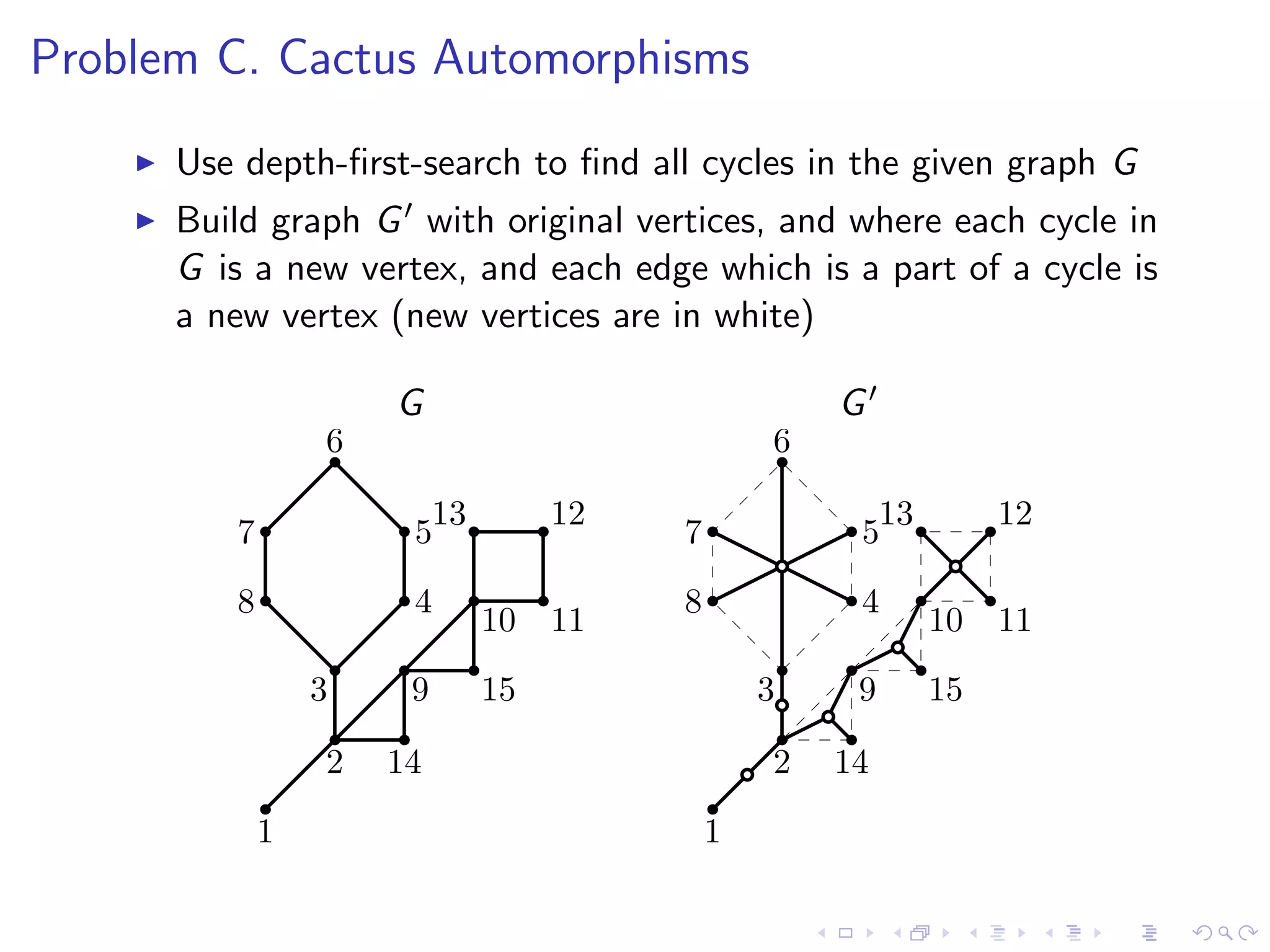
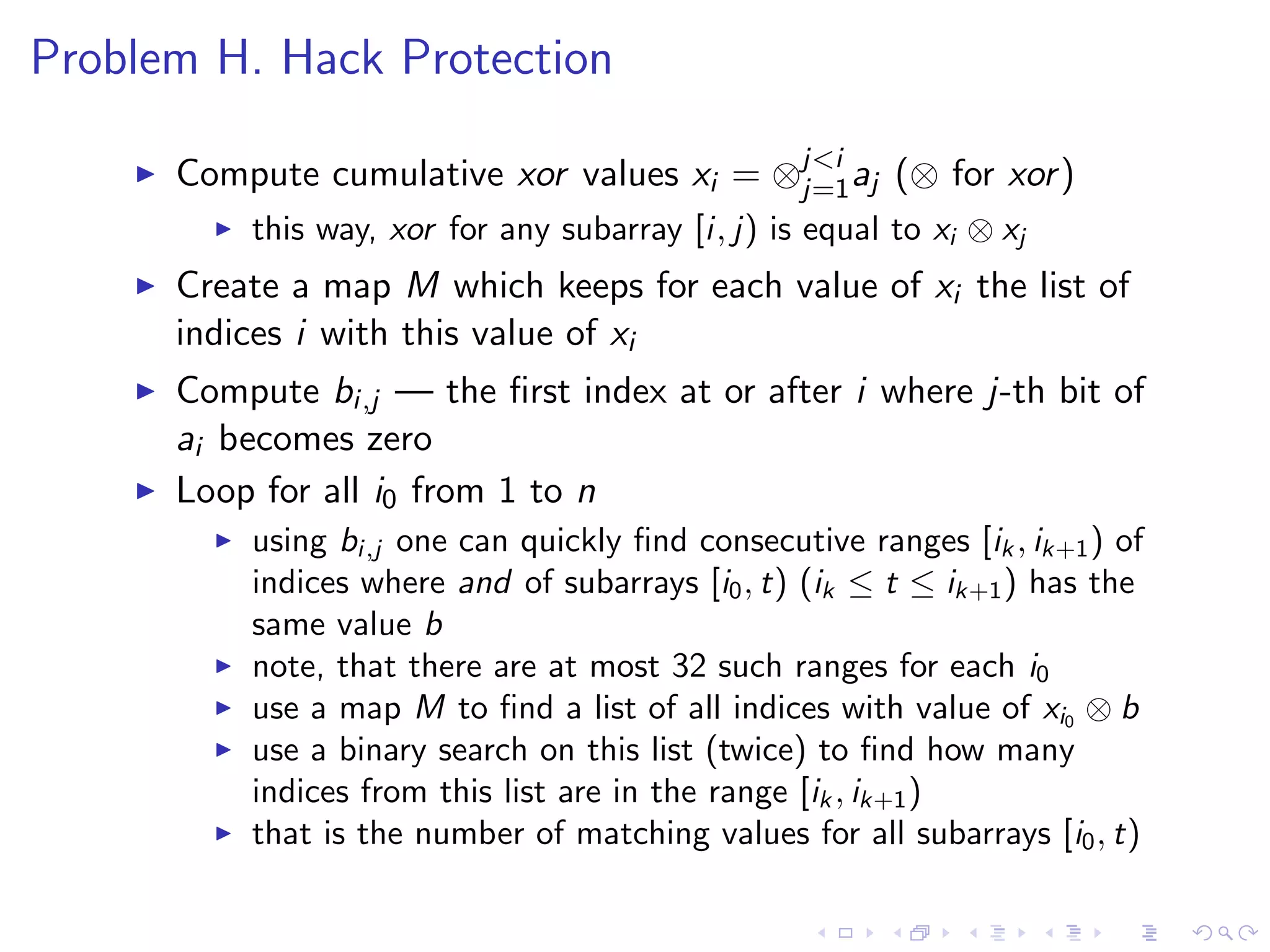
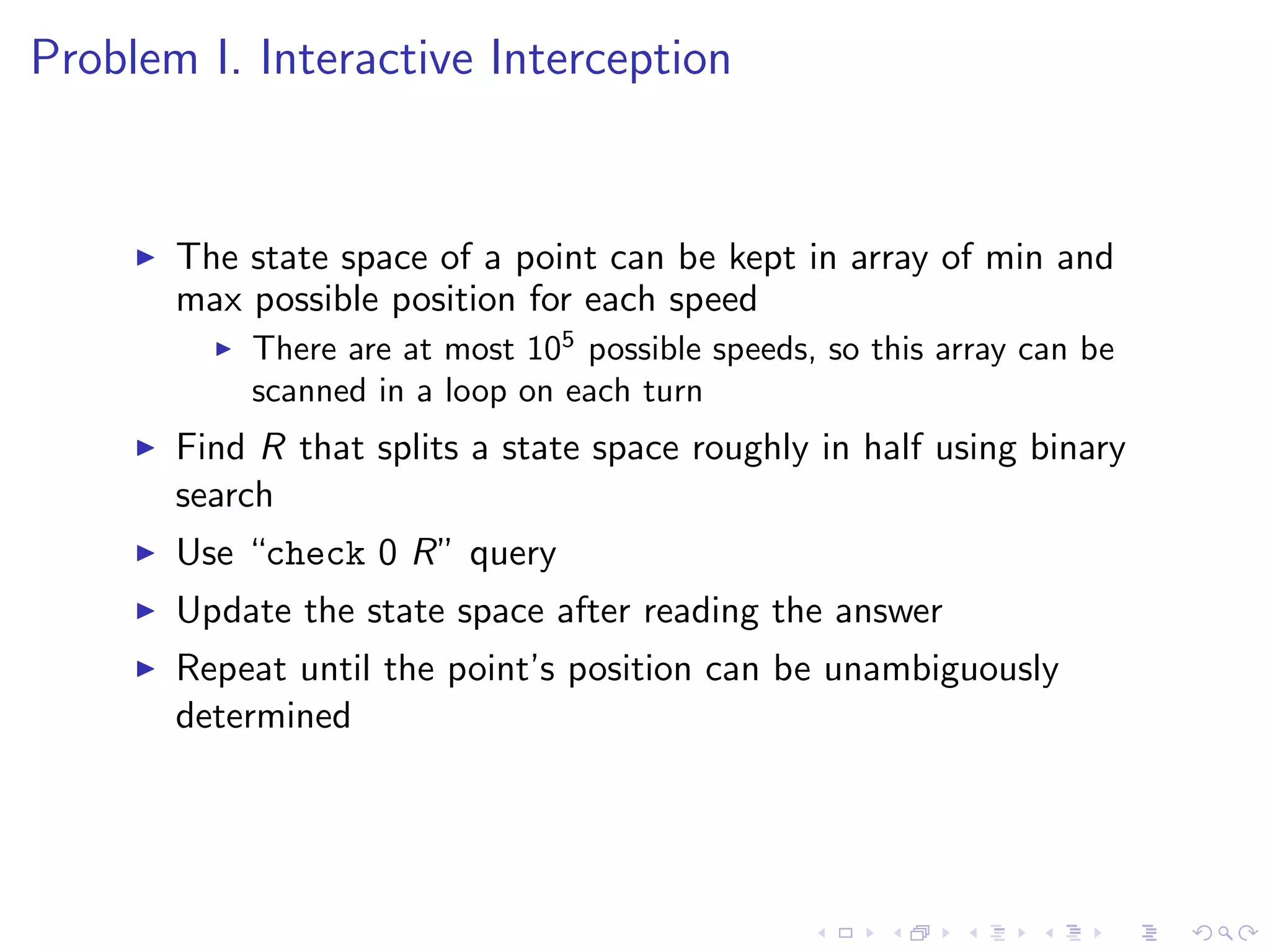
