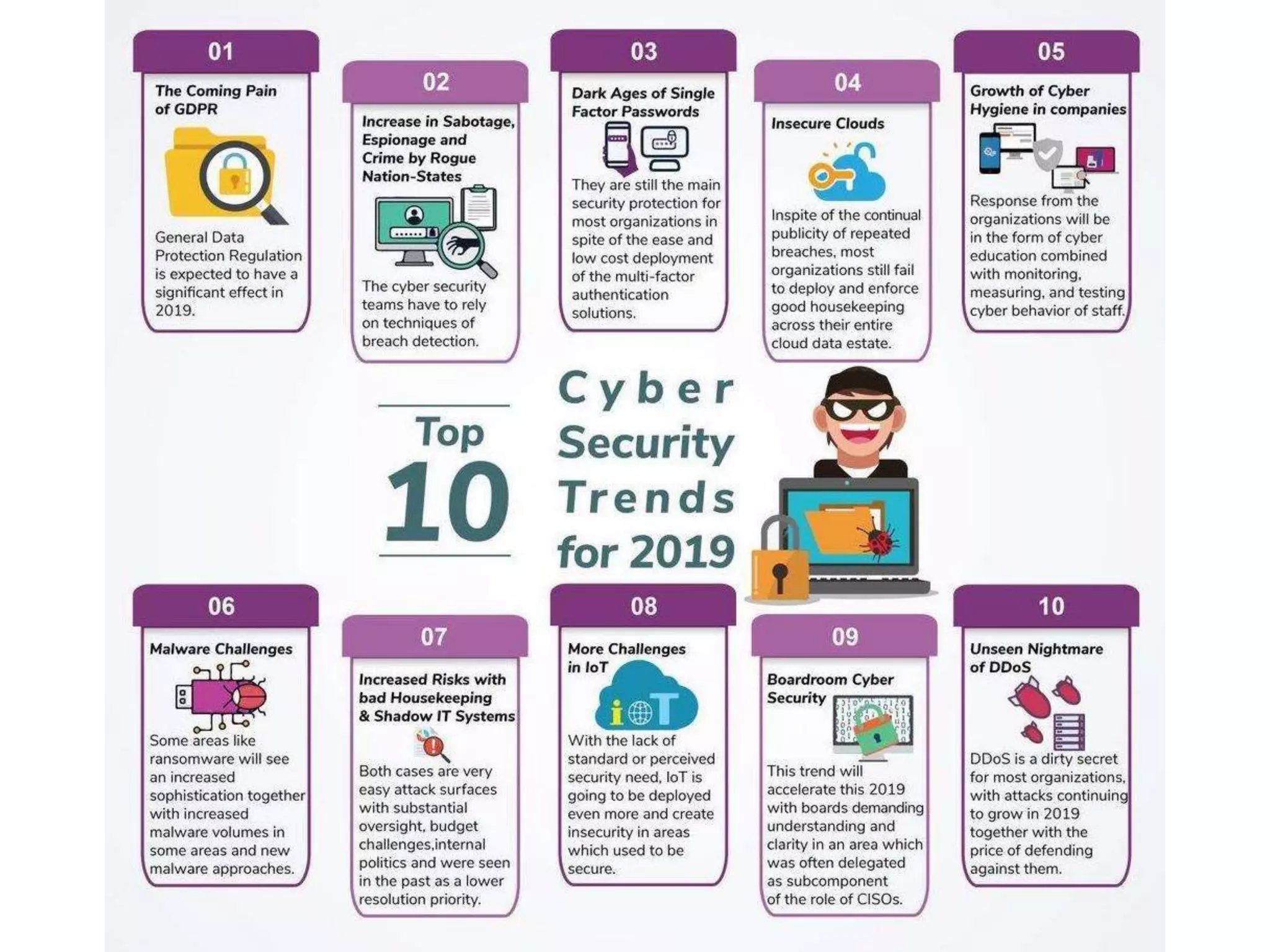
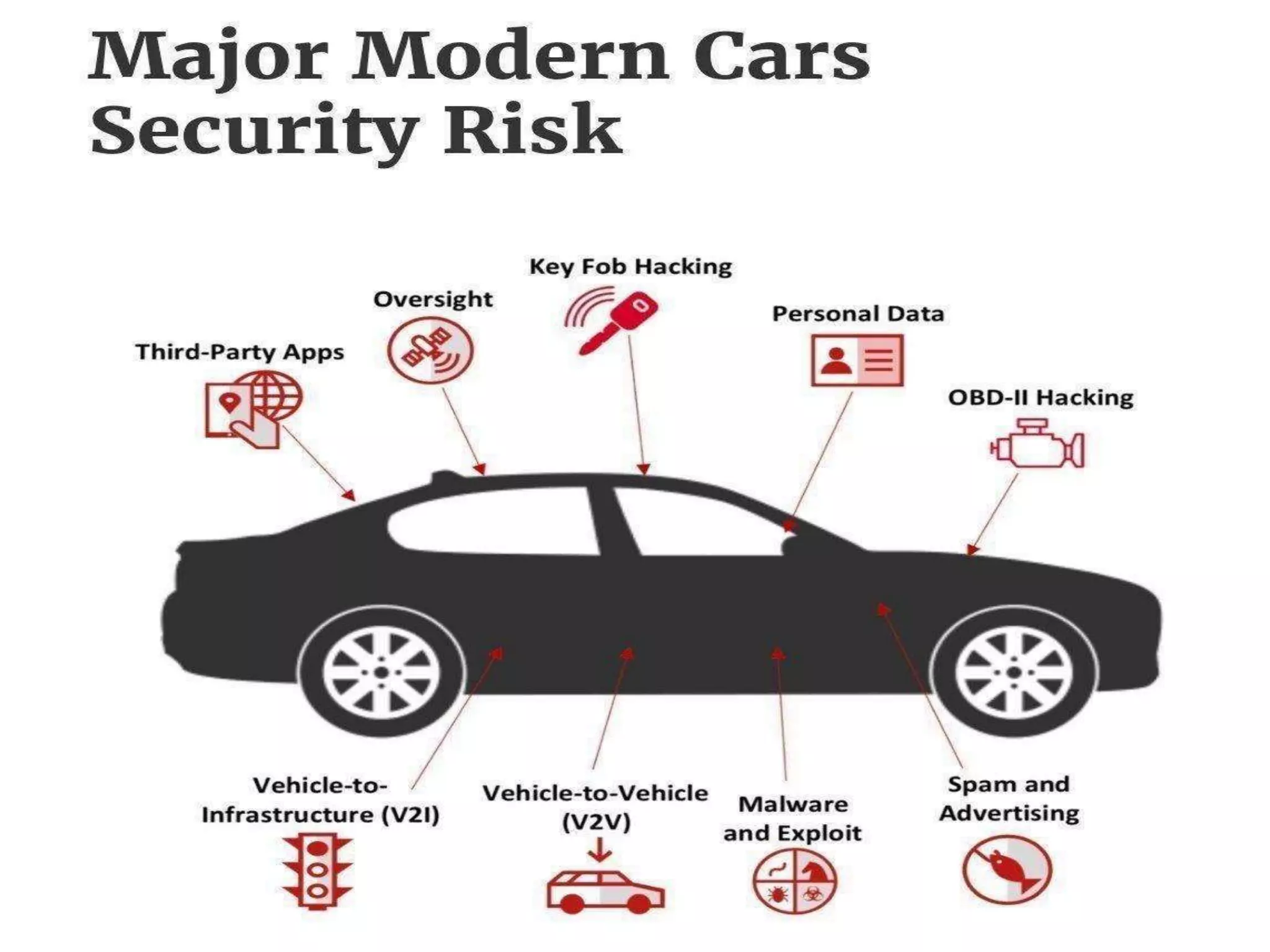
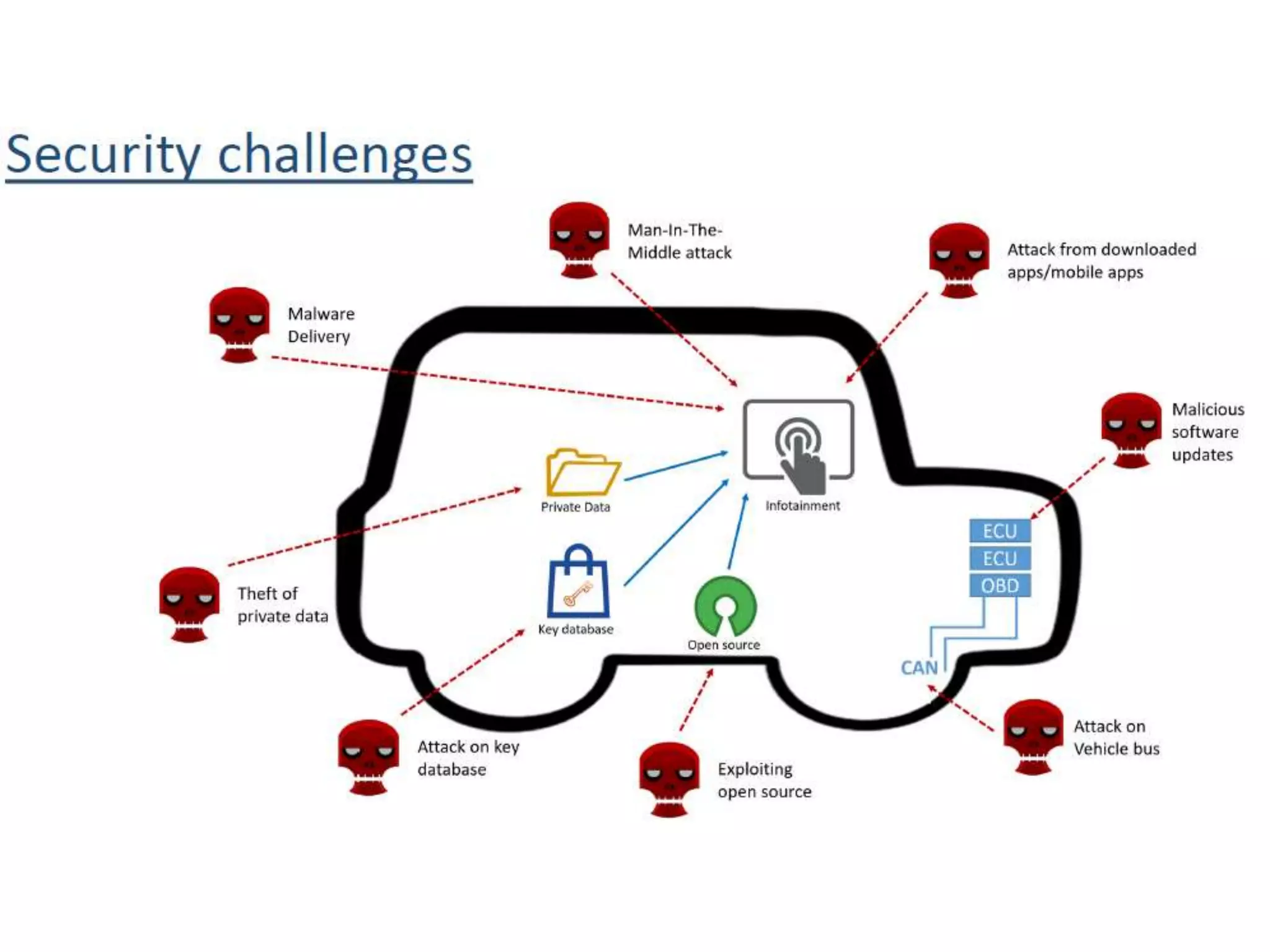
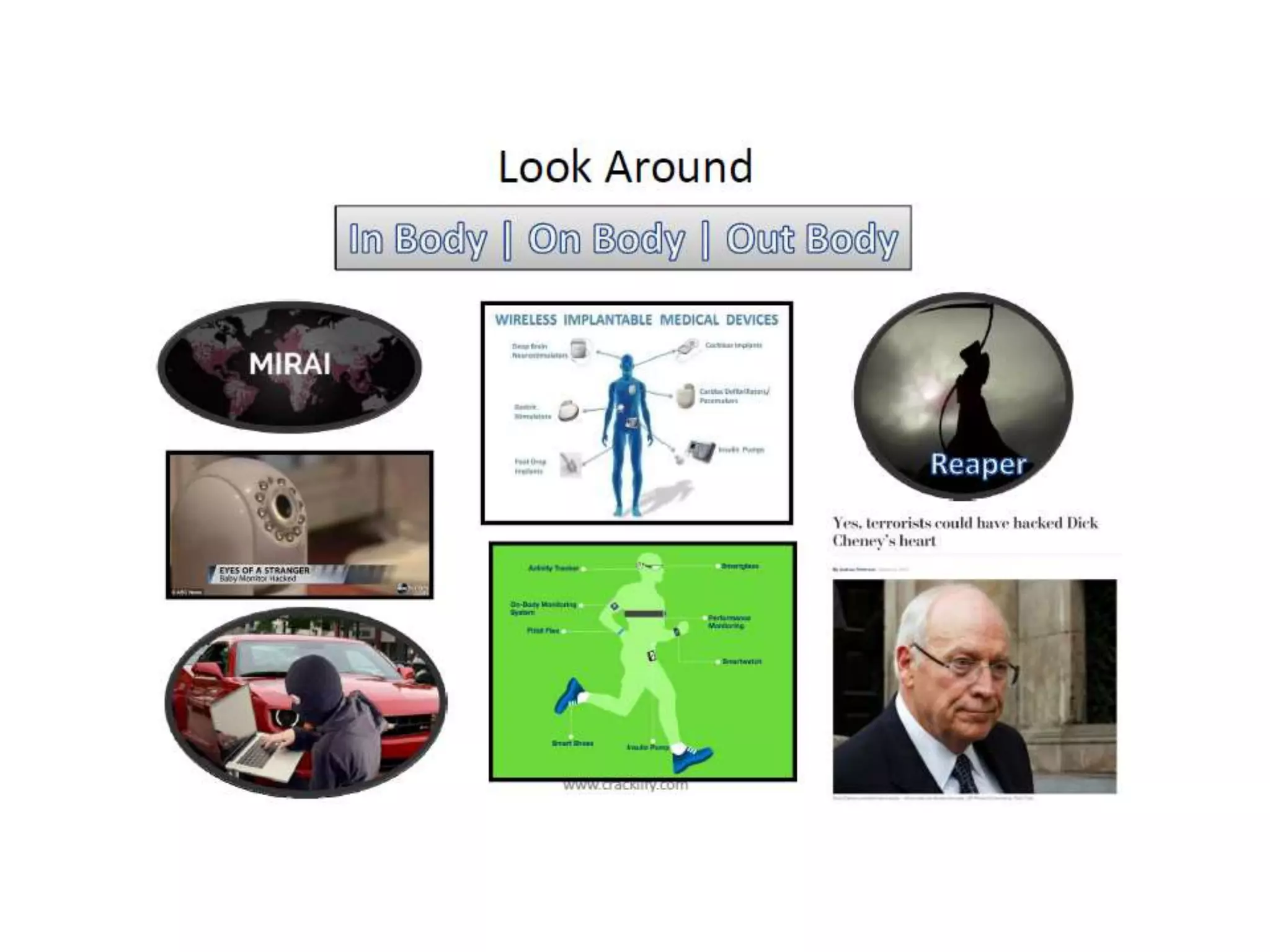
