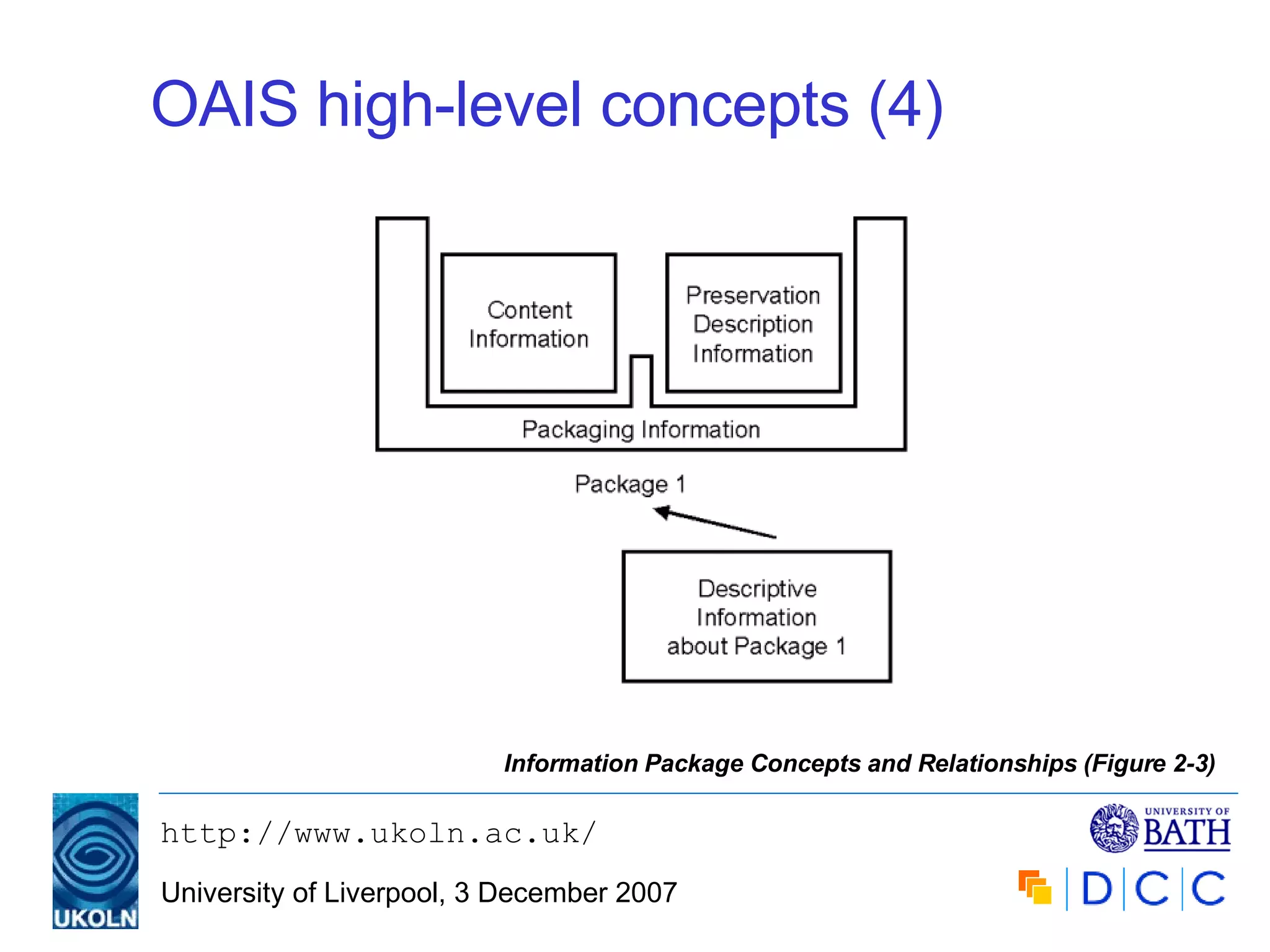
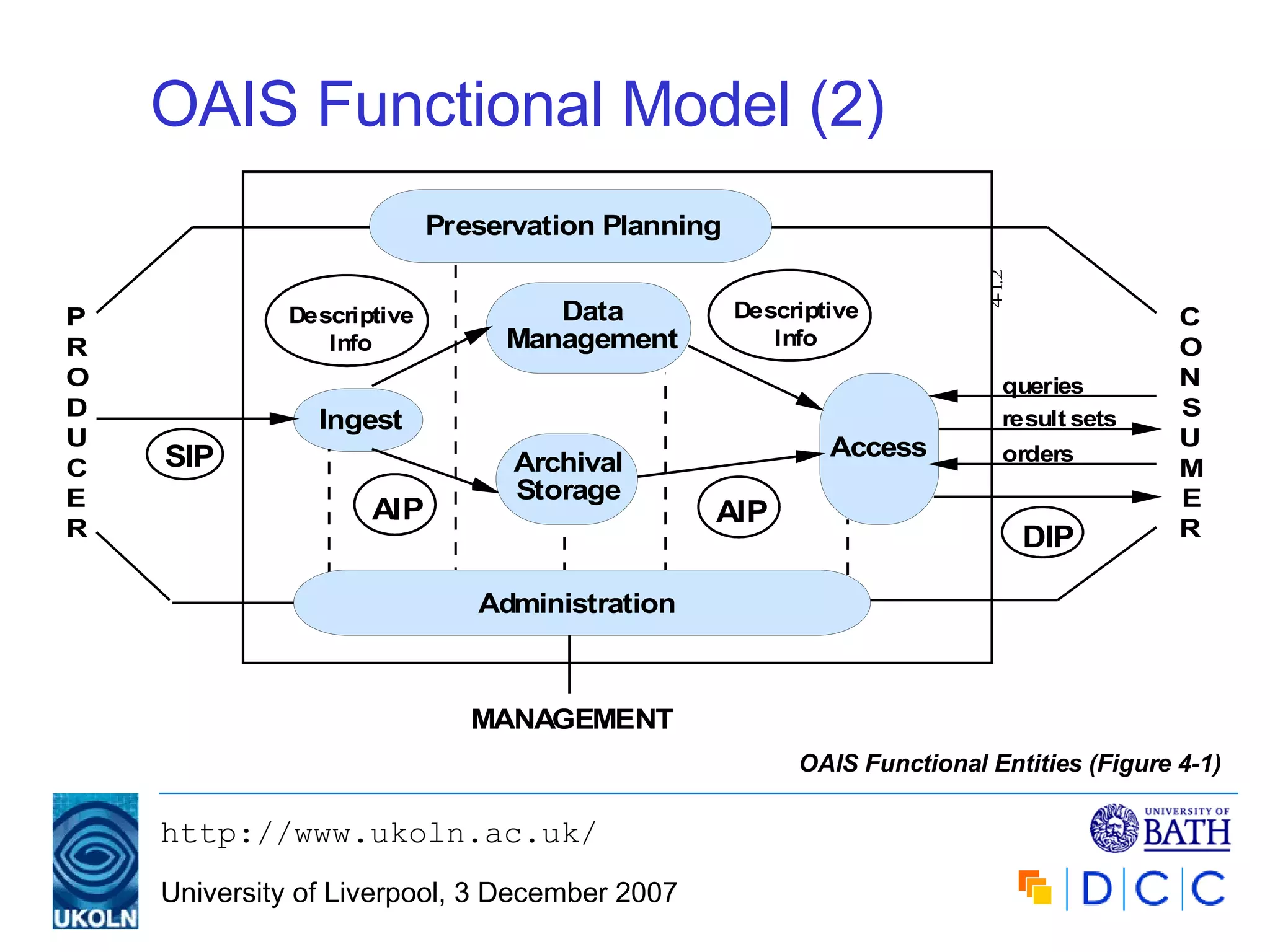
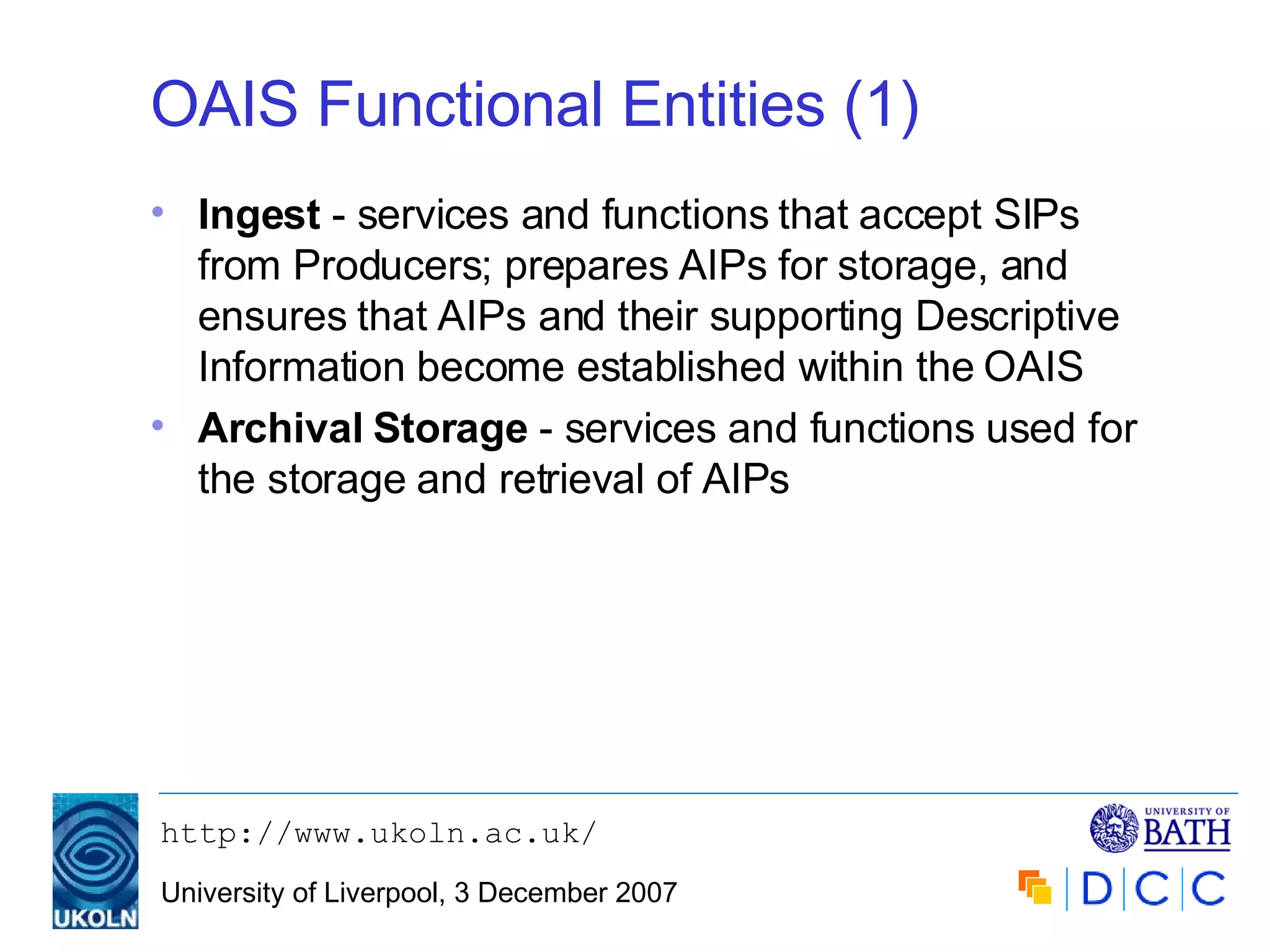
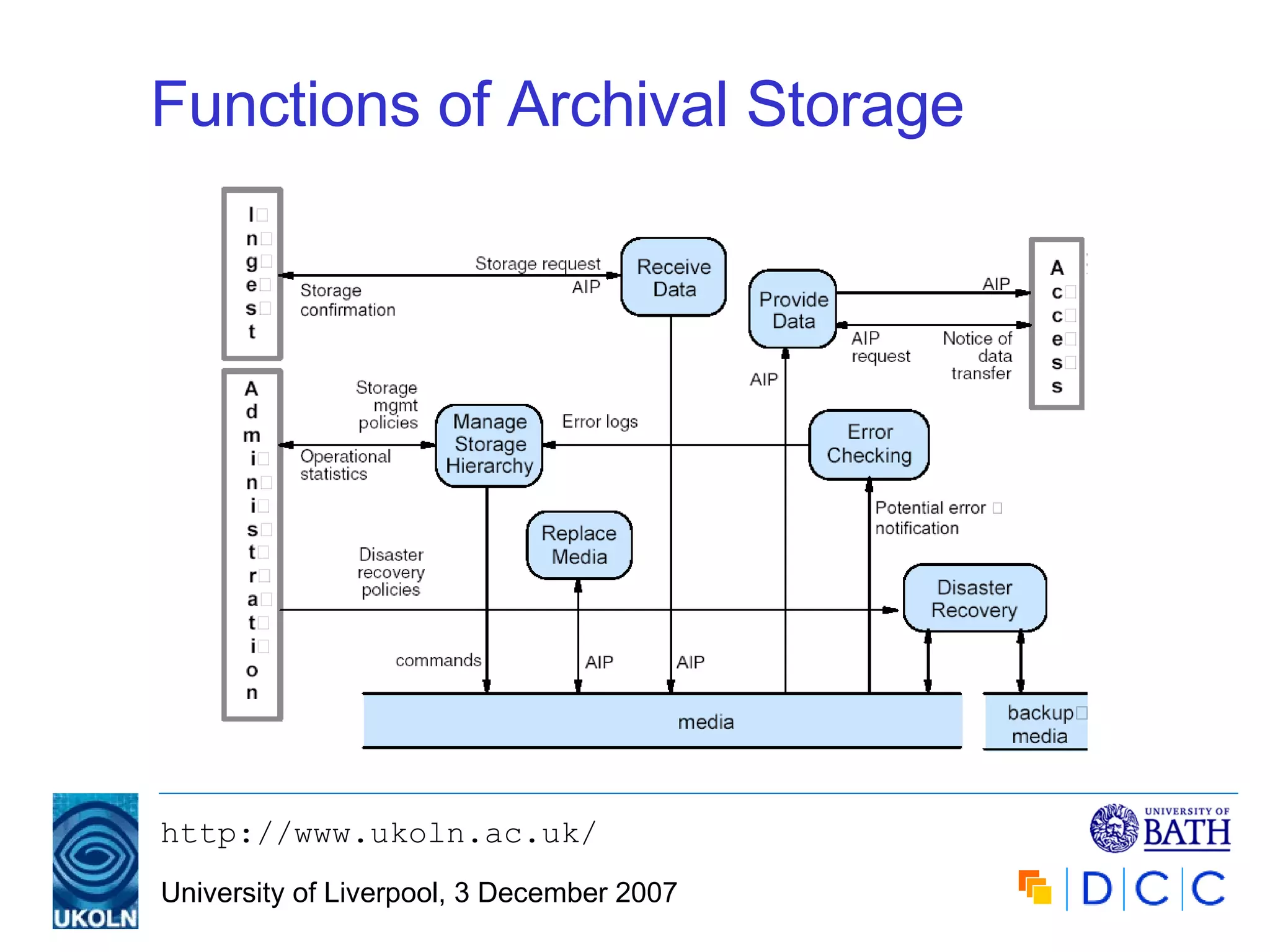
