Hw2 Rec07quest
•Download as PPT, PDF•
0 likes•180 views
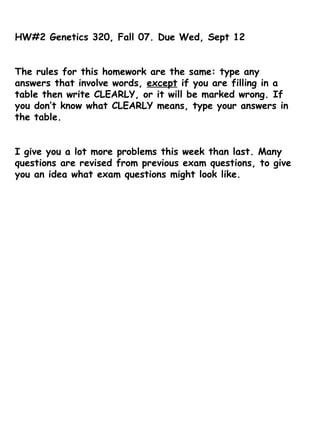
This document contains instructions for homework assignment #2 in a genetics course. It includes questions about gene expression, mutation, protein function, recombination, and cancer genetics. Students are asked to answer questions about DNA sequences, genetic code, chromosome structure, and mechanisms like transcription, translation, and recombination through diagrams and short explanations.
Report
Share
Report
Share
Recommended
Initiation and termination codons , mutation and genetic code

HNGU PATAN.
m.sc sem 3 botany
cbo - 503
Genetic Information Transfer (Biology for Engineers)

Information Transfer: Purpose: The molecular basis of coding and
decoding genetic information is universal. Molecular basis of information
transfer. DNA as a genetic material. Hierarchy of DNA structure- from
single stranded to double helix to nucleosomes. Concept of genetic code.
Universality and degeneracy of genetic code. Define gene in terms of
complementation and recombination.
Recommended
Initiation and termination codons , mutation and genetic code

HNGU PATAN.
m.sc sem 3 botany
cbo - 503
Genetic Information Transfer (Biology for Engineers)

Information Transfer: Purpose: The molecular basis of coding and
decoding genetic information is universal. Molecular basis of information
transfer. DNA as a genetic material. Hierarchy of DNA structure- from
single stranded to double helix to nucleosomes. Concept of genetic code.
Universality and degeneracy of genetic code. Define gene in terms of
complementation and recombination.
Genetic code

Deciphering of genetic code and its salient features for undergraduates in biology, biochemistry and medicine
Genetic code 

Genetic code describes codons that code amino acids. Contents are well defined according to process central dogma specially Translation mechanism.
Genetic code 

This presentation is regarding Genetic code, its properties and exceptions to genetic code
GENETIC CODE

GENETIC CODE
HISTORY AND DISCOVERY
FEATURES OF GENETIC CODE
IMPORTANCE
DEGENERATE CODON
UNAMBIGUOUS NATURE OF CODON
CODON ON mRNA AND ANTICODON ON t RNA
Gene Mutations

A GENE is the basic physical and functional unit of heredity. Genes are made up of DNA. Some genes act as instructions to make molecules called proteins. However, many genes do not code for proteins. In humans, genes vary in size from a few hundred DNA bases to more than 2 million bases.
GENE MUTATIONS
A gene mutation is a permanent alteration in the DNA sequence that makes up a gene, such that the sequence differs from what is found in most people. Mutations range in size; they can affect anywhere from a single DNA building block (base pair) to a large segment of a chromosome that includes multiple genes.
Genetic code - with YouTube video

Dr. Karthikeyan Pethusamy MD DNB (Biochemistry) explains the genetic code for the undergraduate students. Don't miss the YouTube video attached. The video is made with the same power point file.
USMLE Step 1 Molecular Biology and Biochemistry review

This is a review for the USMLE Step 1 exam for Molecular Biology and Biochemistry.
It contains anything you need to know for your exam in pictures, tables and diagrams.
USMLE Step 1 Genetics review

This is a review for the USMLE Step 1 of Genetics. It contains anything you need to know for your exam in pictures, diagrams and tables.
Genetic codons

genetic codons are the series of nucleotides that specifies which amino acid will be added next during the process of photosynthesis
More Related Content
What's hot
Genetic code

Deciphering of genetic code and its salient features for undergraduates in biology, biochemistry and medicine
Genetic code 

Genetic code describes codons that code amino acids. Contents are well defined according to process central dogma specially Translation mechanism.
Genetic code 

This presentation is regarding Genetic code, its properties and exceptions to genetic code
GENETIC CODE