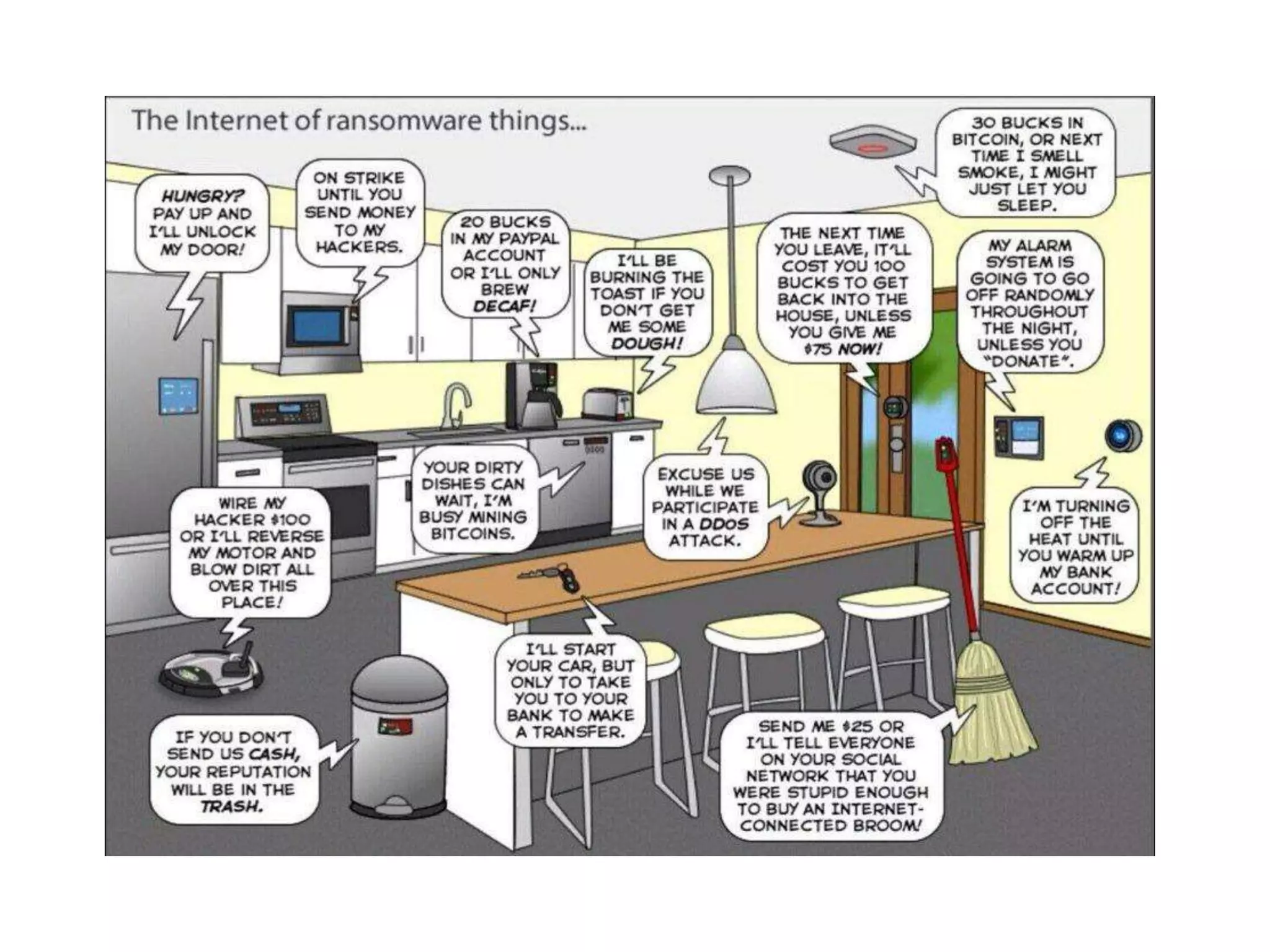
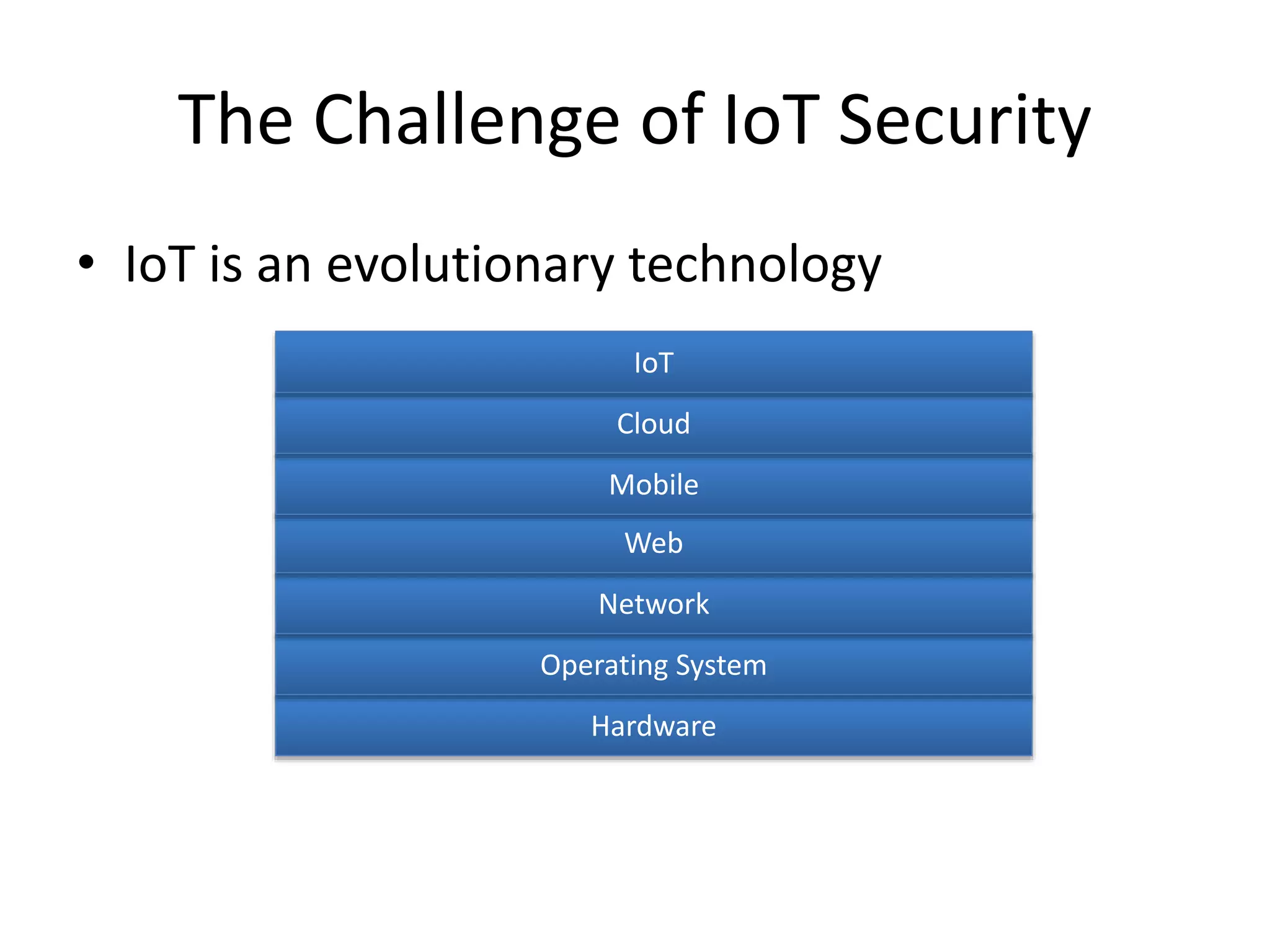
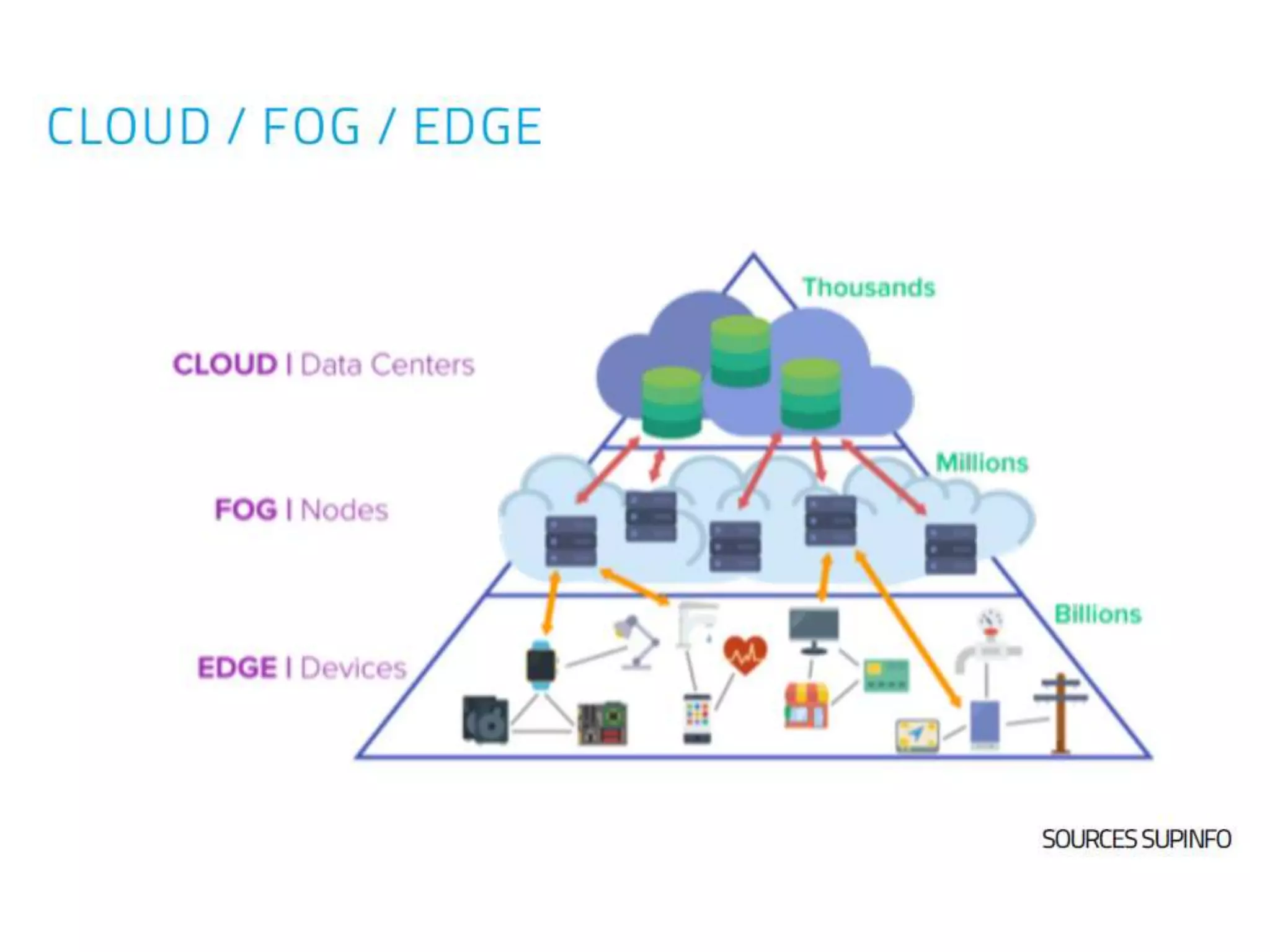
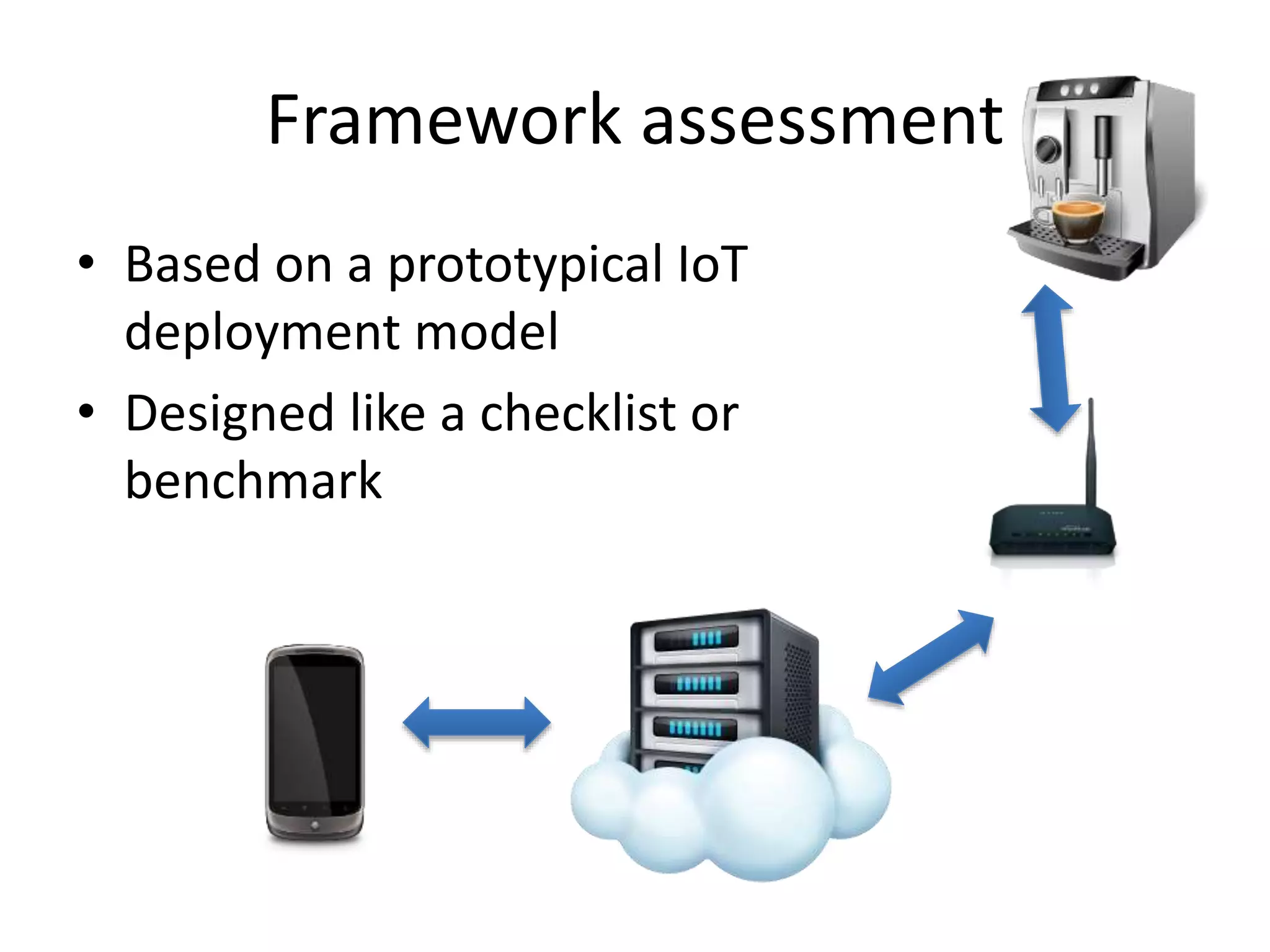
