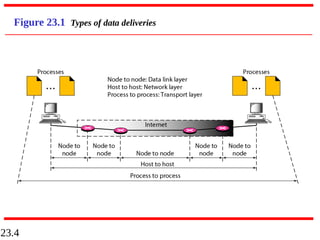
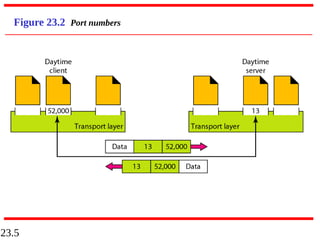
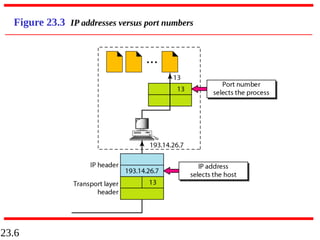
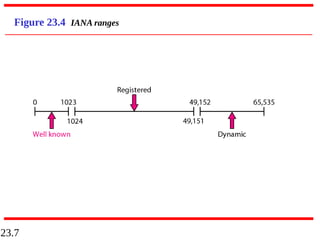
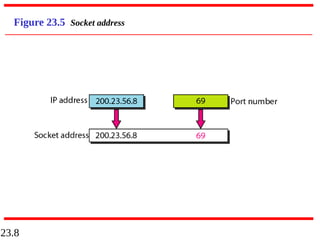
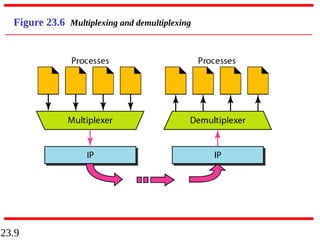
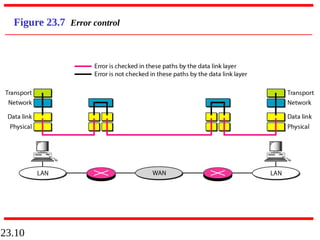
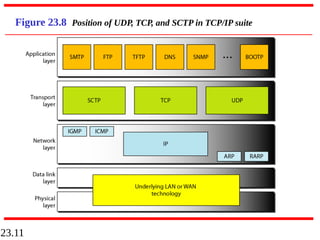
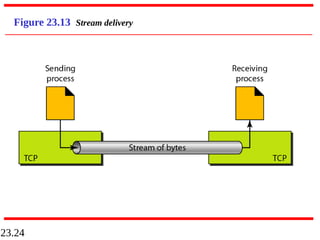
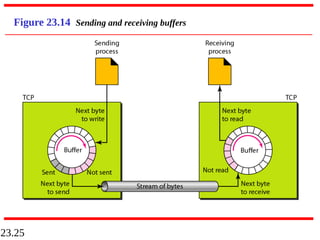
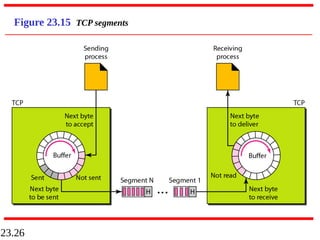
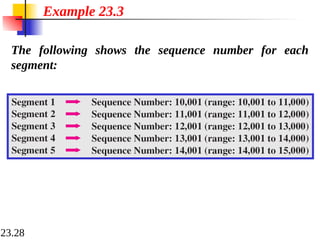
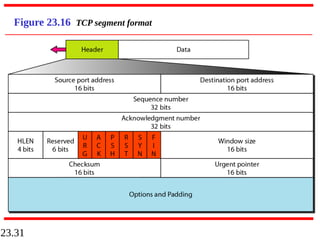
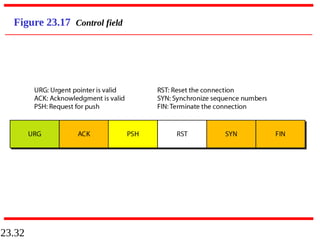
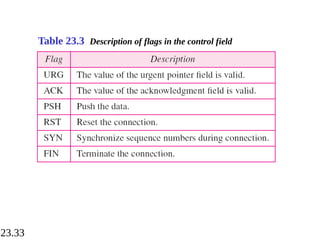
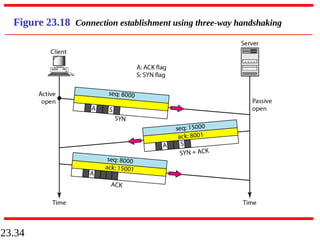
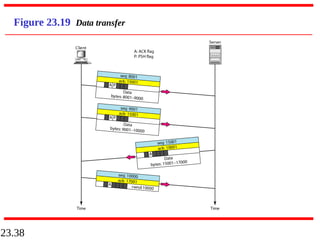
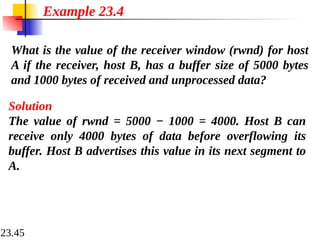
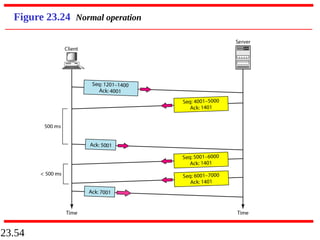
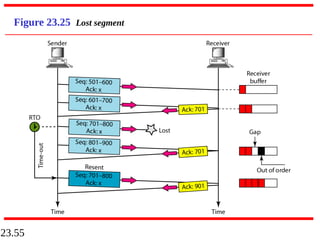
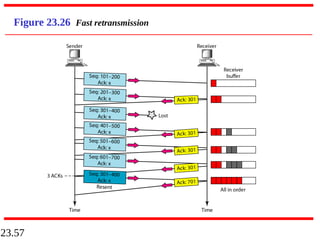
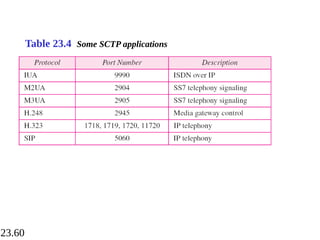
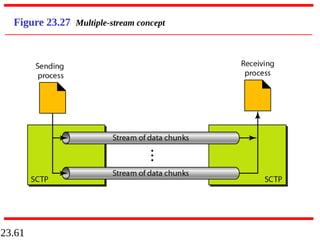
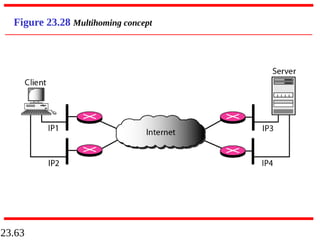
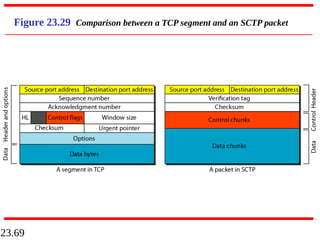
