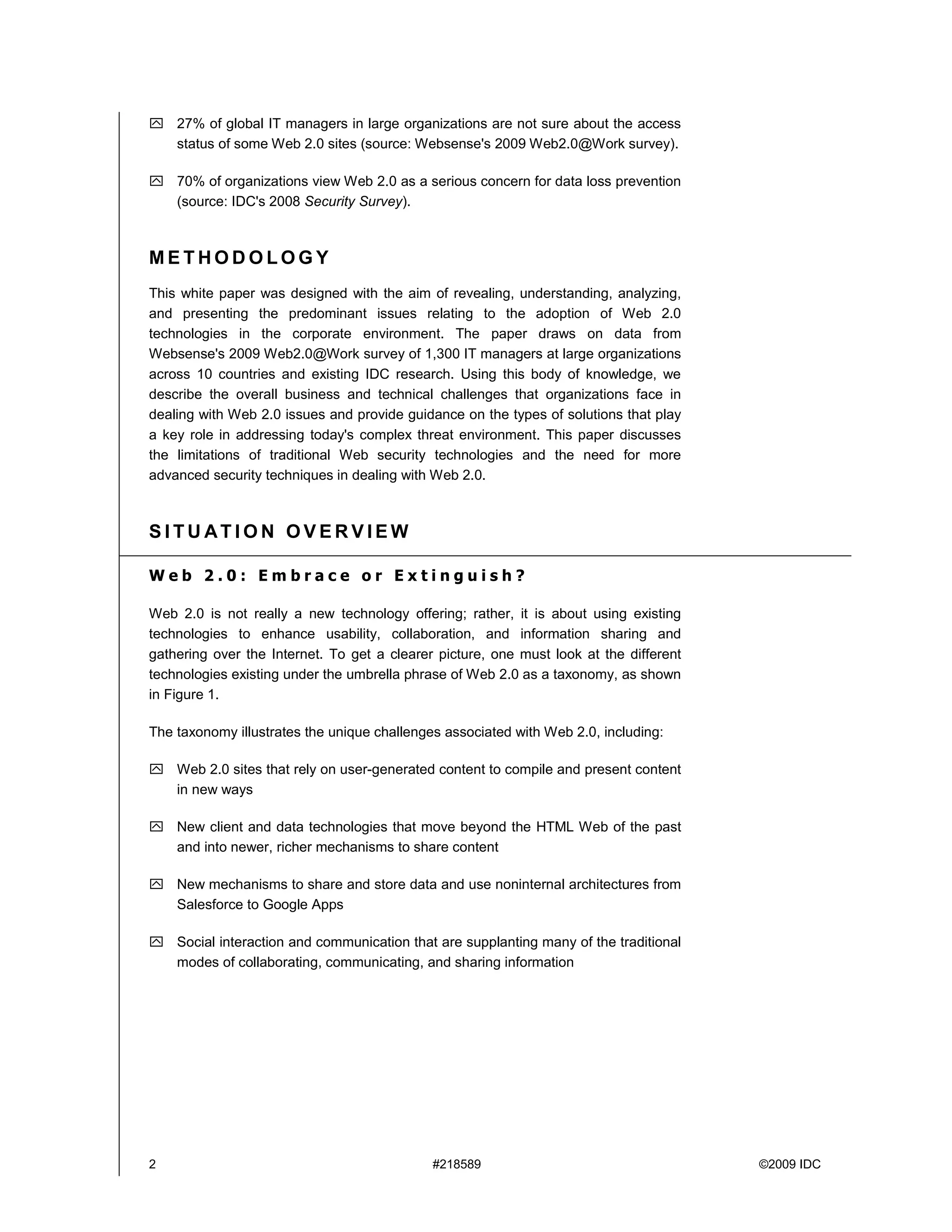
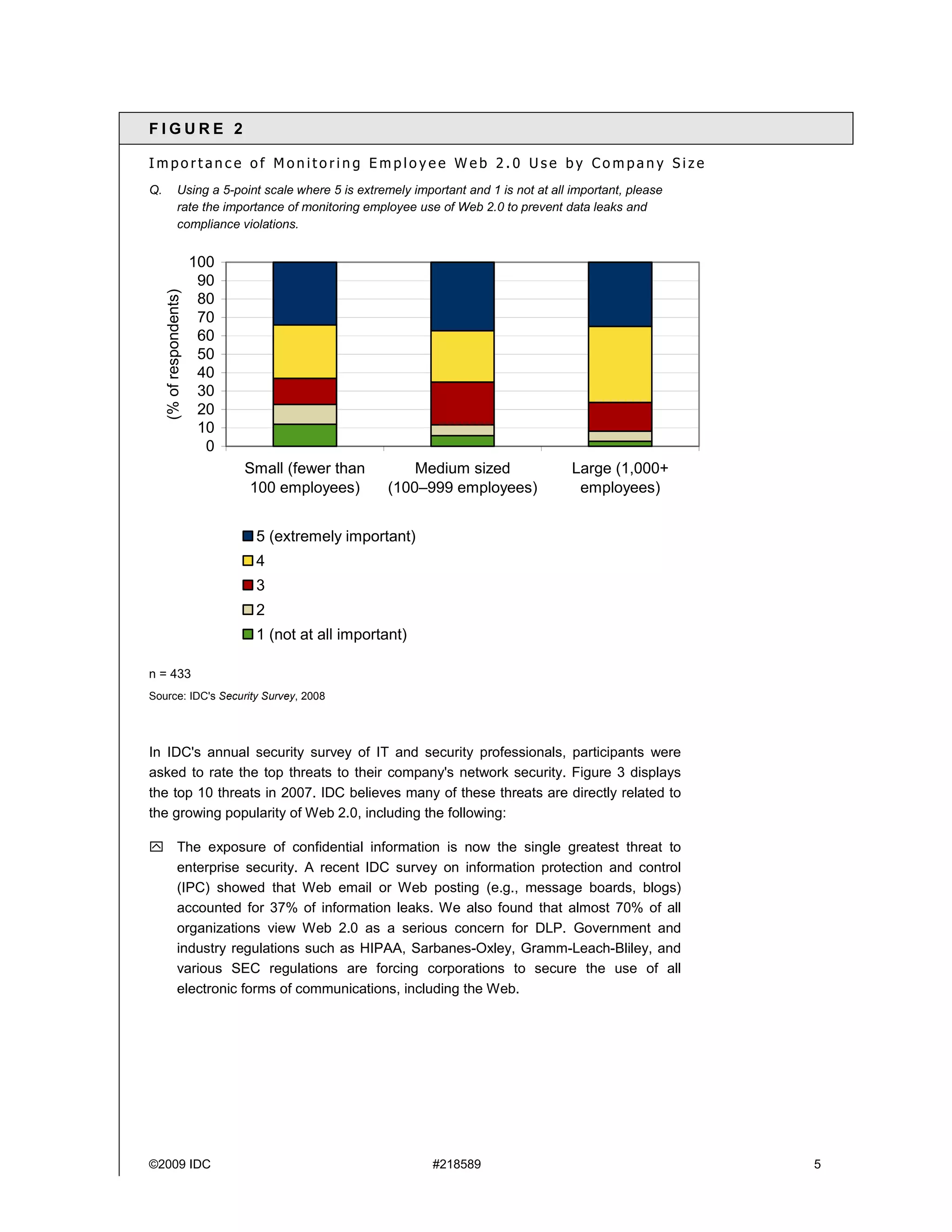
This white paper discusses best practices for securing web 2.0 technologies in organizations. It finds that 95% of organizations allow access to web 2.0 sites and 62% see them as necessary for business. However, only 64% permit access to social networks for business use, while 49% allow personal social networks. The paper provides an overview of web 2.0 technologies and the unique security challenges they pose. It argues that organizations should embrace web 2.0 to increase collaboration and productivity while securing these technologies to avoid security and compliance issues.