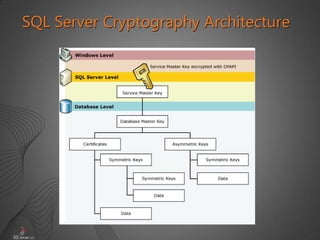
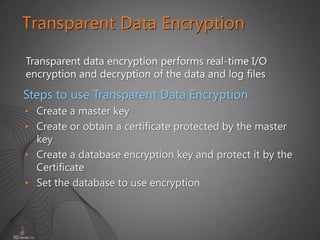
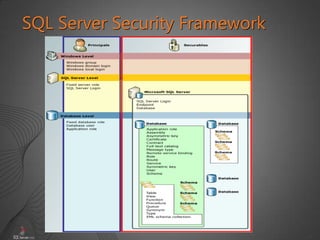
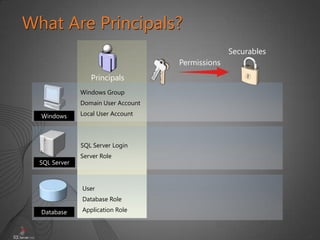
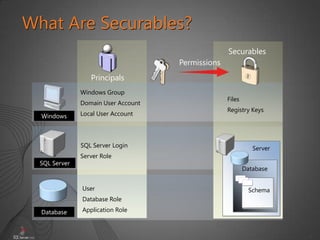
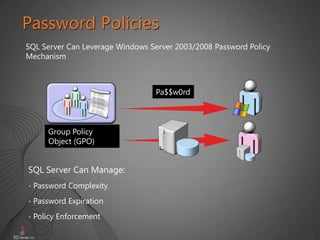
This document provides an overview of security and auditing in SQL Server 2008 R2. It discusses SQL Server security concepts like principals, securables and permissions. It also covers protecting the server and database scope through authentication methods, roles, logins and permissions. The document reviews keys, certificates and transparent data encryption. It concludes with an introduction to auditing security in SQL Server through tools like SQL Server Profiler, DDL triggers and the SQL Server Audit feature.







![16
Managing SQL Server Logins
CREATE LOGIN [SERVERXSalesDBUsers]
FROM WINDOWS
WITH DEFAULT_DATABASE = AdventureWorks2008
CREATE LOGIN Alice
WITH Password = 'Pa$$w0rd'
CREATE LOGIN login_name
{ WITH SQL_login_options
| FROM WINDOWS [ WITH
windows_login_options ] }](https://image.slidesharecdn.com/isaca-sqlserver2008r2securityauditing-130916161825-phpapp02/85/Isaca-sql-server-2008-r2-security-auditing-15-320.jpg)
![19
Server-Scope Permissions
Server permissions
Server-scope securable permissions
USE master
GRANT ALTER ANY DATABASE
TO [AdventureWorks2008Holly]
USE master
GRANT ALTER
ON LOGIN :: AWWebApp
TO [AdventureWorks2008Holly]](https://image.slidesharecdn.com/isaca-sqlserver2008r2securityauditing-130916161825-phpapp02/85/Isaca-sql-server-2008-r2-security-auditing-16-320.jpg)