GENETIC CODE
HISTORY AND DISCOVERY
FEATURES OF GENETIC CODE
IMPORTANCE
DEGENERATE CODON
UNAMBIGUOUS NATURE OF CODON
CODON ON mRNA AND ANTICODON ON t RNA
Gene Mutations

A GENE is the basic physical and functional unit of heredity. Genes are made up of DNA. Some genes act as instructions to make molecules called proteins. However, many genes do not code for proteins. In humans, genes vary in size from a few hundred DNA bases to more than 2 million bases.
GENE MUTATIONS
A gene mutation is a permanent alteration in the DNA sequence that makes up a gene, such that the sequence differs from what is found in most people. Mutations range in size; they can affect anywhere from a single DNA building block (base pair) to a large segment of a chromosome that includes multiple genes.
Genetic code - with YouTube video

Dr. Karthikeyan Pethusamy MD DNB (Biochemistry) explains the genetic code for the undergraduate students. Don't miss the YouTube video attached. The video is made with the same power point file.
USMLE Step 1 Molecular Biology and Biochemistry review

This is a review for the USMLE Step 1 exam for Molecular Biology and Biochemistry.
It contains anything you need to know for your exam in pictures, tables and diagrams.
USMLE Step 1 Genetics review

This is a review for the USMLE Step 1 of Genetics. It contains anything you need to know for your exam in pictures, diagrams and tables.
Genetic codons

genetic codons are the series of nucleotides that specifies which amino acid will be added next during the process of photosynthesis
What's hot (20)
USMLE Step 1 Molecular Biology and Biochemistry review

USMLE Step 1 Molecular Biology and Biochemistry review
Viewers also liked
Salon Jesień - XXII Targi Kosmetyczne i Solaryjne

Specjalnie dla Was nasi reporterzy odwiedzieli XXII Targi Kosmetyczne i Solaryjne - Salon Jesień. Serdecznie zapraszamy na fotorelację.
Fotorelacja Targi Lady 2007

Dziennikarze i fotoreporter portalu ChceBycPiekna.pl podejrzeli wraz z kamerą Międzynarodowe Targi Kosmetyczne Lady, odbywające się na warszawskim Torwarze. Zobacz i Ty, co się tam działo, i co uchwyciła nasza kamera.
Viewers also liked (17)
Similar to Hw2 Rec07quest
Advances In Thalassemia Research

Academic Paper Writing Service
http://StudyHub.vip/Advances-In-Thalassemia-Research 👈
Biology 204 Principles of Biology I Assignment 2C

Biology 204 Principles of Biology I Assignment 2C
For students with first names starting with the letters O to Z.
This assignment is graded out of 110 points, and is worth 10% of your final mark. Please submit this assignment after you have completed Chapter 16 and before you write the final exam
Method and Practice in Biological Anthropology 1st Edition Hens Solutions Manual

Full download : http://alibabadownload.com/product/method-and-practice-in-biological-anthropology-1st-edition-hens-solutions-manual/
Method and Practice in Biological Anthropology 1st Edition Hens Solutions Manual
Antibody diversity with special emphasis on v(d)j recombination

Reason behind antibody diversity and mechanism of V(D)J recombination by Sourin Adhikary.
Genes, Genomics, and Chromosomes computational biology introduction .ppt

