Recommended
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PPTX
PPTX
PPTX
PDF
PDF
PDF
Financial management lecture 6
PPT
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PPTX
PPTX
More Related Content What's hot
PDF
PDF
PDF
PPTX
PPTX
PPTX
PDF
PDF
PDF
Financial management lecture 6
PPT
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
More from Muuluu
PPTX
PPTX
PPTX
PDF
PPT
PPT
PPT
DOC
PPT
PPT
PDF
PPT
PPTX
PPTX
PDF
PPTX
PPTX
PDF
PDF
PDF
IV лекц 1. 2. 3. 4. 5. 6. Áàðèìòòàé àæèëëàõ
Áàðèìò ¿¿ñãýõ, íýýõ
Ýíä Word äýýð øèíý áàðèìò ¿¿ñãýõ, áýëýí
áàðèìò íýýõ, áàðèìòûã õàäãàëàõ õýäýí
àðãûã àâ÷ ¿çüå:
Øèíý áàðèìò ¿¿ñãýõ
Øèíý áàðèìò ¿¿ñãýõäýý äàðààõ àðãóóäààñ
àëü íýãèéã íü ñîíãîíî:
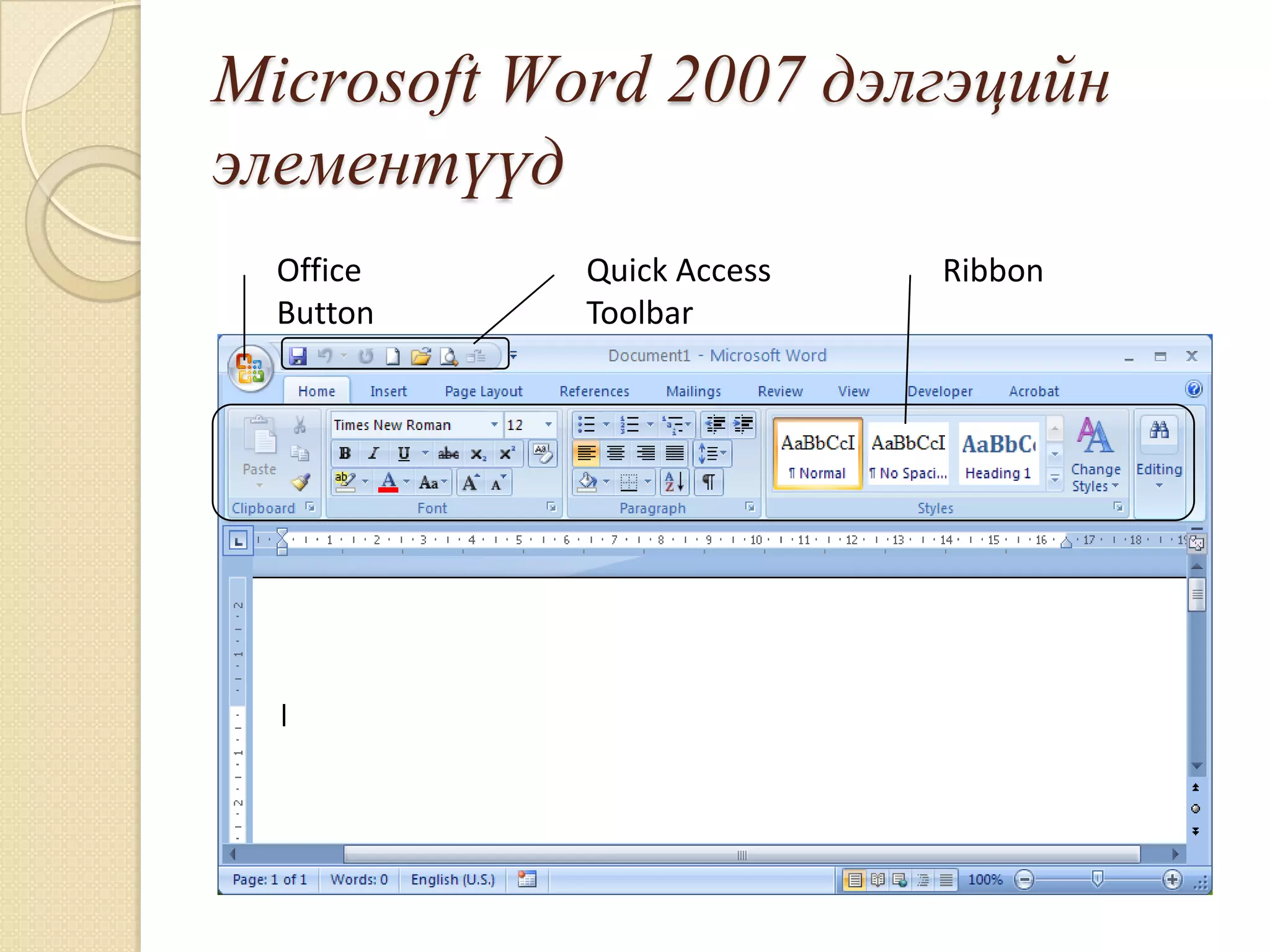
1. Quick Access Toolbar|New òîâ÷ äàðíà.
2. Office Button|New êîìàíä ñîíãîíî.
3. Ãàðíû CTRL+N òîâ÷èéã äàðíà.
7. Áýëýí áàðèìò íýýõ
Áýëýí áàðèìò íýýõäýý äàðààõ àðãóóäààñ
àëü íýãèéã íü ñîíãîíî:
1. Quick Access Toolbar|Open òîâ÷
äàðíà.
2. Office Button |Open êîìàíä ñîíãîíî.
3. Ãàðíû CTRL+O òîâ÷ äàðíà.
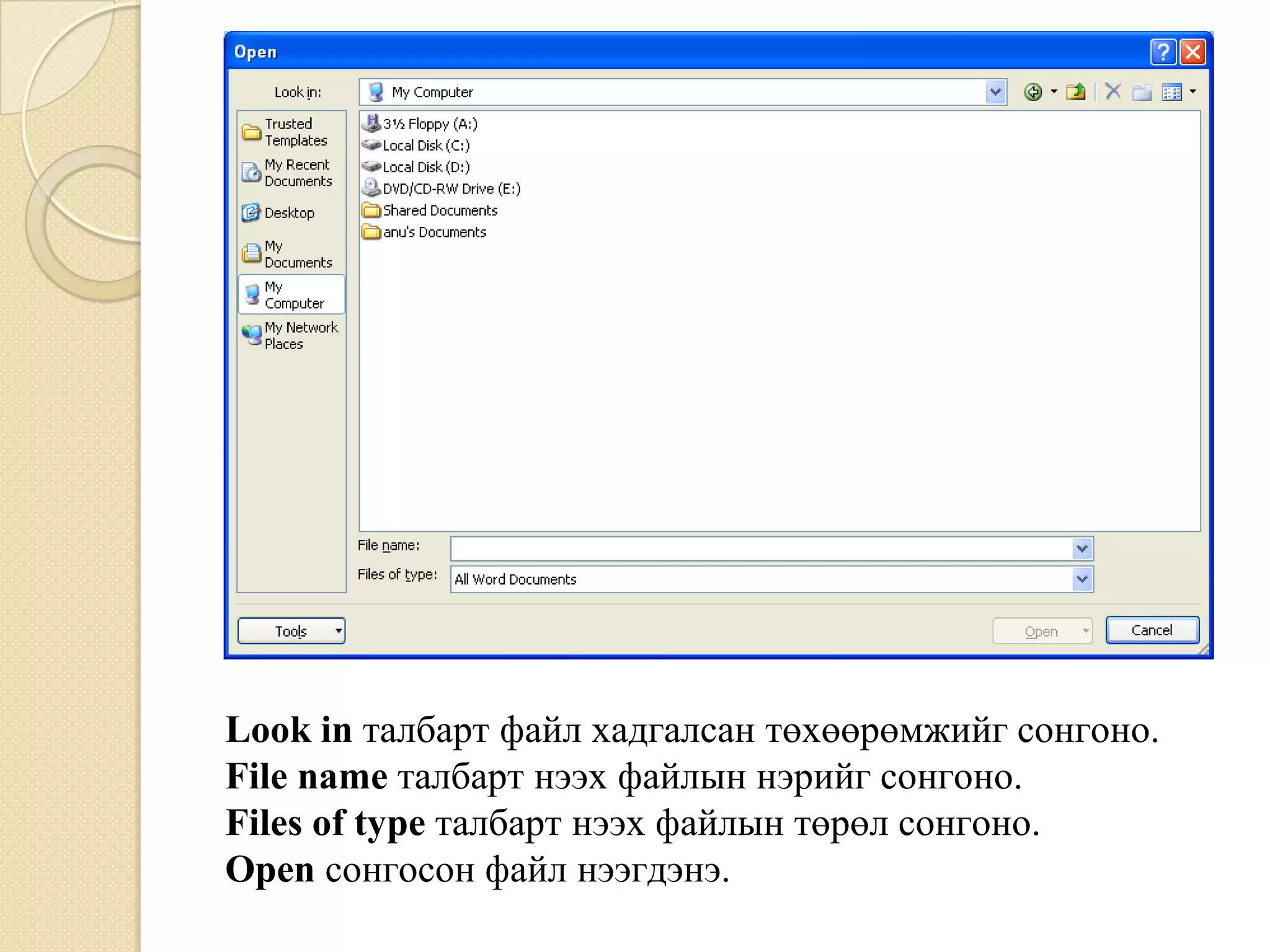
Àëü ÷ àðãûã ñîíãîñîí Open õàðèëöàõ
öîíõ õàðóóëíà. Ôàéëàà ñîíãîîä Open
òîâ÷èéã äàðæ áàðèìòàà íýýíý.