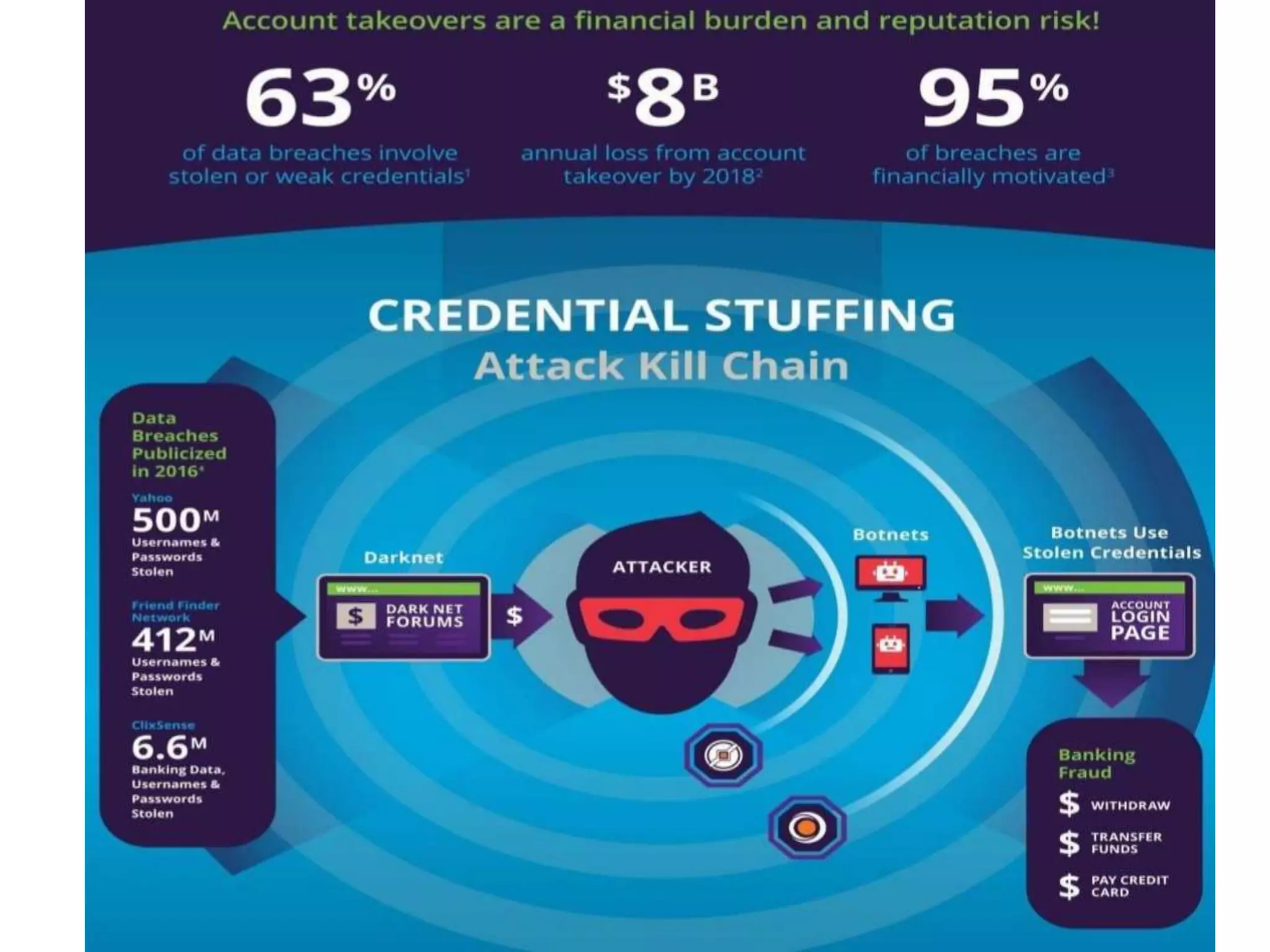
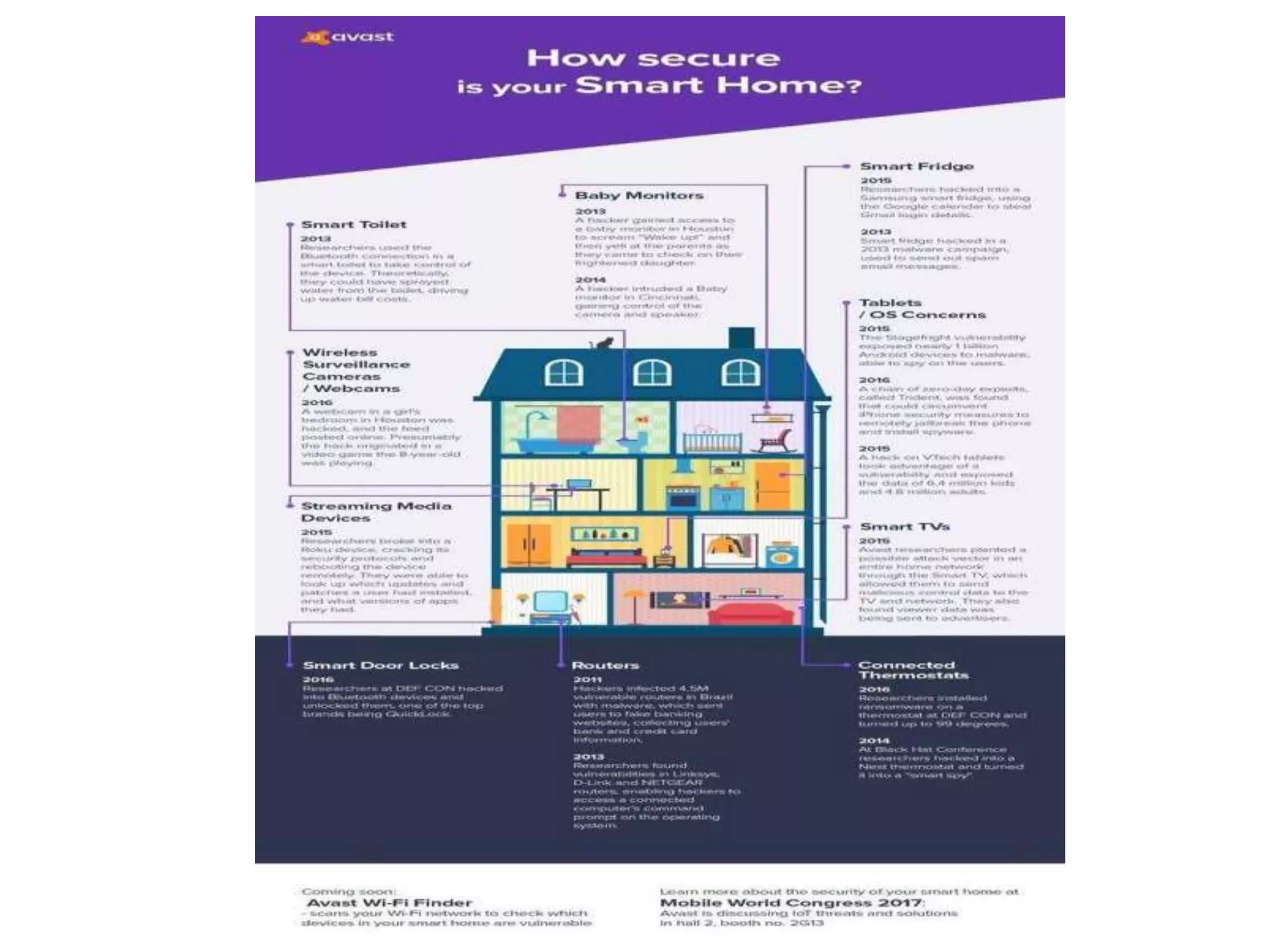
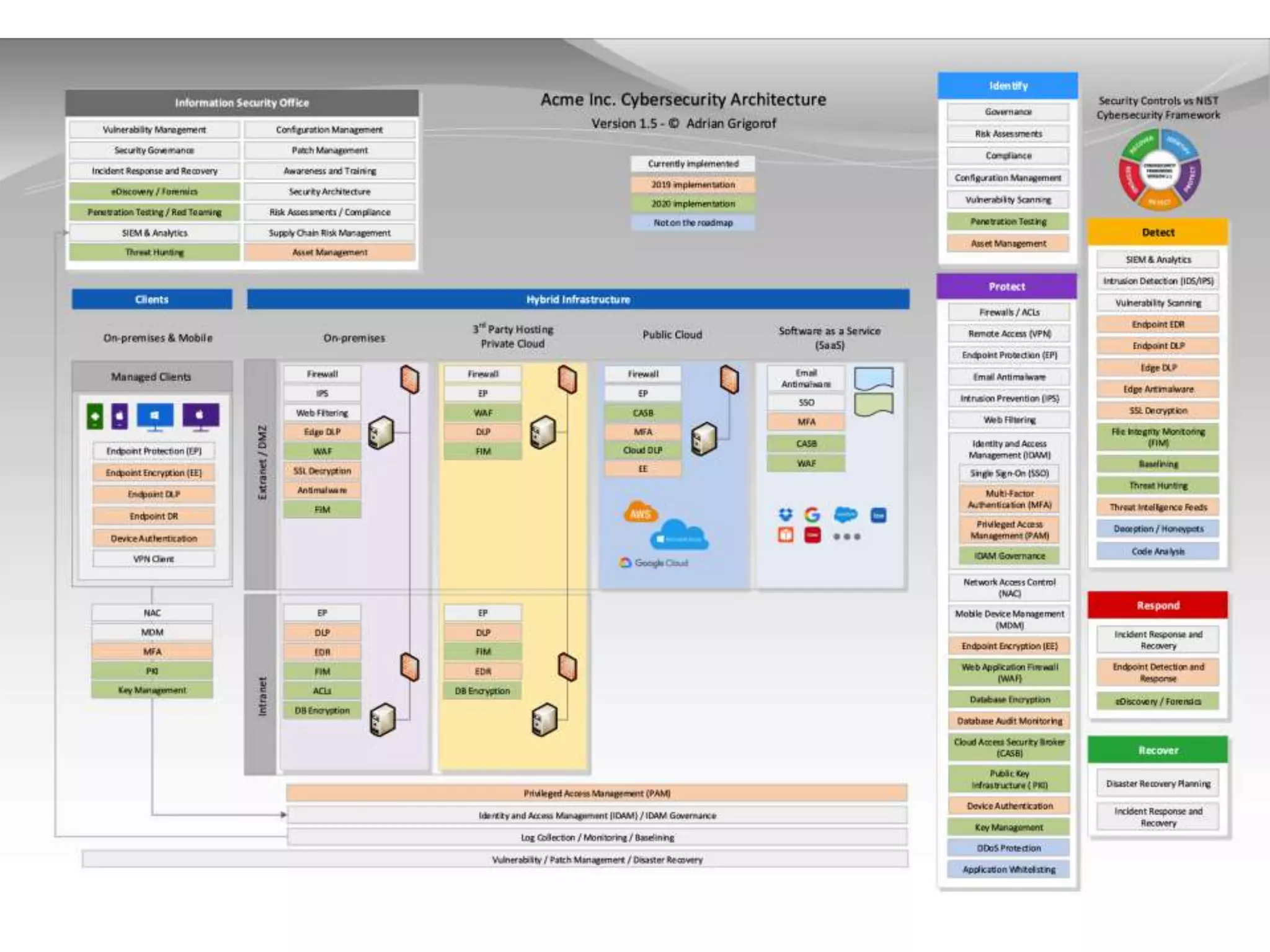
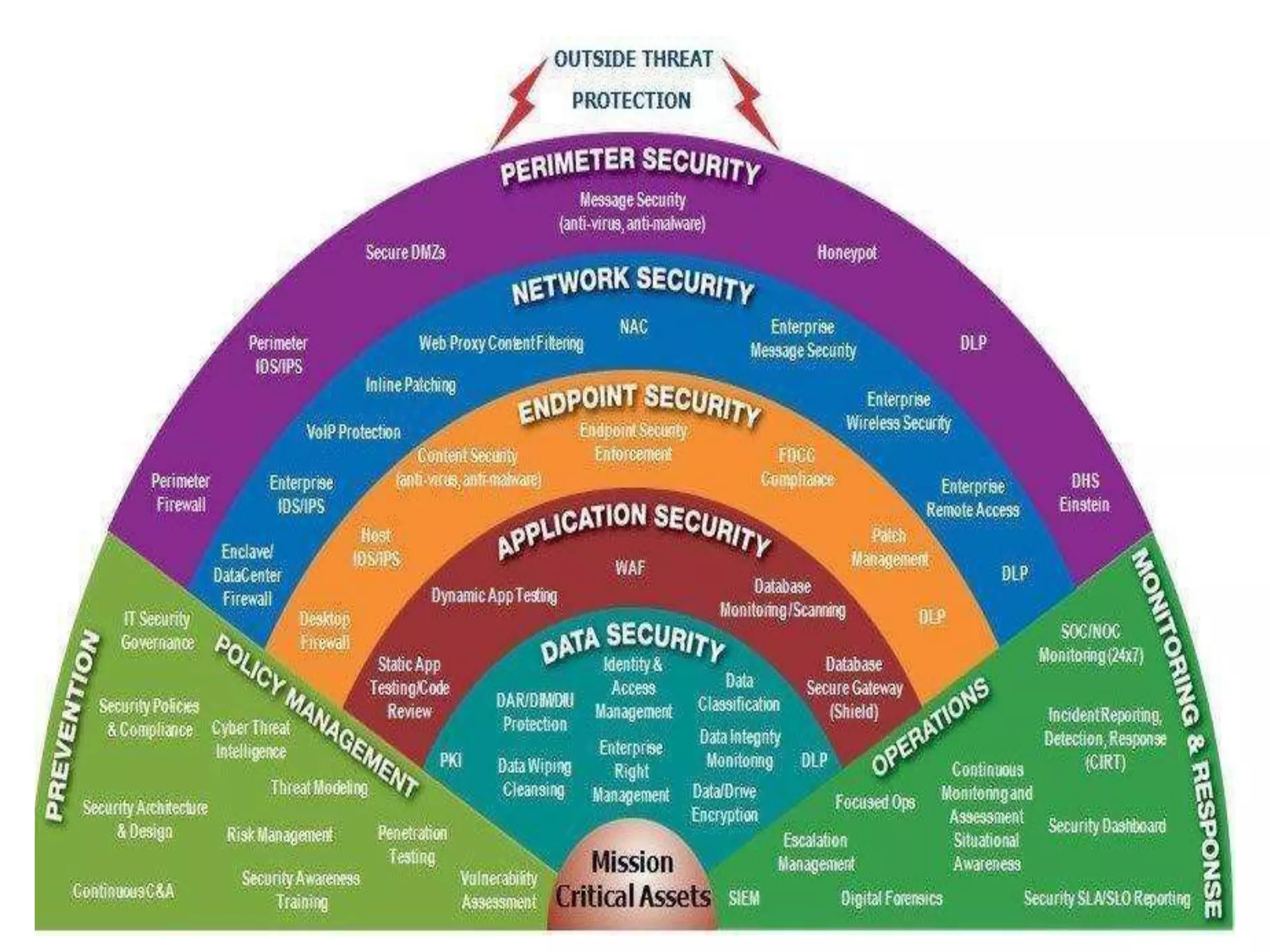
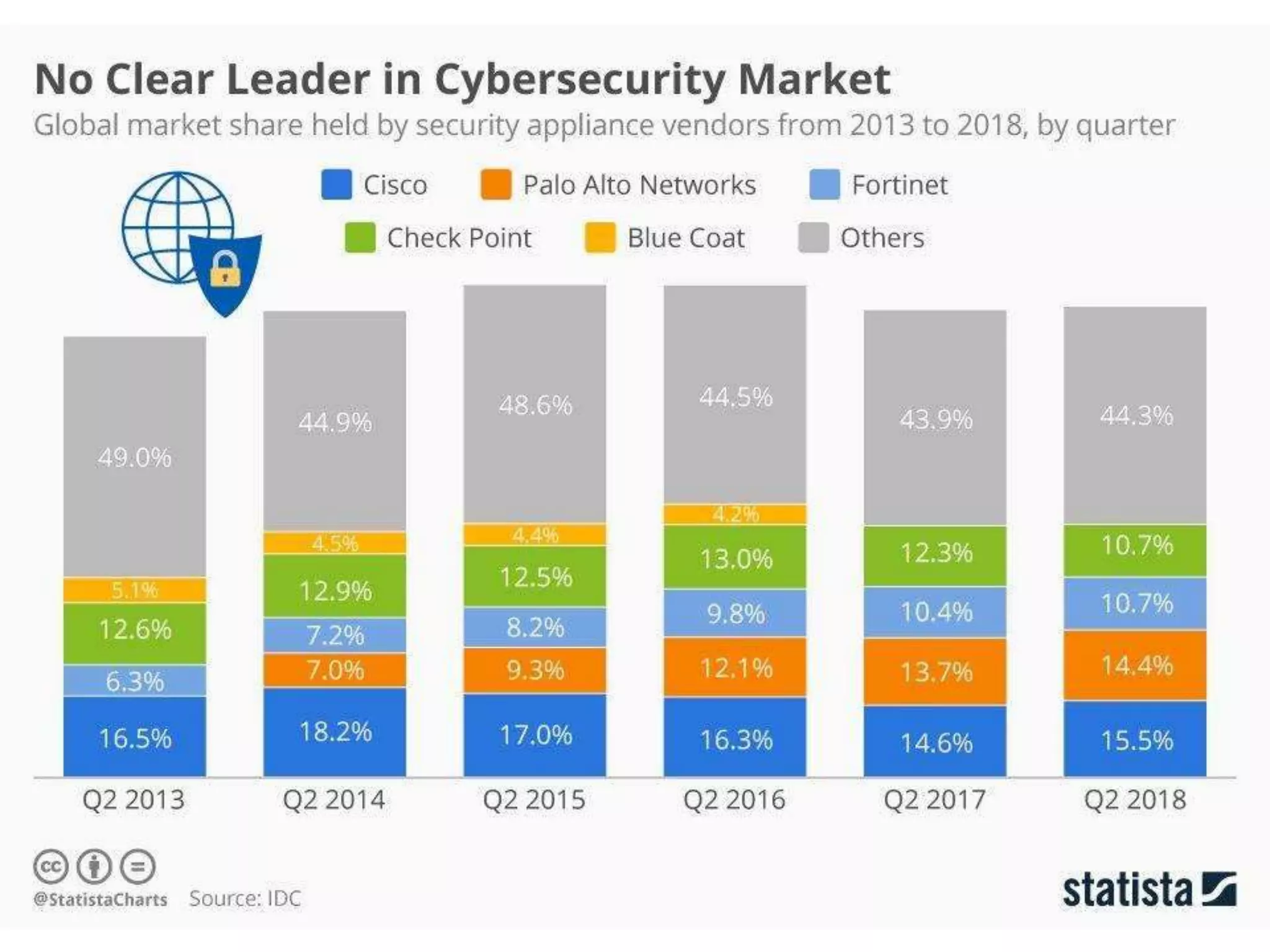
