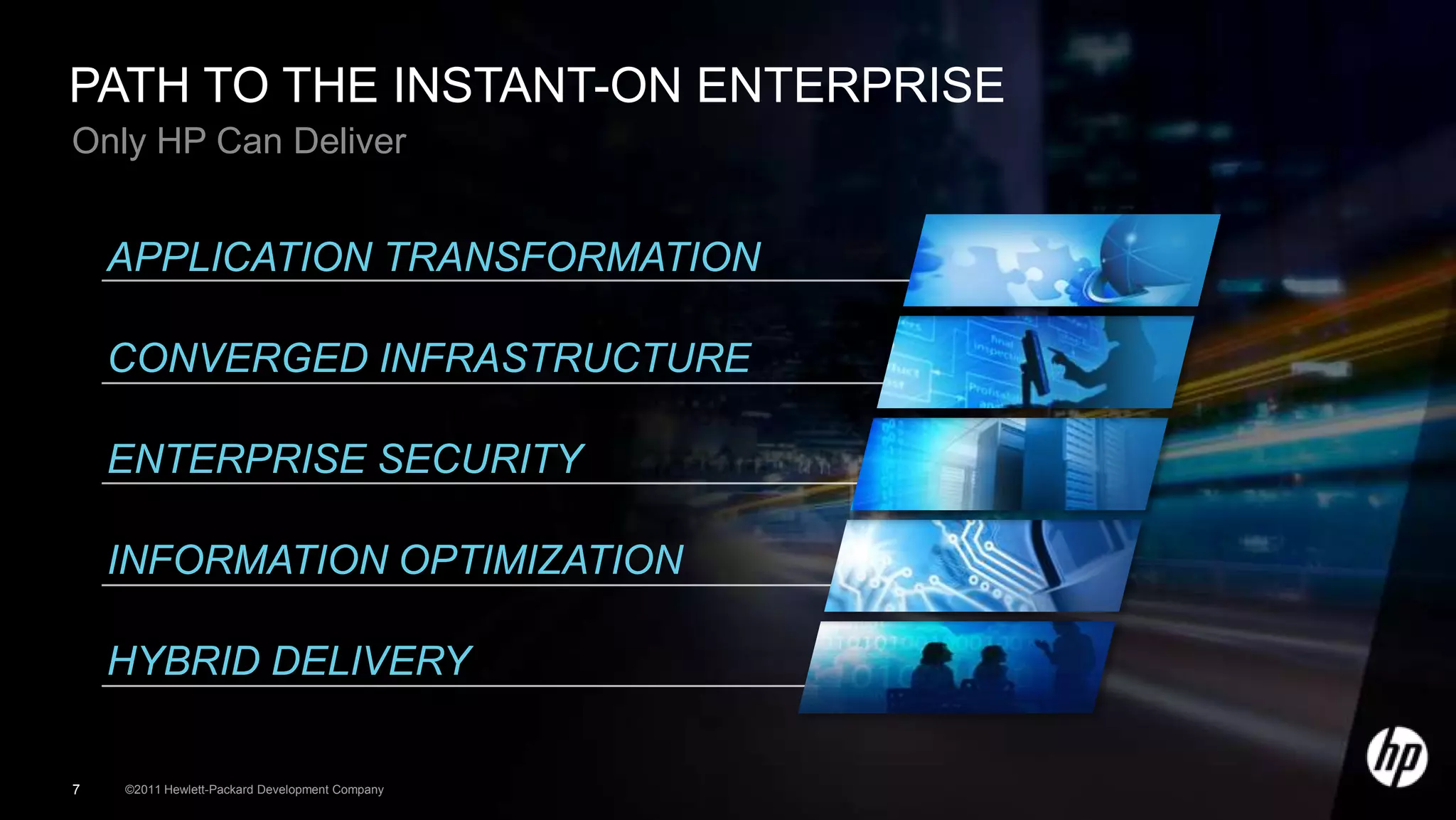
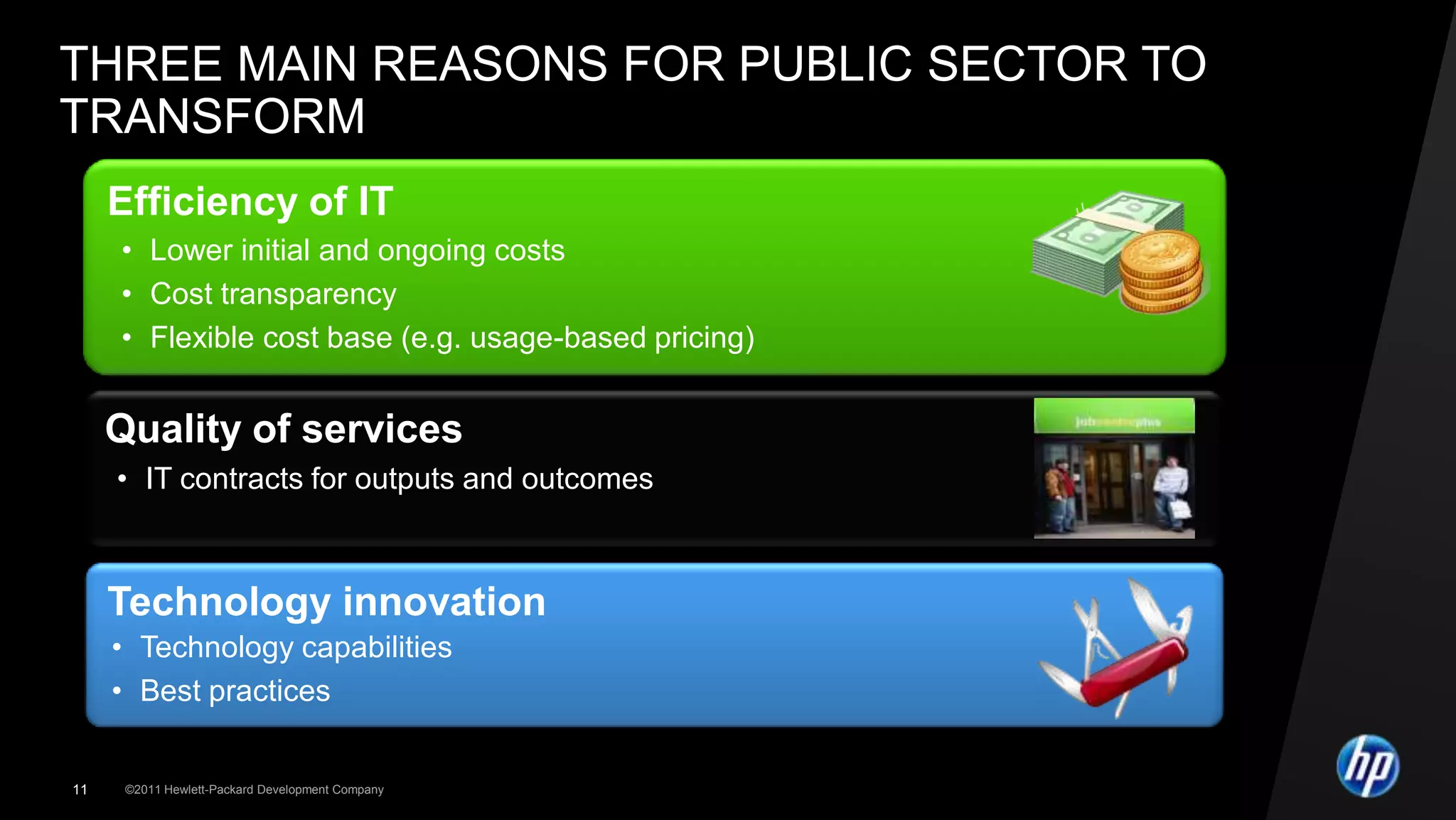
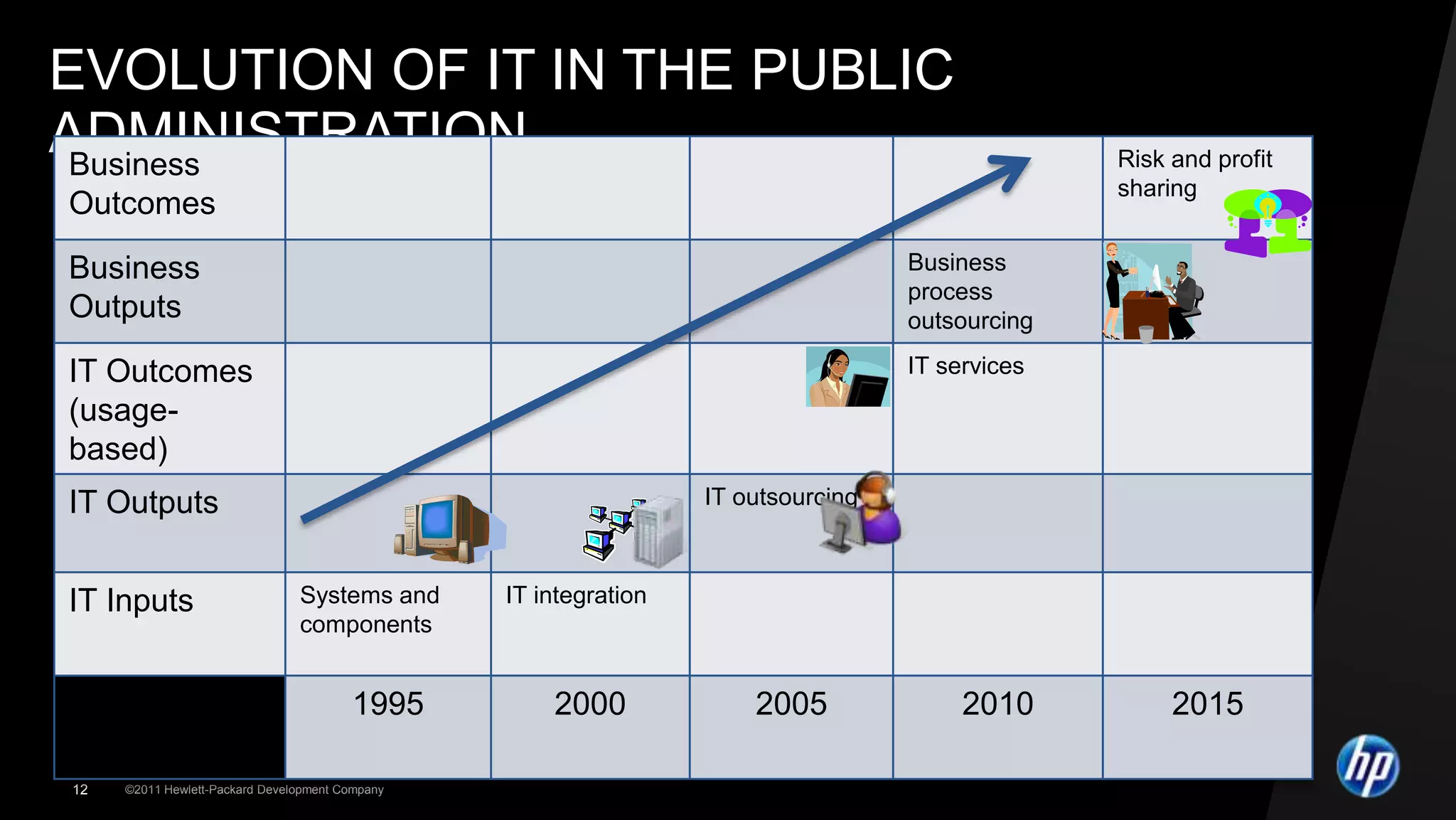
