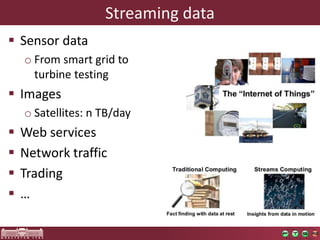
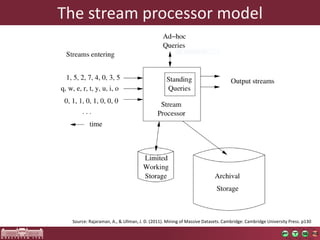
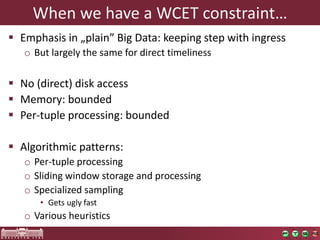
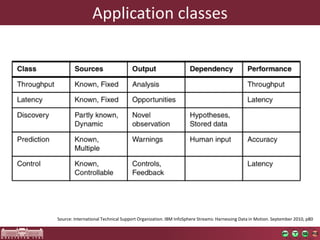
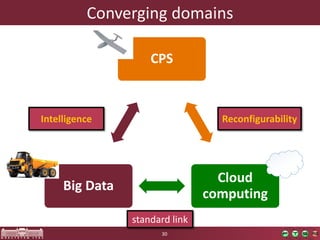
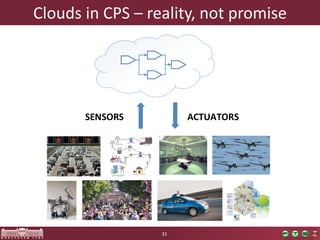
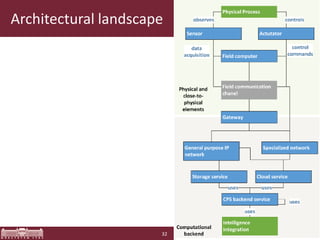
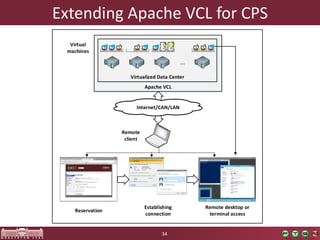
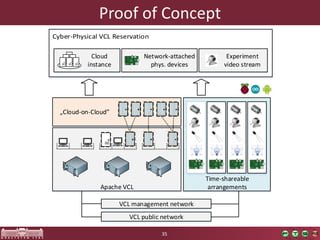
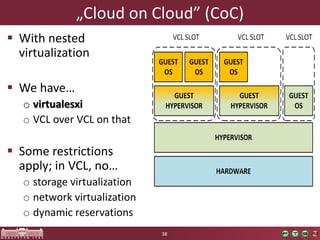
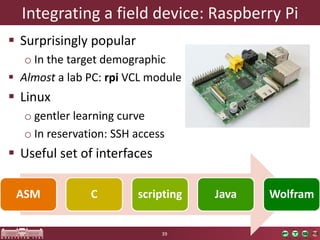
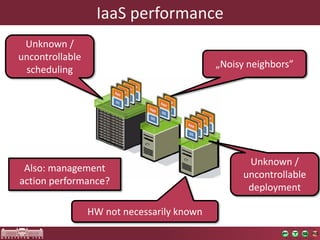
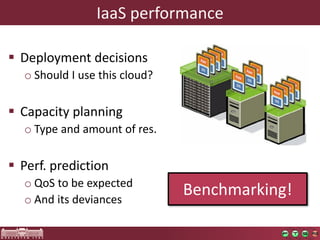
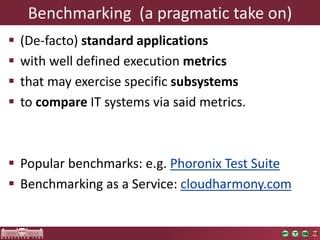
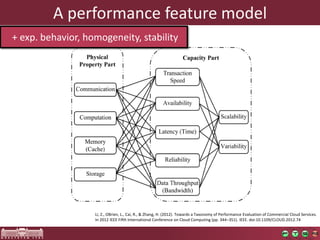
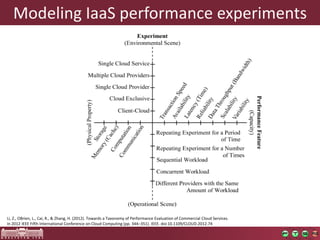
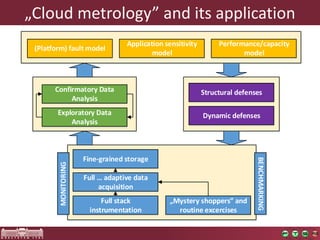
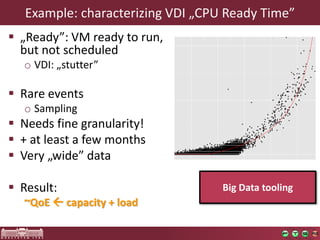
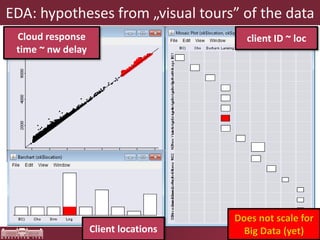
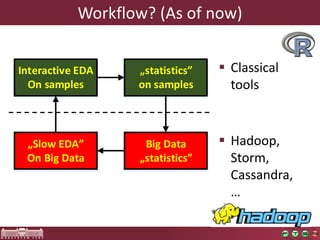
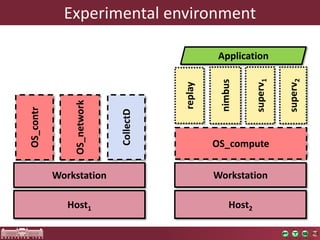
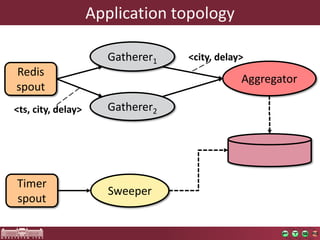
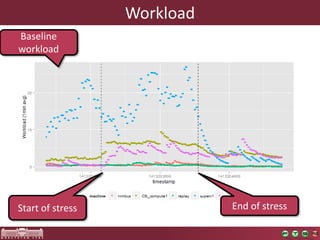
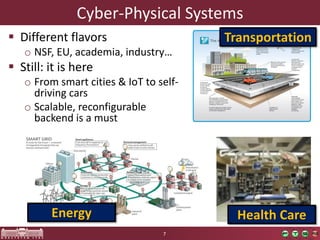
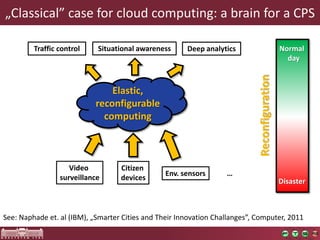
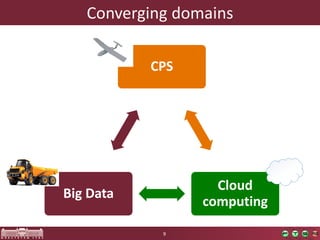
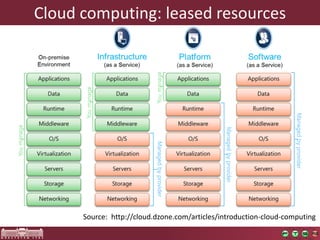
