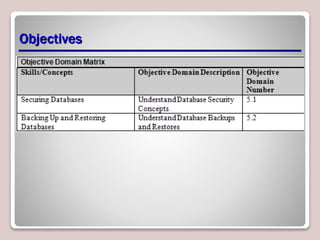
The document discusses database security and administration. It covers topics like database security concepts including permissions, logins, and accounts. It also discusses server-level security, database-level security, object permissions, and authentication. Additionally, it summarizes database server roles, backups, restores, and other administrative tasks.