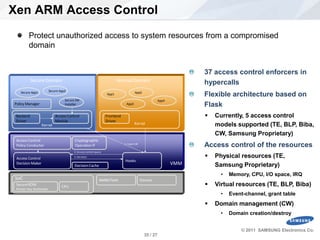
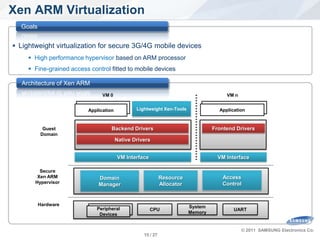
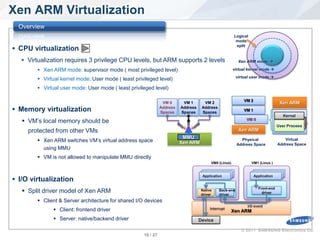
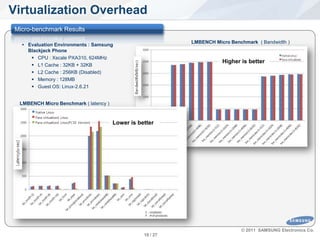
The keynote speech presented by Sang-Bum Suh discusses Xen ARM virtualization, highlighting its significance for mobile device performance, secure application execution, and hardware consolidation. It covers the architecture of Xen ARM, its performance evaluation, and recent industry trends urging the adoption of virtualization technology in embedded devices. The document also outlines future developments and challenges facing Xen ARM, such as the need for lightweight tools and real-time scheduling improvements.







![Future Computing Trends
Changes in
Computing
Closed Keyboard/Mouse Multitouch Augmented Reality Gesture Interactive 3D UI Open
Voice Call, SMS Video Call, MMS Eye-Tracking Manytouch Realtime Web Distributed
Centralized
Correct Info. Centeralized/Concentrated Distributed/Scattered Correct+Timely Info.
Stationary Known Comm. Entities Unknown/Utrusted Comm. Entities Mobile
Collaboration Sensor
Keyboard/ Network
Mouse Every Node
as Both of
Local Multitouch Client/Server
Personal Cloud
Store
Computer
Embedded Single-core Multi-core Many-core
IT Single-core Multi-core Many-core
UC Berkeley [2009] [2012] [2017]
Sensornet Chip Tiger 1GHz Single-Core ARM 2GHz 4-core ARM 3GHz 8-core
(TI MSP430 8MHz Dunnington 3GHz 6-core Intel 4GHz 32-core Intel 6GHz 128-core
core, 10KB RAM) SensorNet Chip
(128MHz core, 160KB RAM)
“Privacy” “Realtime”
© 2011 SAMSUNG Electronics Co.
SW Platform Team. 12 / 27](https://image.slidesharecdn.com/1xsasia11xenarmvirtualization-111102072357-phpapp01/85/Keynote-Speech-Xen-ARM-Virtualization-13-320.jpg)

