This document summarizes a research paper that proposes techniques for fast recovery from dual-link failures in mobile ad hoc networks (MANETs). It discusses link protection and path protection schemes, and proposes two approaches for dual-link failure recovery: failure dependent link protection (FDLP) and failure independent link protection (FILP). The paper develops an integer linear program and heuristic algorithm based on minimum cost path routing to solve the backup link mutual exclusion problem for dual-link failures. It evaluates the performance of the proposed approaches through simulations, finding that FDLP achieves a higher packet delivery ratio than FILP.
![Ms.Ashwina .N. Patil , Prof. S.S. Kanade , Ms. S.S. Bhakare / International Journal of
Engineering Research and Applications (IJERA) ISSN: 2248-9622 www.ijera.com
Vol. 2, Issue4, July-August 2012, pp.1486-1489
Fast Recovery For Dual-Link Failure Through Backup Path
Ms.Ashwina .N. Patil* , Prof. S.S. Kanade** , Ms. S.S. Bhakare***
*
Department of CSE, College of Engineering. Osmanabad
**
Head of E&TC Dept, College of Engineering , Osmanabad
***
Department of CSE, Sinhgad College of Engineering. Pune.
ABSTRACT
The nodes in Mobile Ad Hoc Network [4], [5]. Although the WDM network and wireless
(MANET) are mobile resulting in dynamic ad-hoc settings are quite different in nature, they
topology with high rate of link breakage and share a number of problems and challenges. One of
network partitions leading to interruptions in the them is failures of network components. If a link
ongoing communication. Because of node mobility failure is detected on the primary path (through
and power limitations, the network topology which actual data transmission is taking place), the
changes frequently. Link failures or path failure source can switch to an alternate path instead of
are common in such type of network. Therefore initiating a route discovery/recovery process. A new
the networks employ path/link protection to discovery takes place only when all precomputed
achieve fast recovery from dual failures. While the paths break.
first link failure can be protected using link Since in a wireless ad-hoc network has no
protection, but if second link is failed then we fixed infrastructure and there is no centralized control
have the problem of recover that path so the over the nodes ; no designated routers. So nodes
purpose of our system is that recovery from serve as routers for each other, and data packets are
second failure. One of the strategies to recover forwarded from node to node in a multi-hop fashion.
from dual-link failures is to employ link Protecting the circuits or connections established in
protection for the two failed links independently, such networks against single-link failures may be
which requires that two links may not use each achieved in two ways: path protection or link
other in their backup paths if they may fail protection [6]. Main focus of this paper is to protect
simultaneously. Such a strategy is referred to as end-to-end connections from dual-link failures using
backup link mutual exclusion (BLME). This path protection and link protection.
paper develops a solution to the BLME problem
by using two approaches by: 1) integer linear 2. TAXONOMY OF PROTECTION SCHEMES
program; 2) developing a polynomial time Protection schemes proposed in the
heuristic based on minimum cost path routing. literature can be broadly classified as link protection
and path protection.
Keywords-MANET, BLME, FDLP, FILP.
