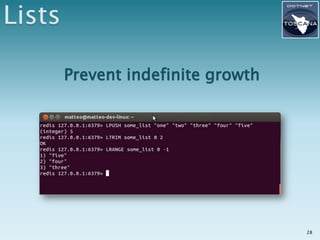
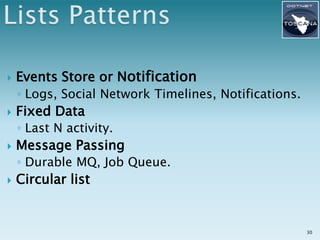
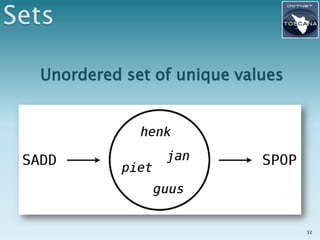
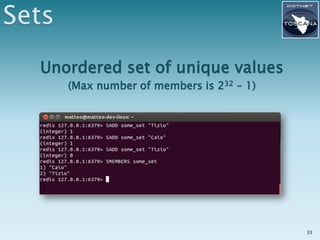
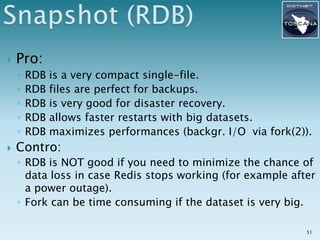
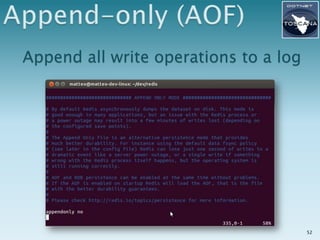
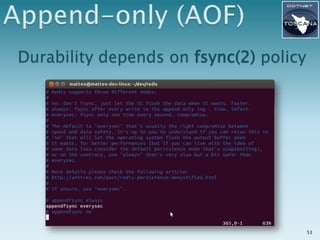
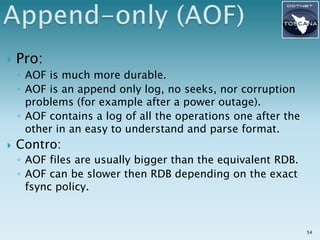
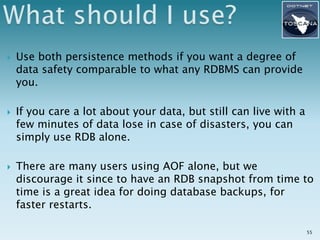
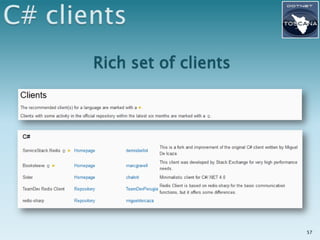
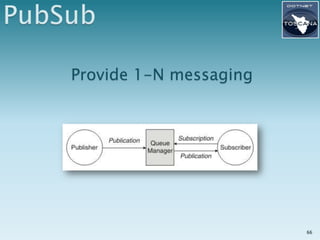
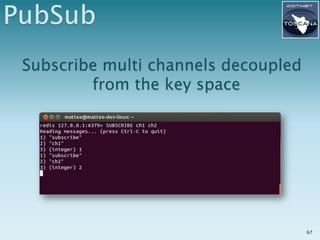
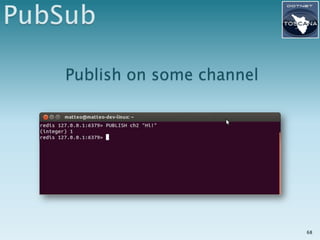
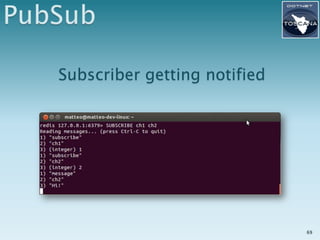
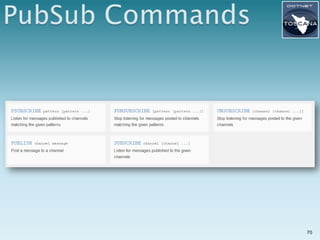
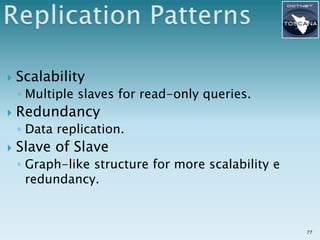
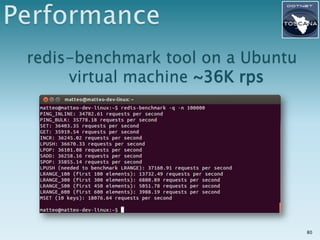
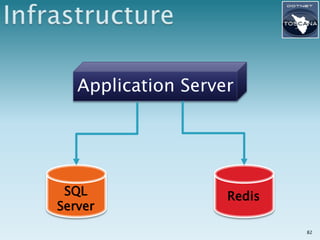
This document provides an overview of Redis, an open source in-memory data structure store. It discusses how Redis can be used as a data store, cache, and message broker. It explains Redis' core abstractions like strings, hashes, lists, sets, sorted sets; persistence options; replication; and pub/sub functionality. The document also provides information about Redis' performance, clients, and how it is well-suited for caching, analytics, and real-time applications.