8. Look in òàëáàðò ôàéë õàäãàëñàí òºõººðºìæèéã ñîíãîíî.
File name òàëáàðò íýýõ ôàéëûí íýðèéã ñîíãîíî.
Files of type òàëáàðò íýýõ ôàéëûí òºðºë ñîíãîíî.
Open ñîíãîñîí ôàéë íýýãäýíý.
9. Áàðèìò õàäãàëàõ
Áàðèìò õàäãàëàõäàà äàðààõ àðãóóäààñ
àëü íýãèéã íü ñîíãîíî:
1. Quick Access Toolbar|Save òîâ÷ äàðíà.
2. Office Button|Save êîìàíä ñîíãîíî.
3. Ãàðíû CTRL+S òîâ÷ äàðíà.
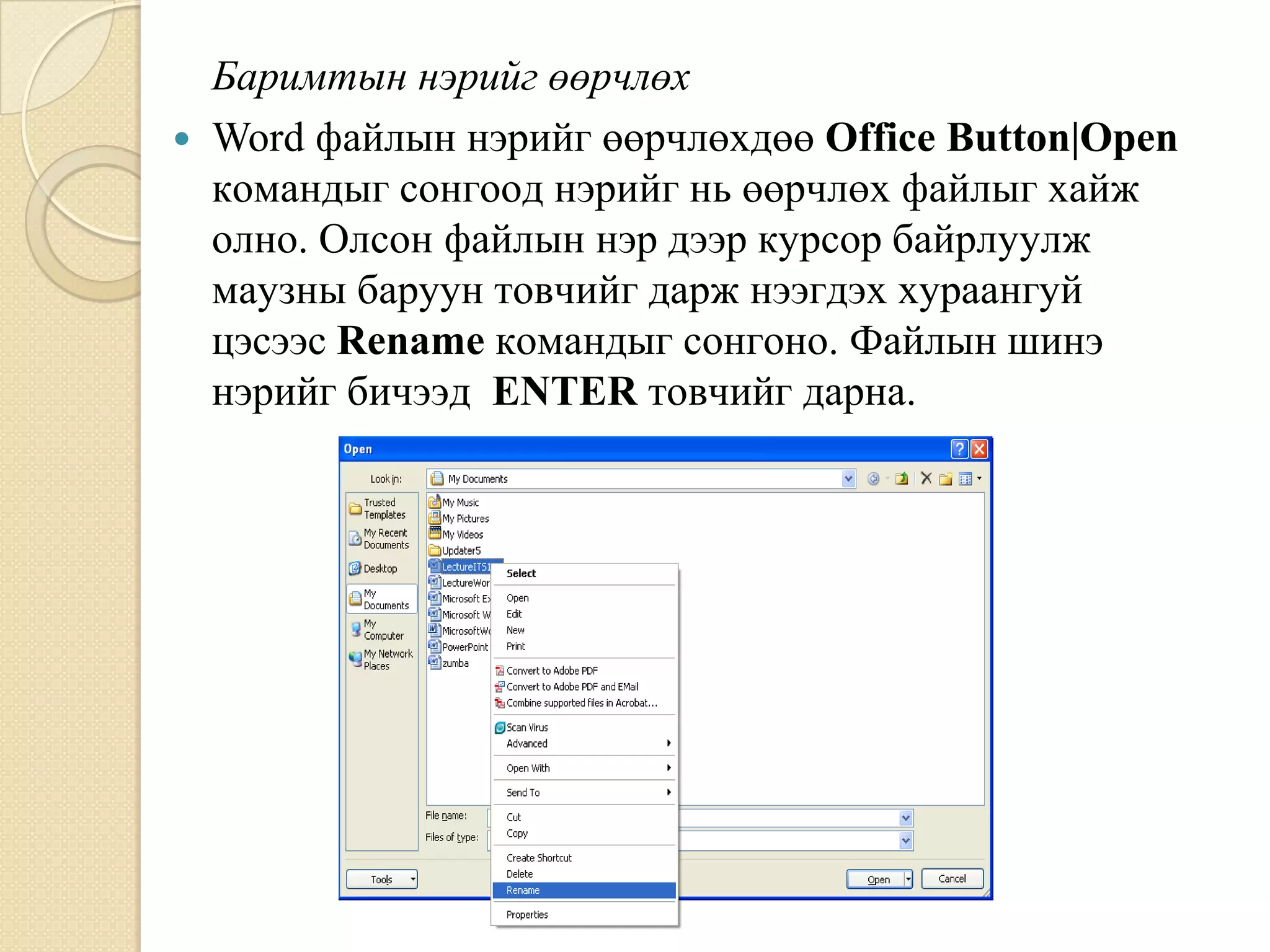
10. Áàðèìòûí íýðèéã ººð÷ëºõ
Word ôàéëûí íýðèéã ººð÷ëºõ人 Office Button|Open
êîìàíäûã ñîíãîîä íýðèéã íü ººð÷ëºõ ôàéëûã õàéæ
îëíî. Îëñîí ôàéëûí íýð äýýð êóðñîð áàéðëóóëæ