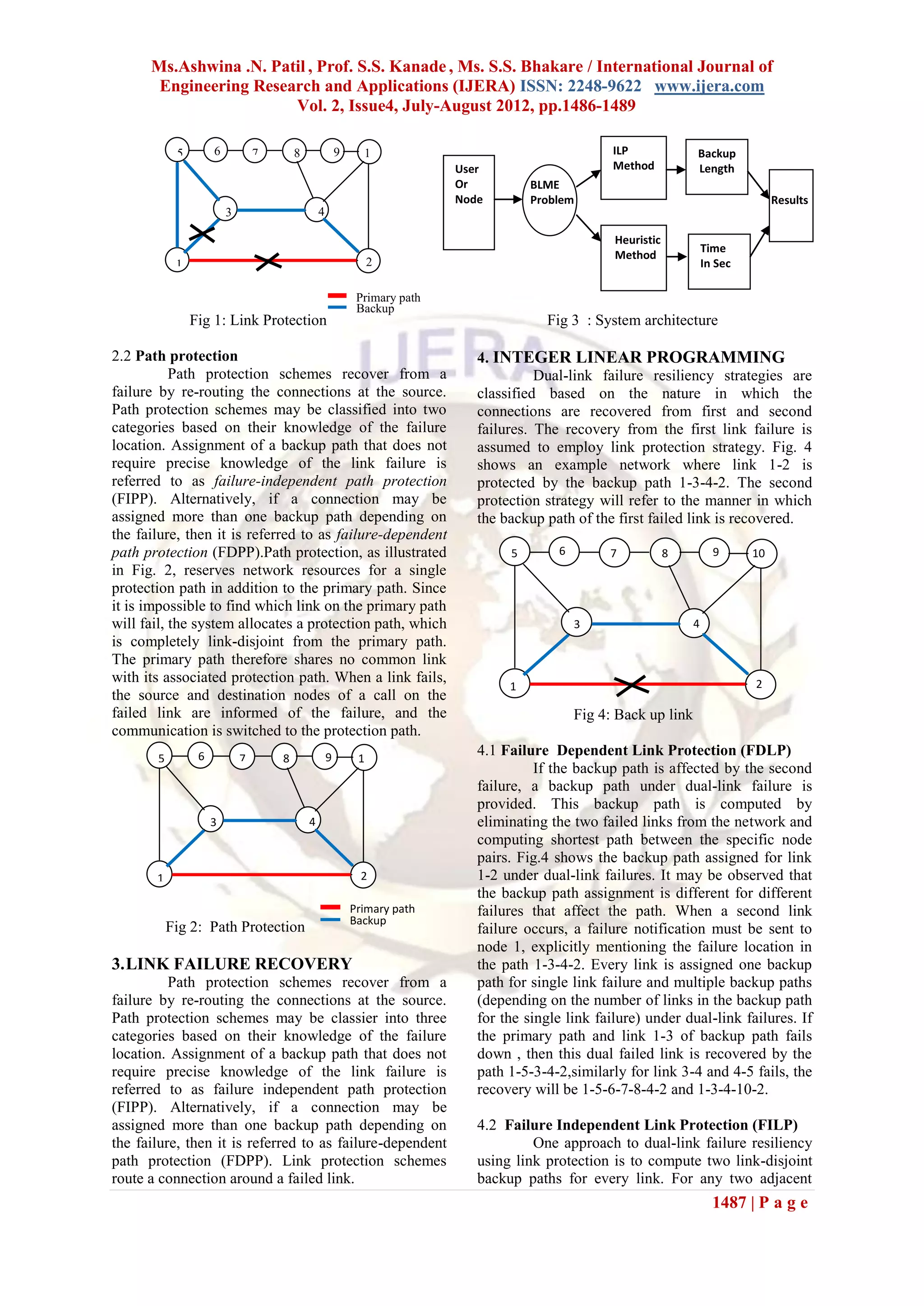
2.1 Link protection
1. INTRODUCTION Link protection schemes route a connection
A Mobile Adhoc Network (MANET) is a around a failed link. Re-routing is performed by the
network composed of mobile nodes mainly node connected to the failed link to the neighboring
characterized by the absence of centralized node on the original path. Such a protection may be
coordination or fixed infrastructure, which makes any achieved in the network in a way that is transparent
node in the network act as potential router. MANETs to the source node, except in cases where a link
are also characterized by a dynamic, random and connected to the source or destination fails. Link
rapidly changing topology. In MANETs, protection, as shown in Fig. 1, reroutes all the
communication link between mobile nodes always connections on the failed link around it. When
require over multi-hop paths. Since no infrastructure accepting a call request, the link protection scheme
exists and node may cause frequent link failure. will reserve the network resource for the associated
In WDM network, the failure of a single protection path. The protection path connects the two
fiber link may lead to tremendous data loss since a nodes adjacent to the failed link. When a link failure
single fiber link can carry a huge amount of data (on occurs, the node adjacent to and upstream of the
the order of terabits per second).Therefore, network failed link immediately redirects the traffic along the
survivability is an important problem in network predetermined protection path to the node on the
design and its real-time operation. In order to reduce other end of the failed link to restores transmission.