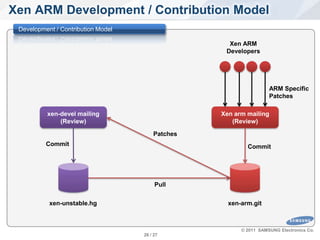
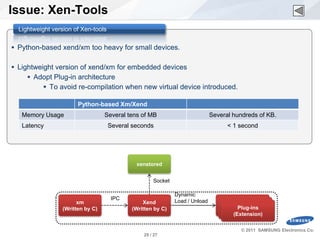
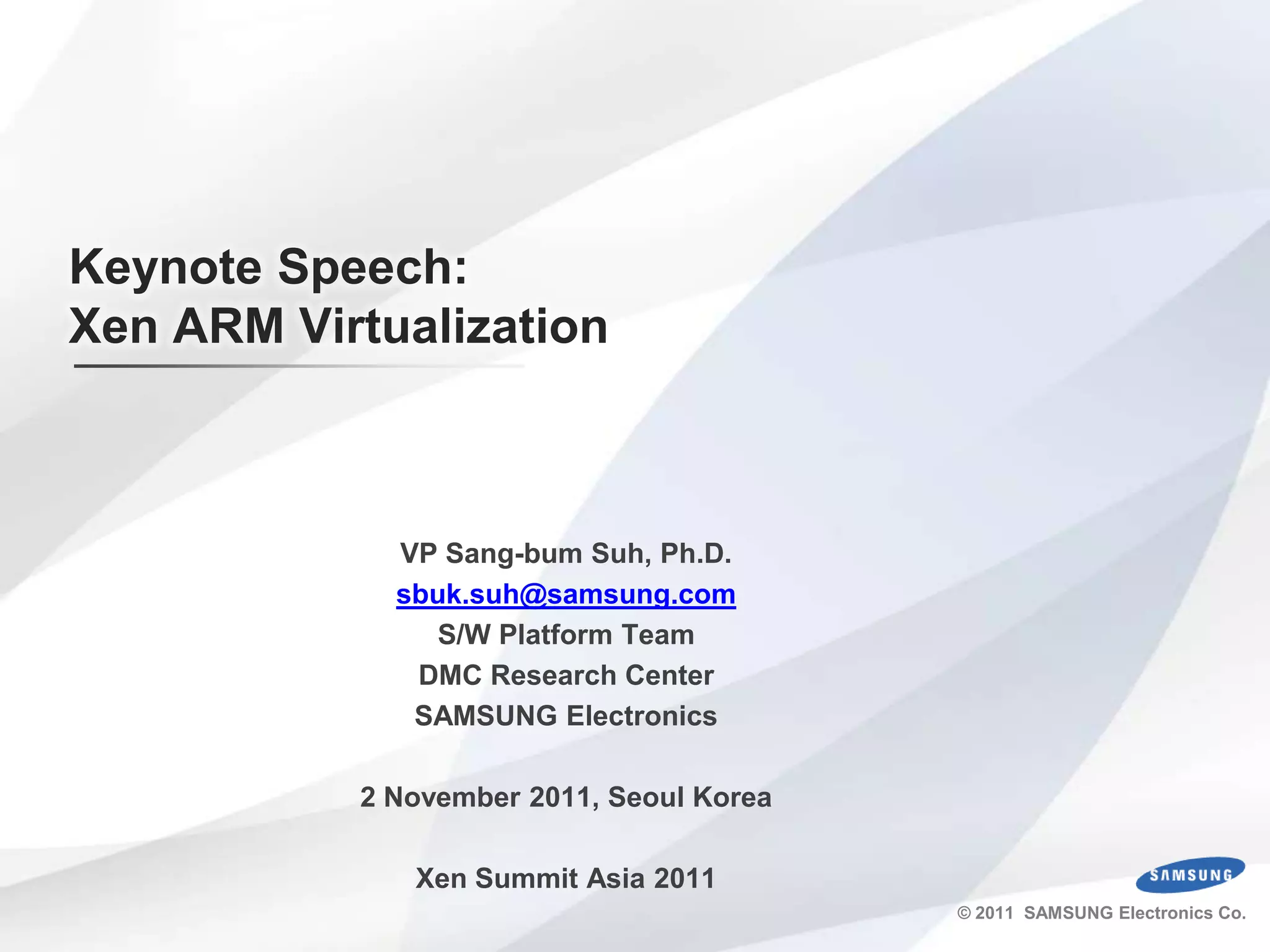
![Issue: Access Control
sHype, XSM and our ACM
sHype[SAI05] XSM [COK06] Xen ARM ACM
Access Control Flexible based on Flexible based on Flexible based on Flask(TE and
Policies Flask(TE and Chinese Flask(TE and Chinese proprietary policy)
Wall) Wall, RBAC, MLS, and
MCS)
Objects of Access Virtual resources and Physical/virtual Physical/virtual resources and
Control domain management resources and domain domain management
management
Protection against N/A N/A Memory, battery, DMA, and
mobile malware- event channels are controlled by
based DoS attacks ACM
Access control to Enforced by ACM at Enforced by ACM at Enforced by ACM at each
objects in each VMM VMM domain(for performance reason)
guest domain
Etc Xen ARM specific hooks
© 2011 SAMSUNG Electronics Co.
SW Platform Team. 31 / 27](https://image.slidesharecdn.com/1xsasia11xenarmvirtualization-111102072357-phpapp01/85/Keynote-Speech-Xen-ARM-Virtualization-32-320.jpg)
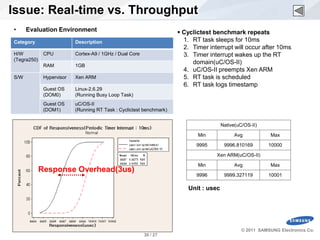
![Mobile Malware Confidential
[Source: F-Secure]
• Number of mobile malware 500 400 421
400 345
– More than 420 mobile phone viruses
(2008) 300
200 146
– Tens of thousands of infections
worldwide 100 27
0
2004 2005 2006 2007 2008
[Source: McAfee]
• Concerns about mobile phone security 100% 6.9 13.9
16.1 18.4
– by market 80%
60%
93.1 86.1
83.9 81.6
40%
Feel safe
20%
Concerned
0%
UK US Japan Total
SW Platform Team.
Mobicom'09, September 20-25, 2009, Beijing, China 33 / 27](https://image.slidesharecdn.com/1xsasia11xenarmvirtualization-111102072357-phpapp01/85/Keynote-Speech-Xen-ARM-Virtualization-34-320.jpg)