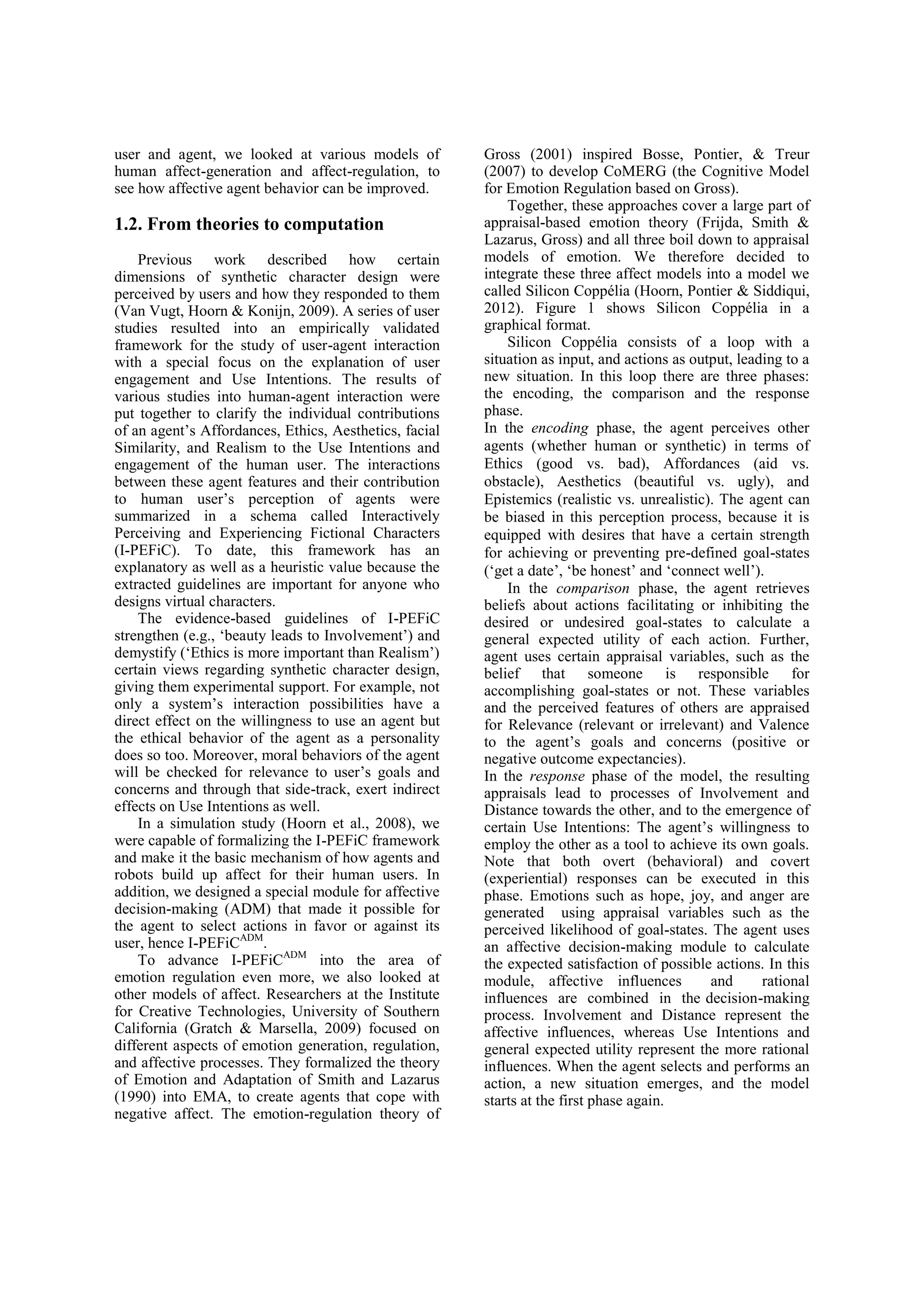
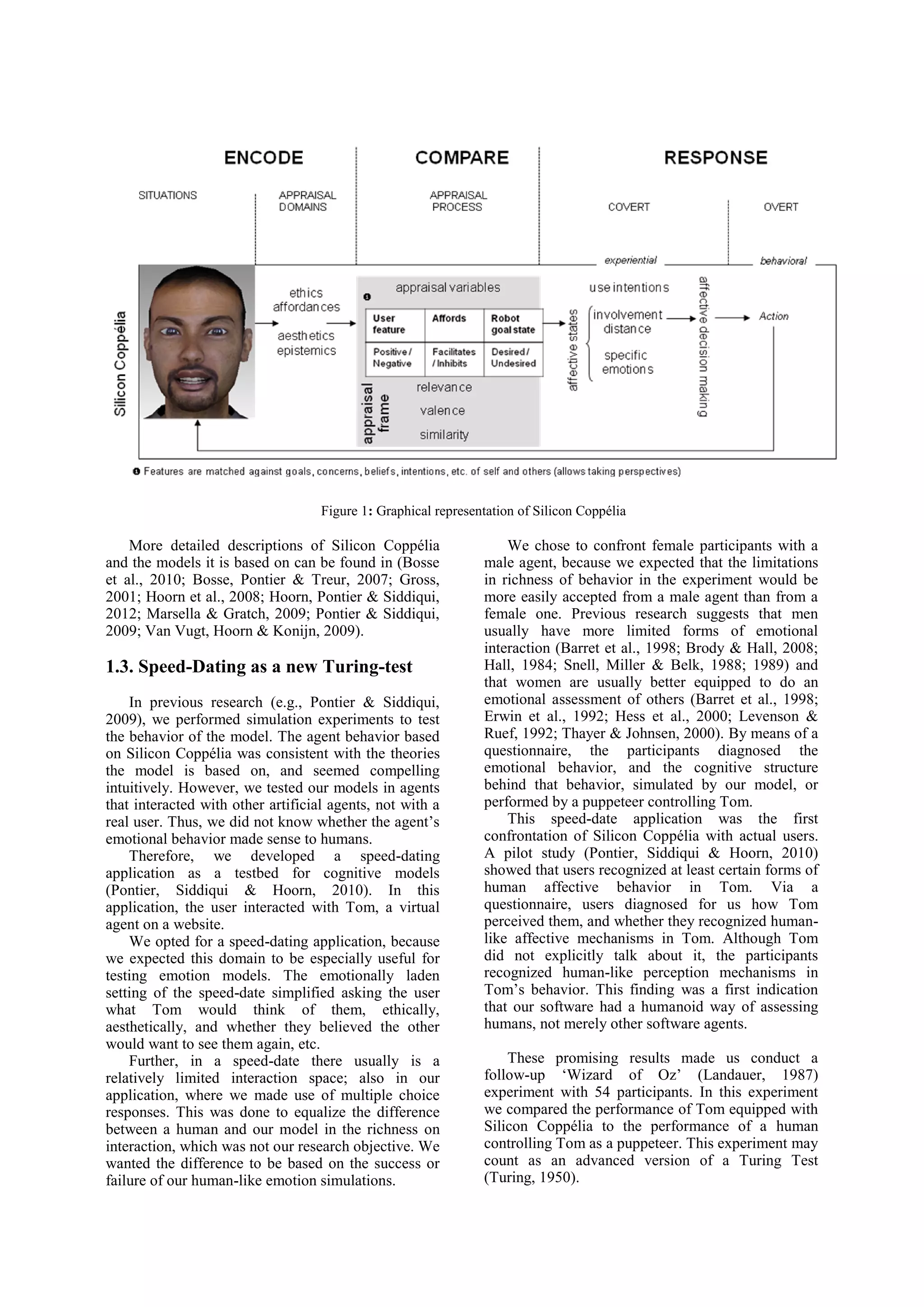
The document discusses the development and testing of a cognitive model for virtual agents, focusing on how these agents can simulate emotional interactions with users. It details a speed-dating experiment where a virtual agent named Tom interacted with participants to assess if users could discern human-like emotional responses between a machine and a human puppeteering a model. The findings suggest that participants did not detect significant differences in emotional behavior between Tom and the human controller, indicating potential for believable emotional expressions in AI systems.