ìàóçíû áàðóóí òîâ÷èéã äàðæ íýýãäýõ õóðààíãóé
öýñýýñ Rename êîìàíäûã ñîíãîíî. Ôàéëûí øèíý
íýðèéã áè÷ýýä ENTER òîâ÷èéã äàðíà.
11. Îëîí áàðèìòòàé àæèëëàõ
Õýðýâ òà îëîí áàðèìò çýðýã çàñâàðëàõ áîë õýä
õýäýí áàðèìòûã íýã çýðýã íýýæ áîëíî.
Íýýëòòýé áàéãàà ººð áàðèìòûã ñîíãîõäîî
äàðààõ àðãóóäààñ àëü íýãèéã íü àâíà:
1. Дýëãýöèéí äîîä õýñýãò áàéðëàõ taskbar äýýðõ
íýðèéã íü äàðíà.
2. View|Window|Switch Windows -ààñ íýðèéã íü
äàðíà.
Áàðèìò õààõ
Áàðèìòûã õààõäàà äàðààõ àðãóóäààñ àëü íýãèéã
íü ñîíãîíî.
1. Quick Access Toolbar|Close òîâ÷ äàðíà.
2. Office Button| Close êîìàíä ñîíãîíî.
3. Ãàðíû CTRL+W òîâ÷ äàðíà.
