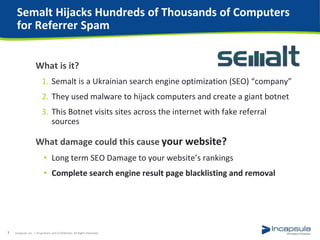
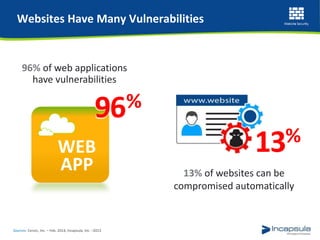
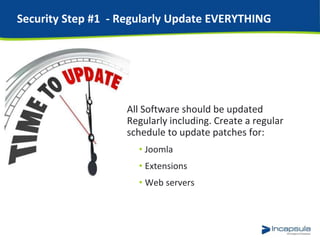
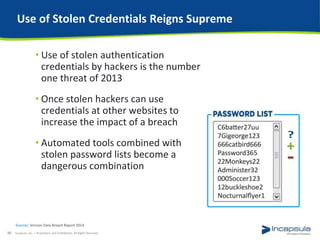
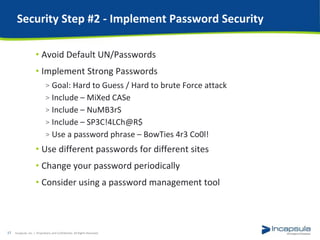
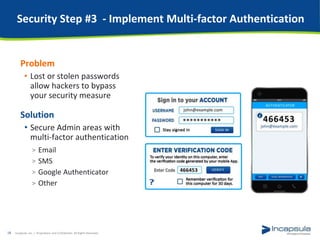
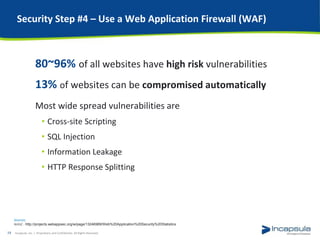
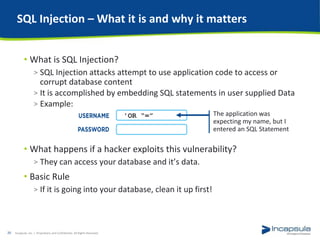
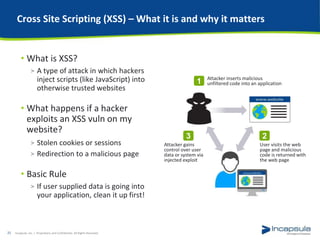
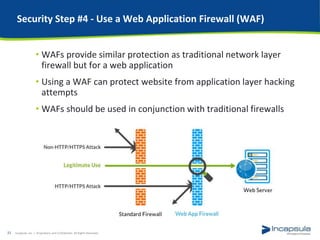
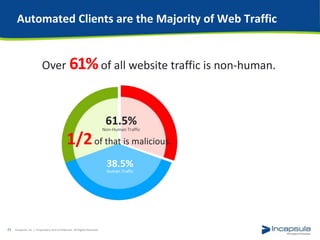
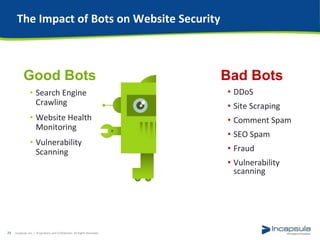
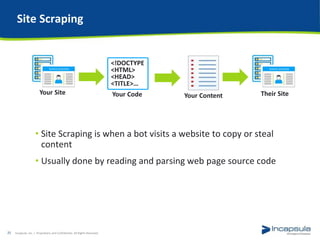
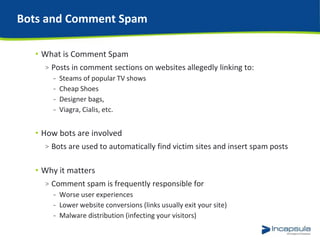
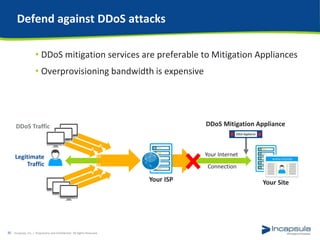
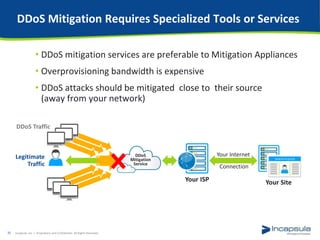
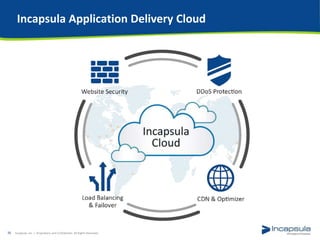
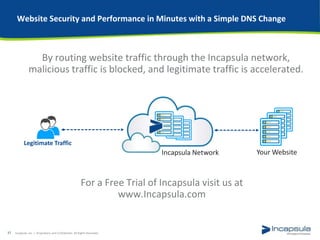
This document outlines seven steps website owners can take to improve the security of their Joomla websites. It begins by discussing recent major security breaches in 2014 like Heartbleed and botnets. It then details the seven steps which are: 1) regularly updating software, 2) implementing strong passwords, 3) multi-factor authentication, 4) using a web application firewall, 5) identifying and blocking bad bots, 6) implementing DDoS mitigation, and 7) using a secure hosting environment. It emphasizes the importance of these steps given the prevalence of vulnerabilities and how automated tools can exploit known issues.


![Heartbleed – the Epic SSL Crisis of 2014
• Heartbleed is a security bug that was
disclosed in April of 2014
• It was present in the widely used
Open SSL Cryptography
• When disclosed, around 17% of
the Internet's secure web servers was vulnerable
• Why do I care?
> The vulnerability allowed for the theft of the servers' private
keys and users' session cookies and passwords
“Some might argue that [Heartbleed] is the worst vulnerability
found since commercial traffic began to flow on the Internet.”
Joseph Steinberg – Forbes
Incapsula, Inc. / Proprietary and Confidential. All Rights Reserved.6](https://image.slidesharecdn.com/joomlasecuritywebinarfinal-141116062753-conversion-gate02/85/Joomla-Security-Simplified-Seven-Easy-Steps-For-a-More-Secure-Website-6-320.jpg)