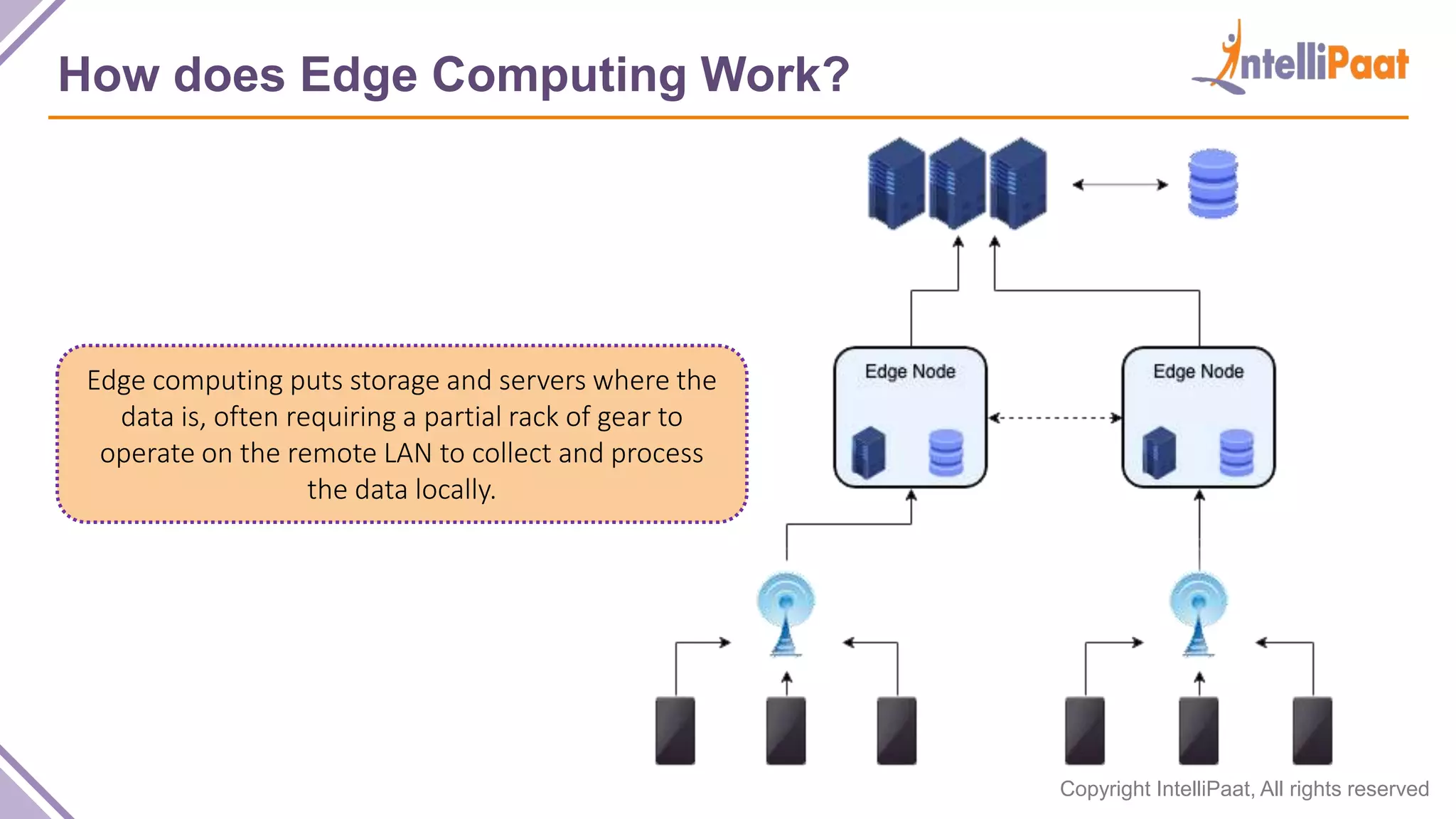
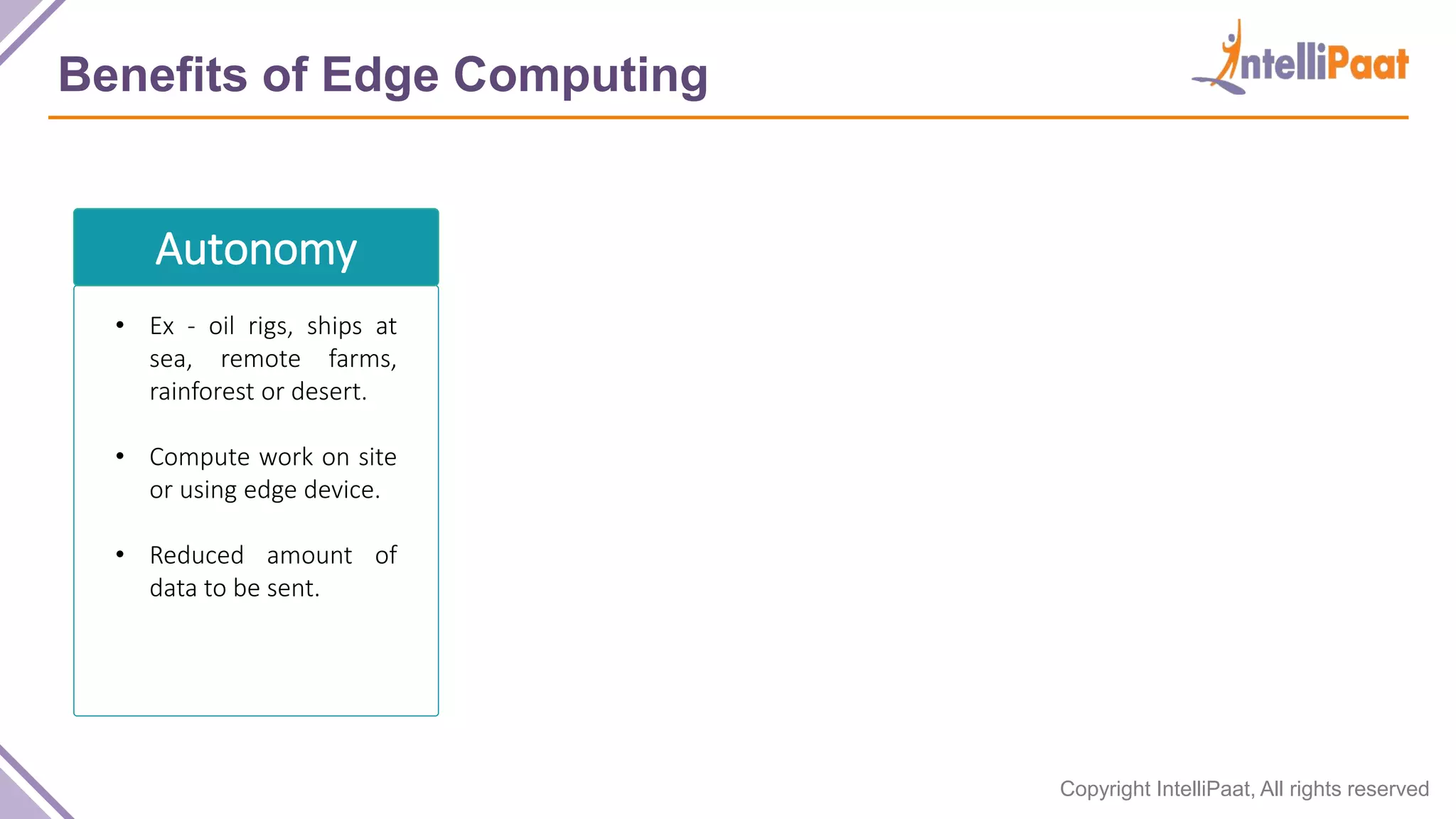
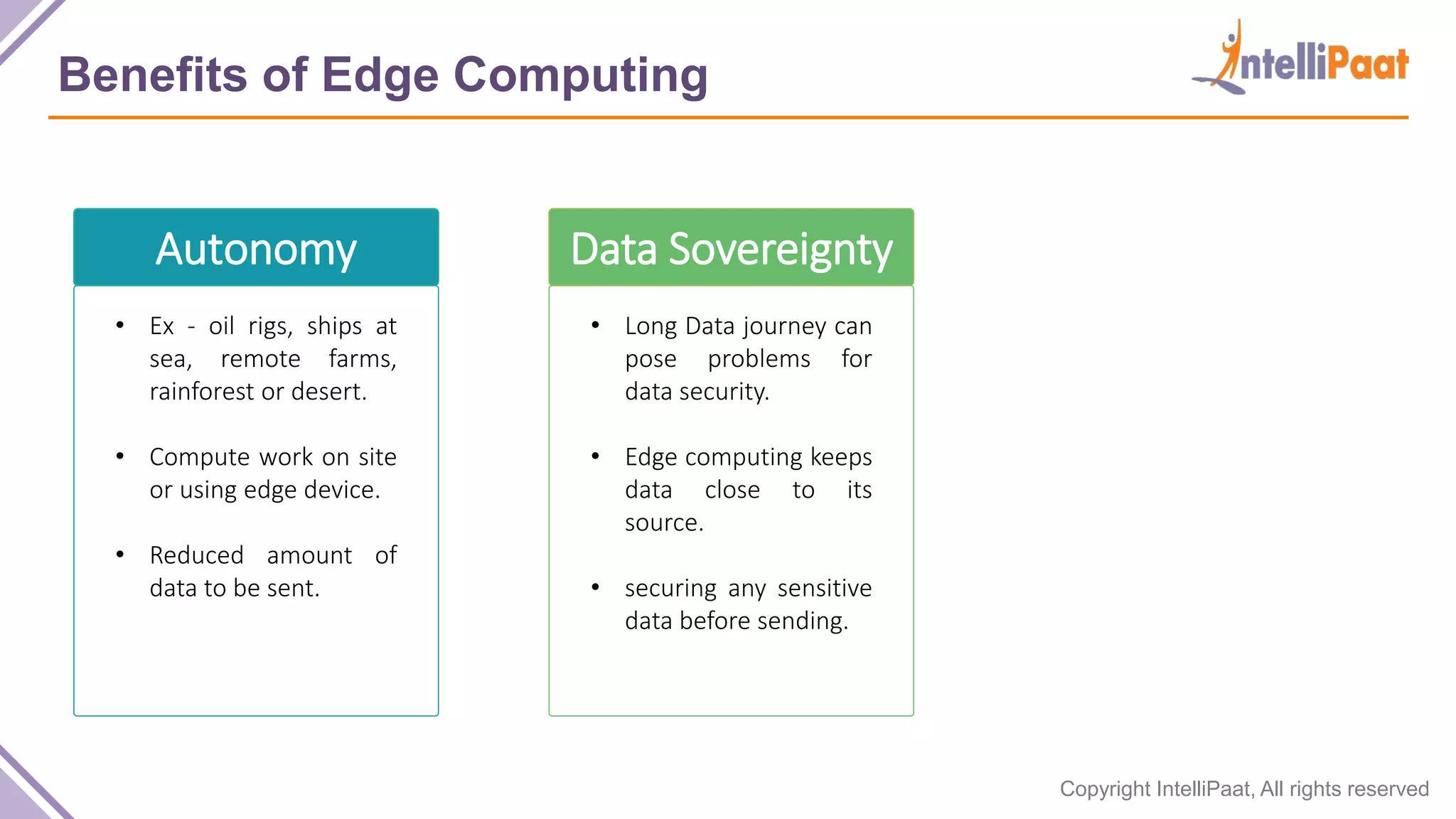