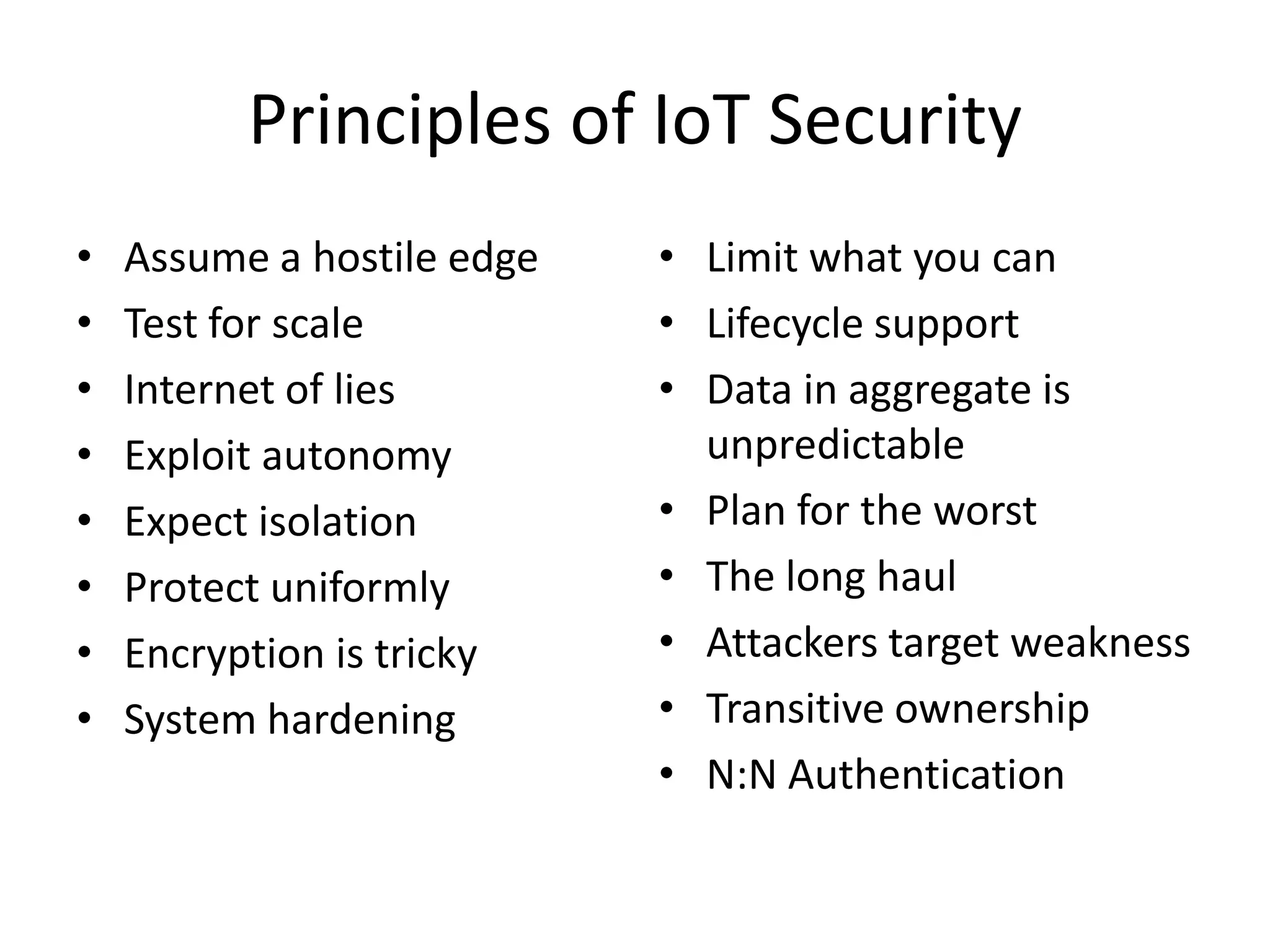
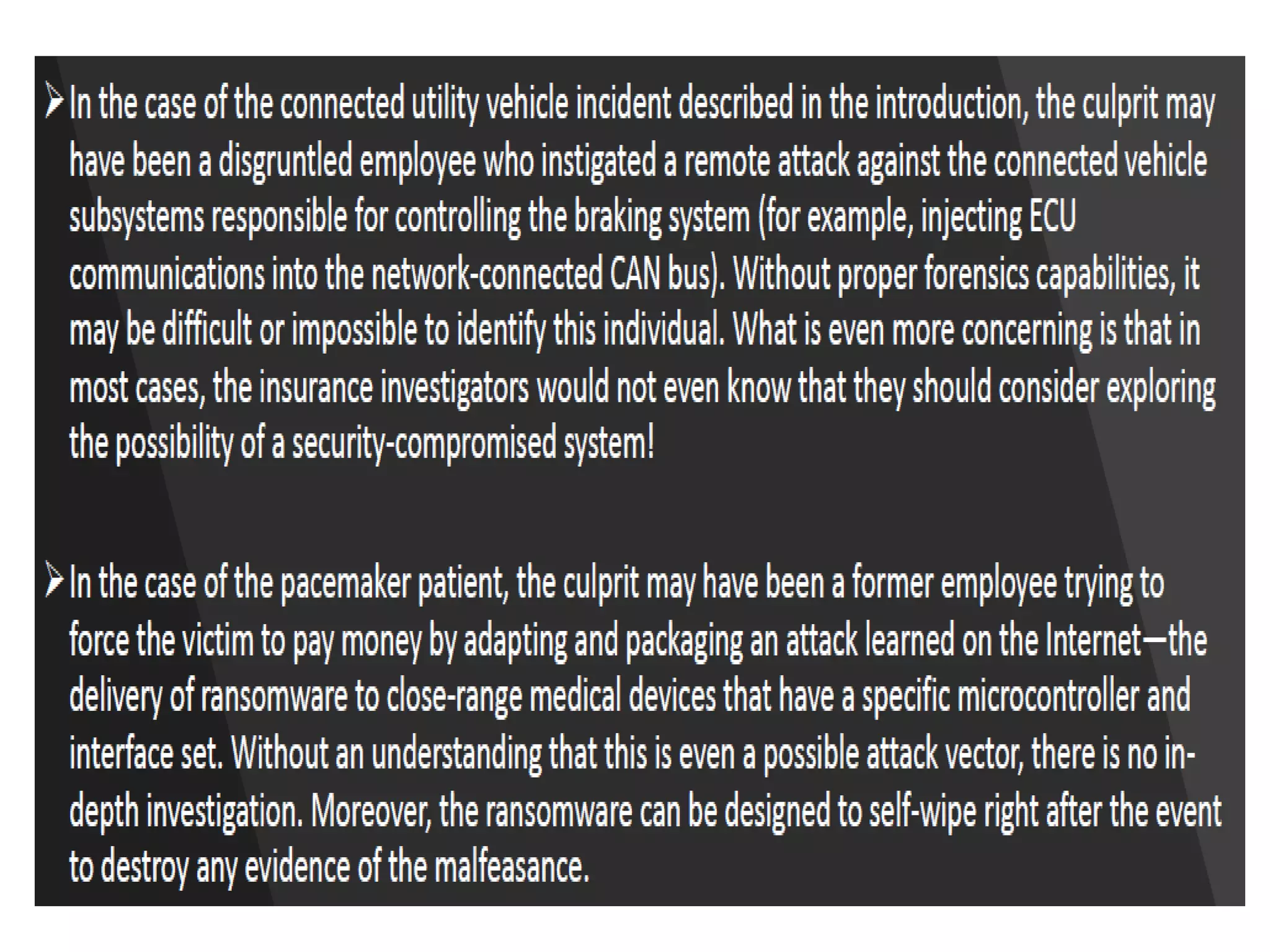
The document provides information from a presentation on IoT security given by Amar Prusty of DXC Technology. It begins with biographical information about the speaker and an overview of what IoT is. It then discusses some of the key security challenges with IoT, including that IoT devices often have weak default credentials, lack of ability to update firmware, and vulnerabilities in web interfaces. The document outlines potential attacks against different components of an IoT system like edge devices, gateways, cloud infrastructure and mobile devices. It proposes using the OWASP IoT security framework to help address vulnerabilities and concludes by discussing the challenges in securing IoT given the current state of tools and methodologies available to builders.