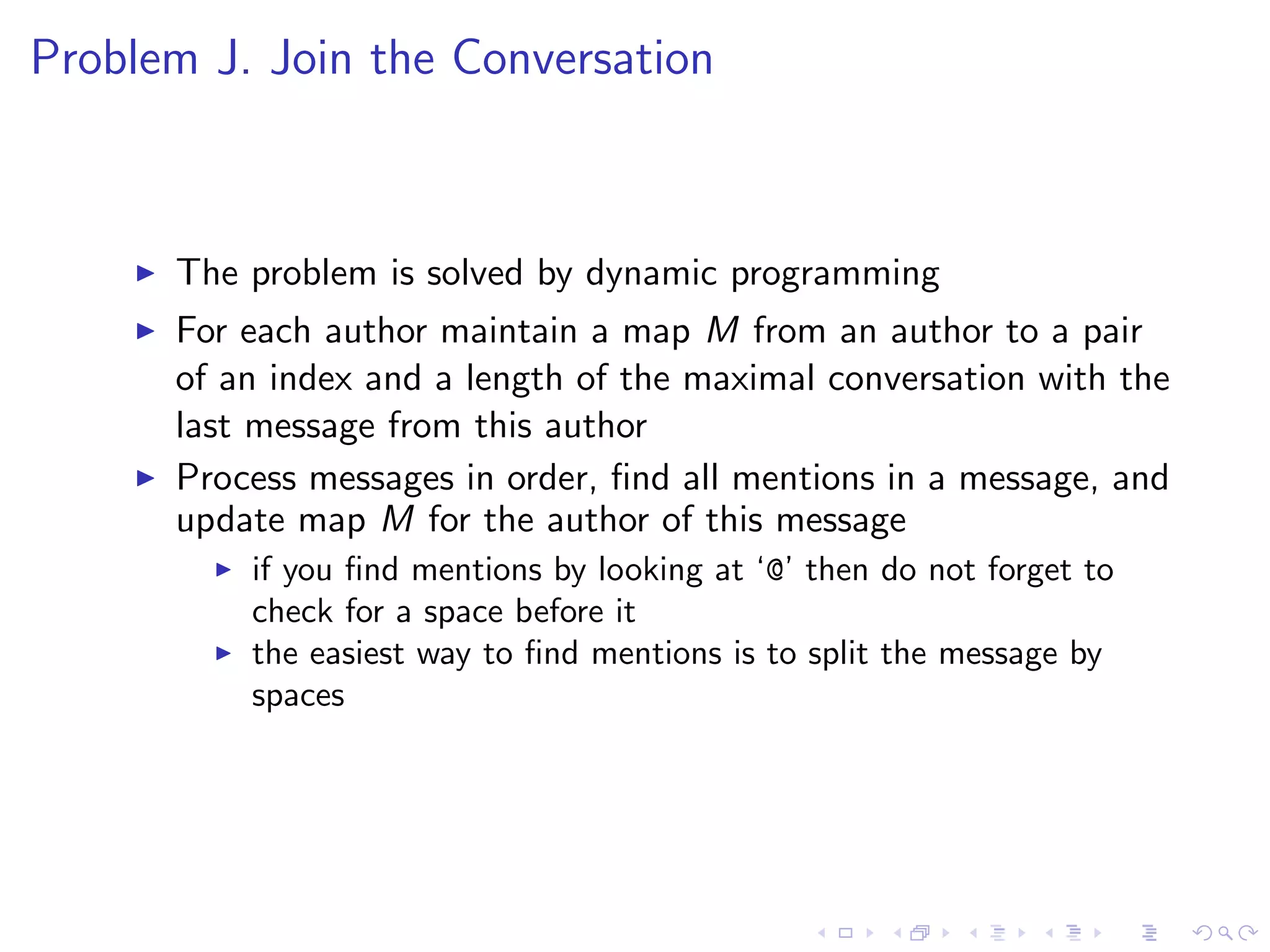
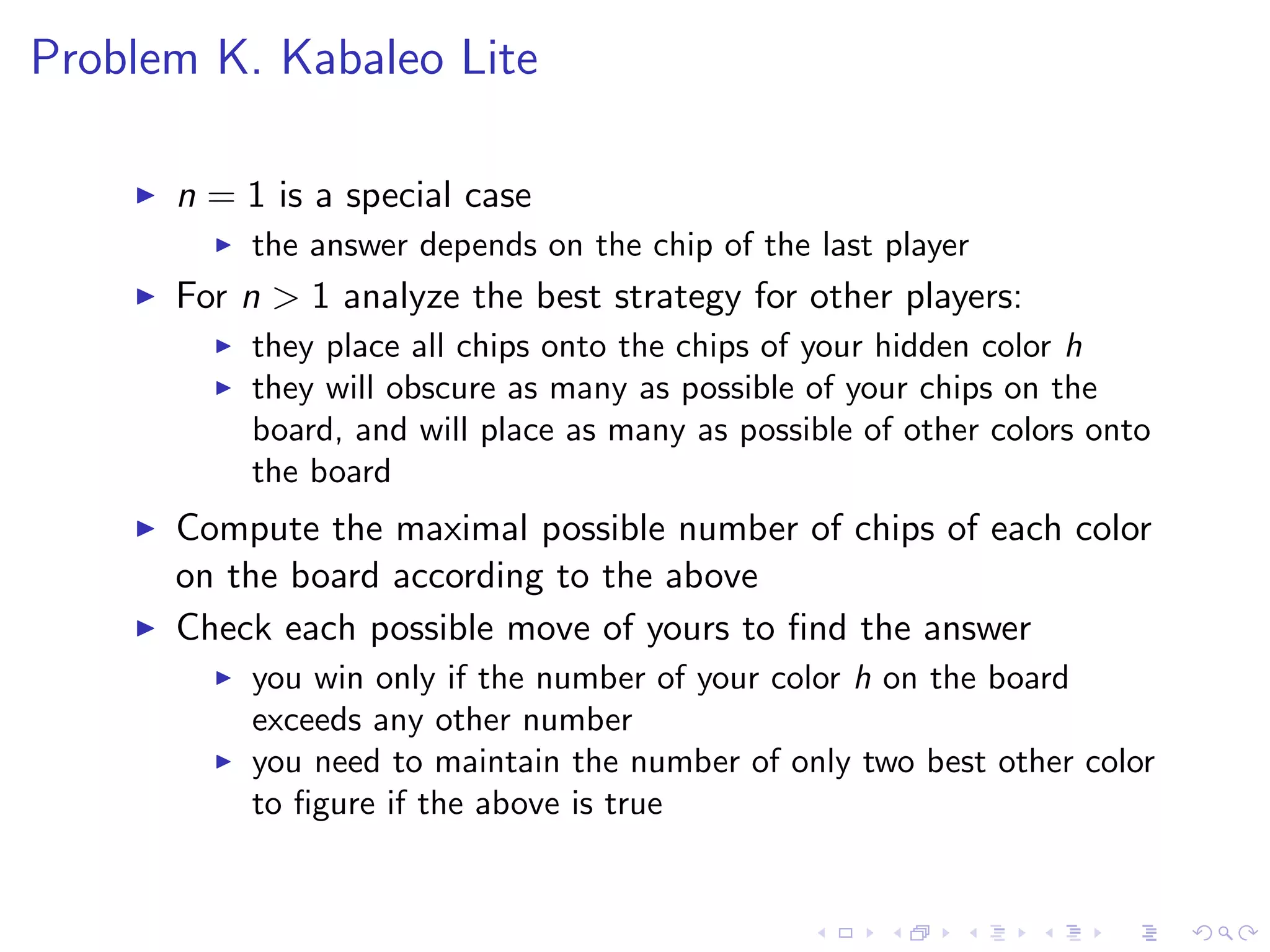
This document summarizes 9 problems from the ACM ICPC 2013-2014 Northeastern European Regional Contest. It provides an overview of the key algorithms and approaches for each problem, describing them concisely in 1-3 sentences per problem. The problems cover a range of algorithmic topics including exhaustive search, dynamic programming, graph algorithms, geometry, and more.