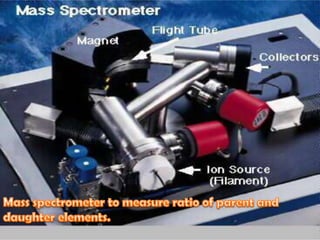
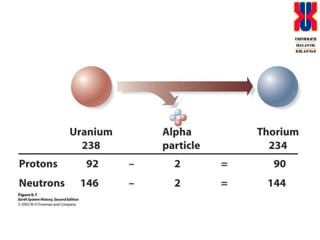
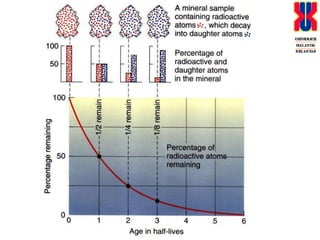
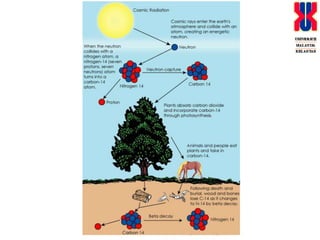
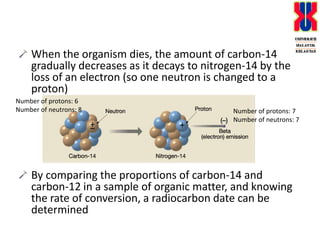
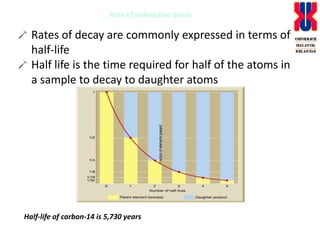
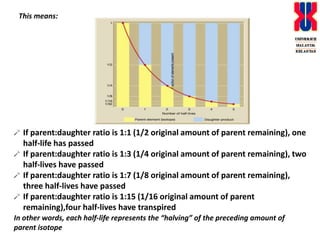
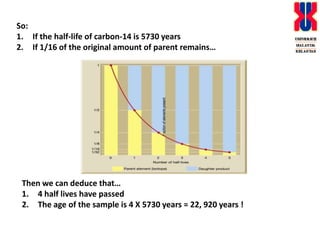
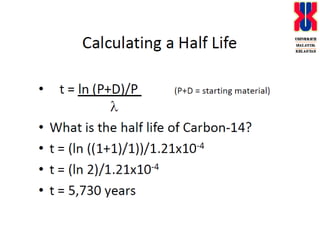
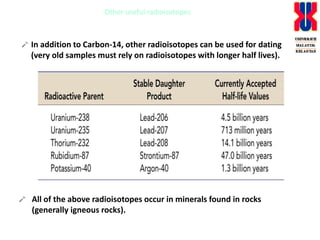
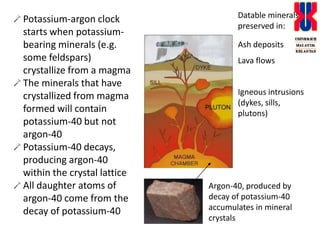
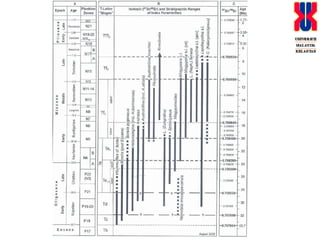
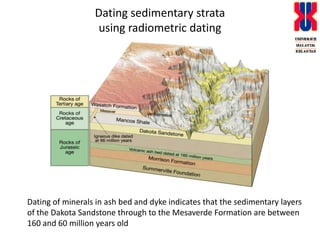
Radiometric dating uses the natural radioactive decay of isotopes to determine the age of rocks and other materials. Only two measurements are needed: the ratio of parent and daughter isotopes, and the decay constant. Examples given include carbon-14 dating of organic materials and potassium-argon dating of igneous rocks. Difficulties can arise from open systems and metamorphism altering isotope ratios, so only fresh samples are suitable for dating. Radiometric dating has established that geological time spans billions of years.