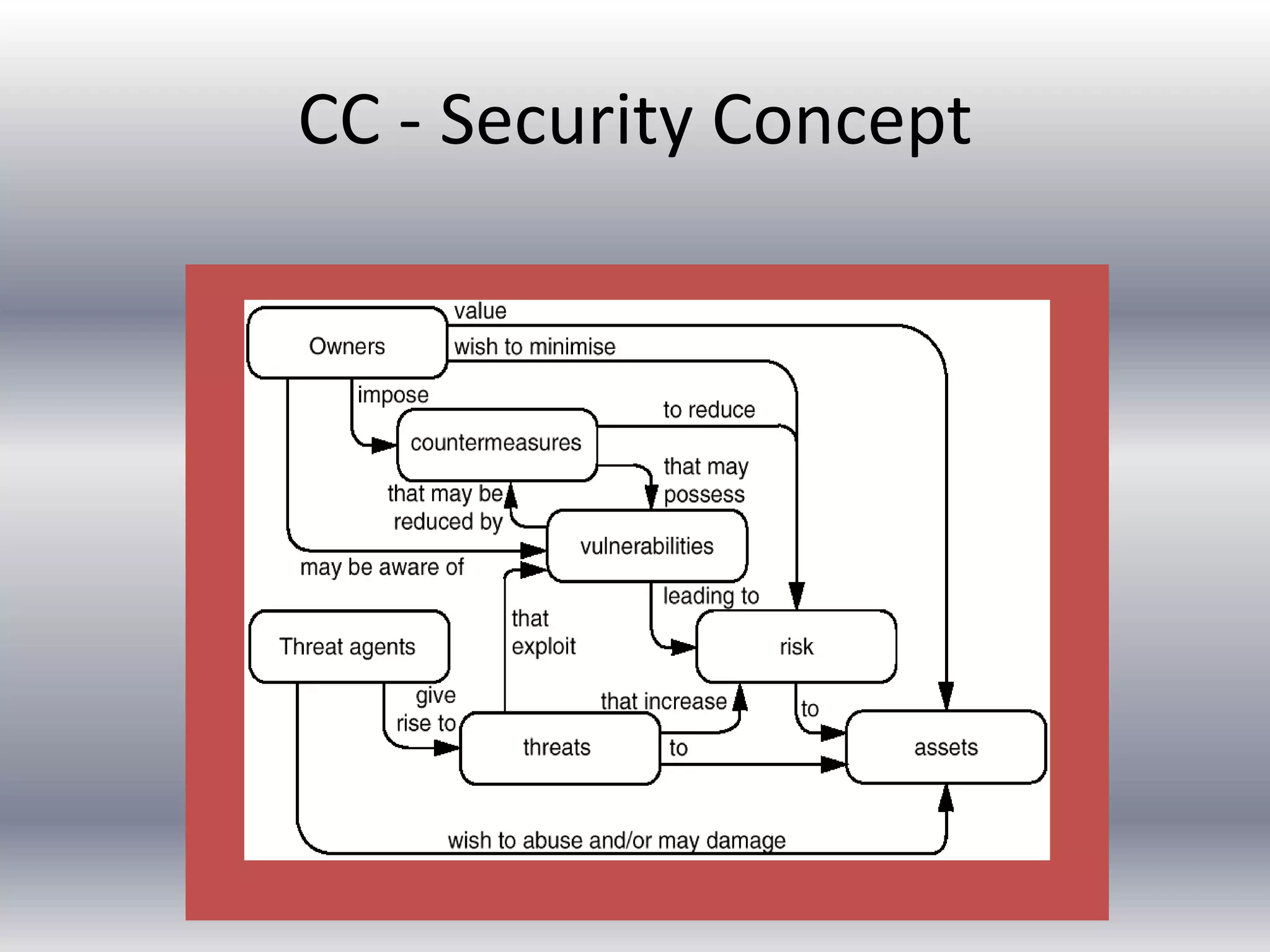
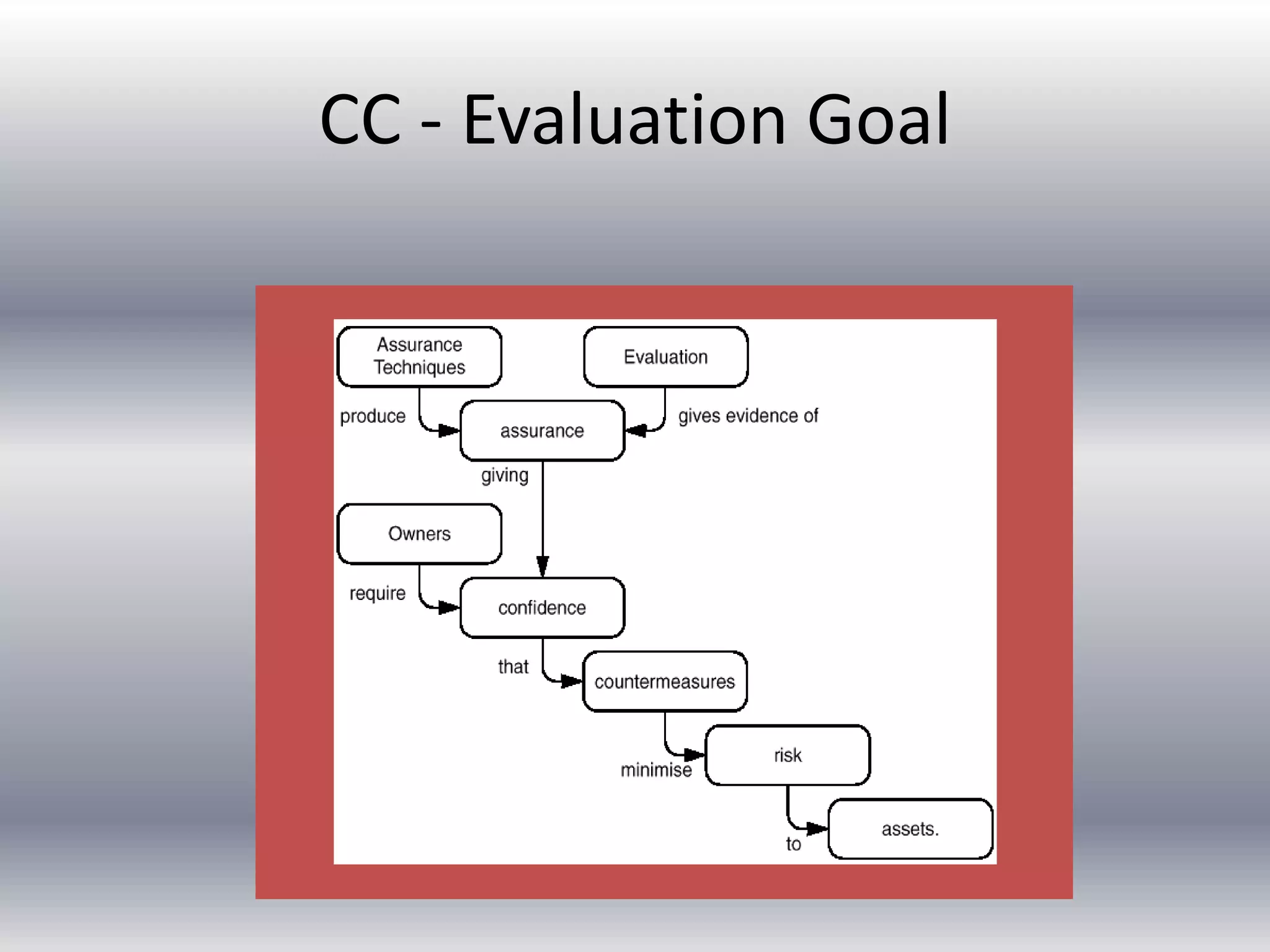
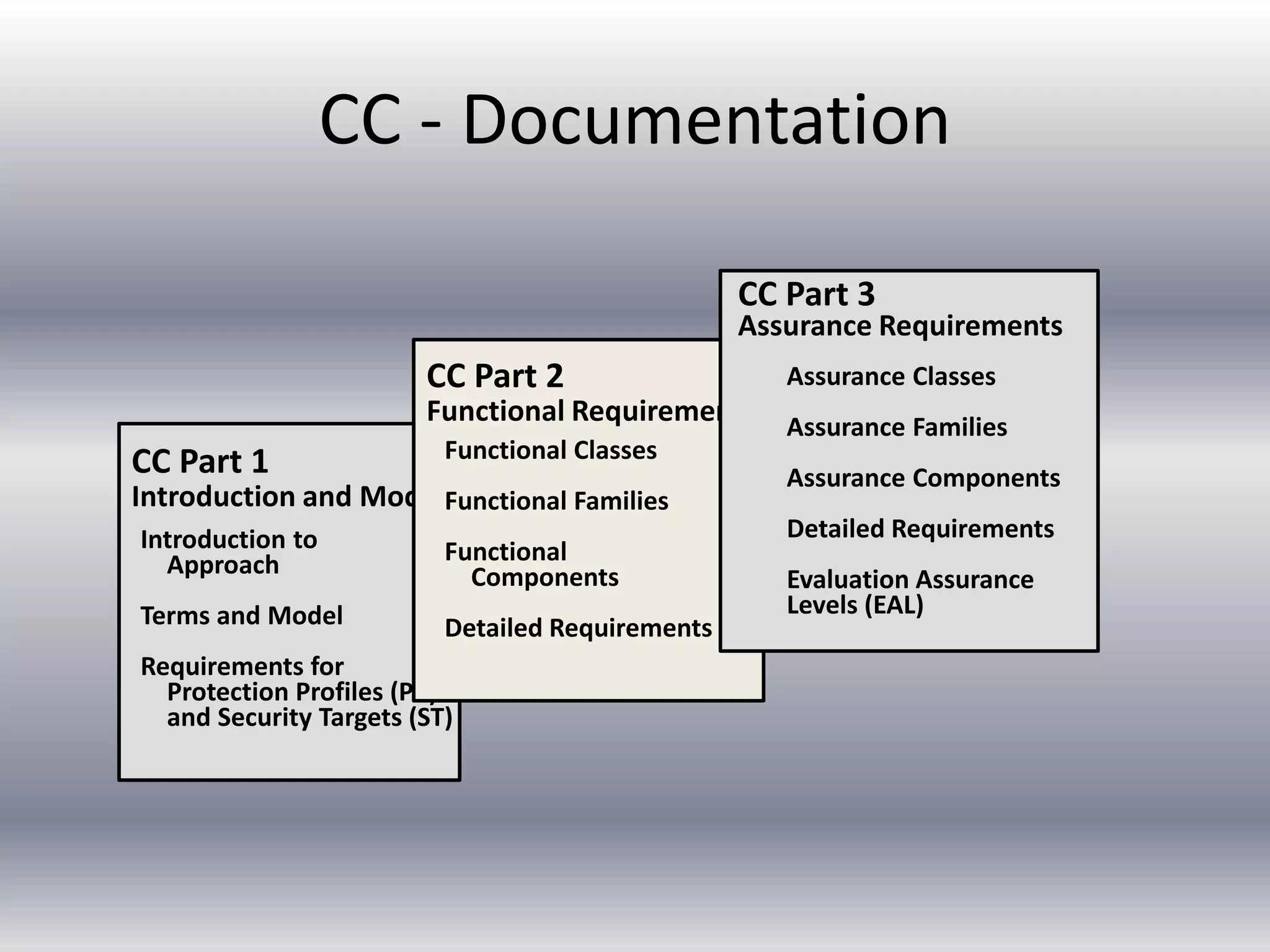
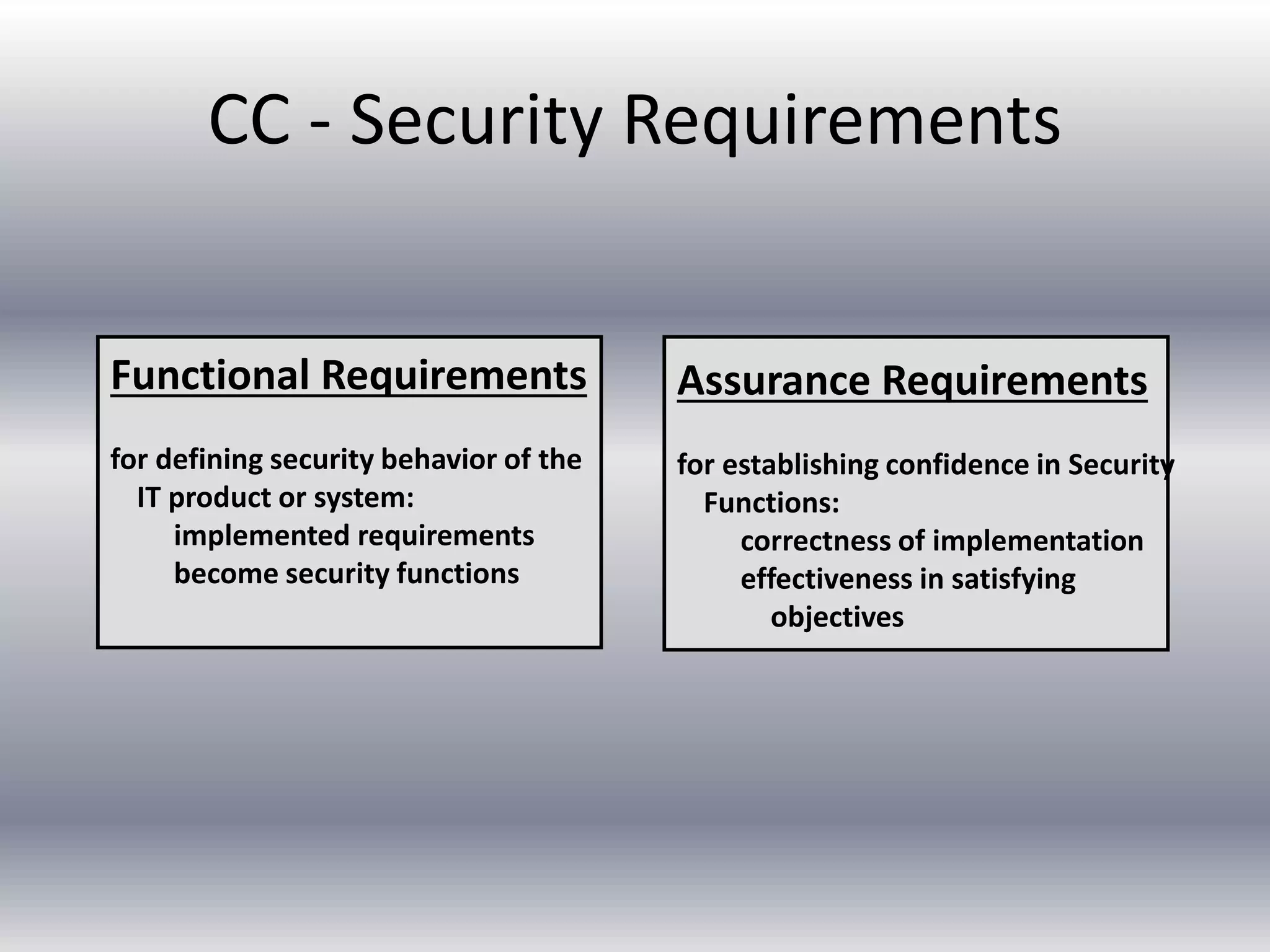
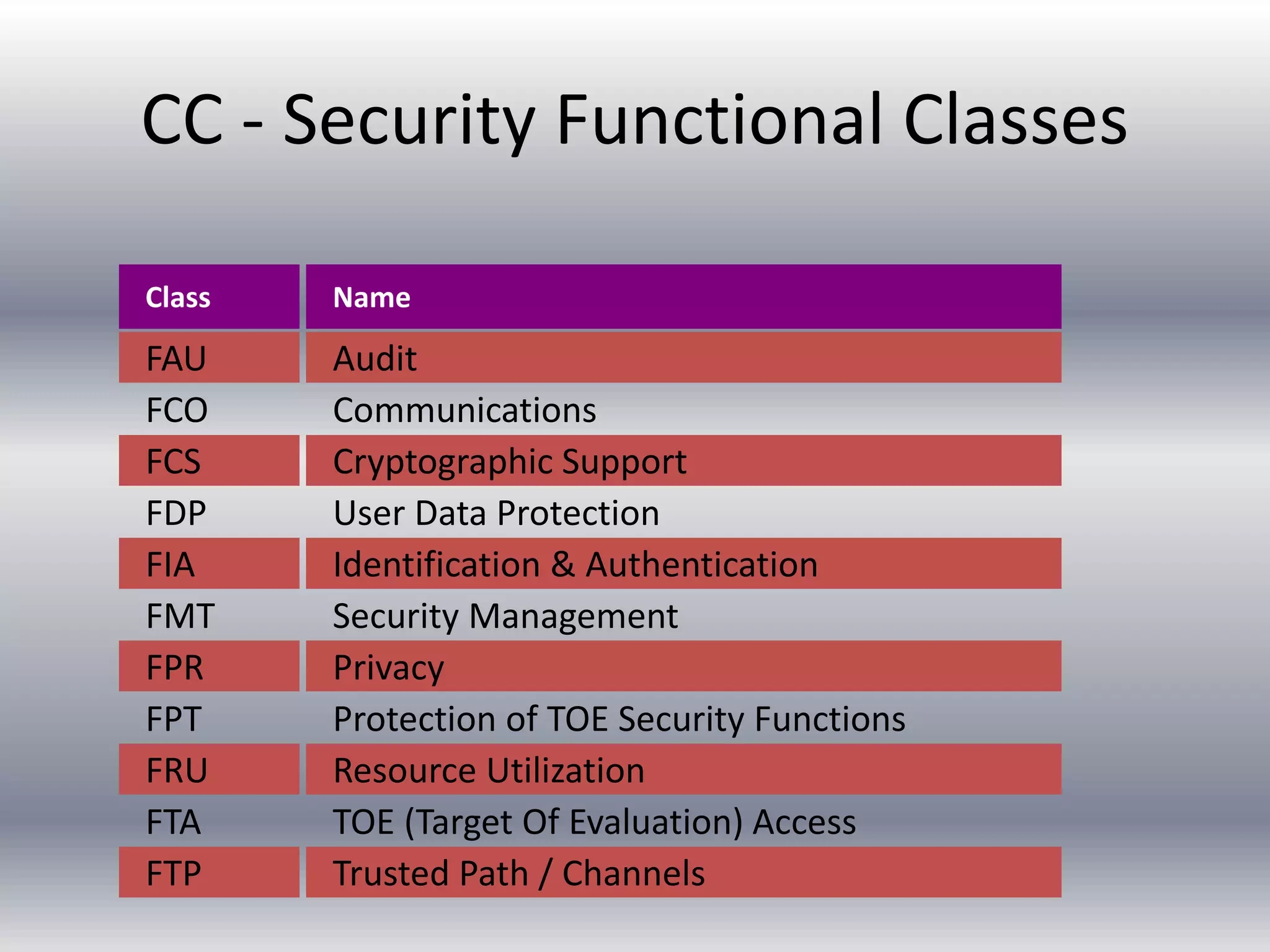
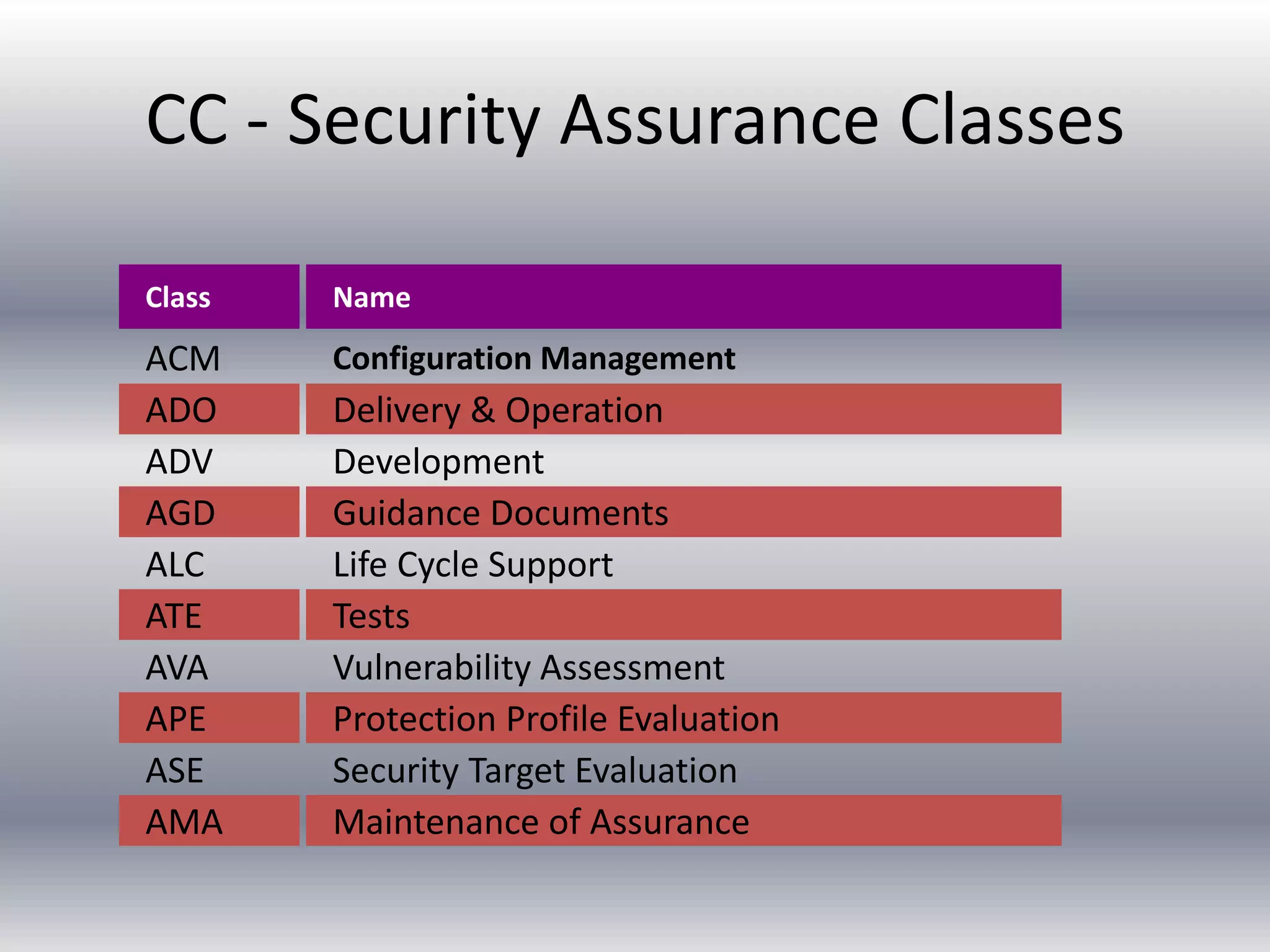
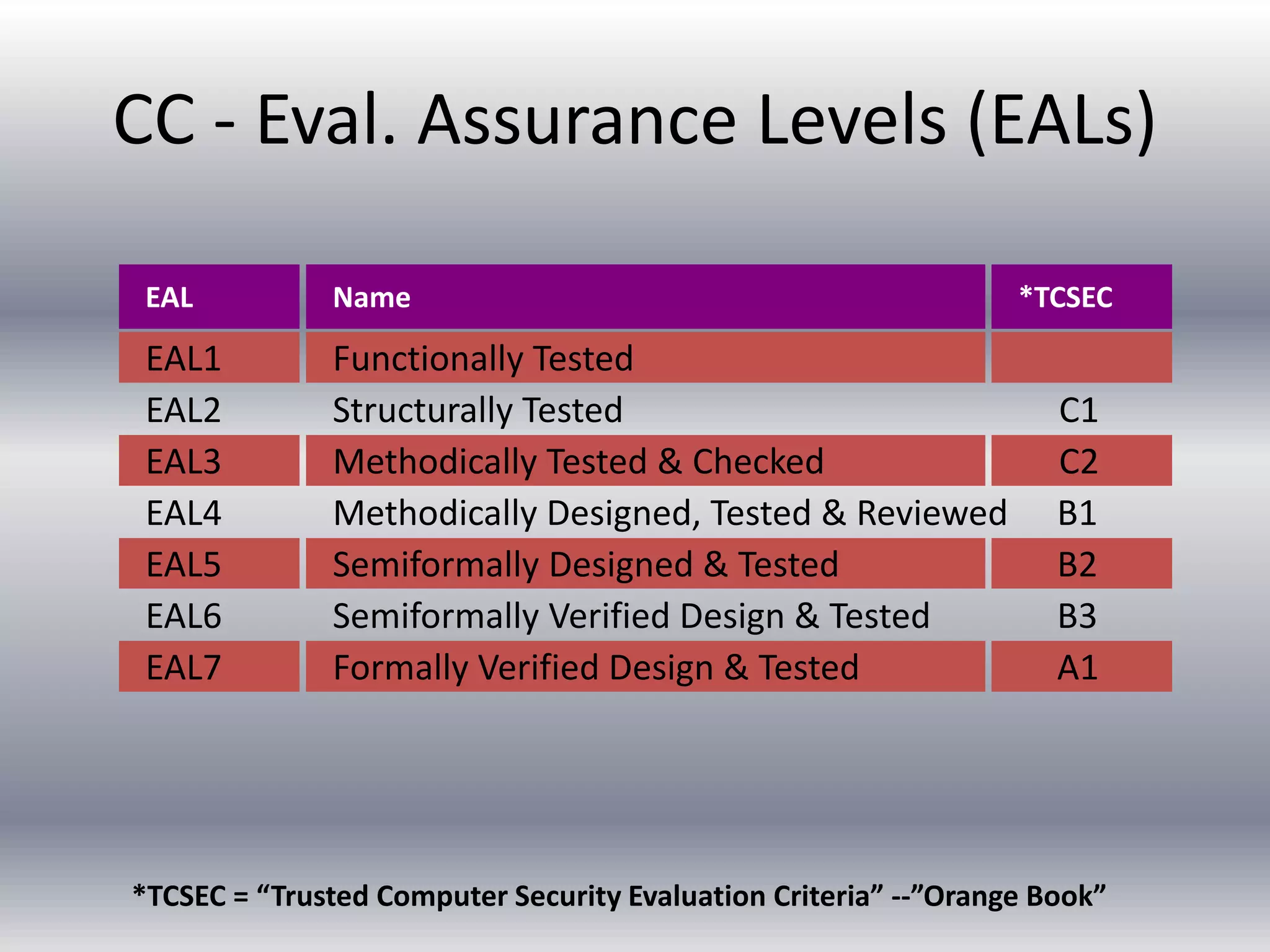