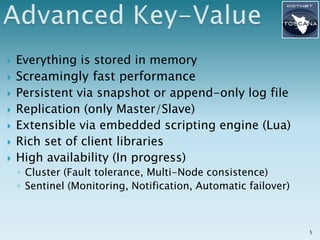
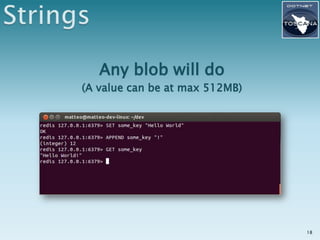
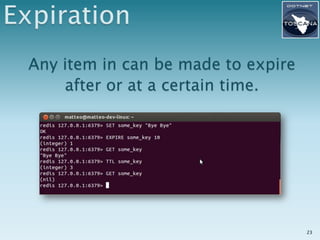
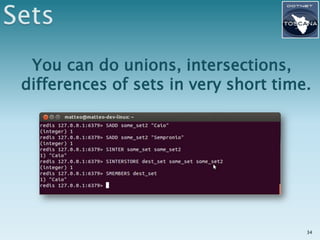
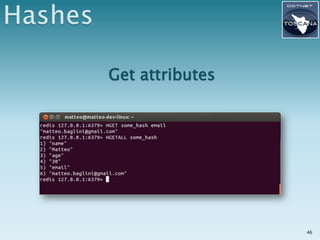
![Key Value
page:index <html><head>[...]
user:123:session xDrSdEwd4dSlZkEkj+
user:123:avatar 77u/PD94bWwgdm+
Everything is a «blob»
Commands, primarily, can GET and SET the values
3](https://image.slidesharecdn.com/04-redis-121216051138-phpapp01/85/Key-value-databases-in-practice-Redis-DotNetToscana-3-320.jpg)
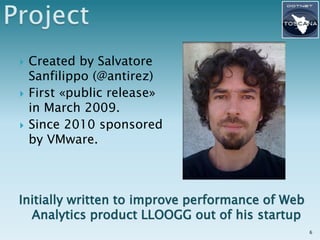
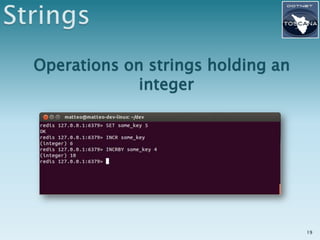
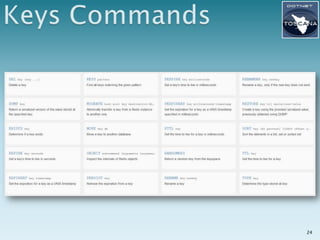
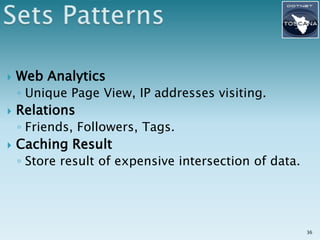
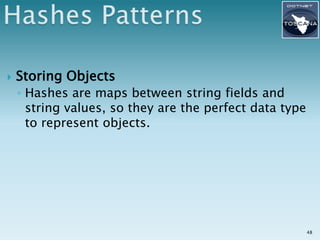
![Key Value Type
page:index <html><head>[...] String
events:timeline { «Joe logged», «File X Uploaded», …} List
logged:today { 1, 2, 3, 4, 5 } Set
time => 10927353
user:123:profile Hash
username => bmatte
joe ~ 1.3483
game:leaderboard smith ~ 293.45 Sorted Set
fred ~ 83.22
Different «data type/structure»
Rich set of specialized commands 4](https://image.slidesharecdn.com/04-redis-121216051138-phpapp01/85/Key-value-databases-in-practice-Redis-DotNetToscana-4-320.jpg)