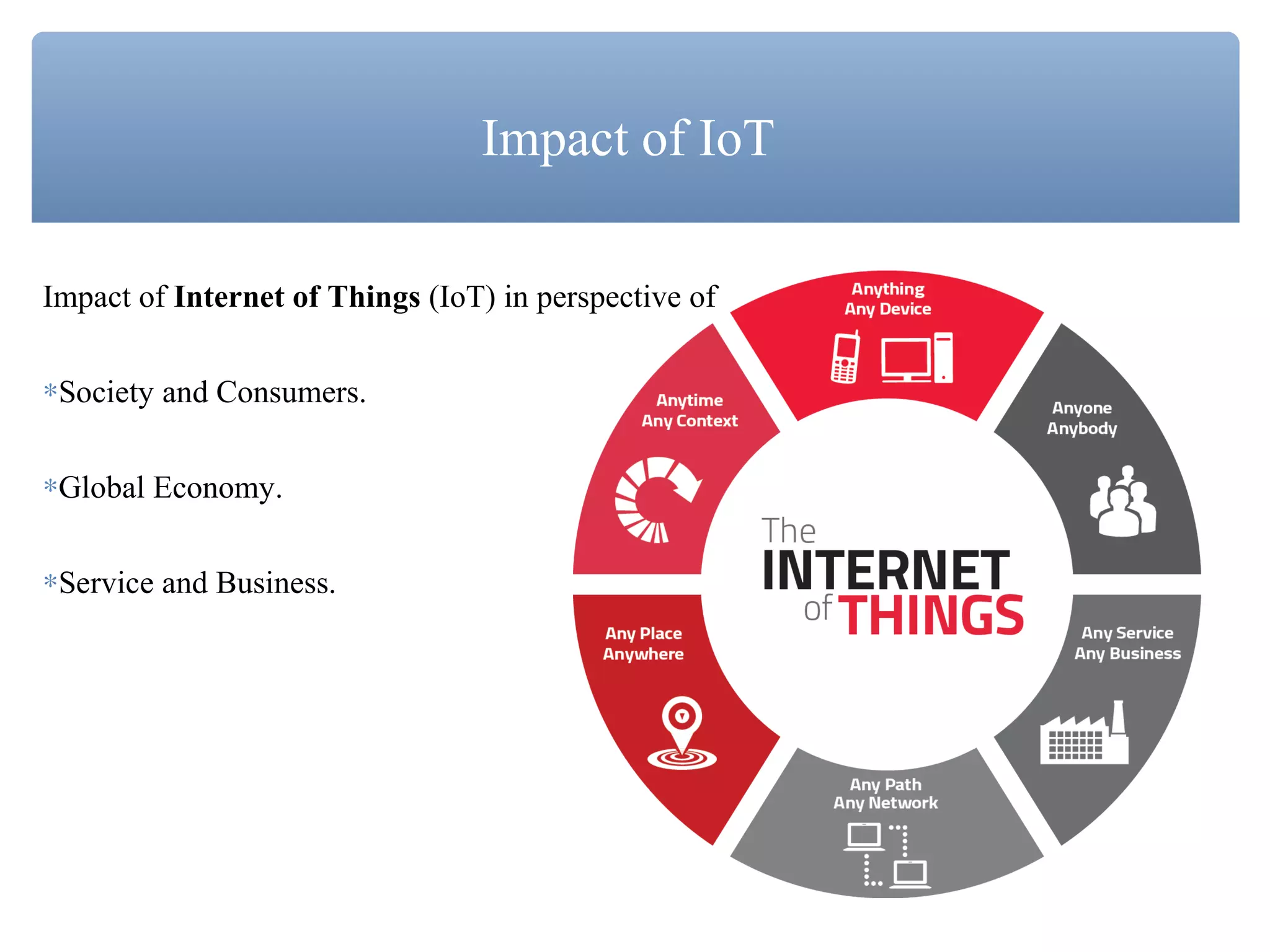
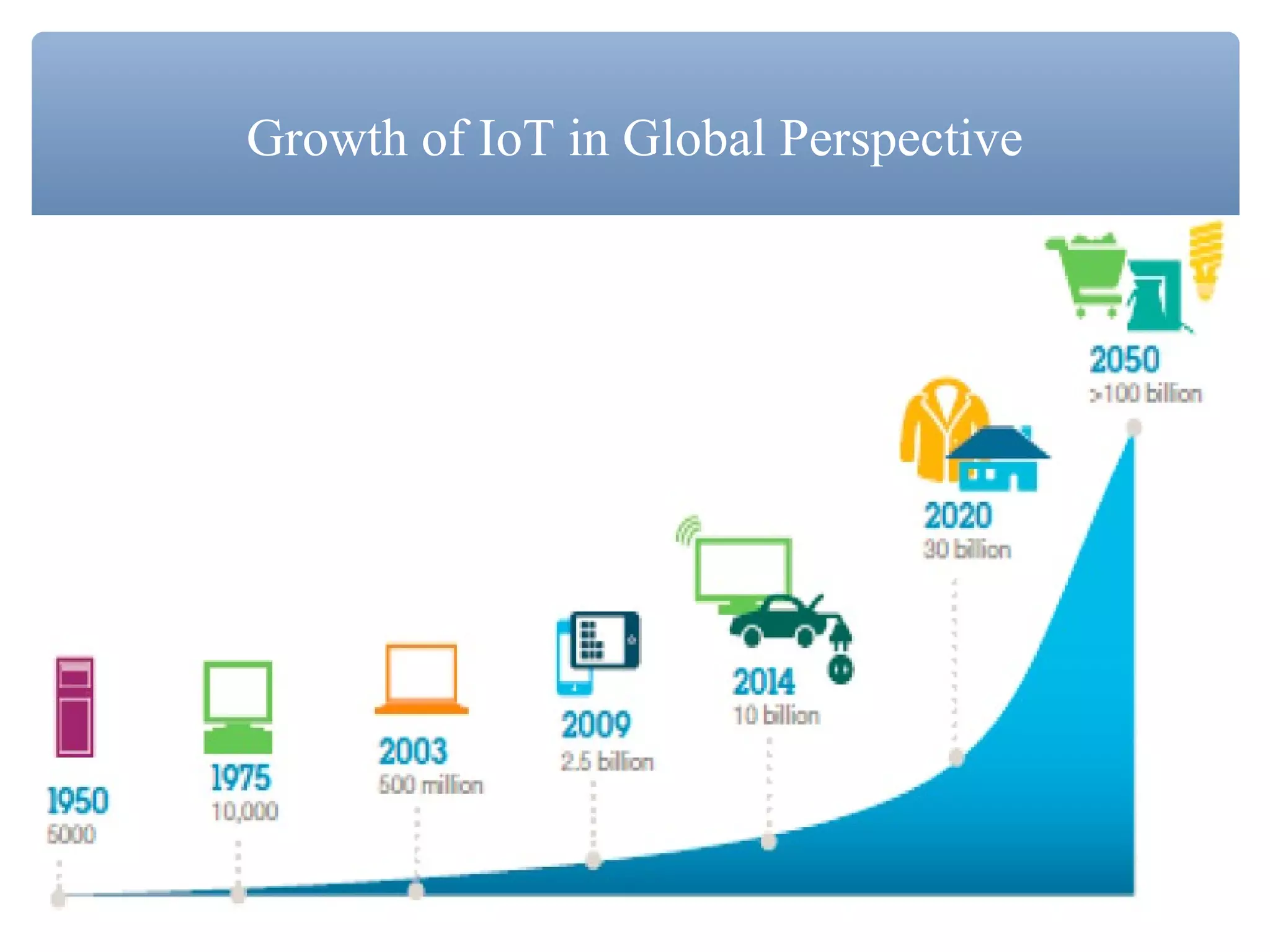
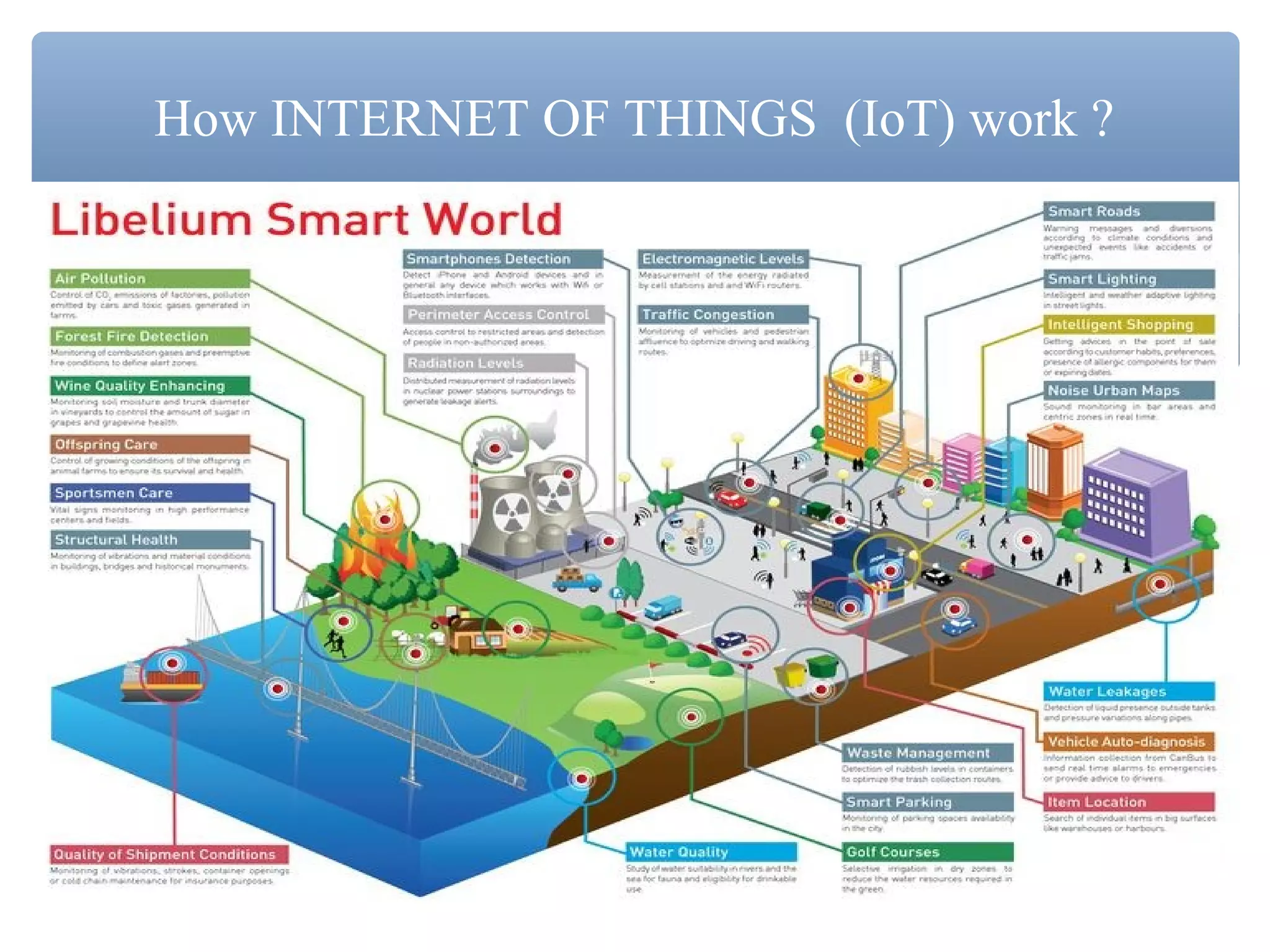
The document discusses the Internet of Things (IoT), emphasizing its definition as interconnected devices using embedded sensors for data optimization. It highlights the benefits IoT brings to various sectors, including enhanced healthcare and improved government efficiency, alongside risks such as security and privacy concerns. Overall, the document suggests that IoT has evolved into the Internet of Everything (IoE), integrating various capabilities for revolutionary application development.