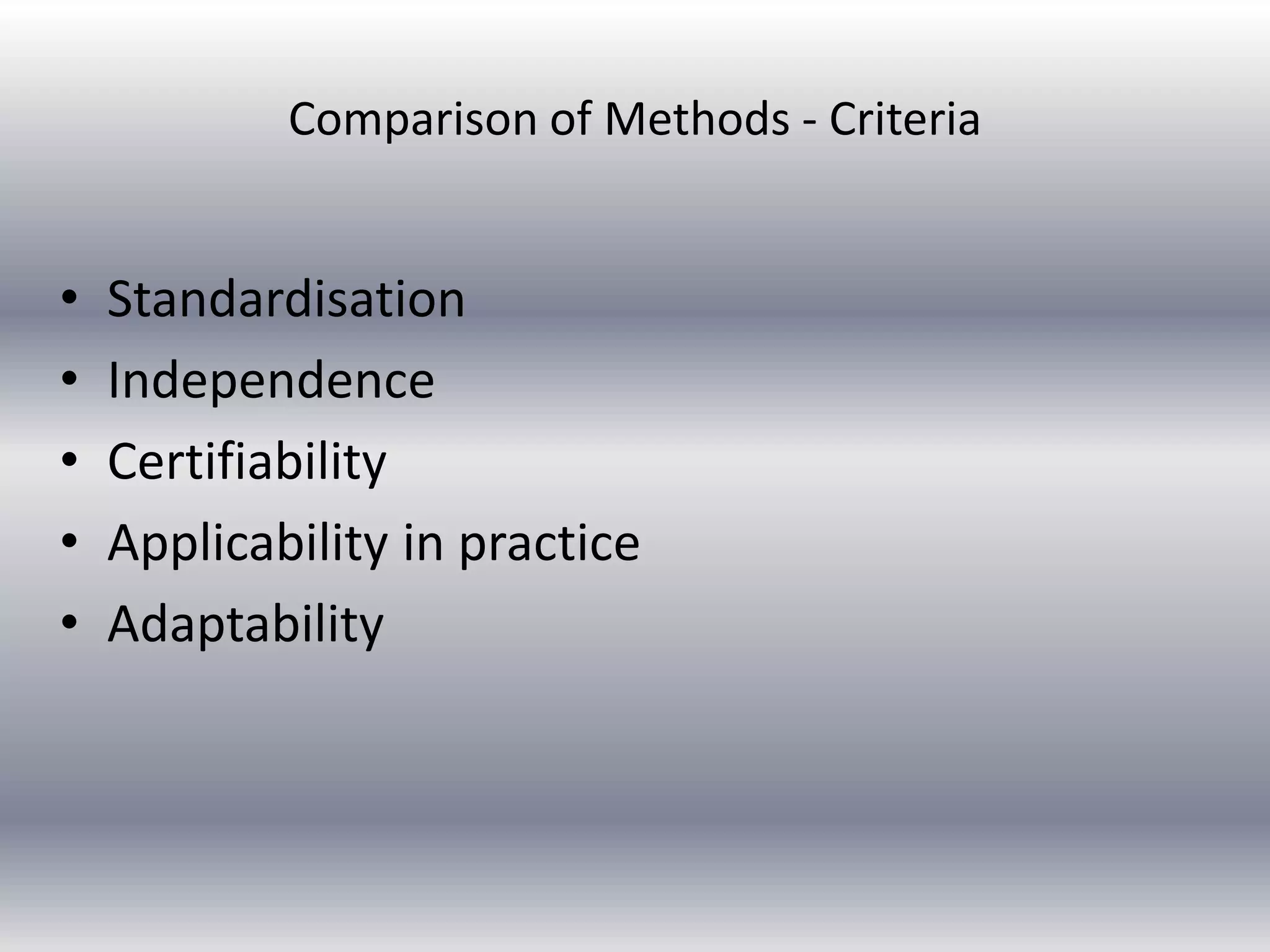
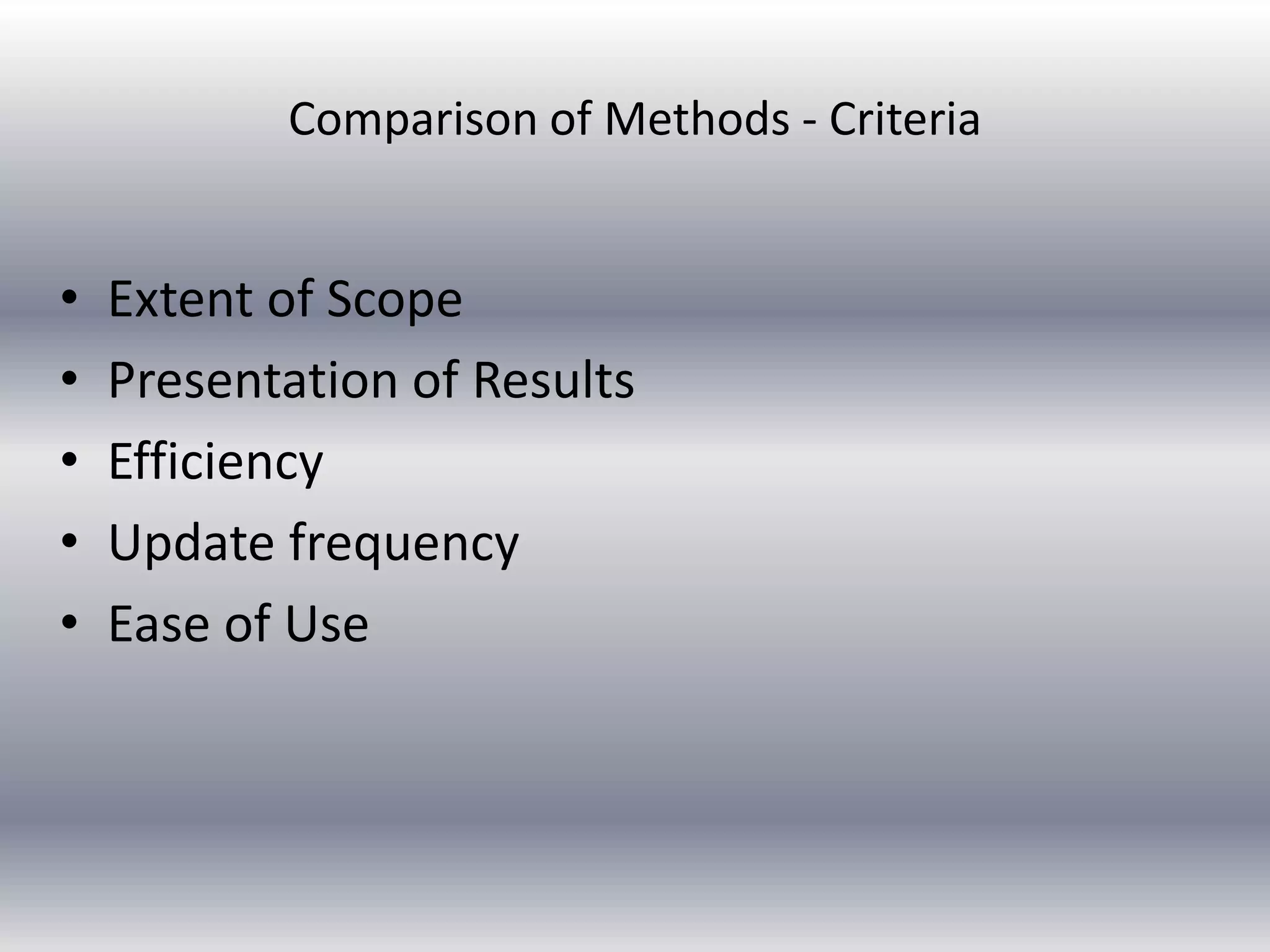
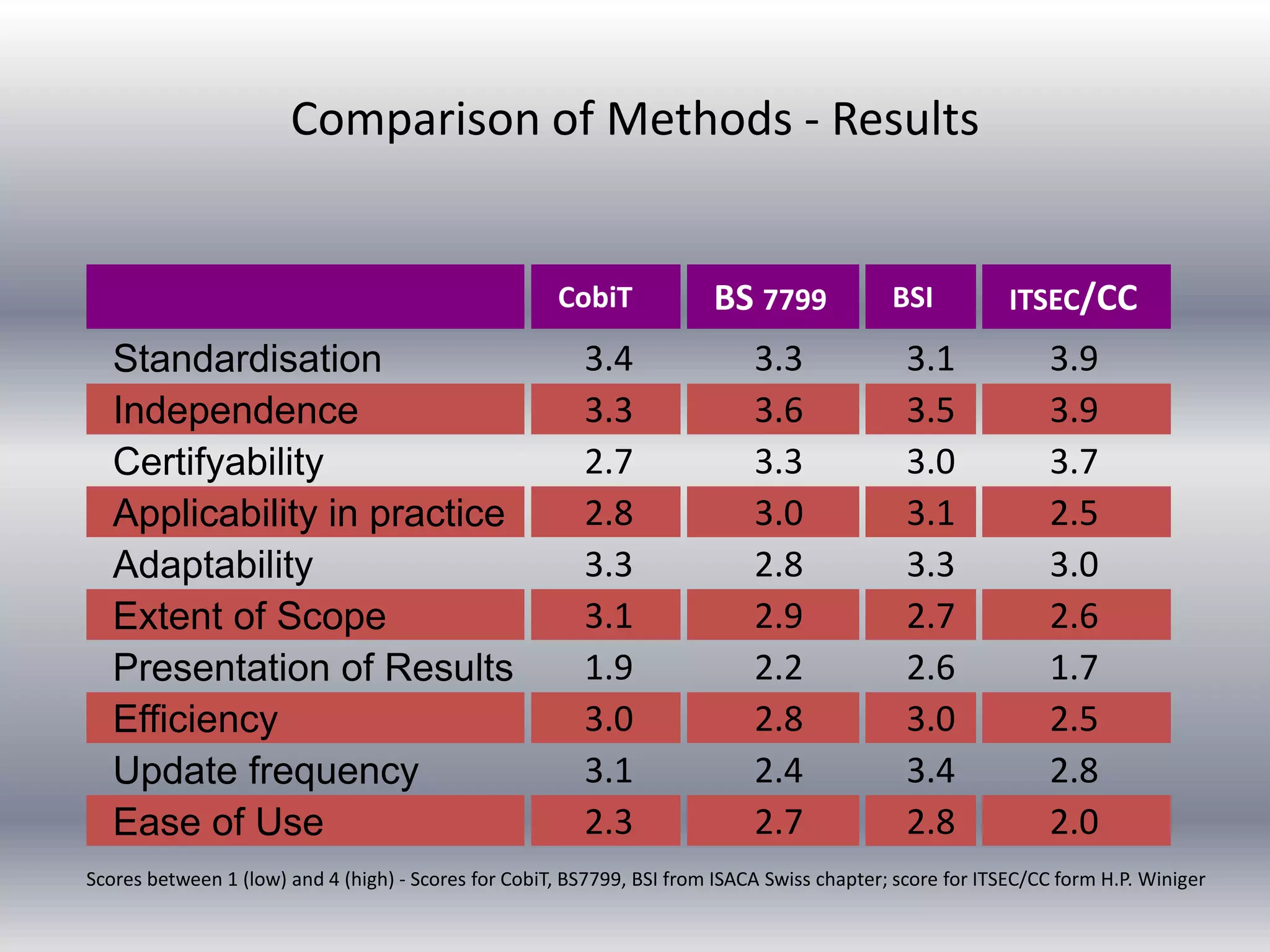
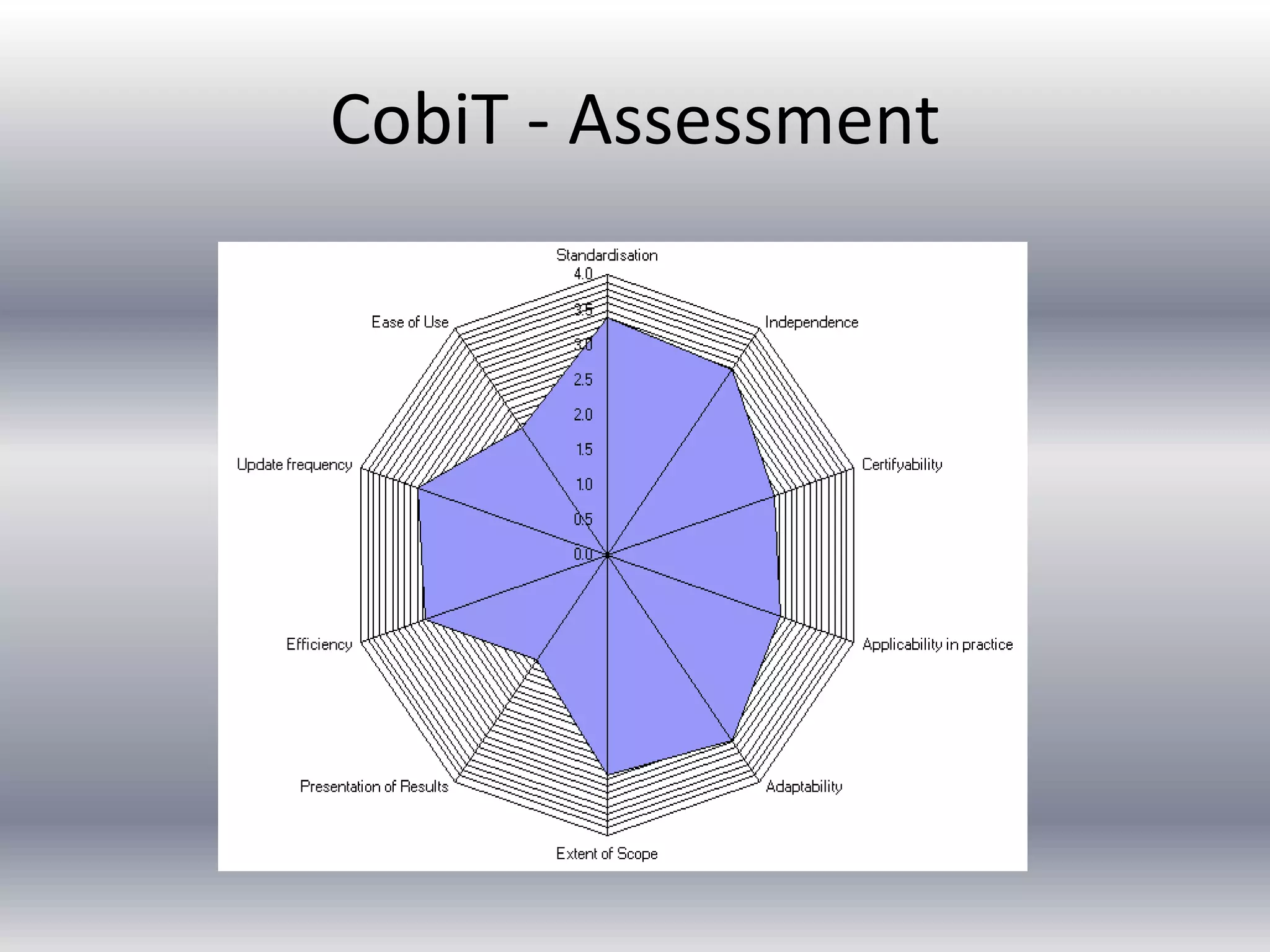
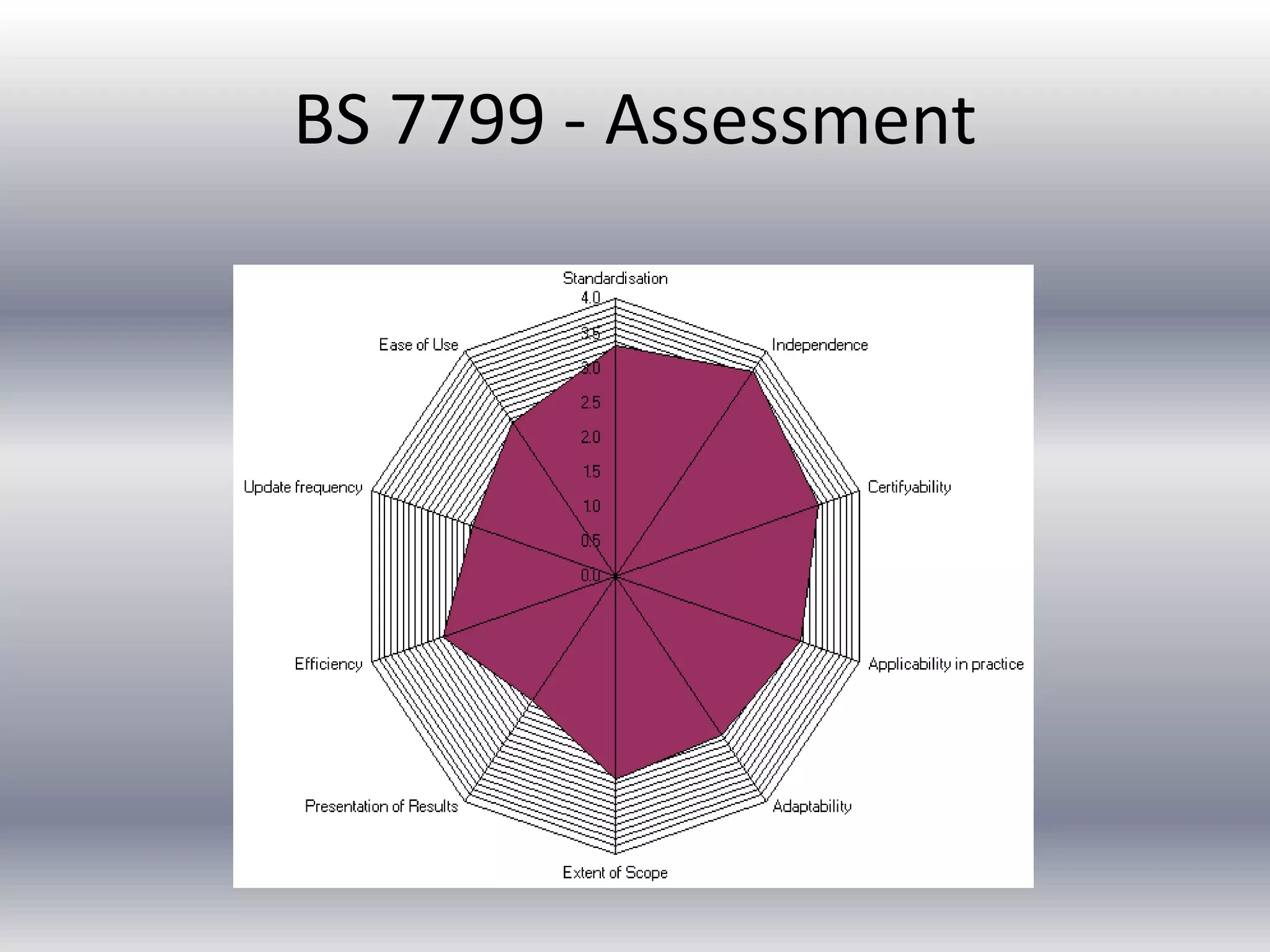
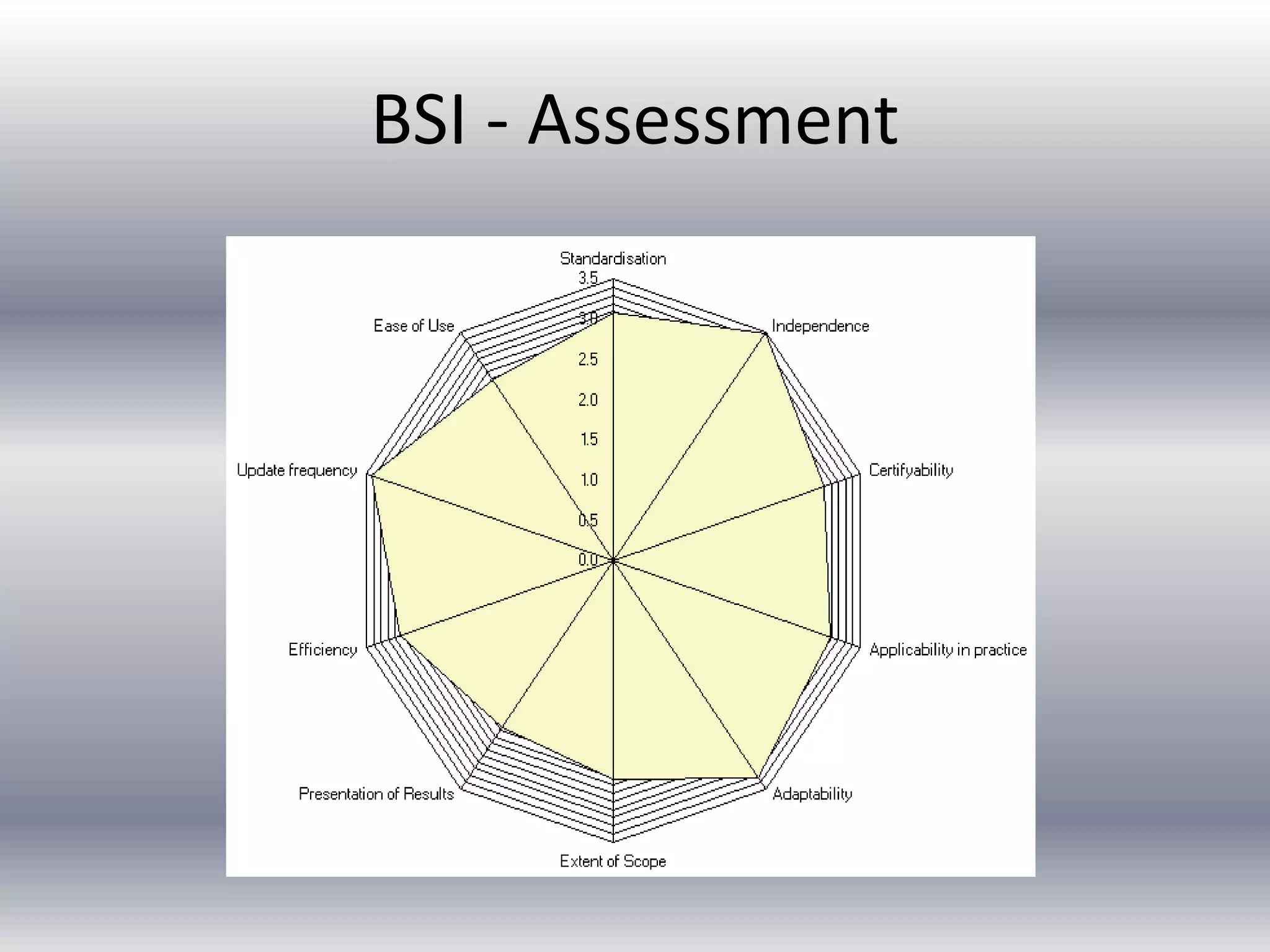
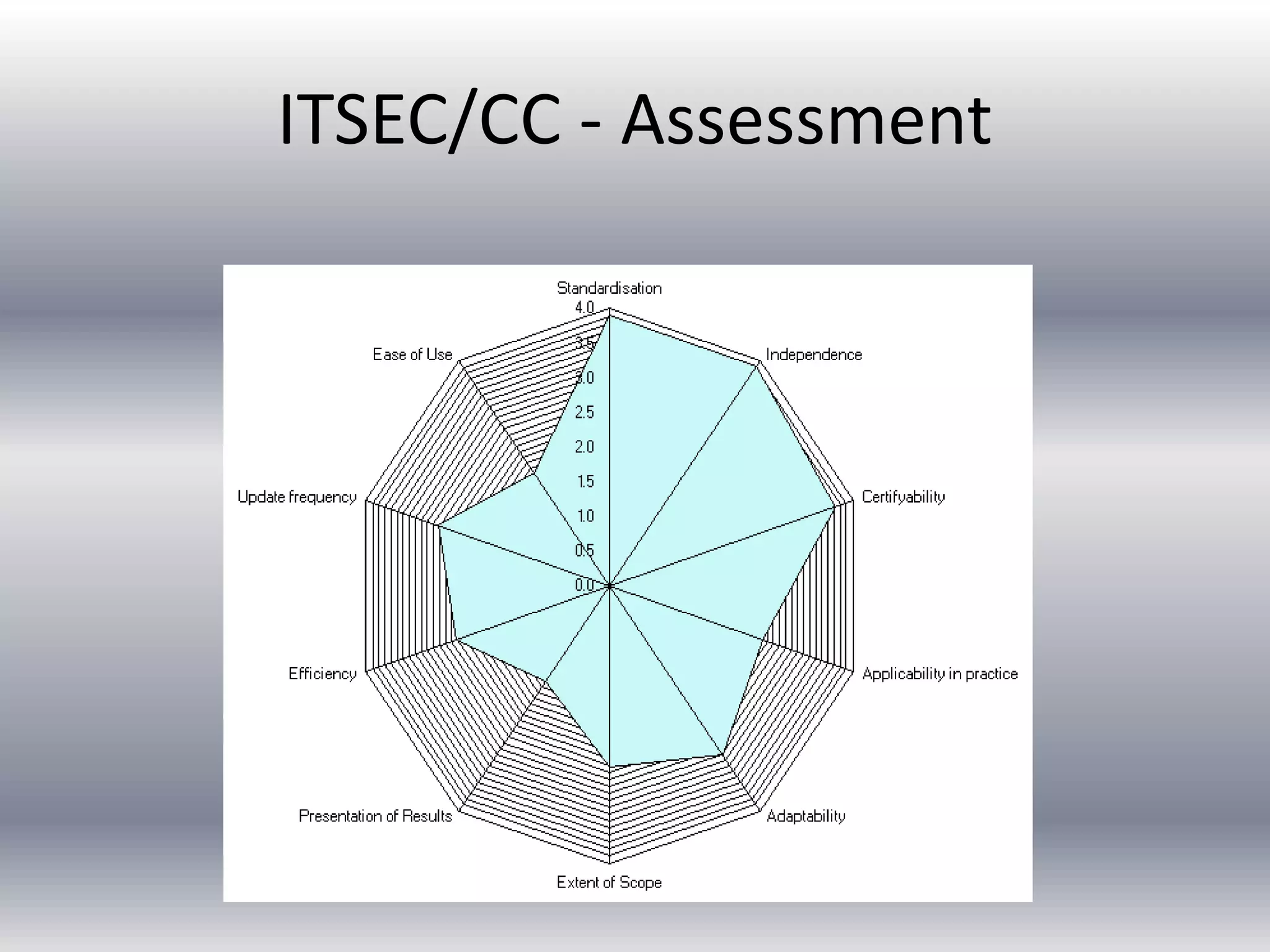
