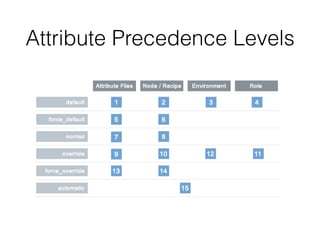
This document provides an introduction to using Chef for infrastructure automation and configuration management. It discusses what Chef is, why it is used, and its core components like recipes, resources, attributes, cookbooks, roles, environments, and more. It also covers how to set up a development environment for Chef, write recipes, and test Chef configurations using tools like Chefspec, Foodcritic, and Test Kitchen with Serverspec. The document aims to help readers understand Chef and be able to use it to define reusable infrastructure configurations.



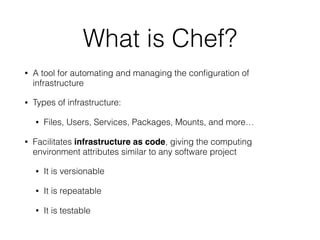


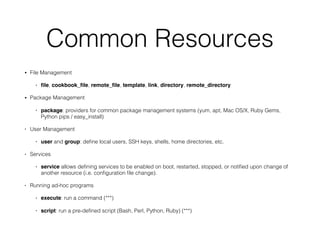
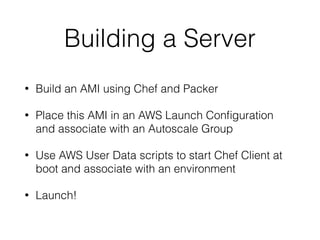
![Example Role
{
“name”:"webserver",
“description":"Web Server”,
“json_class":"Chef::Role",
“chef_type”:"role",
“run_list":[
“recipe[motd]",
“recipe[users]",
“recipe[apache]”
]
}](https://image.slidesharecdn.com/phillychefmeetup-160322134212/85/Introduction-to-Cooking-with-Chef-34-320.jpg)

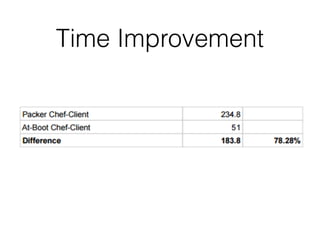


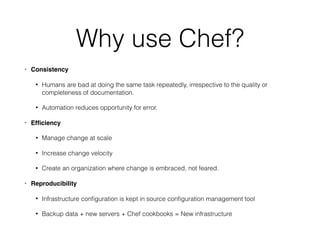
![Starting and Enabling
service 'httpd' do
action [:enable, :start]
end](https://image.slidesharecdn.com/phillychefmeetup-160322134212/85/Introduction-to-Cooking-with-Chef-77-320.jpg)
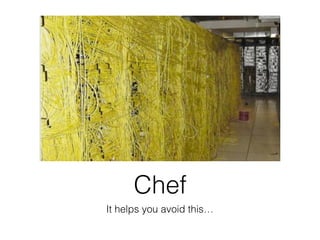
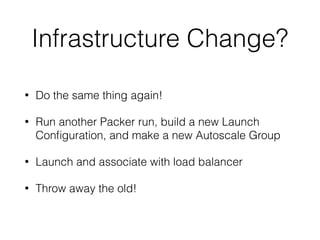
![Static Webpage
• In default.rb
template '/var/www/html/index.html' do
source 'index.html.erb'
mode '644'
end
• In templates/default/index.html.erb
Welcome to LeadiD!
Hostname: <%= node['hostname'] %>](https://image.slidesharecdn.com/phillychefmeetup-160322134212/85/Introduction-to-Cooking-with-Chef-78-320.jpg)
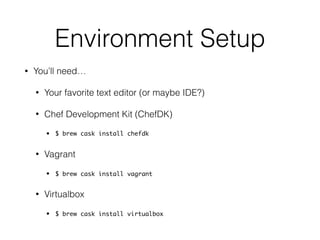
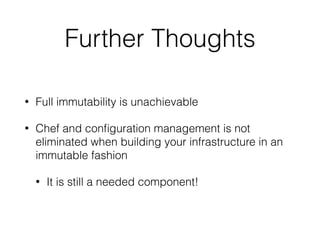
![Verify Success
• In .kitchen.yml
---
driver:
name: vagrant
network:
- ["forwarded_port", {guest: 80, host: 8095}]
• Open http://localhost:8095 in your web browser. Success?](https://image.slidesharecdn.com/phillychefmeetup-160322134212/85/Introduction-to-Cooking-with-Chef-79-320.jpg)