the data loss, various protection and restoration
mechanisms have been proposed and studied in the
literature to recover traffic after a failure occurs and
before the failure is physically repaired [1], [2], [3],
1486 | P a g e](https://image.slidesharecdn.com/il2414861489-121002054800-phpapp01/75/Il2414861489-1-2048.jpg)
![Ms.Ashwina .N. Patil , Prof. S.S. Kanade , Ms. S.S. Bhakare / International Journal of
Engineering Research and Applications (IJERA) ISSN: 2248-9622 www.ijera.com
Vol. 2, Issue4, July-August 2012, pp.1486-1489
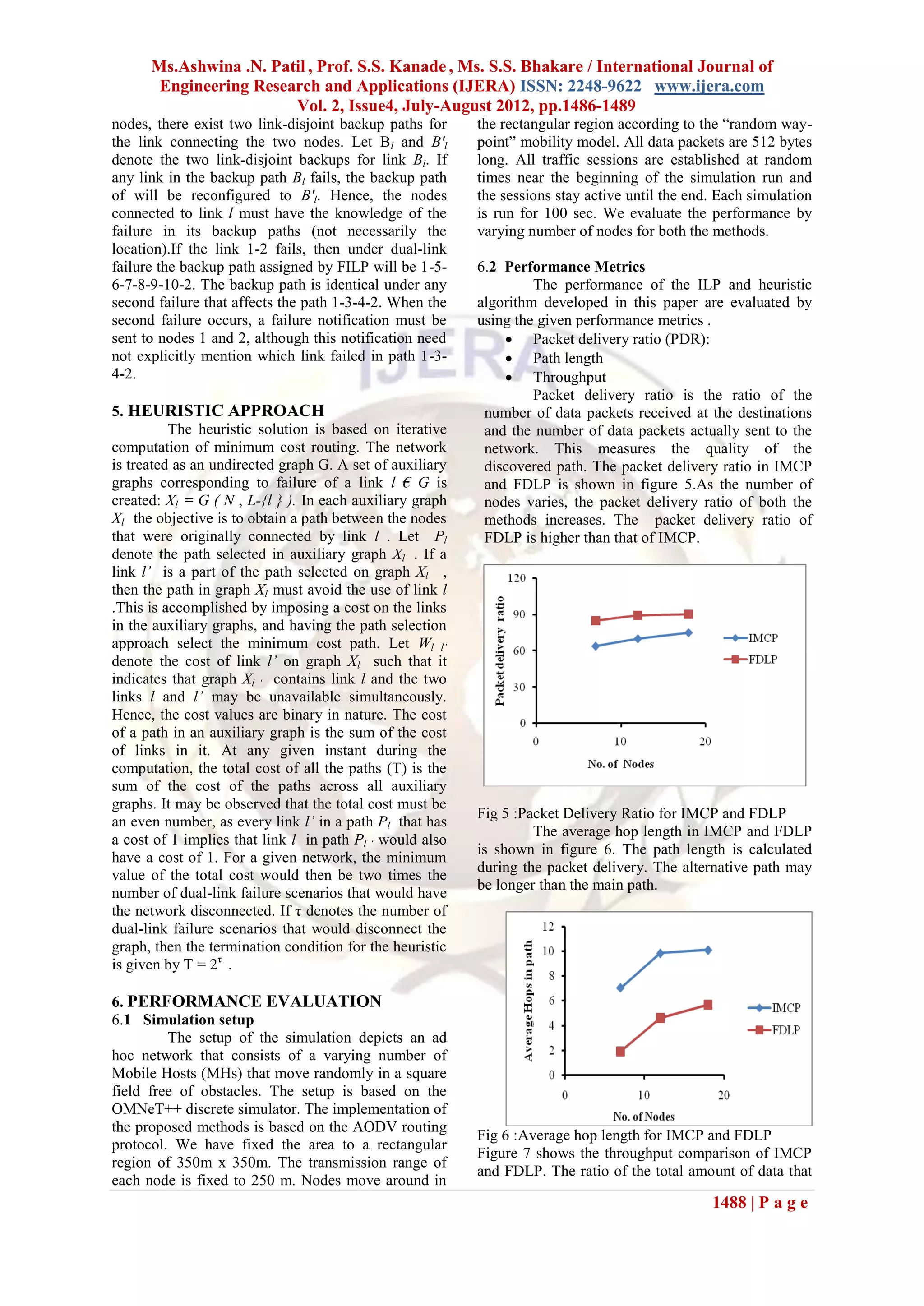
reaches a receiver from a sender to the time it takes [4] M. Clouqueur and W. D. Grover,
for the receiver to get the last packet is referred to as “Availability analysis of spanrestorable
throughput. It is expressed in bits per second or mesh networks,” IEEE J. Select. Areas
packets per second. Factors that affect throughput Commun., vol. 20,no. 4, pp. 810–821, (May
include frequent topology changes, unreliable 2002).