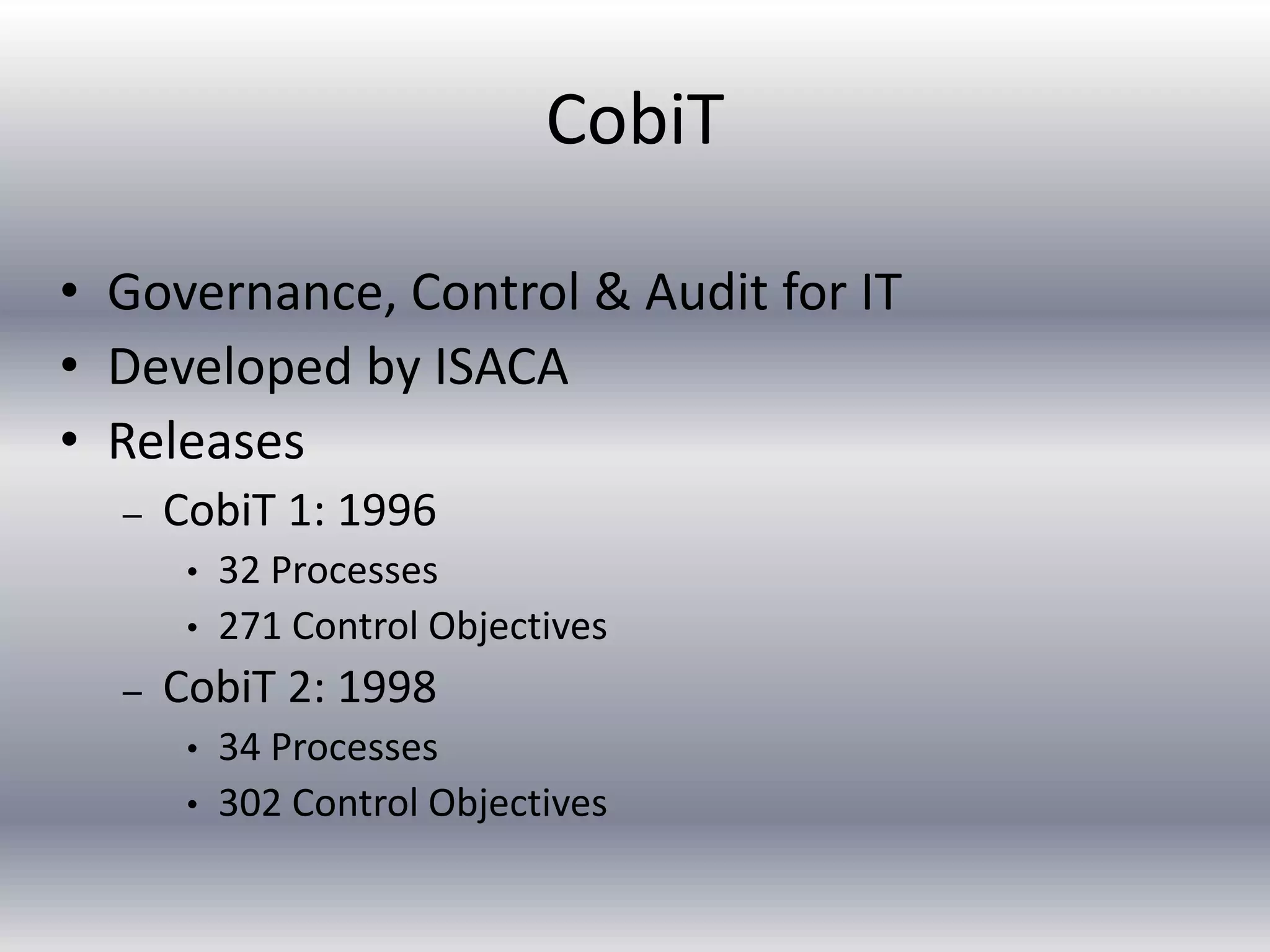
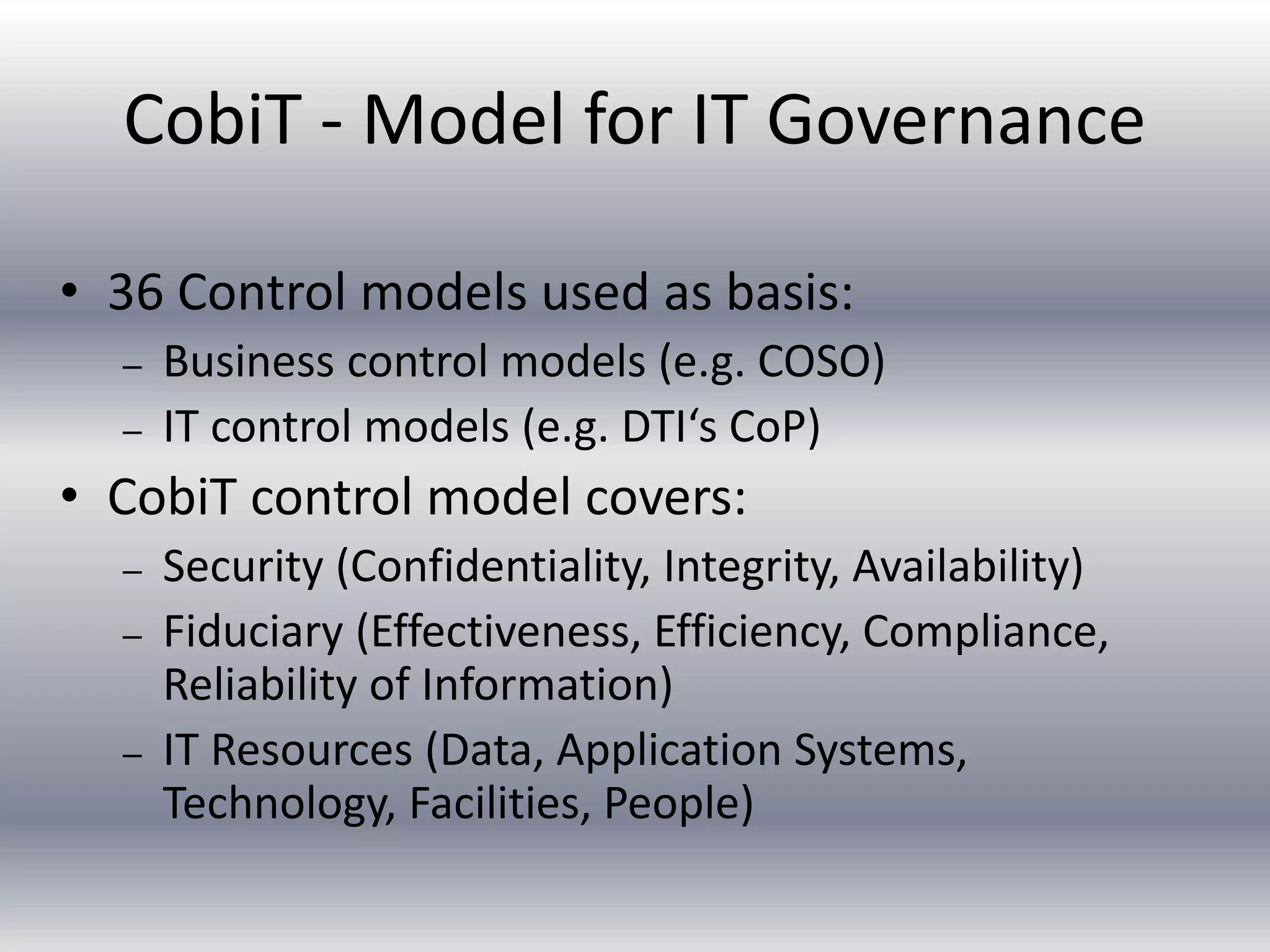
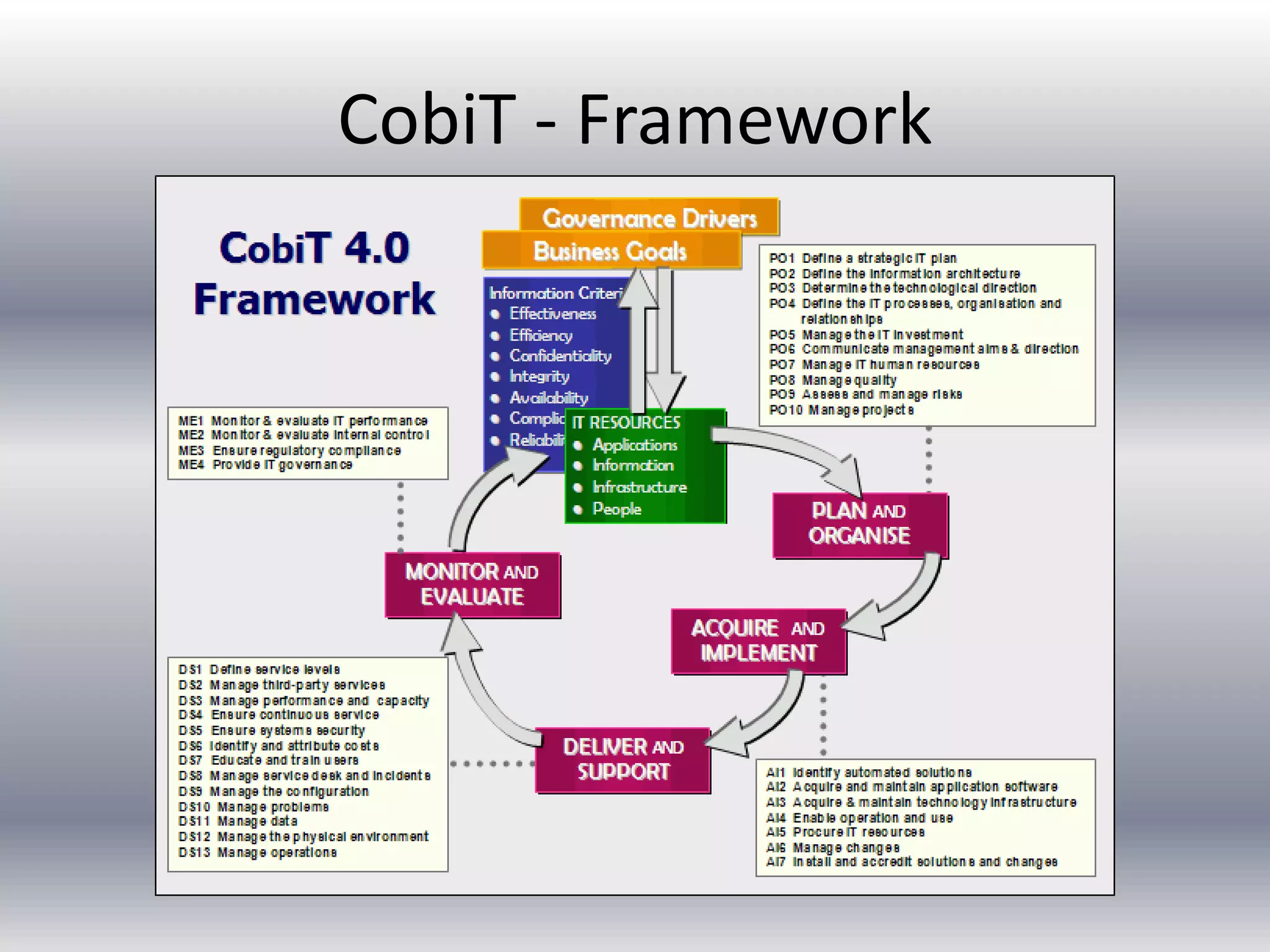
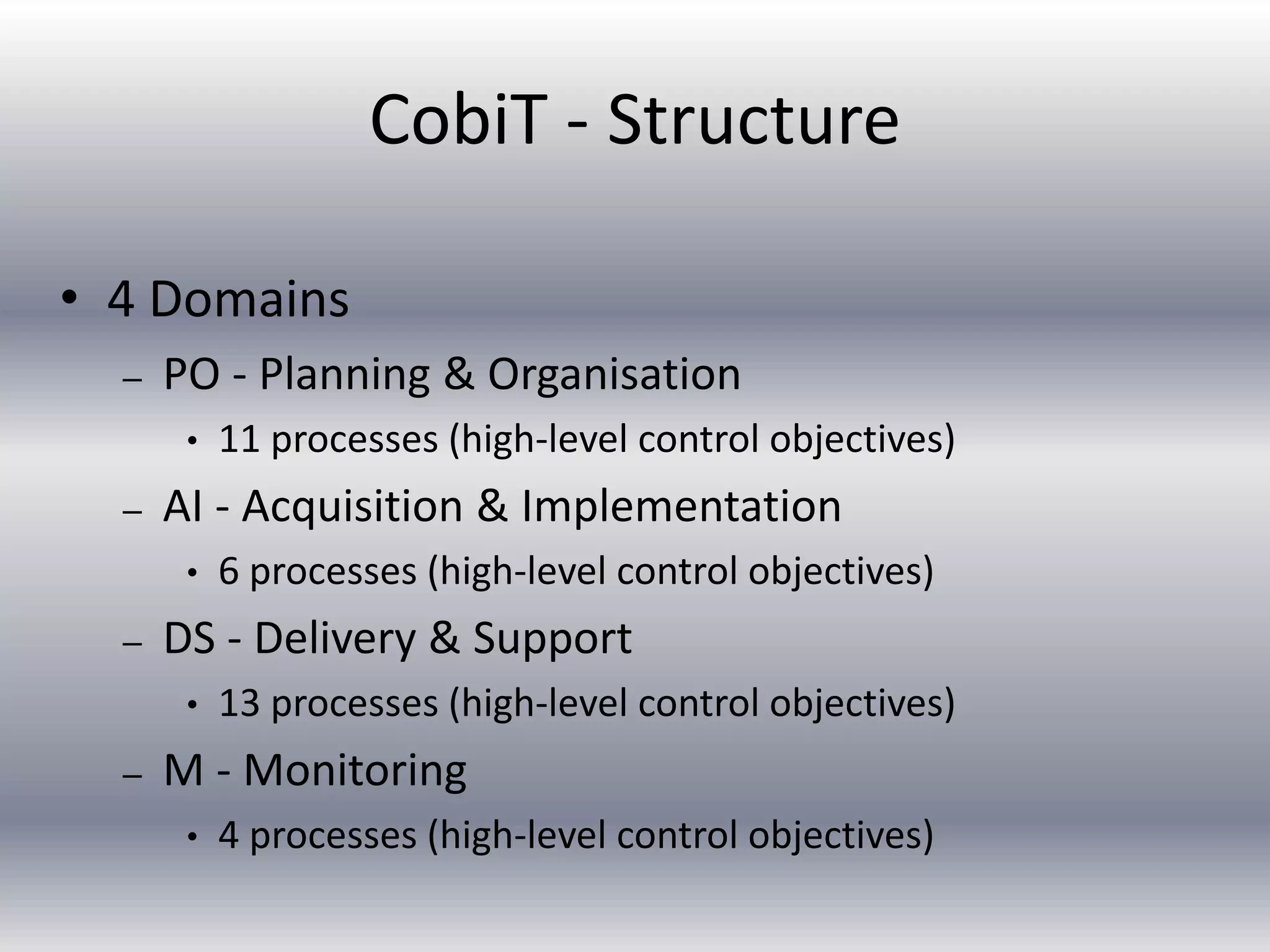
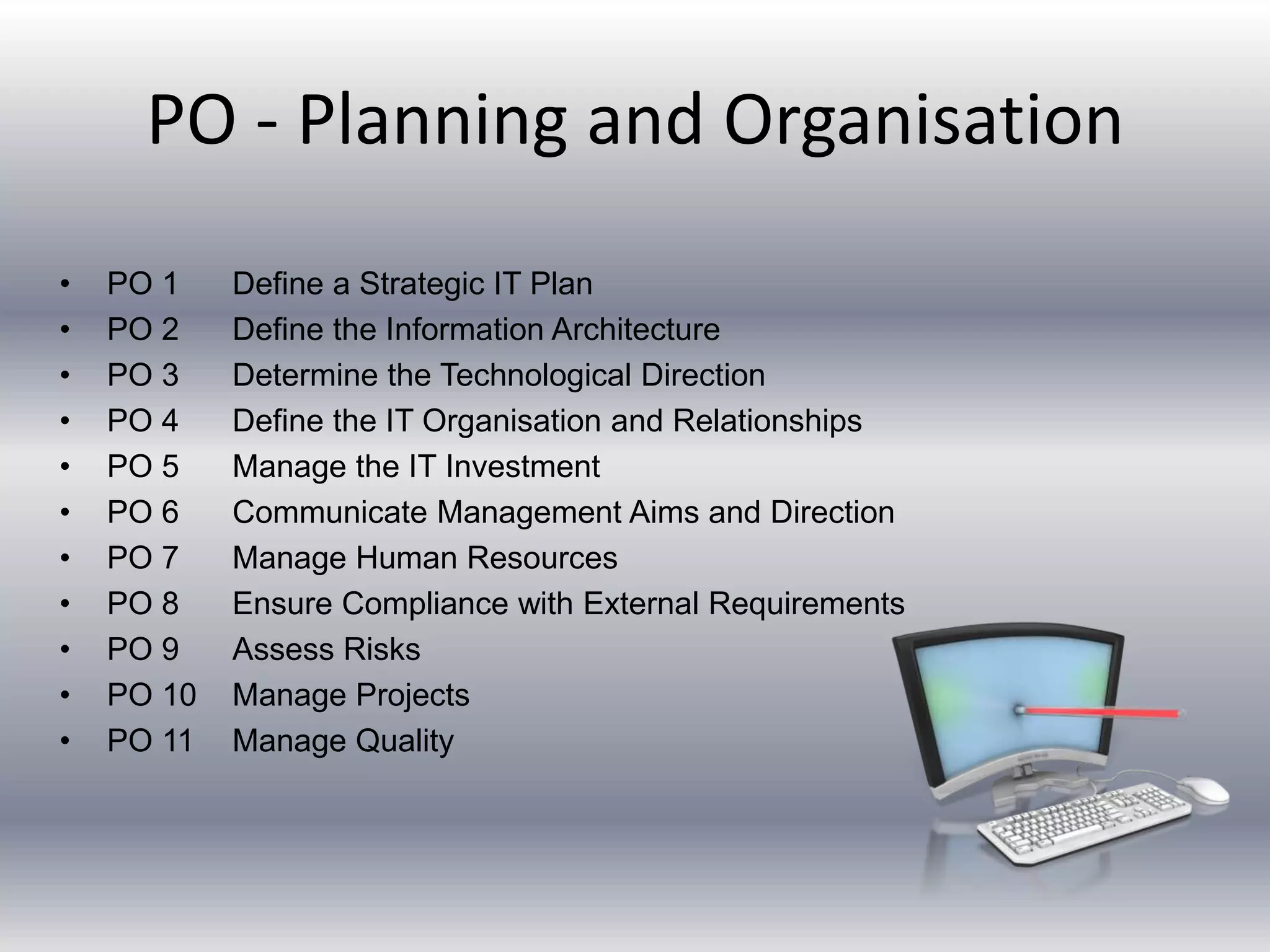
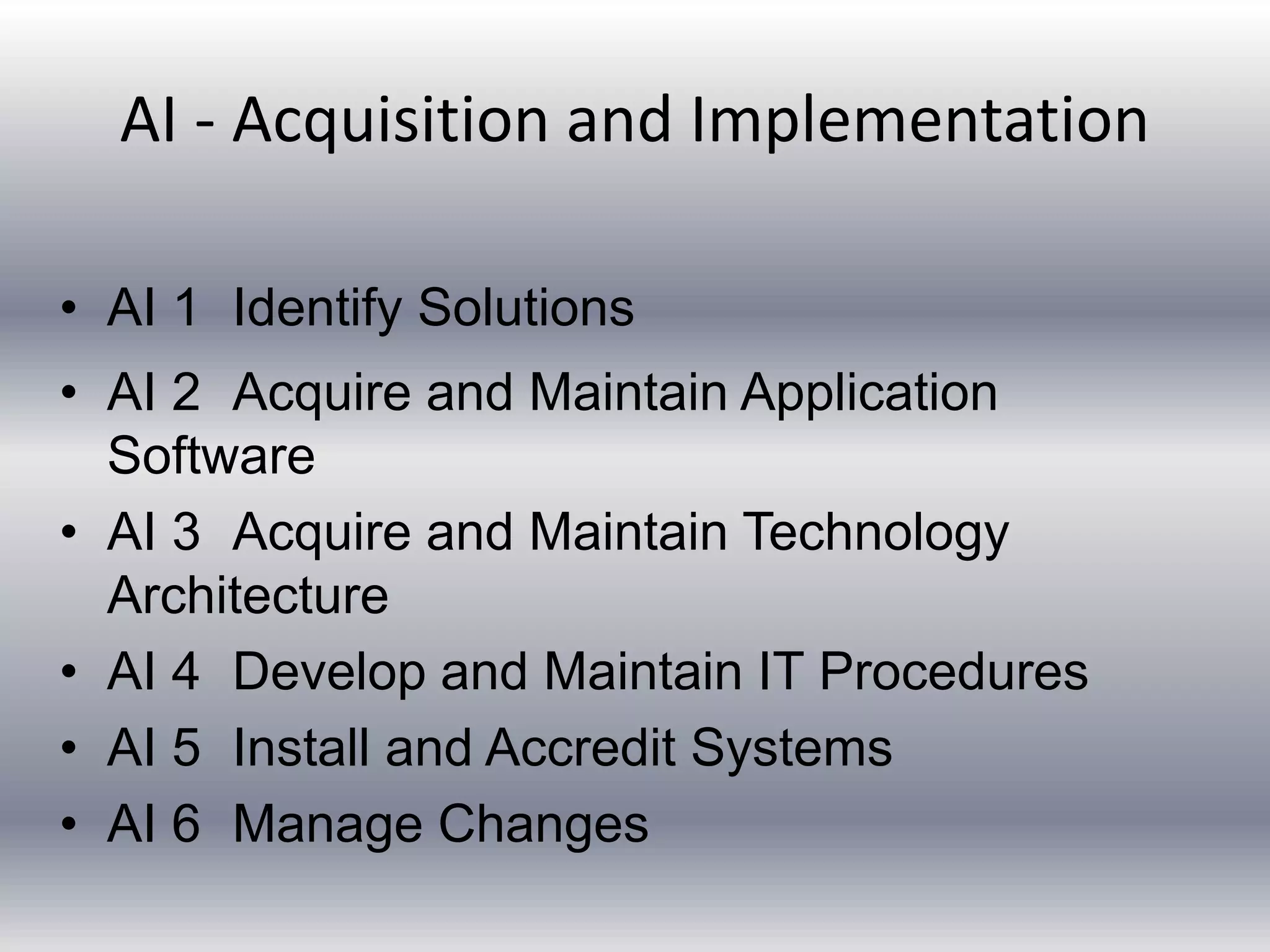
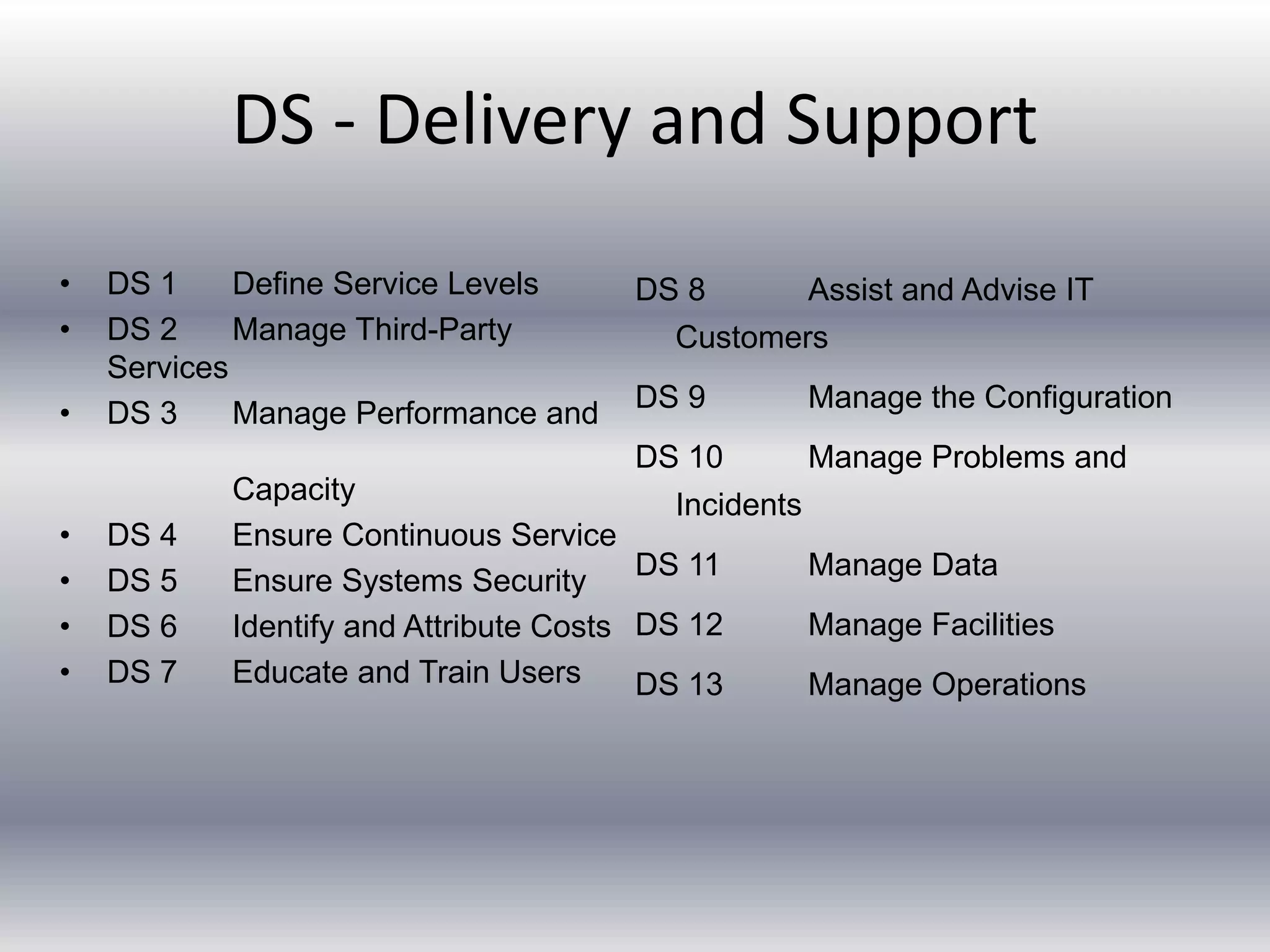
