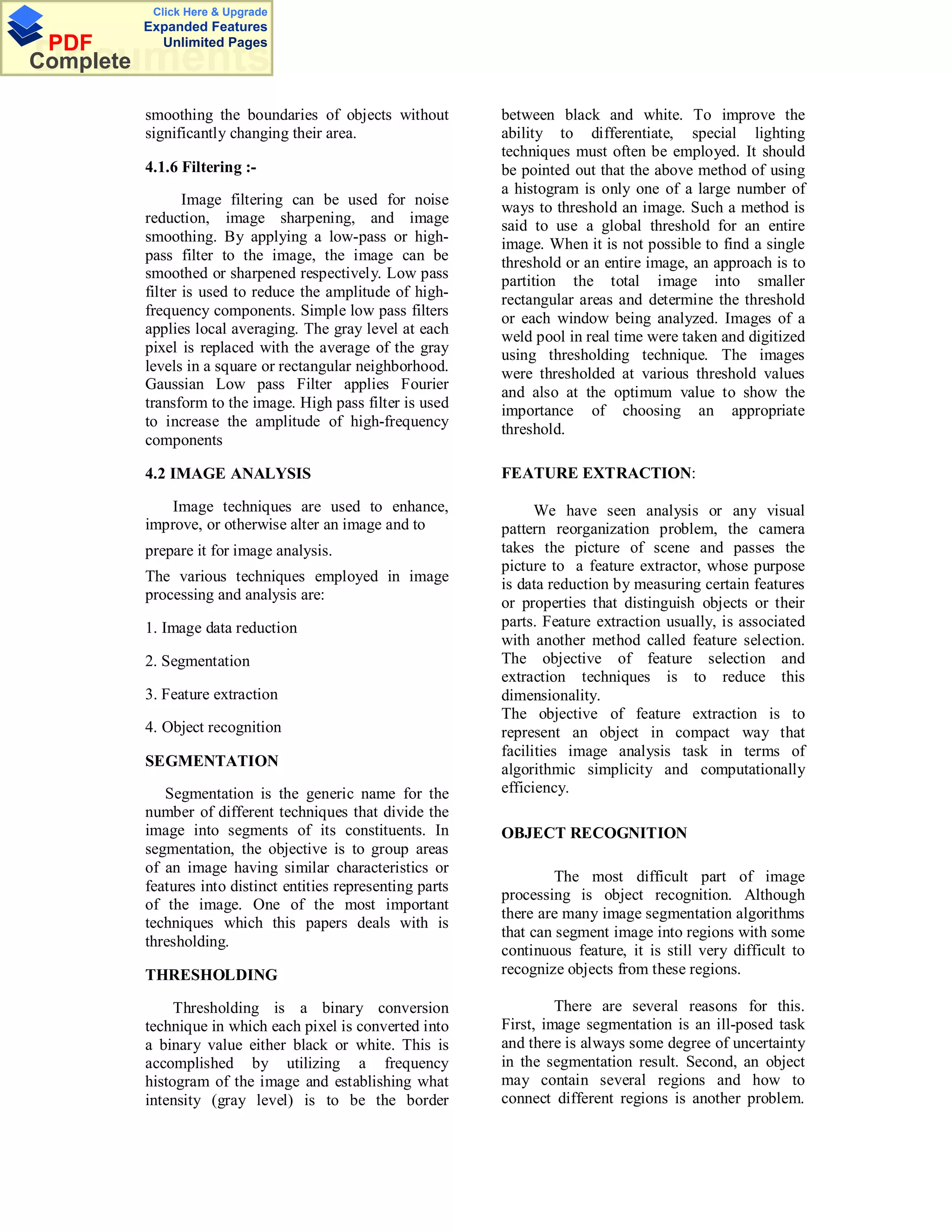
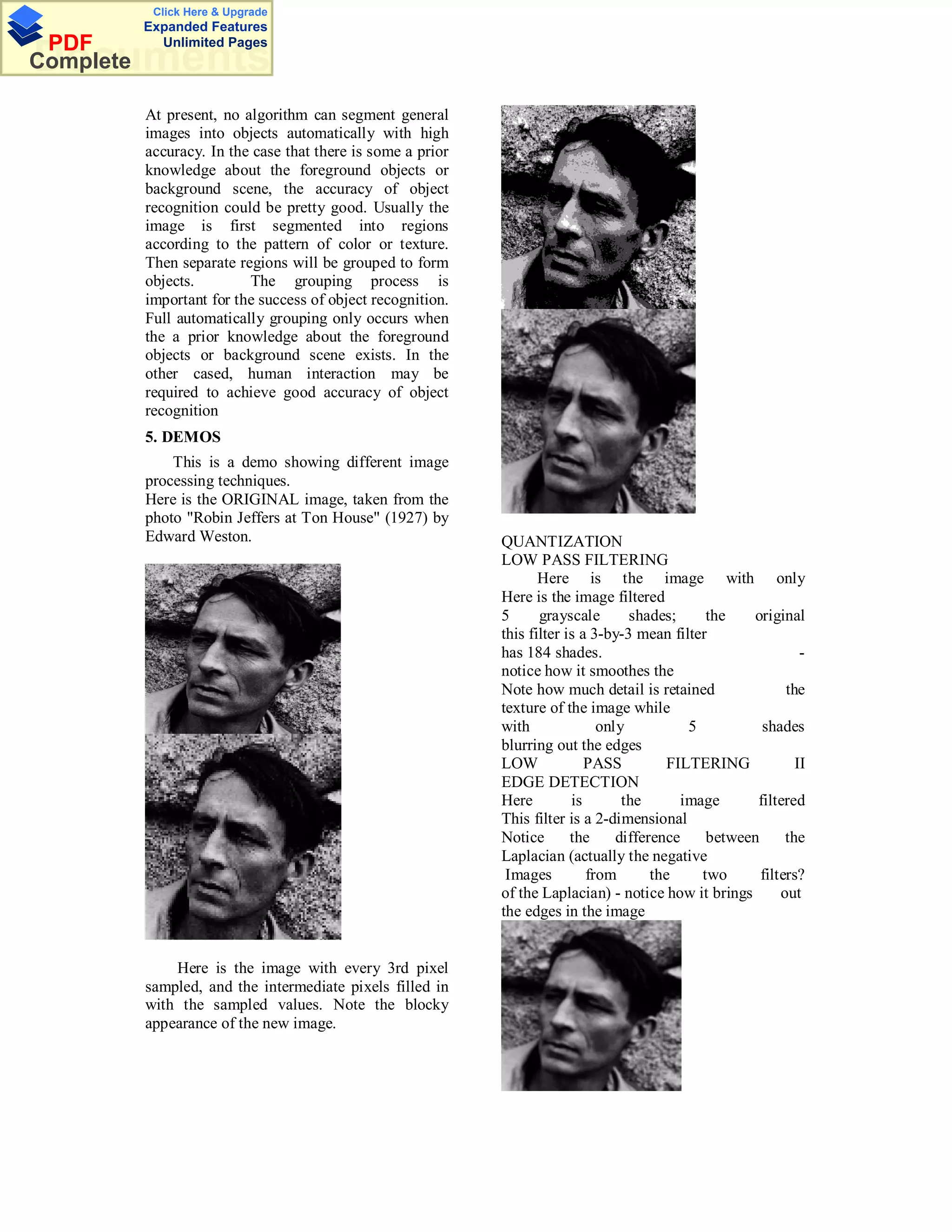
This document discusses image and speech processing. It provides an overview of image processing techniques including dithering, erosion, dilation, opening, and closing. These techniques are used to manipulate digital images by modifying pixels at image boundaries or within images. The document also discusses using speech recognition to improve human-computer interfaces and synchronization of image and speech processing.