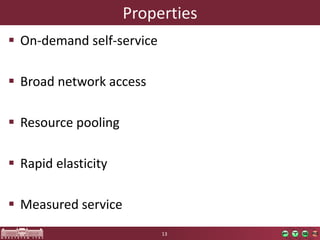
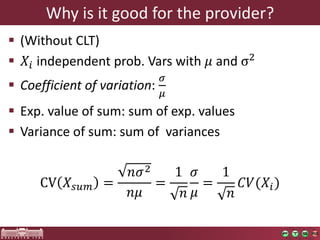
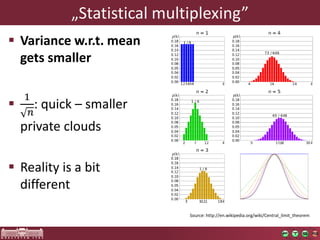
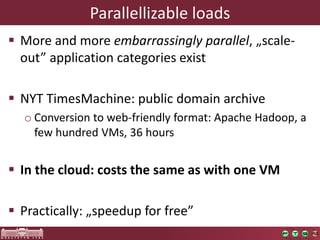
The document discusses the integration of cloud computing within cyber-physical systems (CPS), emphasizing the need for resilience in design and operation. It outlines various applications of CPS in fields such as healthcare and transportation while highlighting the importance of big data analytics in these systems. The paper also explores concepts such as resource pooling, performance evaluation, and the challenges of managing variability and real-time processing in a cloud environment.
![MapReduce(ApacheHadoop)
Distributed File System[ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ , ] [ ,[ , , ]] [ ,[ , , ]] [ ,[ , , ]] [ ,[ , , ]] [ ,[ , , ]] SHUFFLE Map Reduce [ , ][ , ][ , ][ , ][ , ]](https://image.slidesharecdn.com/imrekocsisserene2014school-141118025747-conversion-gate02/85/SERENE-2014-School-Measurement-Driven-Resilience-Design-of-Cloud-Based-Cyber-Physical-Systems-22-320.jpg)