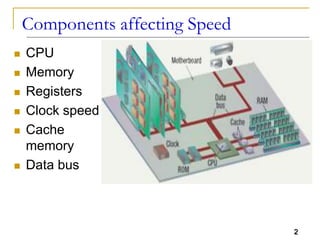
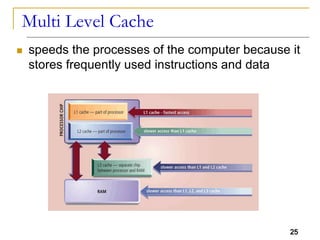
The document discusses various components that affect processor speed, including the CPU, memory, registers, clock speed, and cache memory. It describes how processor speed has been increased over time through shrinking components, increasing clock rates, optimizing cache sizes and speeds, and implementing parallelism. The document also discusses registers in detail, including their functions, sizes, and different types. It explains the role of the system clock and clock rate in governing processor operations. Finally, it covers cache memory hierarchies, bus architectures, and the functions of data, address and control buses.