communication, limited bandwidth and limited [5] S. Ramamurthy, L. Sahasrabuddhe, and B.
energy. Packet delivery capacity of the proposed Mukherjee, “Survivable WDM mesh
method decreases as the network size increases. This networks,” IEEE/OSA J. Lightwave
is due to the route breaks as the number of size Technology, vol. 21,no. 4, pp. 870–883,
increases. (Apr. 2003).
[6] A. Chandak and S. Ramasubramanian,
“Dual-link failure resiliency through backup
link mutual exclusion,” in Proc. IEEE Int.
Conf. Broadband Networks, Boston, MA,
(Oct. 2005), pp. 258–267.
[7] R. Ramamurthy, A. Akyamac, J.-F.
Labourdette, and S. Chaudhuri, “Preemptive
reprovisioning in mesh optical networks,” in
Proc. OFC’(2003), pp. 785–787.
[8] H. Choi, S. Subramaniam, and H.-A. Choi,
“On double-link failure recovery in WDM
optical networks,” in Proc. IEEE
INFOCOM’(2002),vol. 2, pp. 808–816.
[9] S. Kim and S. Lumetta, “Evaluation of
protection reconfiguration for multiple
Fig 7: Variation of throughput with network size for failures inWDM mesh networks,” in Proc.
IMCP and FDLP OFC’(2003), pp. 210–211.
[10] D. Schupke and R. Prinz, “Performance of
7. CONCLUSION path protection and rerouting for WDM
This paper focuses on the approaches for networks subject to dual failures,” in Proc.
providing dual-link failure resiliency. Recovery from OFC’(2003),pp. 209–210. [10] S. S.
a dual-link failure using an extension constraint, Lumetta
referred to as BLME constraint, whose satisfiability [11] Perkins C E., “Ad Hoc Network”,
allows the network to recover from dual-link failures. Switzerland: Addsion-Wesley, (2000).
In this paper, we motivated the need for considering [12] S.J. Lee, E. Royer and C.E. Perkins,
double-link failures and presented some approaches “Scalability study of the ad hoc on-demand
for handling such failures. So here, we have proposed distance vector routing protocol”,
two schemes to solve BLME problem . The proposed International Journal of Network
scheme shows significant improvements in terms of Management, Vol.13, (2003), pp. 97–114.
packet delivery ratio, average hop length and [13] S. Corson and J. Macker, “Mobile ad hoc
throughput. networking (MANET): routing protocol
performance issues and evaluation
REFERENCES considerations”, RFC. 2501, (1999).
[1] B. Mukherjee, “WDM optical networks: [14] D.B Johnson, D.A Maltz and Josh Broch,
progress and challenges,” IEEE J. Select. “DSR: The Dynamic Source Routing
Areas Commun., vol. 18, pp. 1810–1824, Protocol for Multi-Hop Wireless Ad Hoc
(Oct. 2000). Networks”, In Ad Hoc Networking, edited
[2] O. Gerstel and R. Ramaswami, “Optical by Charles E. Perkins, Chapter 5, pp. 132–
layer survivability: a services perspective,” 172, Addison-Wesley, (2001).
IEEE Commun. Mag., vol. 38, pp. 104–113, [15] C.E. Perkins and E.M. Royer, “Ad-Hoc On
(March 2000). Demand Distance Vector Routing,”
[3] G. Mohan, C. S. R. Murthy, and A. K. Proceedings of the 2nd IEEE Workshop on
Somani, “Efficient algorithms for routing Mobile Computing Systems and
dependable connections in WDM optical Applications (WMCSA), New Orleans, LA,
networks,” IEEE/ACM Trans. Networking, (February 1999), pp. 90-100
vol. 9, pp. 553–566, (Oct. 2001)
1489 | P a g e](https://image.slidesharecdn.com/il2414861489-121002054800-phpapp01/75/Il2414861489-4-2048.jpg)