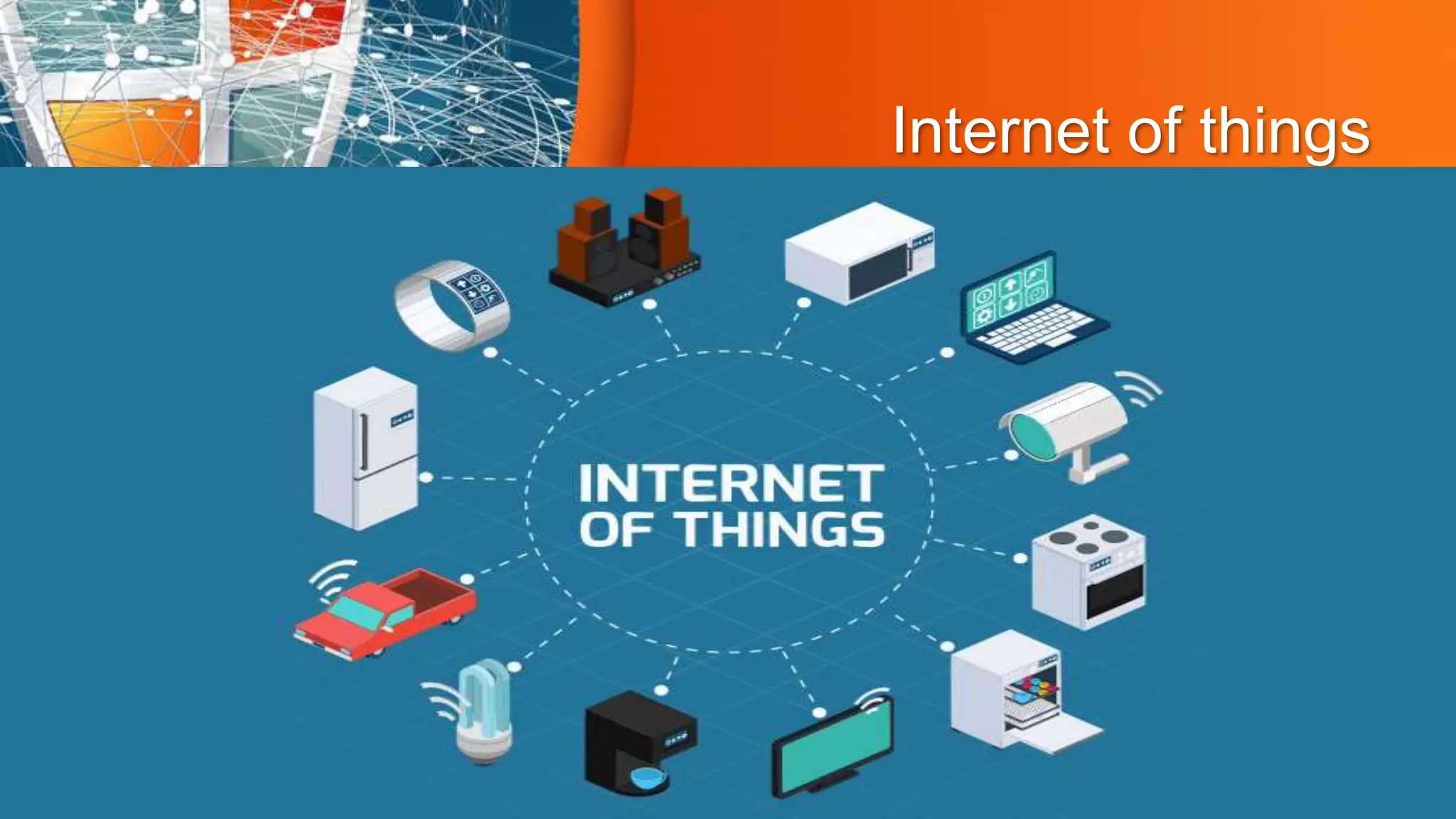
The document discusses Internet of Things (IoT) security. It begins with an introduction to IoT, defining it as physical objects embedded with sensors and software to connect and exchange data over the internet. It then defines IoT security as securing these connected devices and objects. The document outlines the importance of IoT security to protect hardware, software, connectivity and user data. It discusses key elements of IoT security like authentication, access control, data security, and availability. It also covers common problems in IoT security such as device hijacking, insufficient testing, botnet attacks, and a lack of user awareness. The document provides solutions to these problems and describes attacks like denial of service, man-in-the-middle,