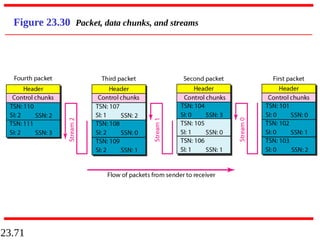
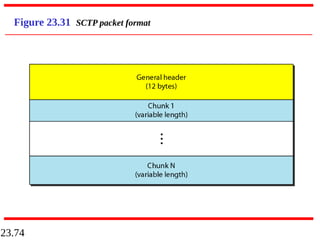
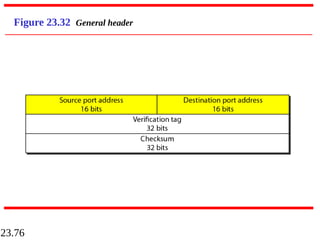
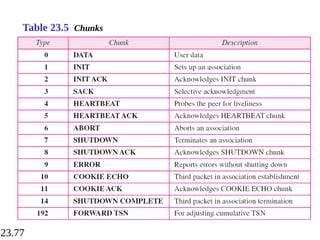
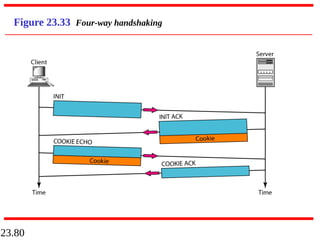
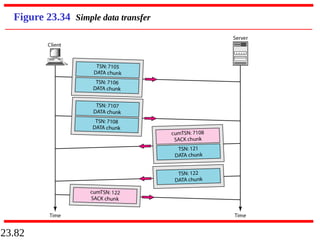
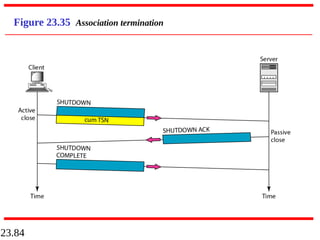
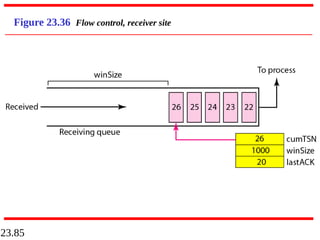
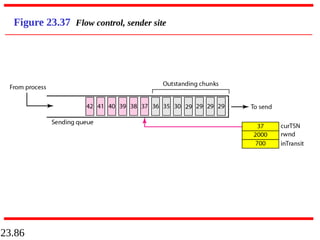
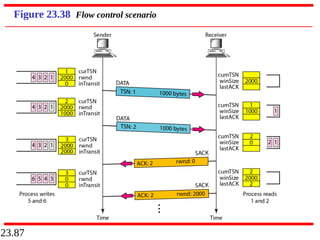
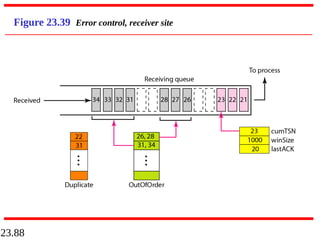
The document discusses process-to-process delivery at the transport layer and three protocols used: UDP, TCP, and SCTP. The transport layer is responsible for delivering packets from one process to another in a client/server relationship. UDP provides basic connectionless and unreliable delivery, while TCP provides reliable connection-oriented delivery using mechanisms like flow control, error control, and sliding windows. SCTP is a newer protocol that combines features of UDP and TCP, and provides reliability with multiple streams and multihoming capabilities.