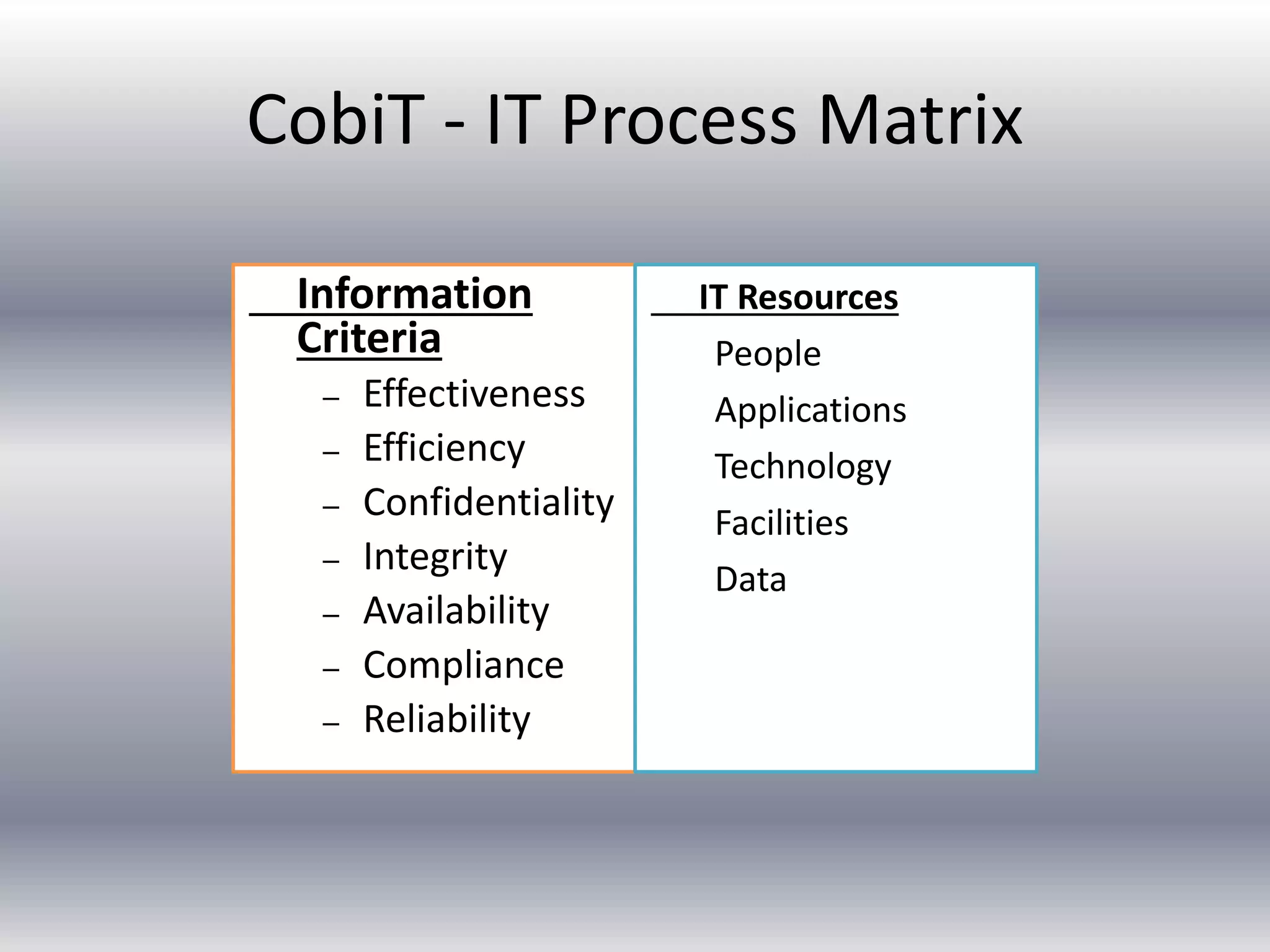
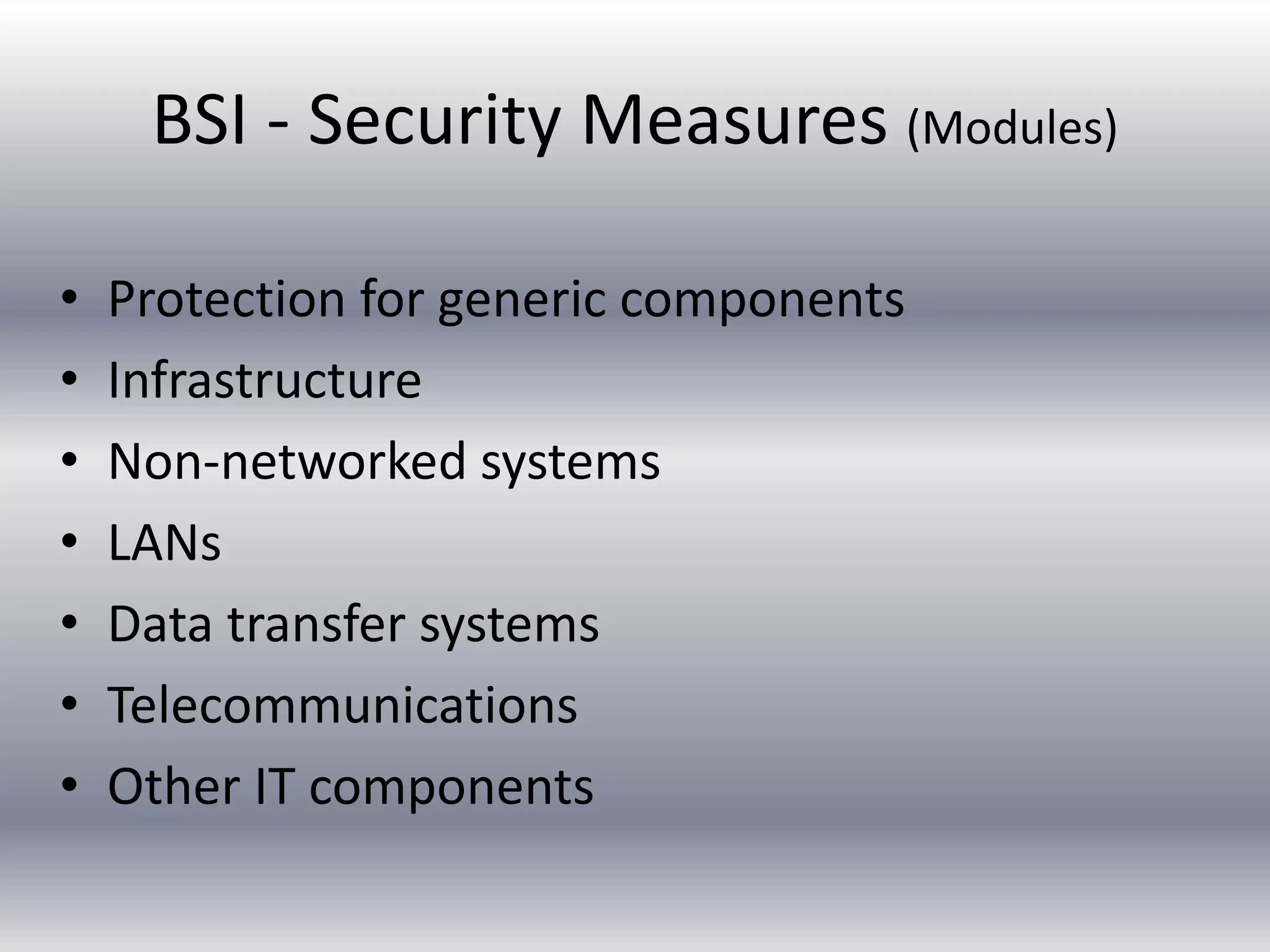
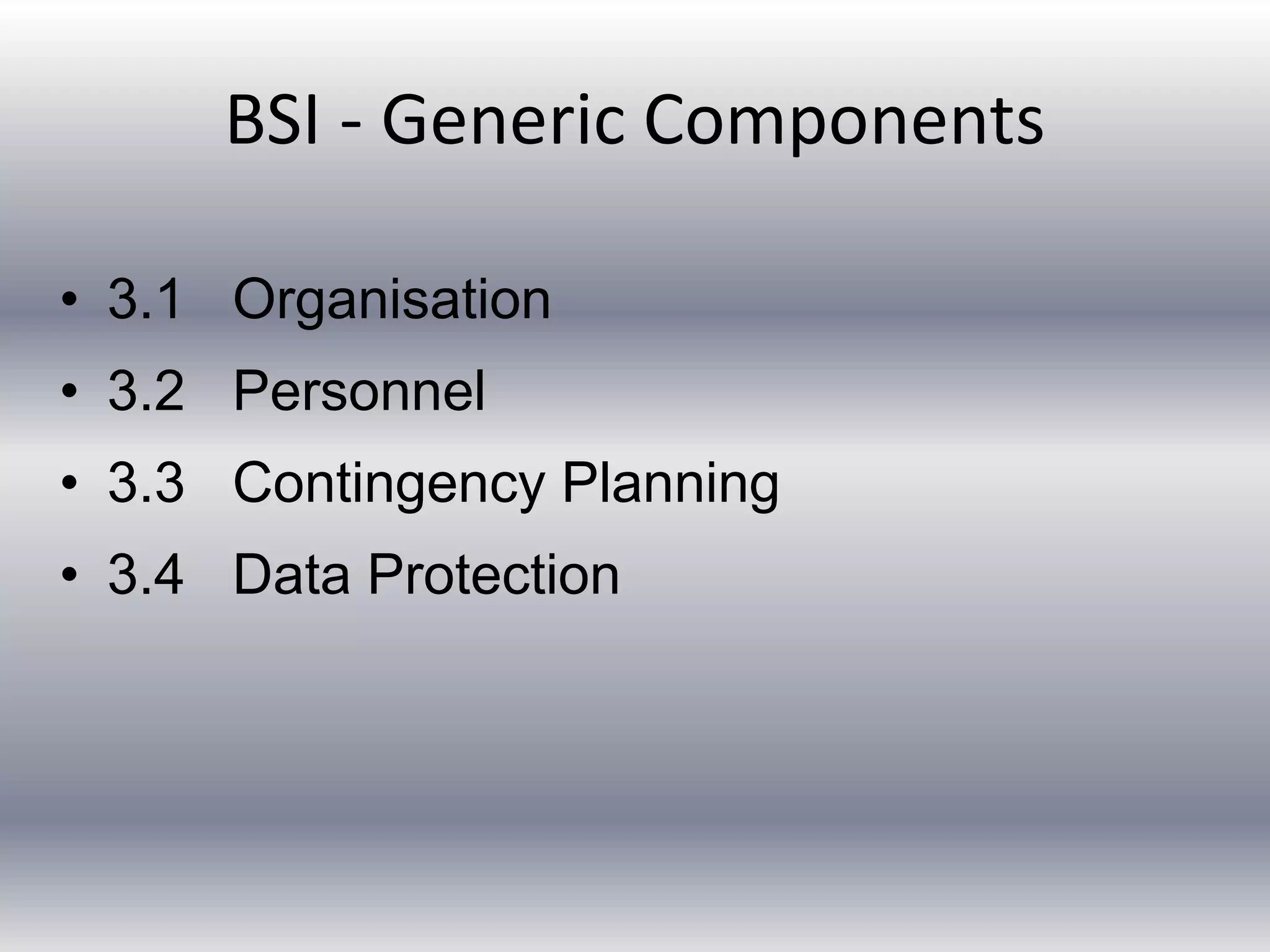
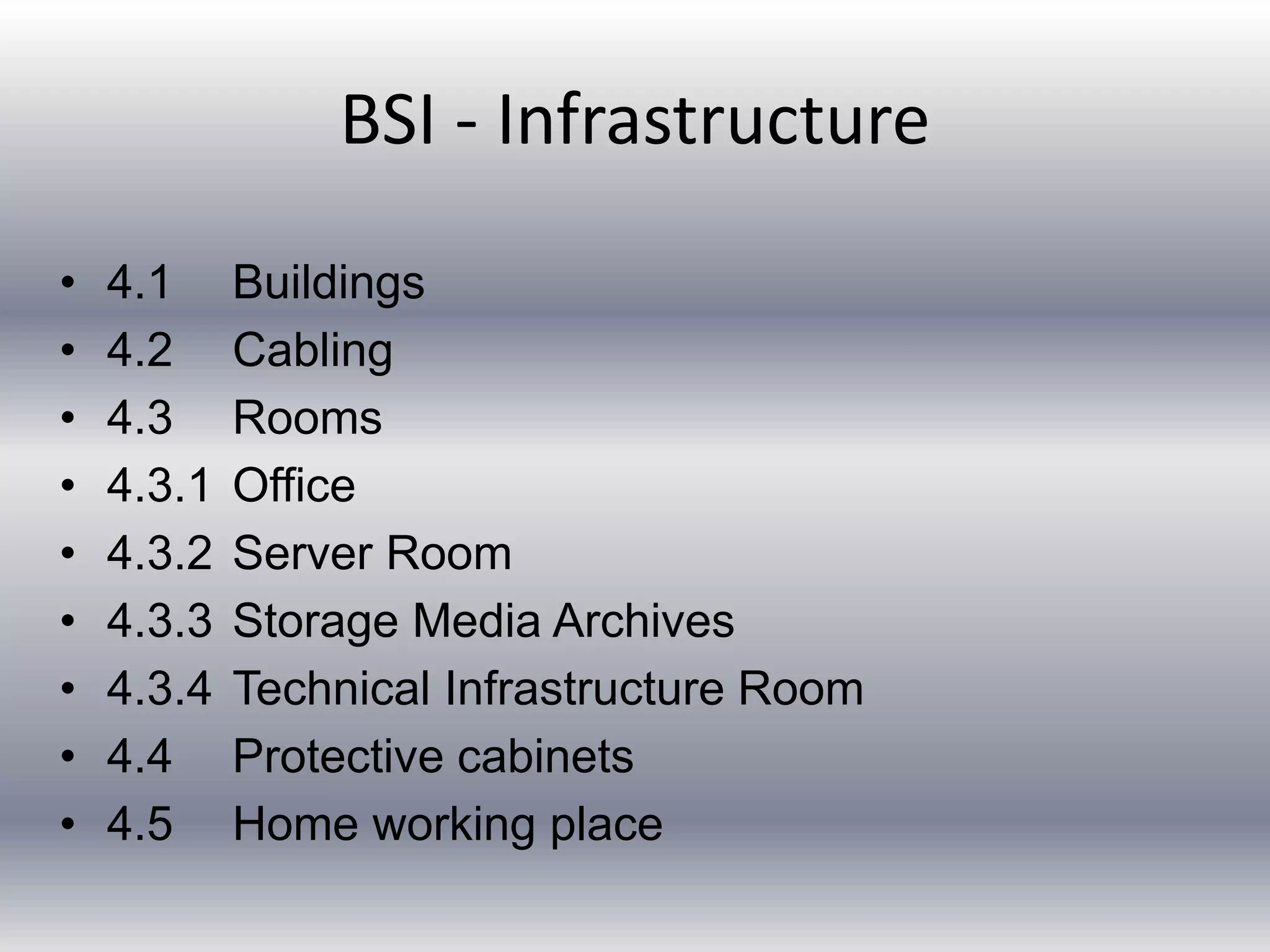
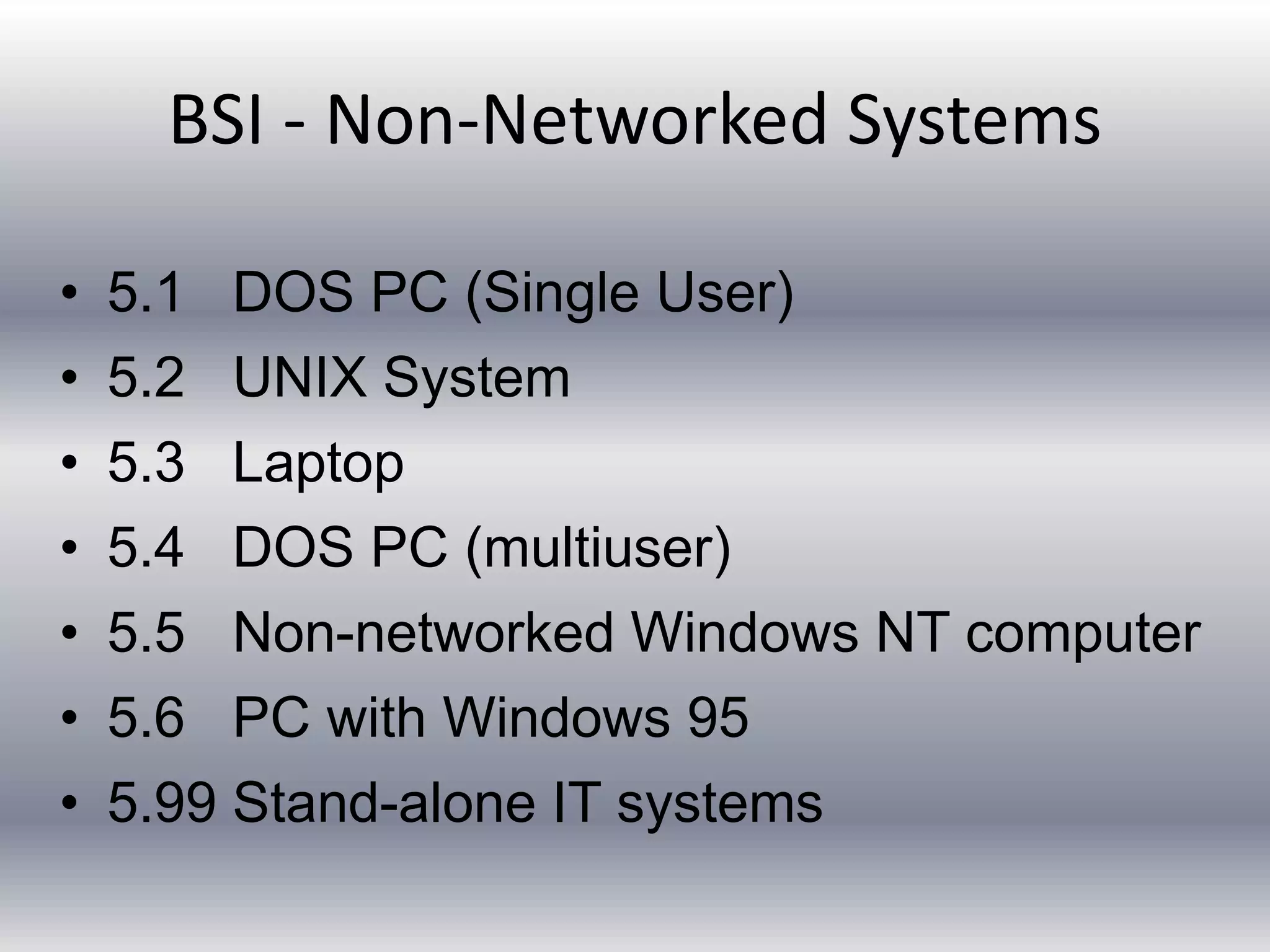
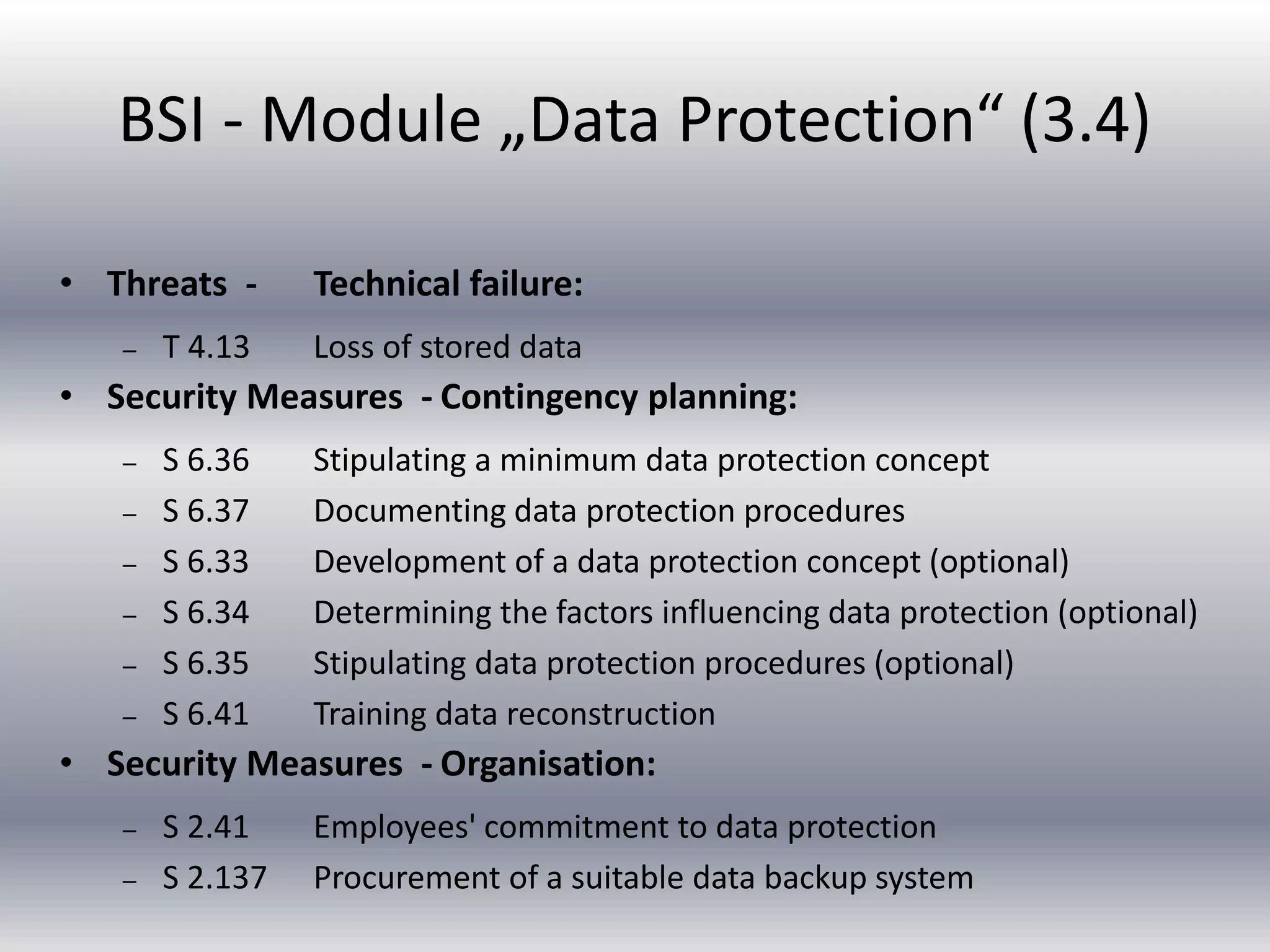
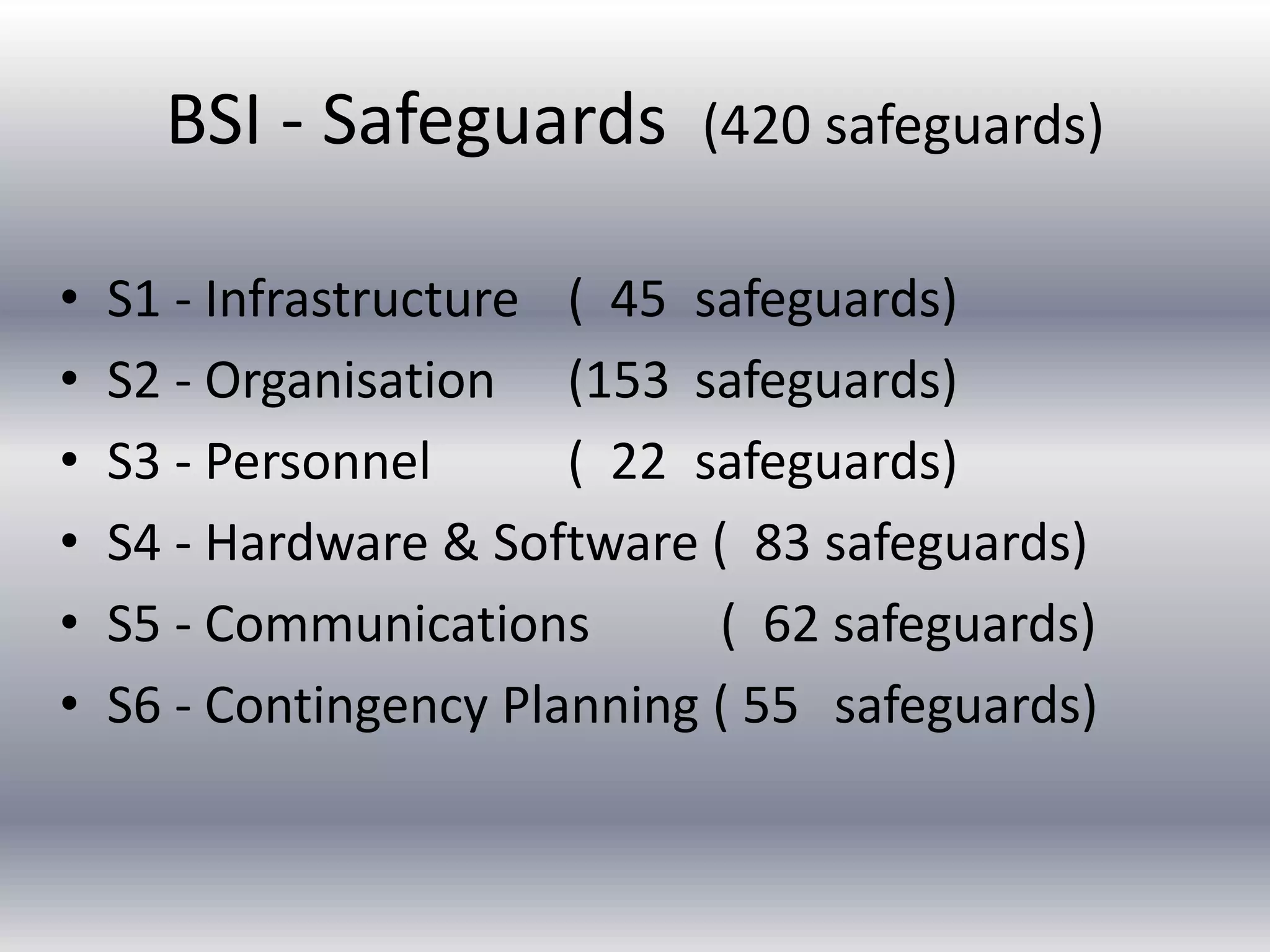
This document provides an overview of several IT audit methodologies: CobiT, BS 7799, BSI, ITSEC, and Common Criteria. CobiT is a framework for IT governance and control developed by ISACA that defines 34 processes across 4 domains (planning, acquisition, delivery, and monitoring). BS 7799 is a British standard focused on IT security baseline controls across 10 categories. BSI is a German manual that describes 34 security modules, 420 security measures, and 209 threats. ITSEC and Common Criteria are methodologies for evaluating the security of IT systems and products at defined assurance levels. Each methodology has different strengths in areas like scope, structure, user-friendliness, and frequency of updates


![BSI - S1-Infrastructure (45 safeguards)
• S 1.7 Hand-held fire extinguishers
• S 1.10 Use of safety doors
• S 1.17 Entrance control service
• S 1.18 Intruder and fire detection devices
• S 1.27 Air conditioning
• S 1.28 Local uninterruptible power supply [UPS]
• S 1.36 Safekeeping of data carriers before and
after dispatch](https://image.slidesharecdn.com/itauditmethodologies-141012234458-conversion-gate01/75/It-audit-methodologies-33-2048.jpg)