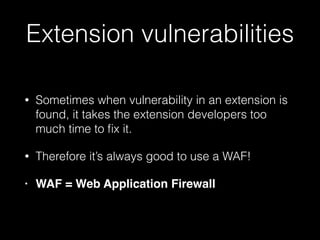
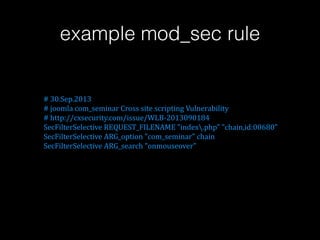
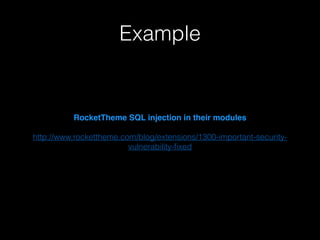
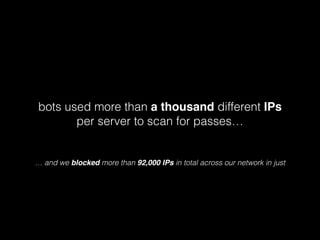
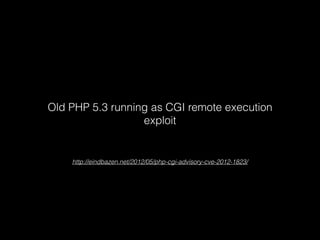
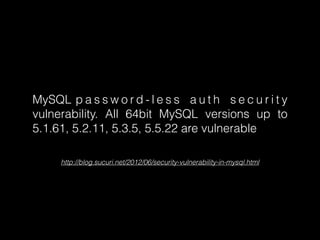
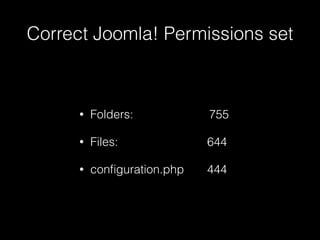
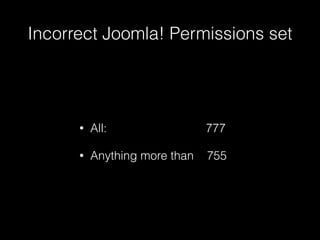
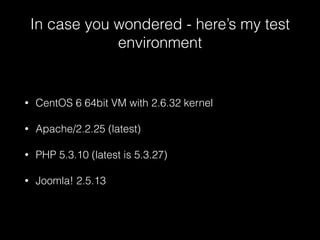
The document presents eight essential tips for securing Joomla! websites, emphasizing the importance of keeping the core, extensions, and themes updated to prevent vulnerabilities. It highlights the need for strong passwords, proper server configurations, and awareness of malware threats. The author, Tenko Nikolov, stresses that security is an ongoing process, not a one-time solution.