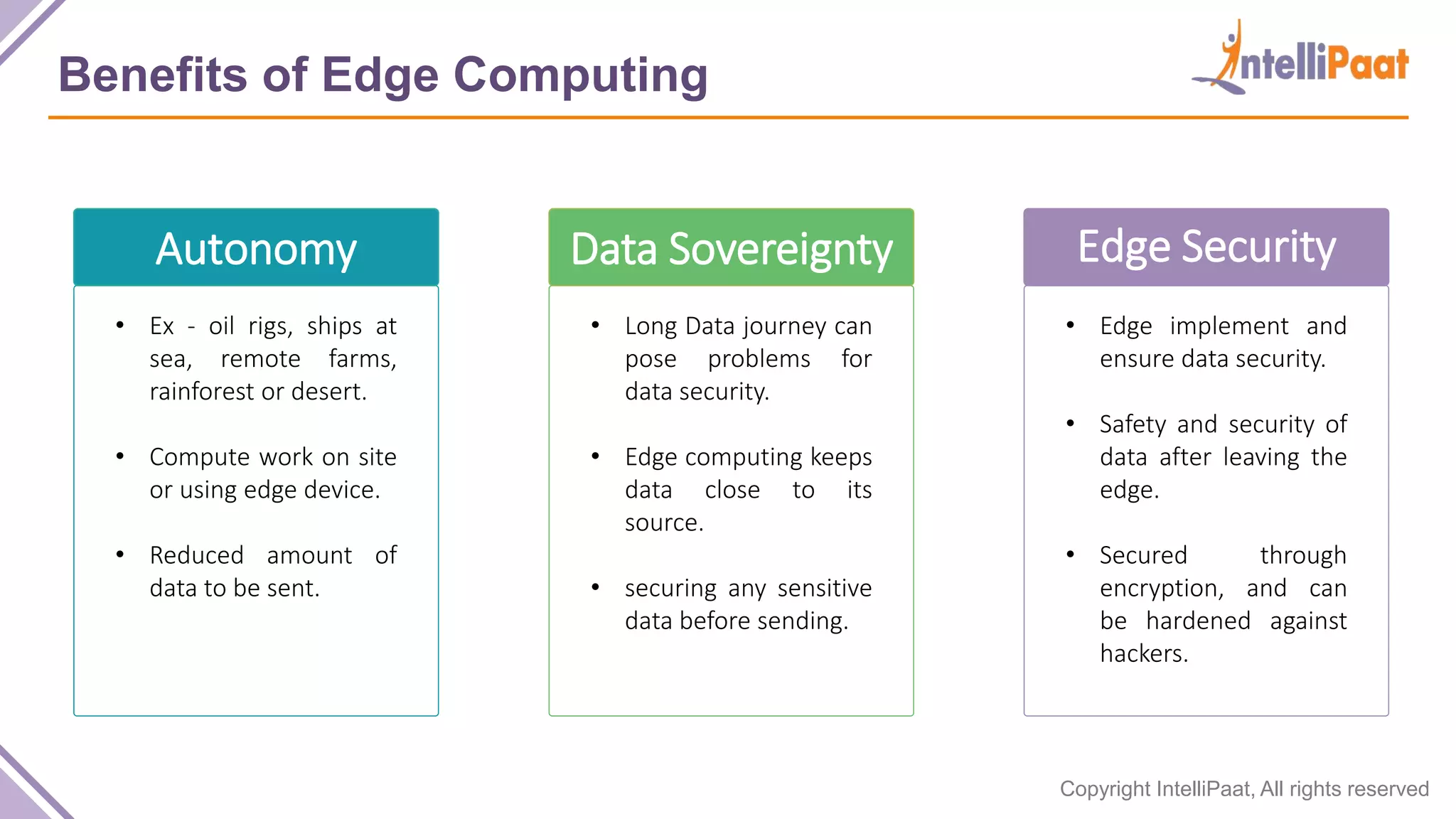
The document provides an overview of edge computing, explaining its definition, origins, functionality, and various use cases. It highlights the benefits, such as improved data autonomy and security, while also discussing challenges like connectivity issues and the need for proper device management. Use cases include manufacturing, healthcare, transportation, and retail.