challenges in graph drawing representations, and suggests using primal-dual circle packings as a promising approach.