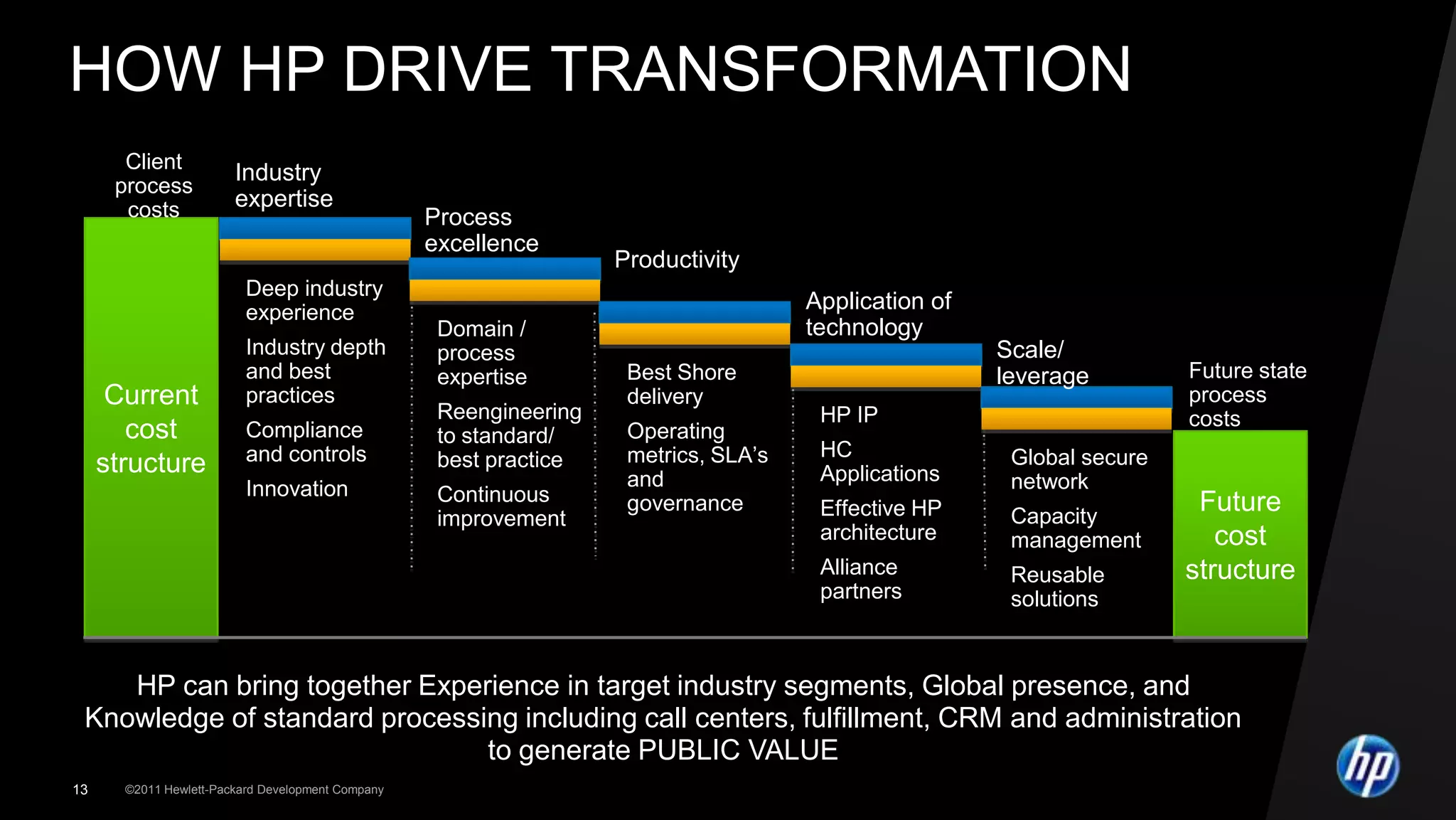
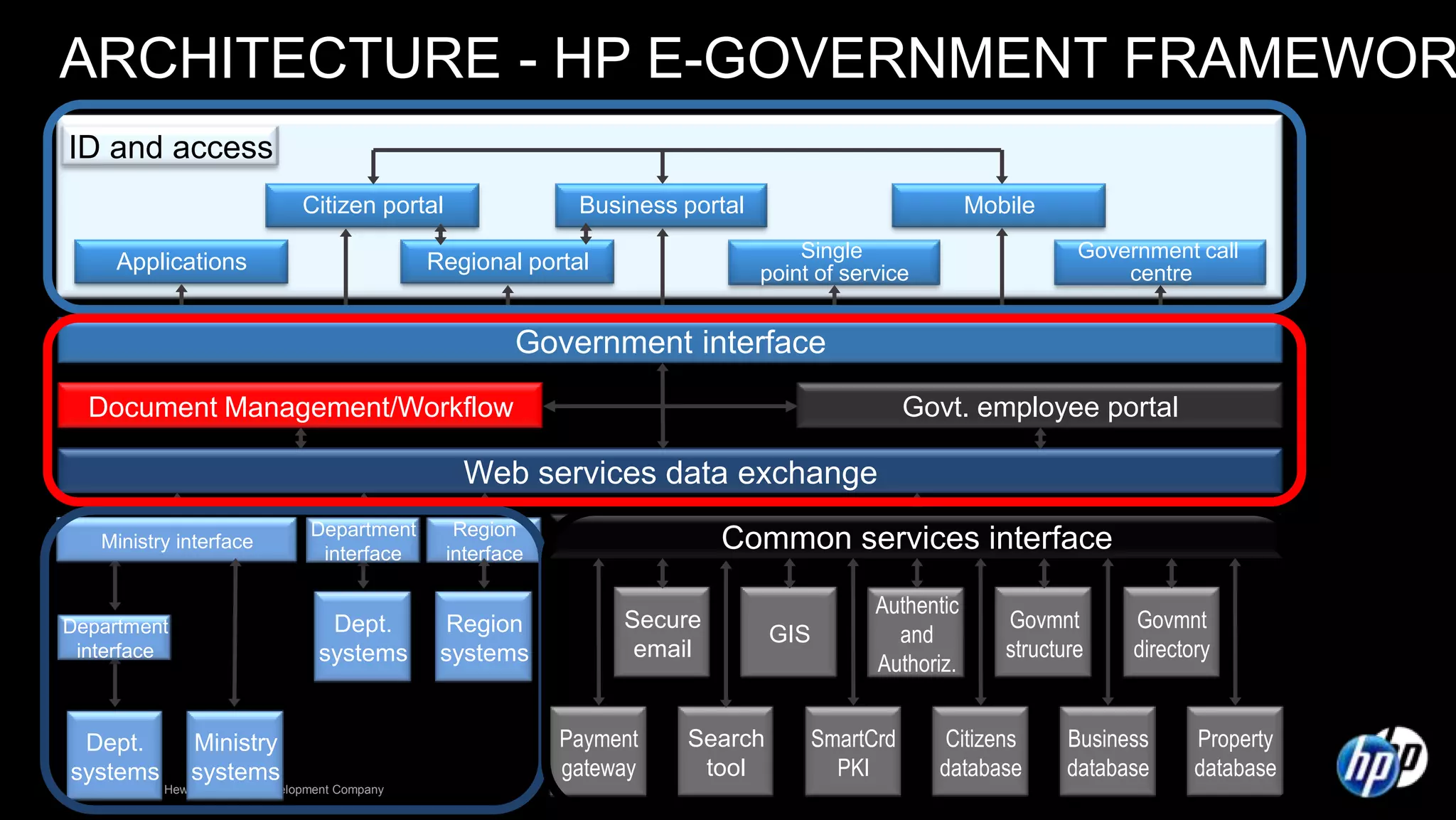