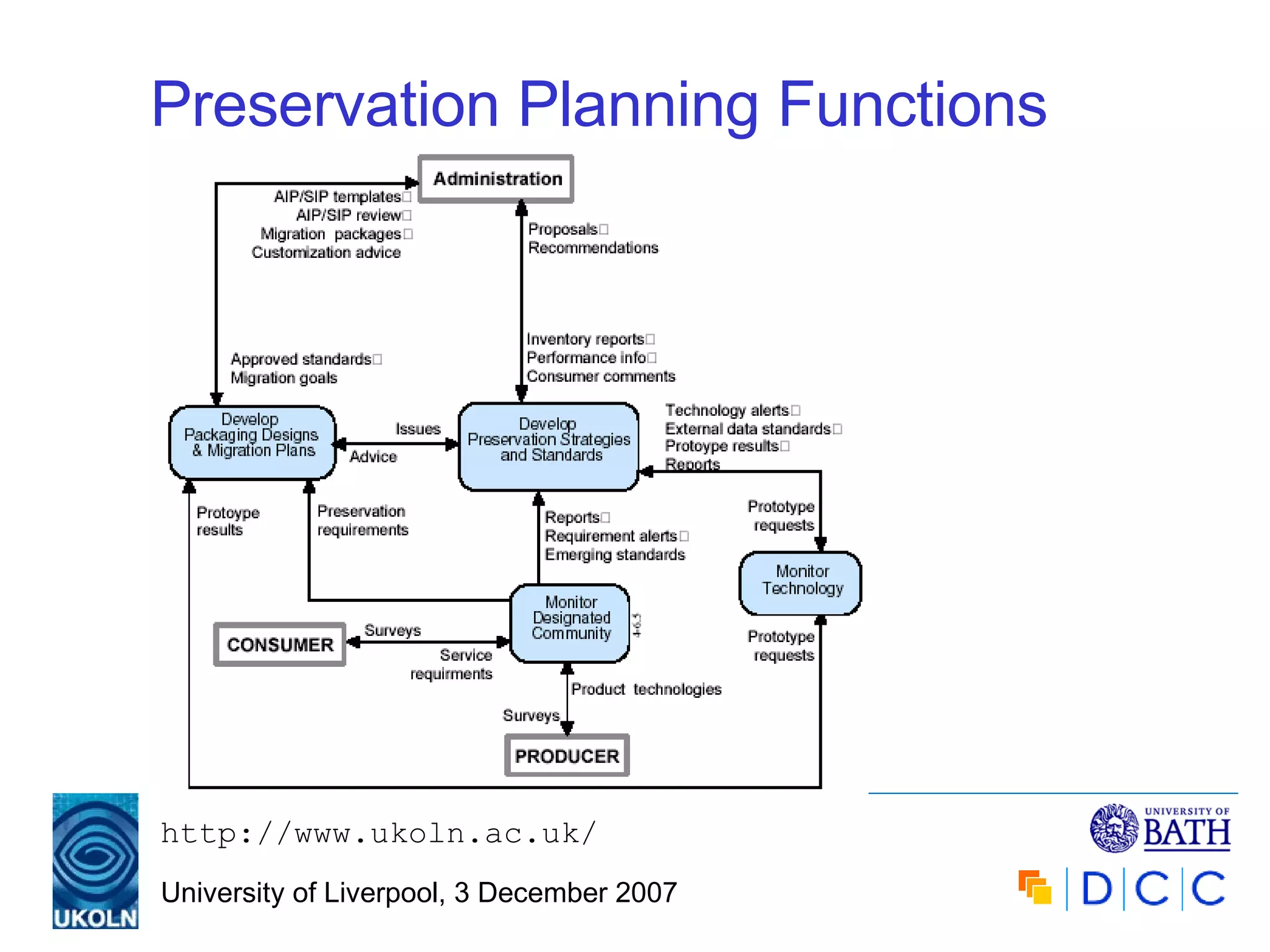
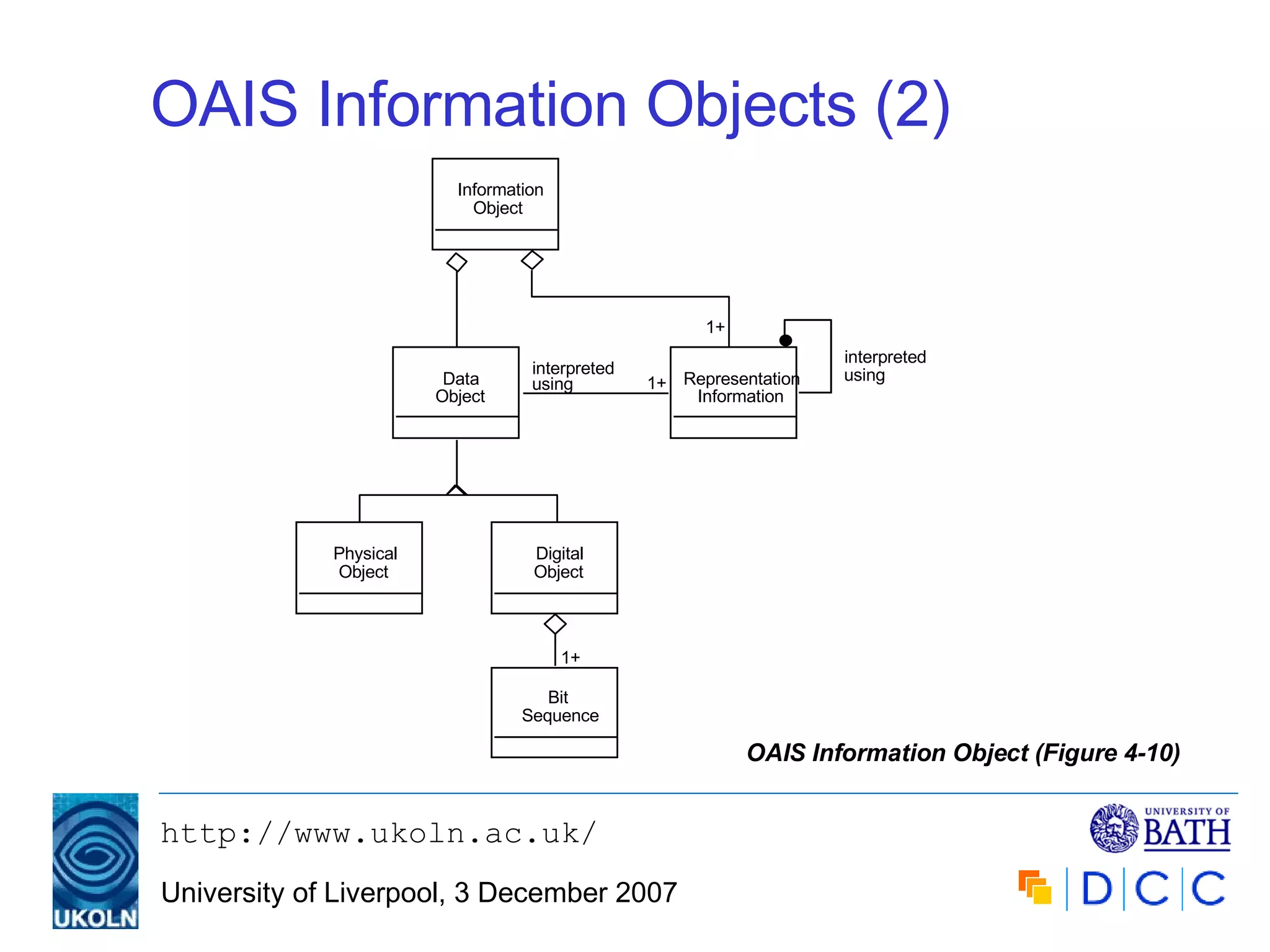
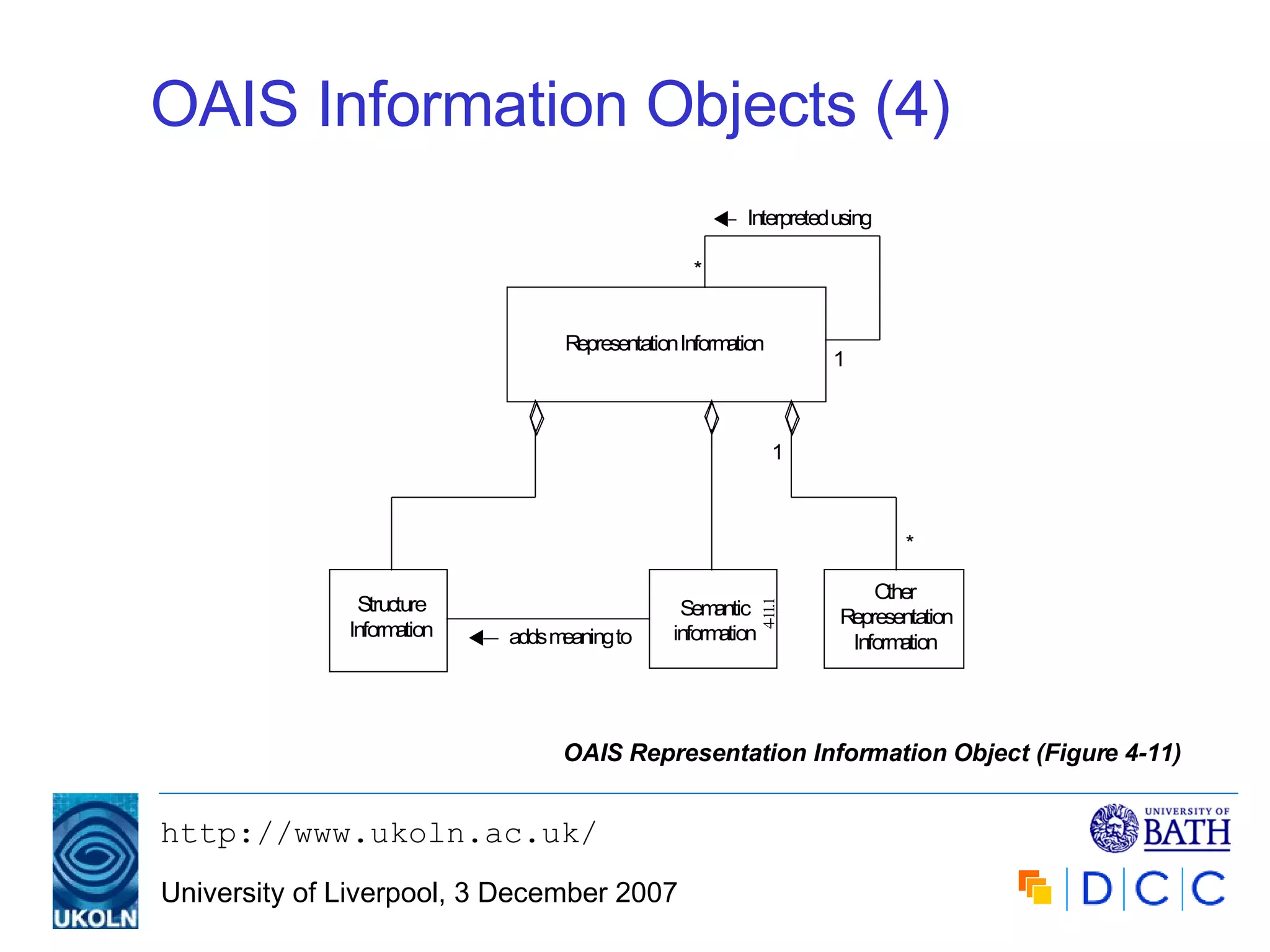
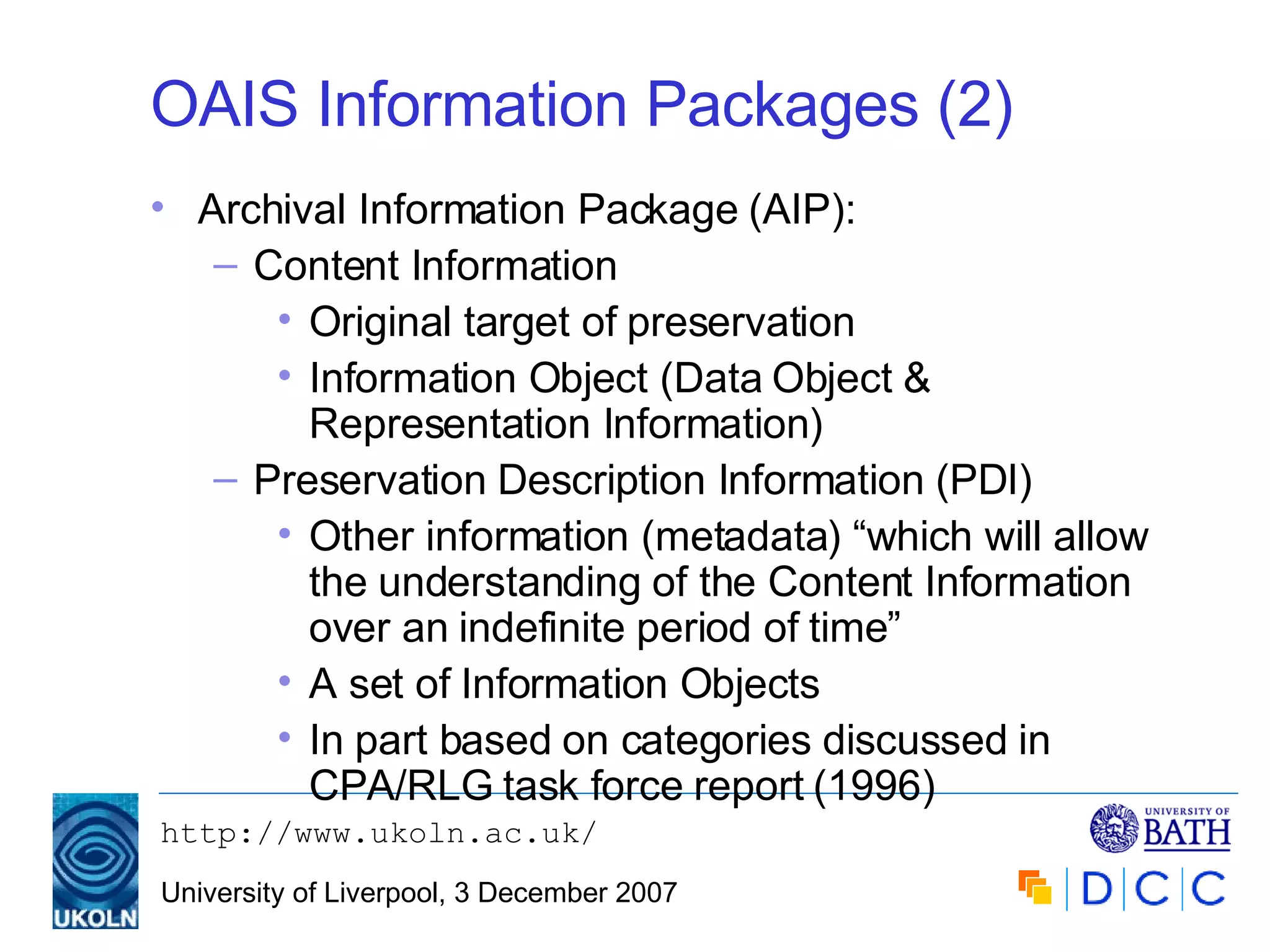
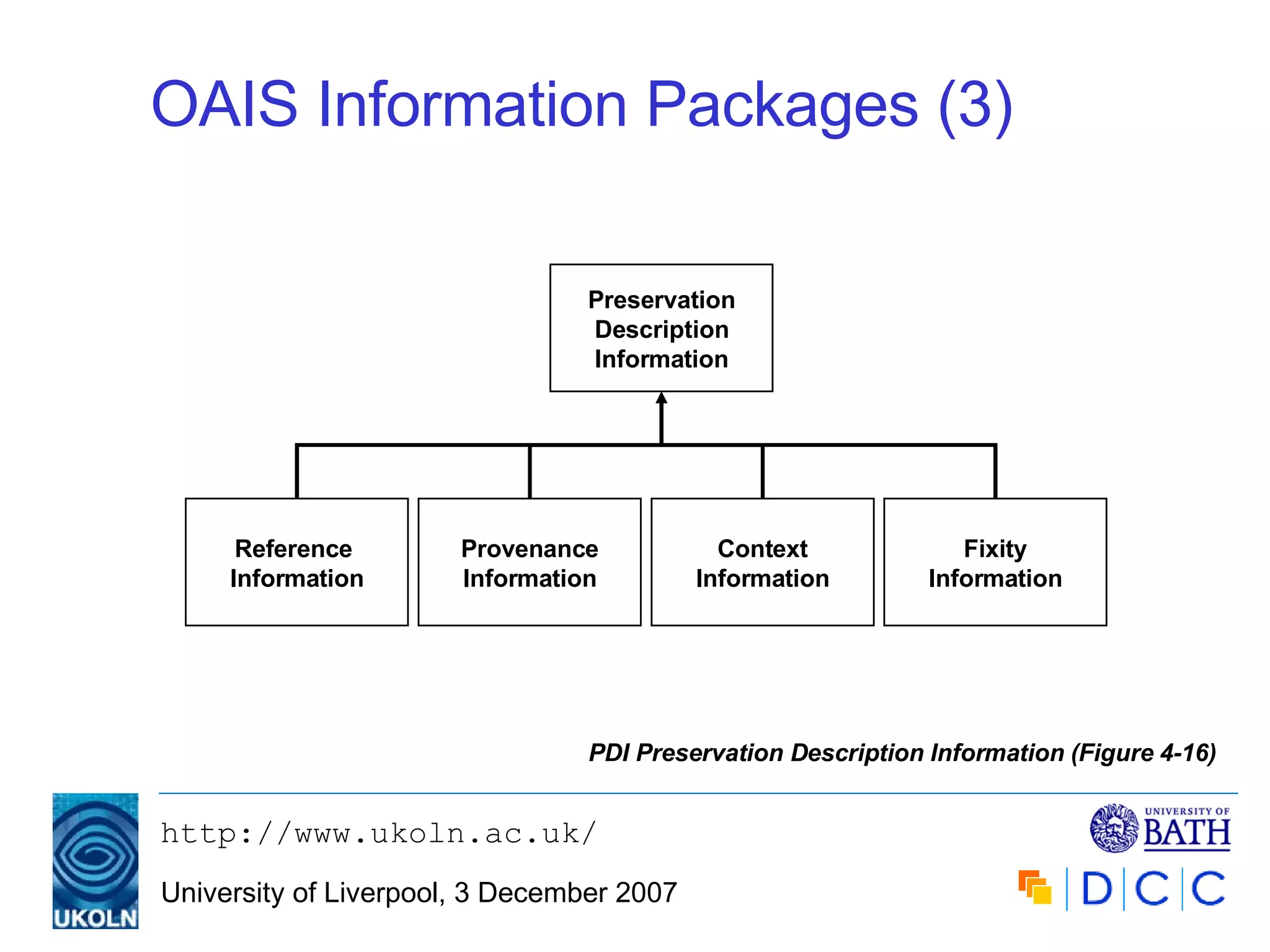
