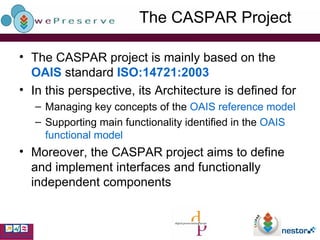
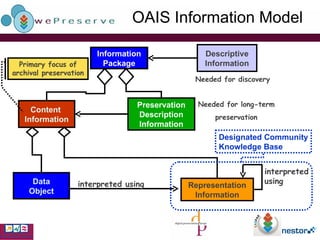
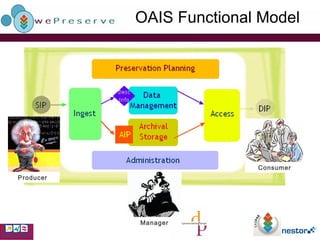
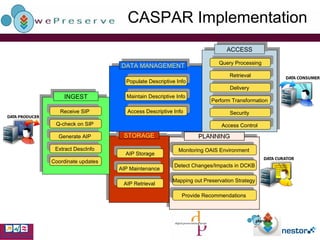
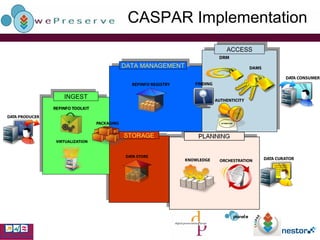
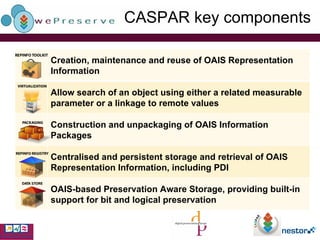
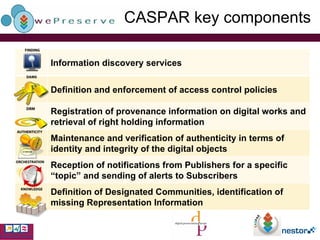
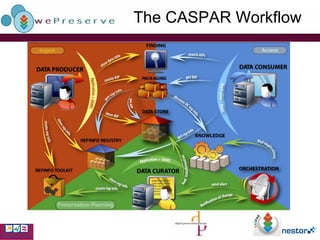
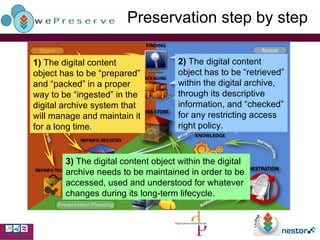
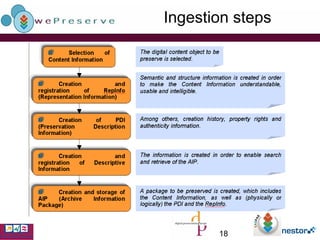
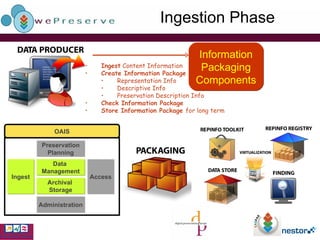
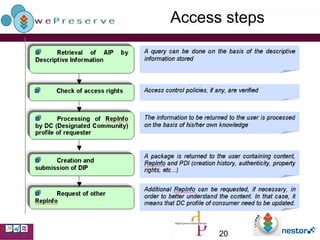
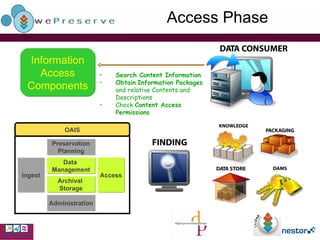
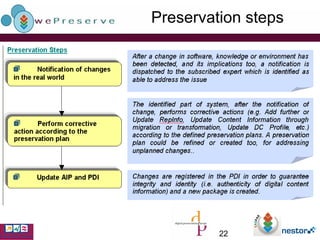
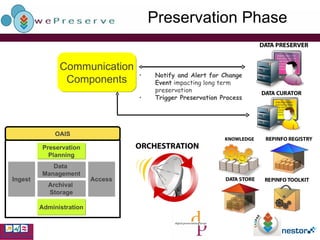
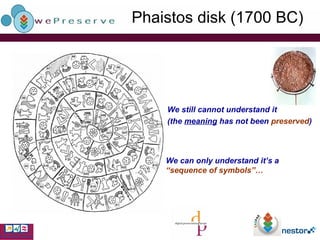
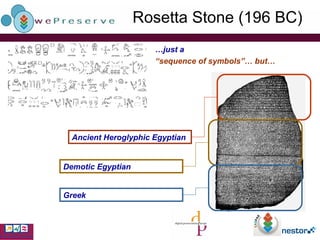
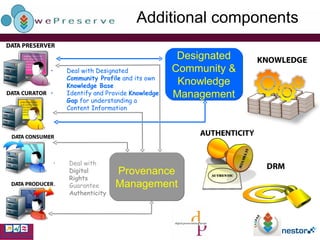
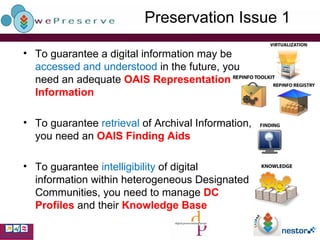
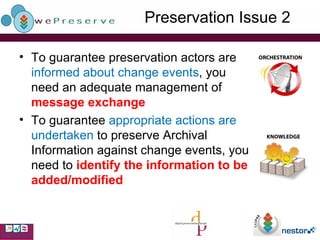
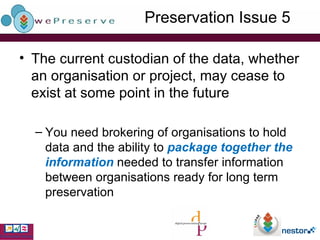
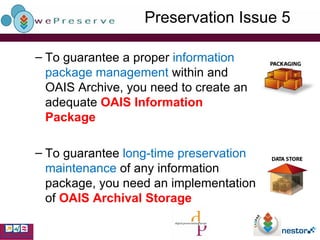
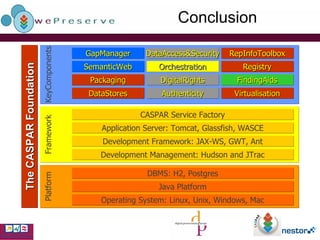
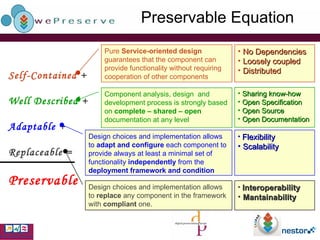
The CASPAR project addresses digital preservation challenges by implementing a framework based on the OAIS model, focusing on the long-term understandability and access to digital content amidst technological changes. It outlines preservation strategies that ensure the integrity, authenticity, and usability of digital objects while managing hardware, software, and data rights. Key innovations include a service-oriented design and mechanisms for handling digital rights and community-specific knowledge, aiming for a comprehensive preservation solution.