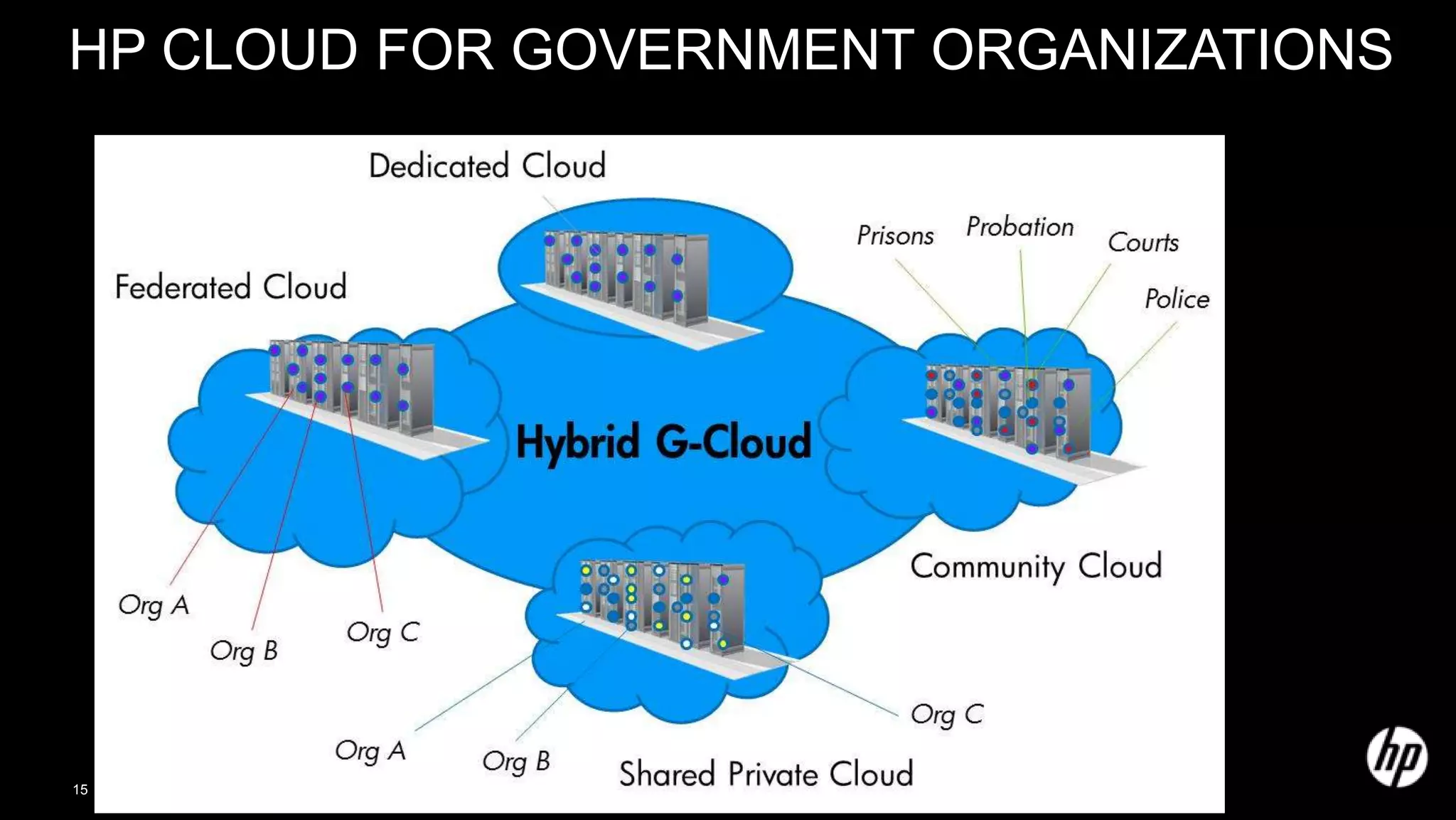
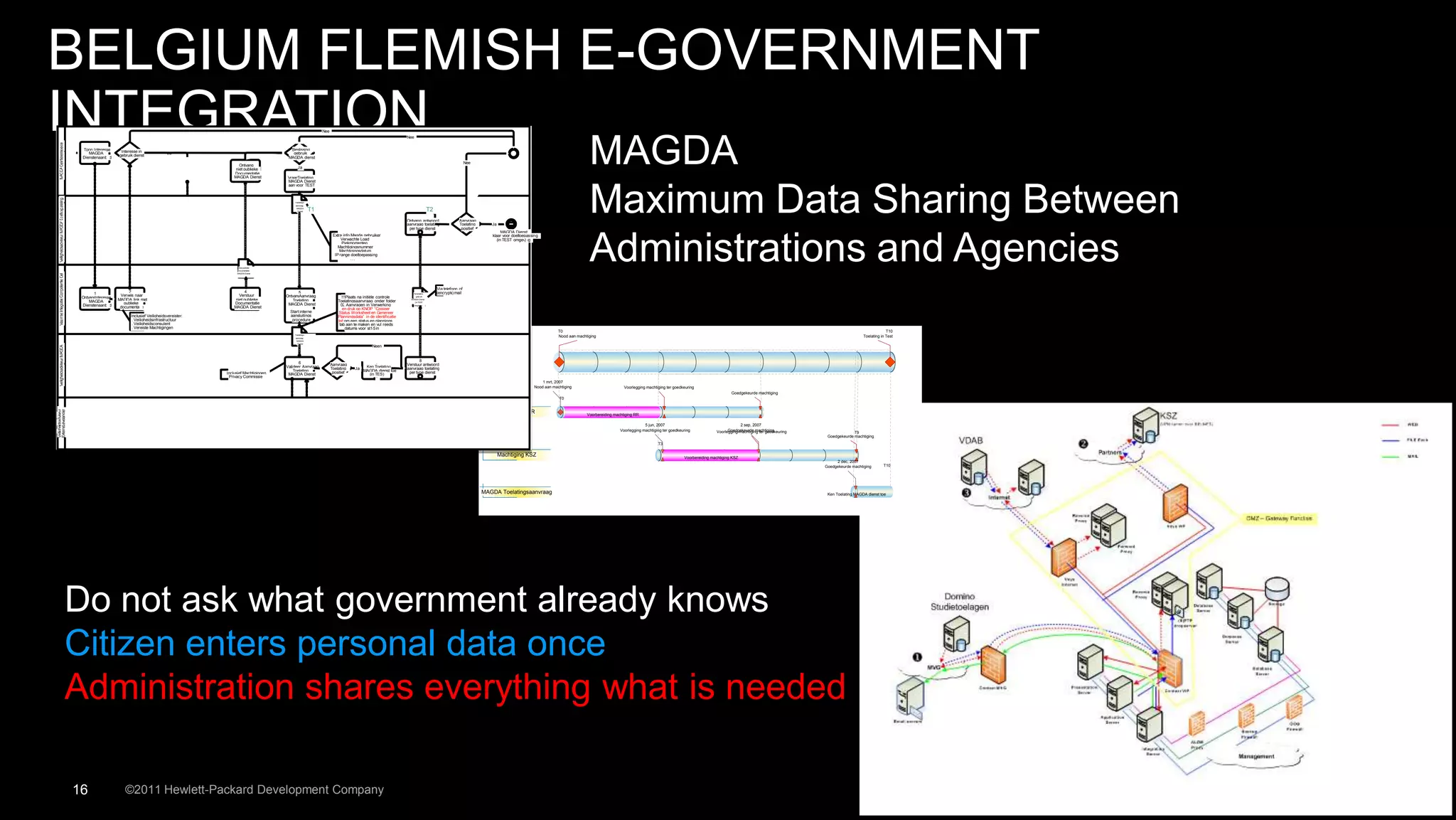
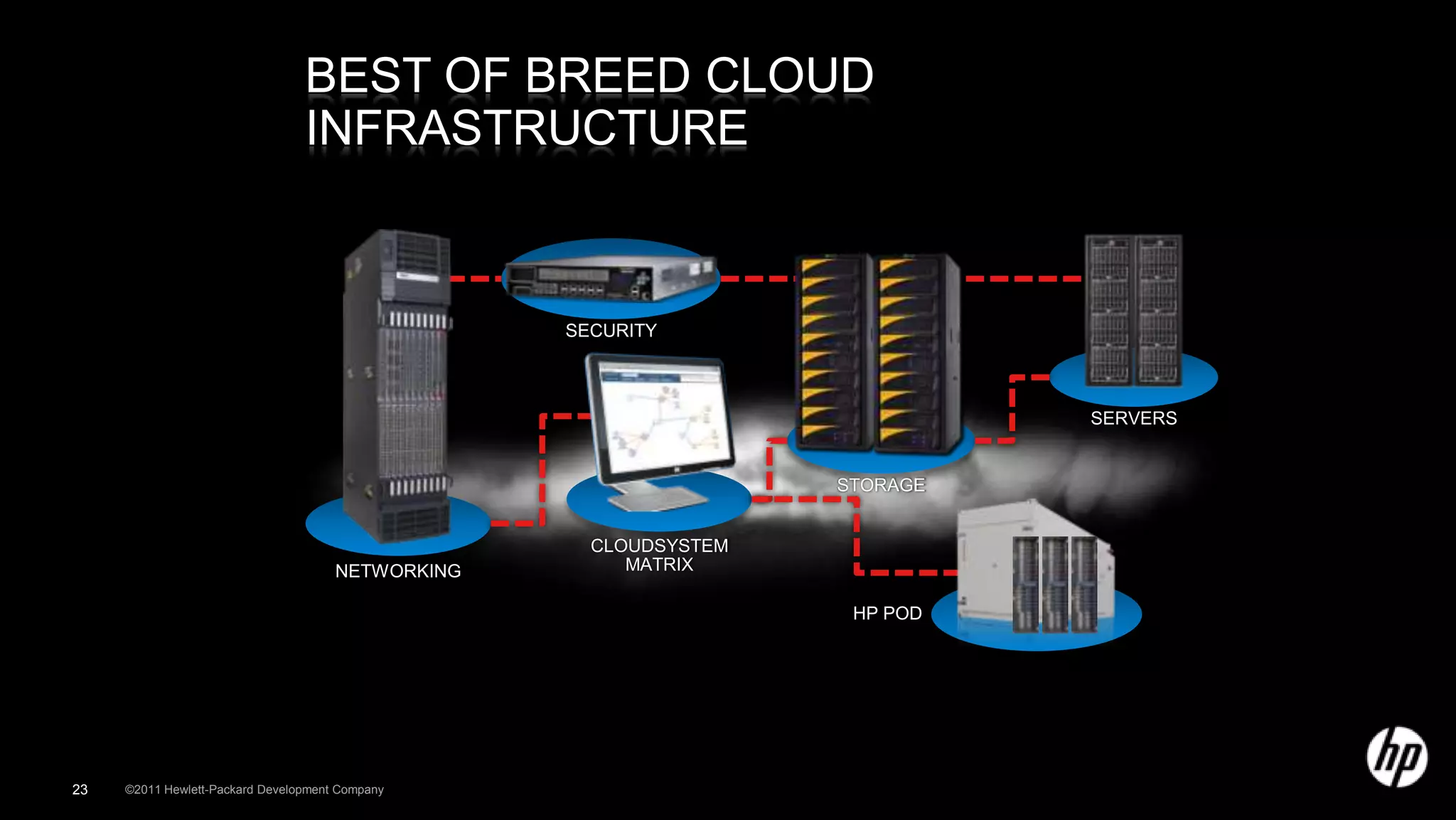
HP can help governments transform to an instant-on enterprise through application transformation, converged infrastructure, enterprise security, information optimization, and hybrid delivery models. HP drives transformation by leveraging its industry expertise, process excellence, productivity improvements from best shore delivery and use of HP intellectual property, and ability to scale and leverage solutions globally. This transformation helps governments improve efficiency, quality of services, and ability to adopt new technologies.