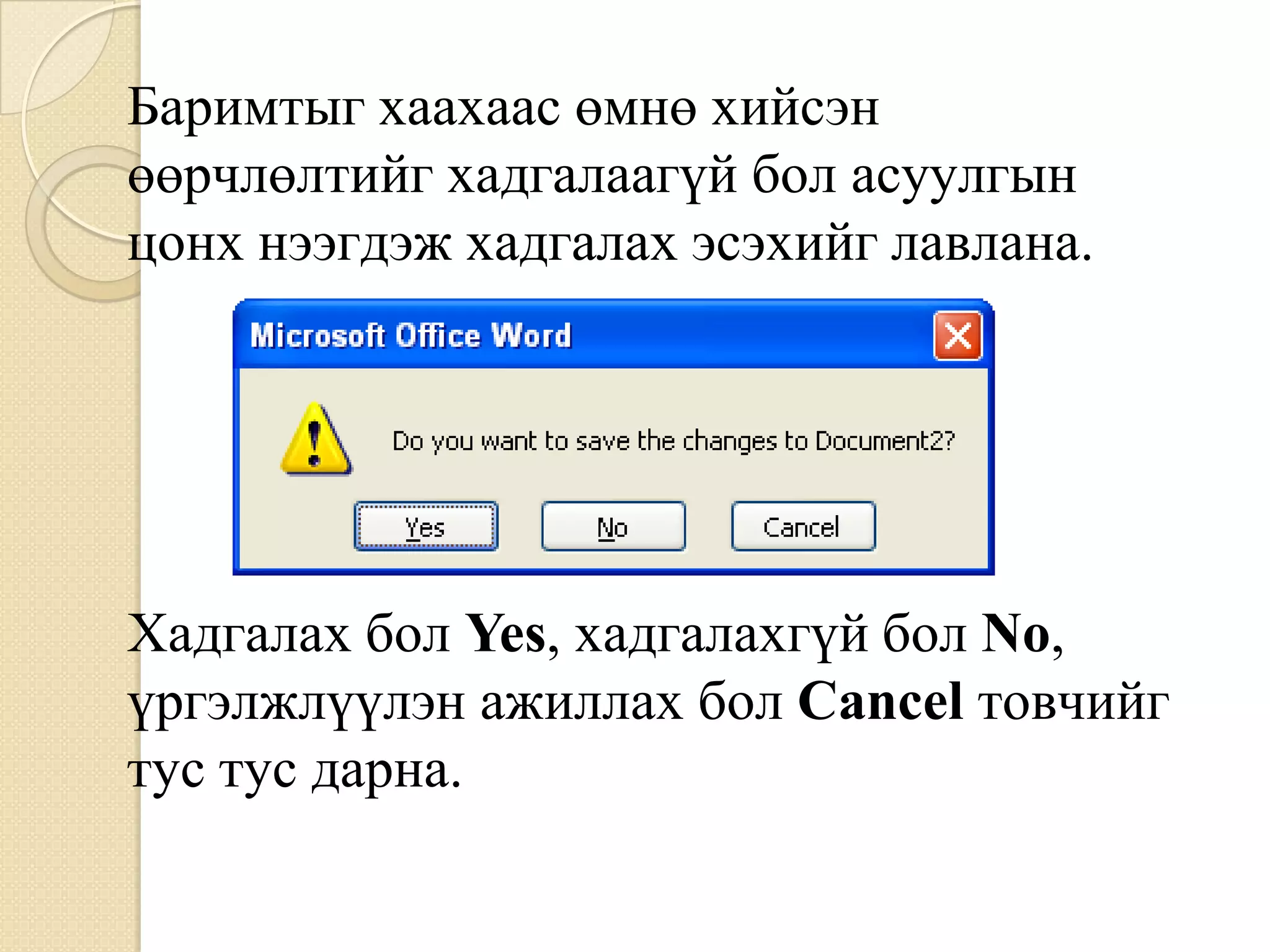
12. Áàðèìòûã õààõààñ ºìíº õèéñýí
ººð÷ëºëòèéã õàäãàëààã¿é áîë àñóóëãûí
öîíõ íýýãäýæ õàäãàëàõ ýñýõèéã ëàâëàíà.
Õàäãàëàõ áîë Yes, õàäãàëàõã¿é áîë No,
¿ðãýëæë¿¿ëýí àæèëëàõ áîë Cancel òîâ÷èéã
òóñ òóñ äàðíà.