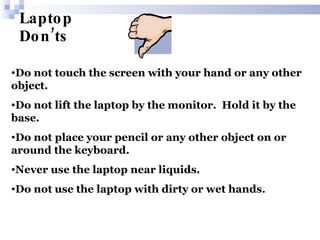
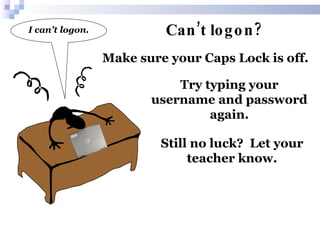
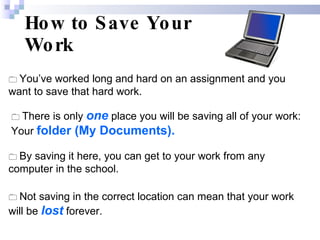
Each student is assigned a numbered laptop and shelf. Students must only use their assigned laptop, and should unplug it before removing it from the cabinet. The document provides instructions on properly handling and using laptops, such as only using clean hands, carrying it securely with two hands, asking permission before printing, and returning it to the proper shelf. Students are told to save work only in their personal folder and follow the technology agreement.