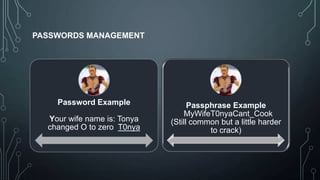
This document provides an overview of securing WordPress websites. It discusses securing the local work environment by keeping software updated, using antivirus and firewalls, and locking down the browser. It also covers securing WordPress installations by using strong passwords, two-factor authentication, keeping software updated, and testing sites in a local environment. The presentation aims to educate users on security best practices to protect against hackers and secure their WordPress websites.