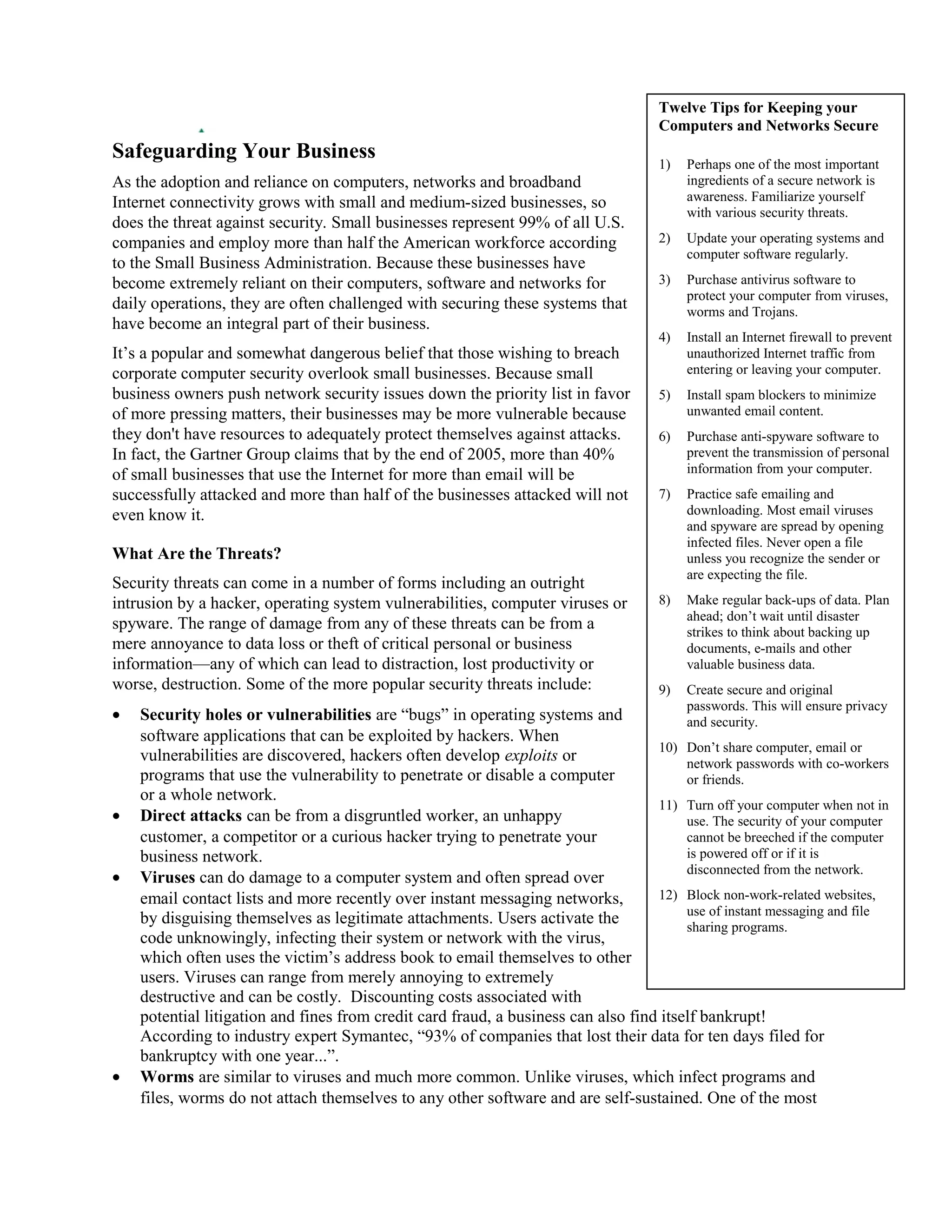
As small businesses have become increasingly reliant on computers and networks, the threats to their security have also grown. Small businesses are often challenged to secure their systems as they have limited resources. Over 40% of small businesses using the internet for more than email will be successfully attacked by the end of 2005, with over half not even realizing it. Security threats to businesses can come in many forms, including hacker intrusions, viruses, spyware, and more, which can potentially cause data loss, theft of information, and bankruptcy. It is important for small businesses to take basic steps to protect their computers and networks such as keeping software updated, using firewalls and antivirus software, and practicing safe email and internet habits.