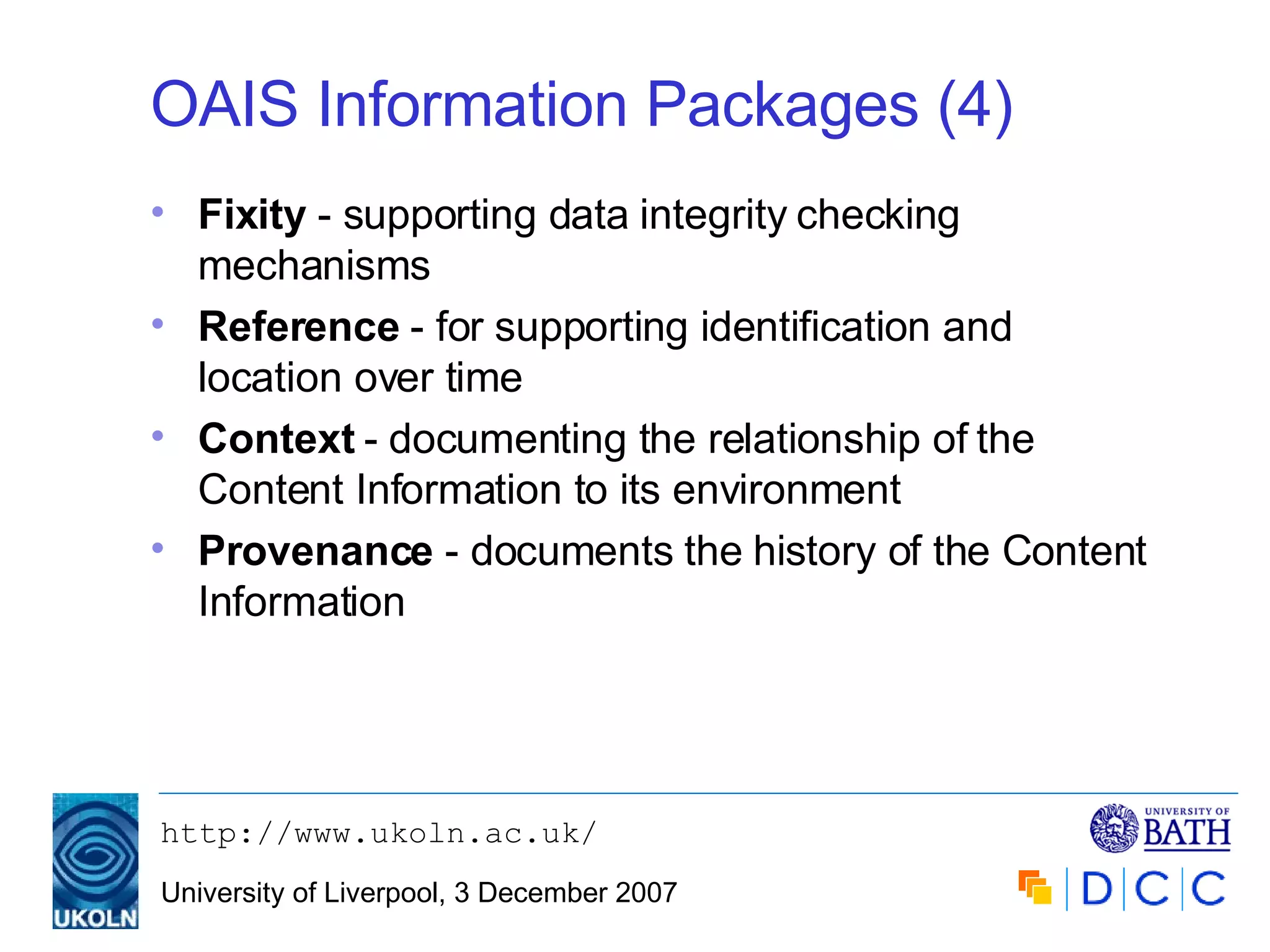
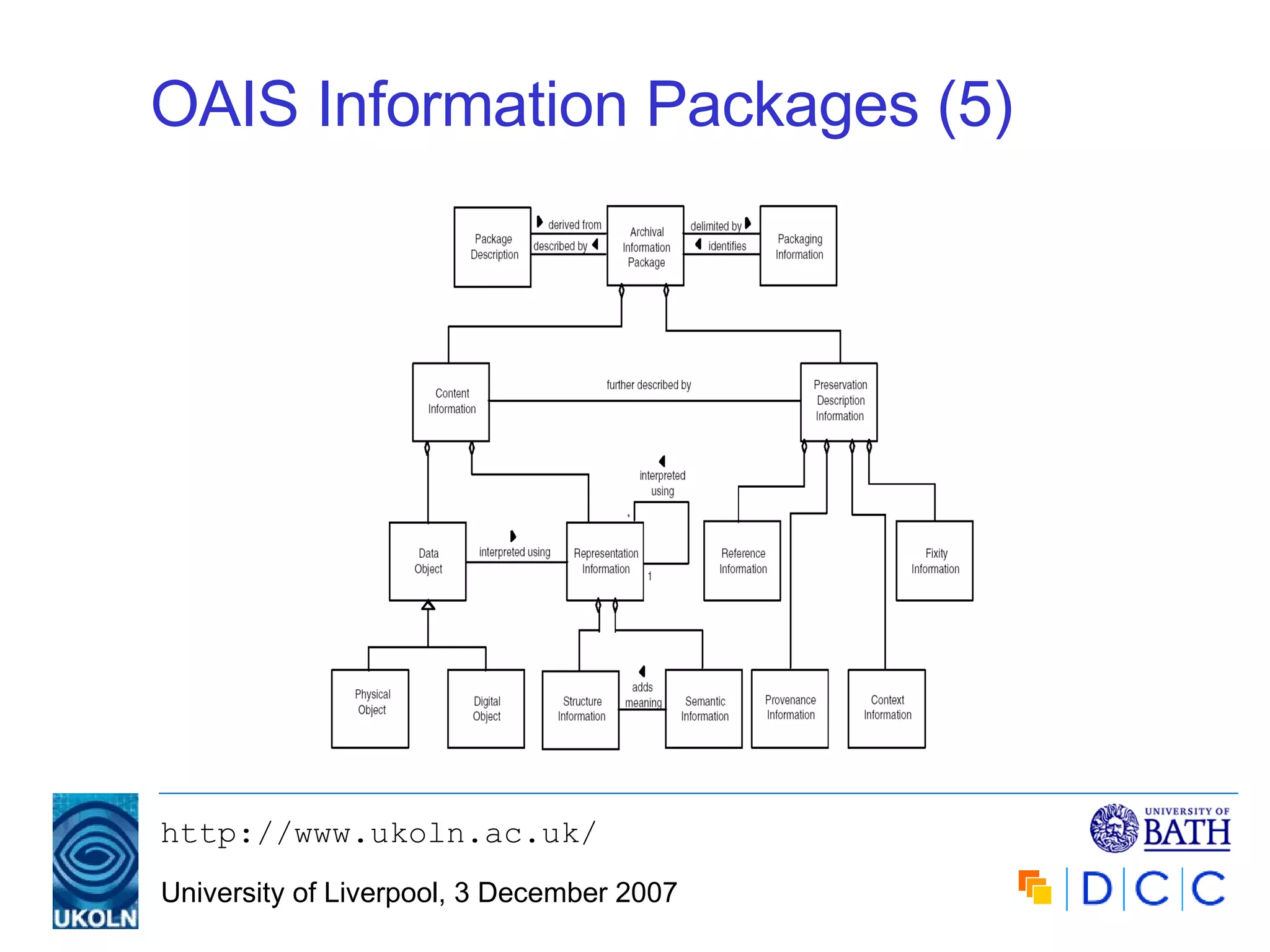
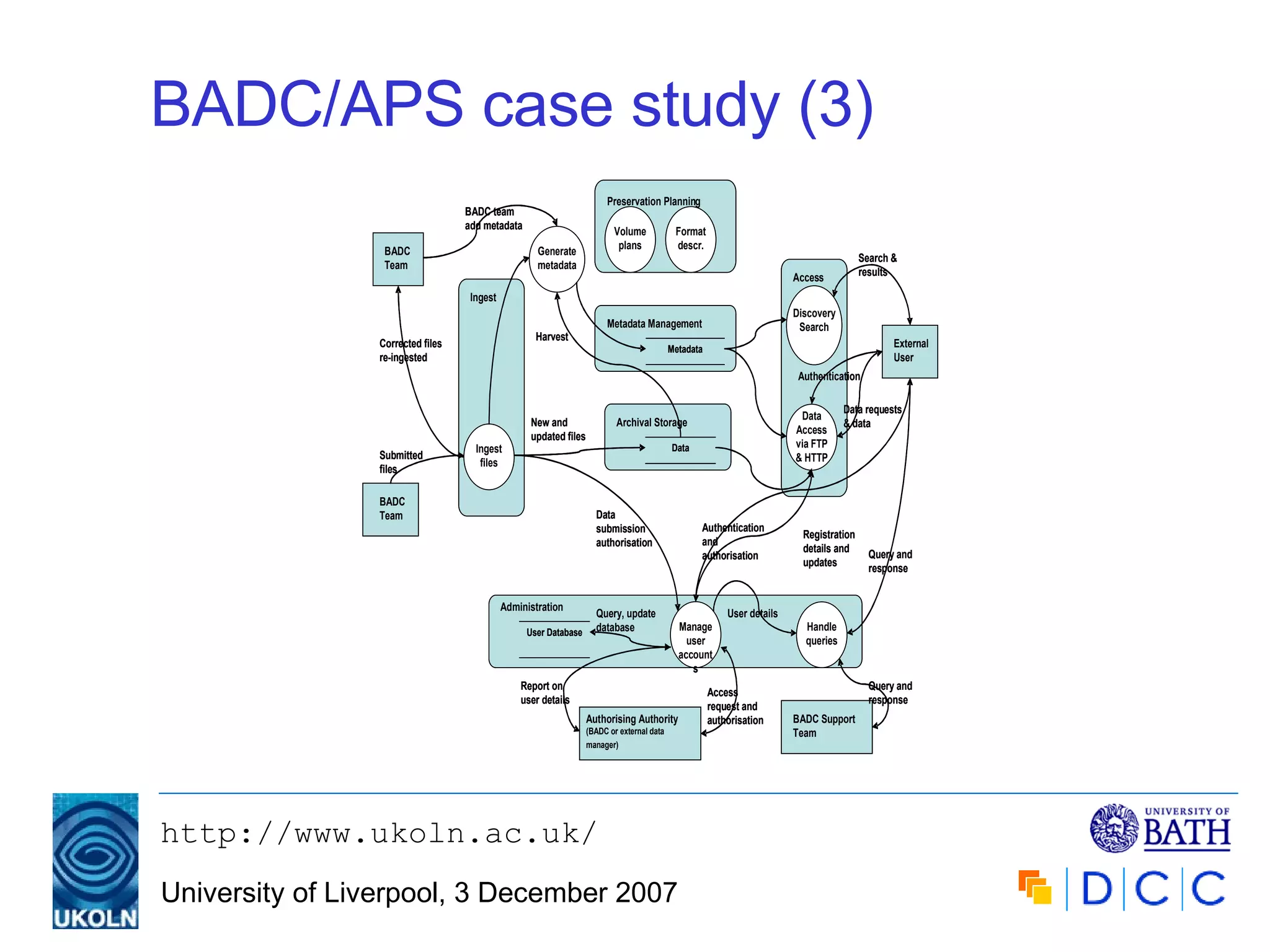
The document introduces the Open Archival Information System (OAIS) reference model, detailing its purpose, scope, and mandatory responsibilities for digital preservation. It covers key conceptual frameworks, information categories, and operational functions essential for maintaining long-term access to digital information in archives. The model serves as a guide for developing compliant repositories and assessing the effectiveness of existing archival systems.
![Introduction to the Reference Model for an Open Archival Information System (OAIS) Michael Day, Digital Curation Centre UKOLN, University of Bath [email_address] Archives and Records Management, HIST 564 Applied Communication and IT Skills, University of Liverpool, 3 December 2007](https://image.slidesharecdn.com/introduction-to-oais-model-1203438185684787-5/75/Introduction-to-the-Reference-Model-for-an-Open-Archival-Information-System-OAIS-1-2048.jpg)