The 5 ß-globin genes are derived from an ancestral ß-globin gene via gene duplication. Over time, these genes accumulated adaptive mutations via sequence drift resulting in the specialized species of ß-globin proteins. Genomic DNA also contains nonfunctional DNA sequences called pseudogenes that are derived from gene duplication or reverse transcription and integration of cDNA sequences made from mRNA (covered below). ß-globin pseudogenes contain introns and thus were derived by gene duplication. Over time these genes became nonfunctional also due to sequence drift. Because they are not harmful, pseudogenes remain in the genome, marking a gene duplication event in an earlier ancestor.
The ß-globin gene cluster on chromosome 11 is shown in Fig. 6.4a. The ß-globin genes are expressed in different stages of life. , Ag, and Gg are expressed during different trimesters of fetal development (next slide). ß expression begins around birth & continues throughout adult life. Fetal hemoglobin molecules made with the d and G or A polypeptides have a higher affinity for O2 than maternal hemoglobin, facilitating O2 transfer to the fetus.
Higher eukaryotes contain far more noncoding DNA between genes than bacteria and simple eukaryotes (Fig. 6.4). The region of human genomic DNA containing the ß-globin gene cluster shown in the figure actually is a relatively "gene-rich" region of human DNA. Some regions known as gene-poor "deserts" also occur. Higher eukaryotes also contain a larger amount of intron DNA. Although one-third of human DNA is transcribed into pre-mRNA, 95% ends up being degraded after RNA splicing reactions. On average, the typical exon is 50-200 bp in length, while the median length of introns is 3.3 kb in human genes.
DNA fingerprinting is a method for identifying individuals based on their minisatellite DNA (Fig. 6.7). It was developed in the mid-80s and is widely used in forensics, paternity analysis, and for research purposes. In the method, minisatellite DNA from a genomic DNA specimen is amplified by PCR using primers that bind to unique sequences flanking minisatellite repeat units. Bands corresponding to each minisatellite locus then are separated on gels. Although satellite DNA is highly conserved in sequence, the number of tandem copies at each loci is highly variable between individuals. This results from unequal crossing over during formation of gametes in meiosis. Due to the variation in the number of repeats at each locus, different individuals can be readily distinguished based on banding patterns.
Interspersed repeat DNA comprises the largest fraction of repetitious DNA in eukaryotic genomes. This DNA, which is also called moderately repeated DNA makes up ~45% of human genomic DNA. Interspersed repeat DNA is composed of partial and complete transposon sequences or "mobile DNA". Mobile DNAs were discovered by Barbara McClintock in the 1940s. These sequences move by "transposition". Transpositions in germ line cells are inhe
Similar to Hw2 Rec07quest (20)
Method and Practice in Biological Anthropology 1st Edition Hens Solutions Manual

Method and Practice in Biological Anthropology 1st Edition Hens Solutions Manual
Antibody diversity with special emphasis on v(d)j recombination

Antibody diversity with special emphasis on v(d)j recombination
Genes, Genomics, and Chromosomes computational biology introduction .ppt

Genes, Genomics, and Chromosomes computational biology introduction .ppt
Recently uploaded
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
ODC, Data Fabric and Architecture User Group

Let's dive deeper into the world of ODC! Ricardo Alves (OutSystems) will join us to tell all about the new Data Fabric. After that, Sezen de Bruijn (OutSystems) will get into the details on how to best design a sturdy architecture within ODC.
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Recently uploaded (20)
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Hw2 Rec07quest
- 1. HW#2 Genetics 320, Fall 07. Due Wed, Sept 12 The rules for this homework are the same: type any answers that involve words, except if you are filling in a table then write CLEARLY, or it will be marked wrong. If you don’t know what CLEARLY means, type your answers in the table. I give you a lot more problems this week than last. Many questions are revised from previous exam questions, to give you an idea what exam questions might look like.
- 5. 4. Consider the cell 1 and cell 2 with the chromosomes shown. In Cell 1, Gene A is 50cM from the centromere, and in Cell 2 Gene C is 10cM from the centromere. In both cells the wildtype allele is on the top homolog, and the mutant allele on the bottom homolog. This problem involves mitotic recombination . Gene A+ + - a. Will Cell 1 or Cell2 form homozyous mutants at the highest frequency? Explain. b. A new Cell 3 is like Cell 1 except that it has a recessive lethal mutation. d- 10cM to the left of the GeneA+ allele. Where would the D+ allele be in Cell 3? (this should be obvious) c. Will Cell 1 or Cell 3 give the most viable a-/a- mutants? Explain. Cell 1 Cell 2 Gene C + -
- 7. 6. Explain why a person with a germline genotype of p53+/- is prone to cancer while a person with a germline genotype of CFRT-/+ is not prone to cystic fibrosis. 7. In the pedigree shown below, compare the relative extent of heterology (between any two homologous chromosome) in individual 1, individual 2 and individual 3. 1 2 3